Search results for "ransomware "
-

 107Malware
107MalwareODCODC Ransomware Decryptor released by BloodDolly
A decryptor has been released by ransomware expert BloodDolly that will allow victim’s encrypted by the ODCODC Ransomware to recover their files...
-

 117Incidents
117IncidentsWhy It May Be Worth Paying The Ransom In A Ransomware Attack
Australia is being hit hard by ransomware attacks and we’ve heard a lot of security vendors advise against paying the ransom that...
-

 241Data Security
241Data SecurityWave of business websites hijacked to deliver crypto-ransomware
Sites exploited by SoakSoak bots give the gift of CryptXXX malware. If you’ve visited the do-it-yourself project site of Dunlop Adhesives, the...
-
 107Malware
107MalwareRansomware As A Service Being Offered For $39 On The Dark Net
Hackers who want to make money but don’t want to get involved in the messy business of extracting payment from victims have turned...
-
 88Malware
88MalwareRansomware’s Motto: The Simpler, The Scarier, The Better
A lot has been said about the ransomware epidemic. The number of infections worldwide increases daily, as well as the number of...
-

 352Cyber Crime
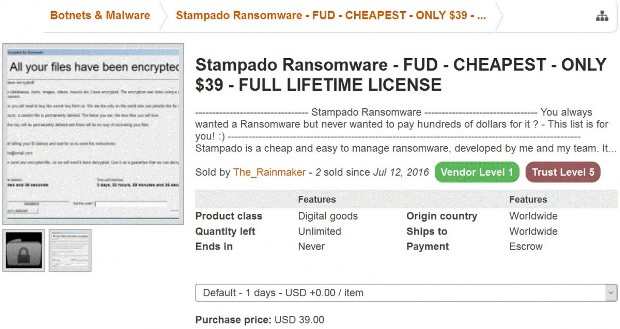
352Cyber CrimeHackers Selling FUD Stampado Ransomware for Just $39
Hackers are selling Stampado Ransomware on the dark net for just $39 — They claim it’s FUD (fully undetectable)! The Dark Net is full of...
-

 200Data Security
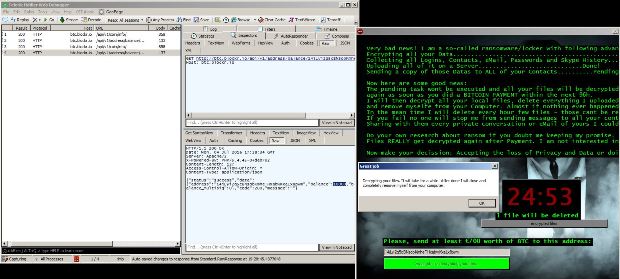
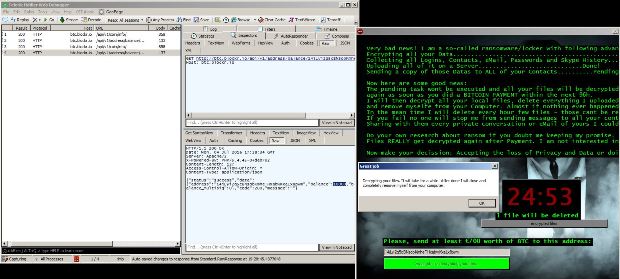
200Data SecurityPosing as ransomware, Windows malware just deletes victim’s files
Tagged as “Ranscam”, Powershell and script-based malware is a botched smash-and-grab. There has been a lot of ingenuity poured into creating crypto-ransomware, the...
-
 213Malware
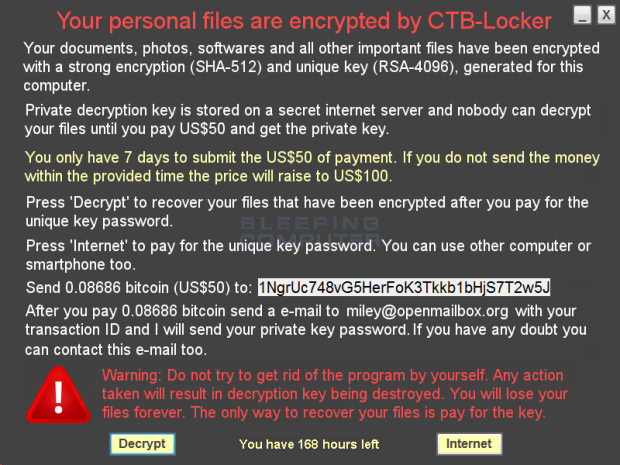
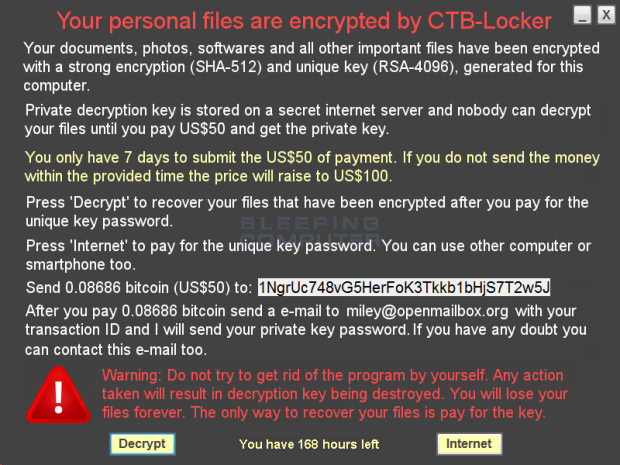
213MalwareCTB-Faker Ransomware does a poor job imitating CTB-Locker
A new ransomware called CTB-Faker was discovered that pretends to be the CTB-Locker ransomware. It is a poor imitator, though, as instead of...
-
 112Malware
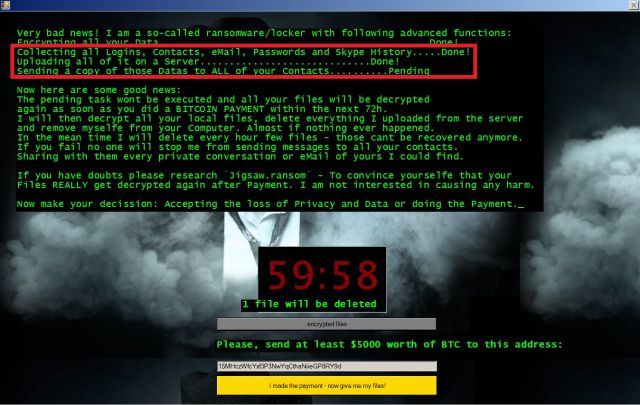
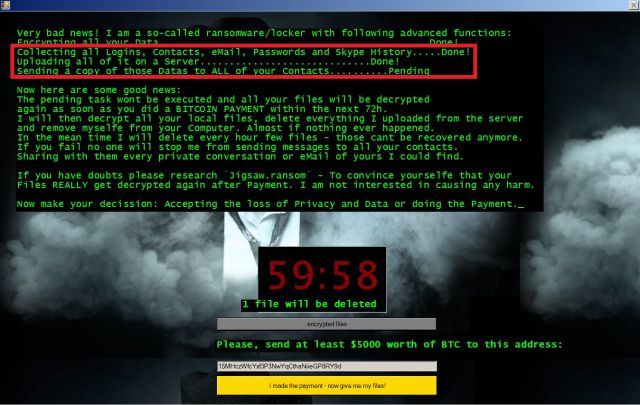
112MalwareJigsaw Ransomware Defeated Again, Free Decrypter Available
Decrypter works with older Jigsaw versions as well. Security researchers from Check Point announced over the weekend that they identified a way to...
-

 222Malware
222MalwareNew Alfa, or Alpha, Ransomware from the same devs as Cerber
Security researcher BloodDolly recently discovered a new file encrypter called Alfa Ransomware, or Alpha Ransomware, which is from the developers of Cerber....
-

 208Malware
208MalwareAndroid Nougat prevents ransomware from resetting device passwords
The upcoming version of Android introduces a new condition so the “resetPassword” API cannot be used to reset a device’s password. The...
-
 190Malware
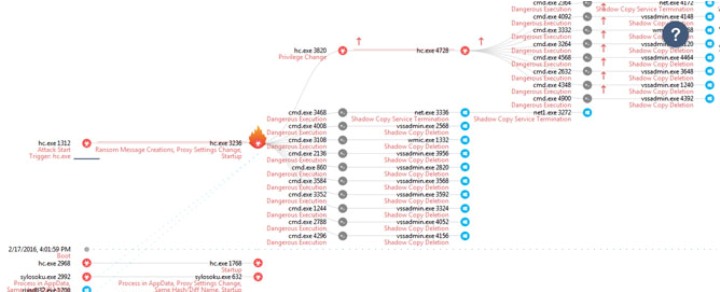
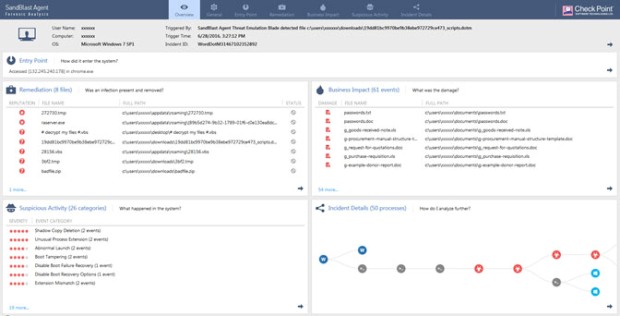
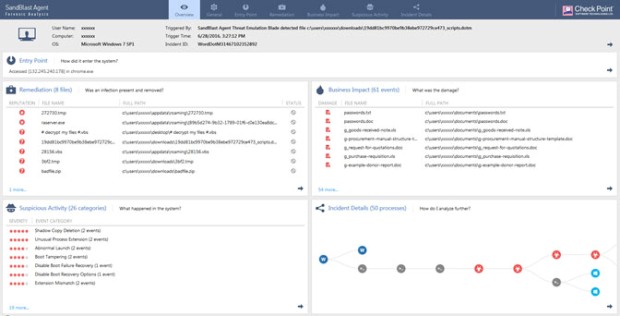
190MalwareForensic Files: Cerber Ransomware Distribution using Office DOTM files
The start of a series This blog entry is the first in a new series featuring reports from Check Point SandBlast Agent...
-
 128Malware
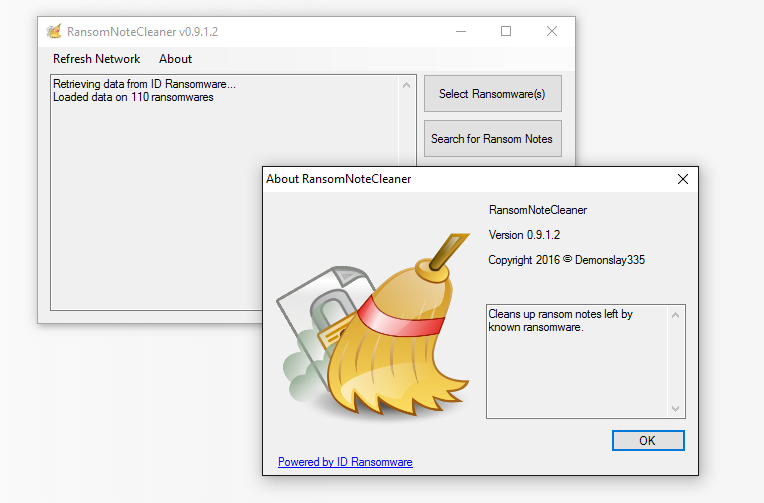
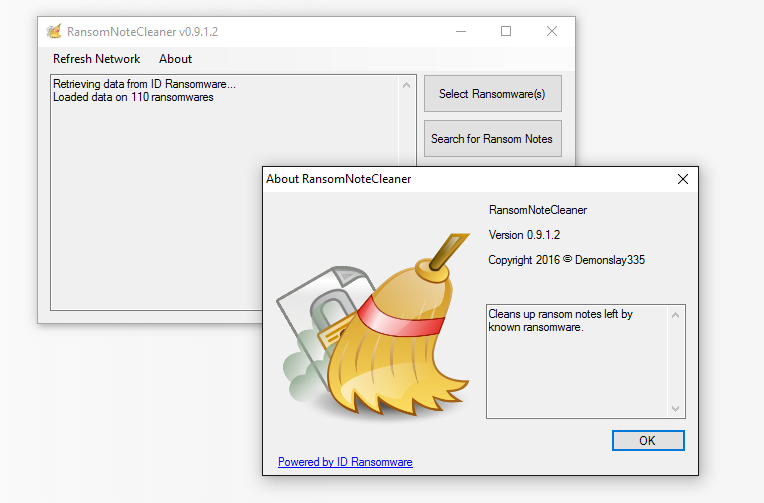
128MalwareRansom Note Cleaner Removes Ransomware Junk From Your PC
RansomNoteCleaner Windows app cleans up the ransom note spam left behind after removing a ransomware infection. Security researcher Michael Gillespie, one of...
-

 83Incidents
83IncidentsKlepto Zepto could steal millions in looming ransomware wave
Talos have observed a large uptick in the Zepto ransomware and have identified a method of distribution for the Zepto ransomware, Spam...
-
 327Hacked
327HackedMicrosoft Office 365 Hit With Massive “Cerber Ransomware” Attack
Short Bytes: The Cerber ransomware is here to lock down your important documents and force you to pay ransom in the form of...
-
 171Malware
171MalwareMeet Jigsaw, the ransomware that taunts victims and offers live support
As data-encrypting malware proliferates, new entrants search for ways to stand out. The crypto ransomware racket is a booming business thatgenerates lots...
-

 156Vulnerabilities
156VulnerabilitiesWidespread Attack on Office 365 Corporate Users with Zero-day Ransomware Virus
Millions of Office 365 business users likely effected. Starting June 22 at 6:44 a.m. UTC, Avanan’s Cloud Security Platform started to detect a...
-

 152Malware
152MalwareDoh! New “Bart” Ransomware from Threat Actors Spreading Dridex and Locky
The actors behind Dridex 220 and Locky Affid=3 have introduced a new ransomware called “Bart”. They are using the RockLoader malware to...
-
 103Malware
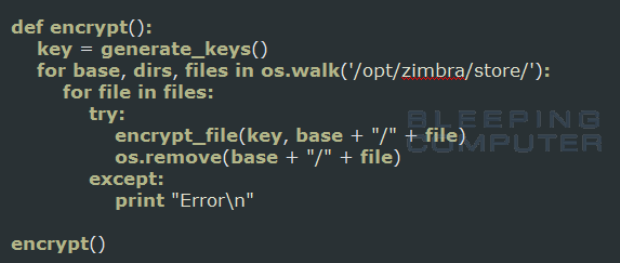
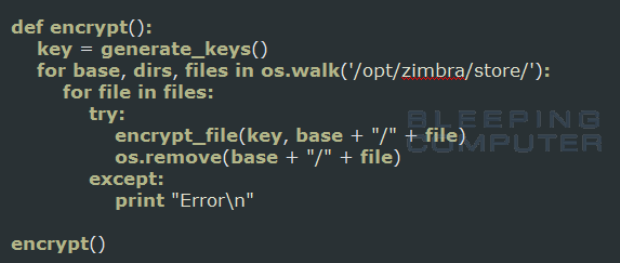
103MalwareZimbra Ransomware written in Python targets Zimbra Mail Store
A new ransomware was discovered that is written in Python and targets theZimbra enterprise collaboration software. Reported by one of our visitors, this...
-
 205Incidents
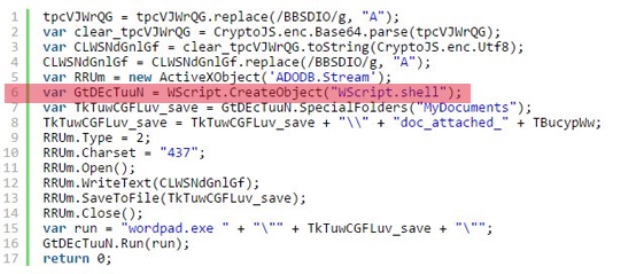
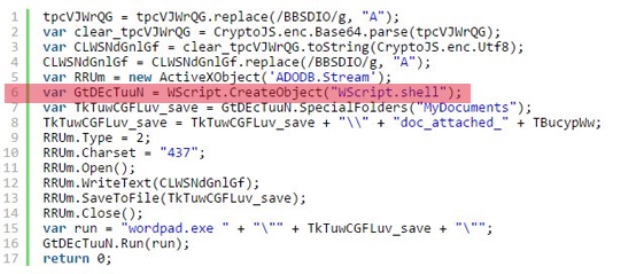
205IncidentsJScript-toting Ransomware Can Steal Your Passwords and Bitcoin Wallets, Too
In an effort to develop a target base and increase the conversion rate of victims, ransomware perpetrators will try to veer away...
-
 102Data Security
102Data SecurityWhy Ransomware Works: Tactics and Routines Beyond Encryption
How do companies regardless of size and industry prepare for ransomware attacks? A recent study revealed that businesses are considering saving up Bitcoins,...






