Search results for "windows malware"
-
 203Incidents
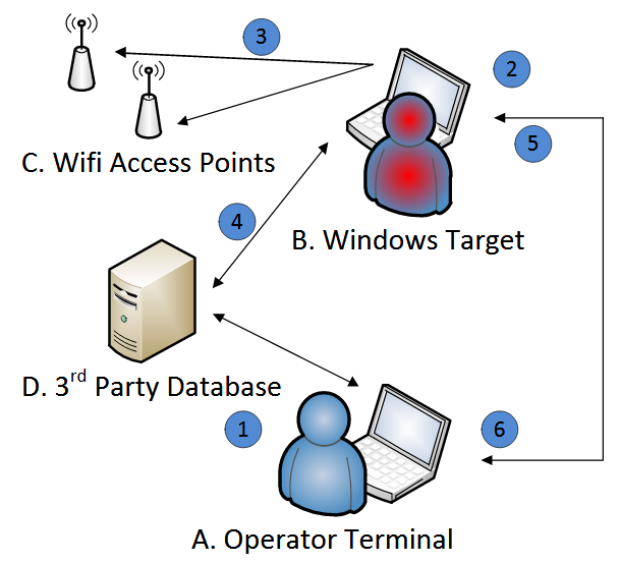
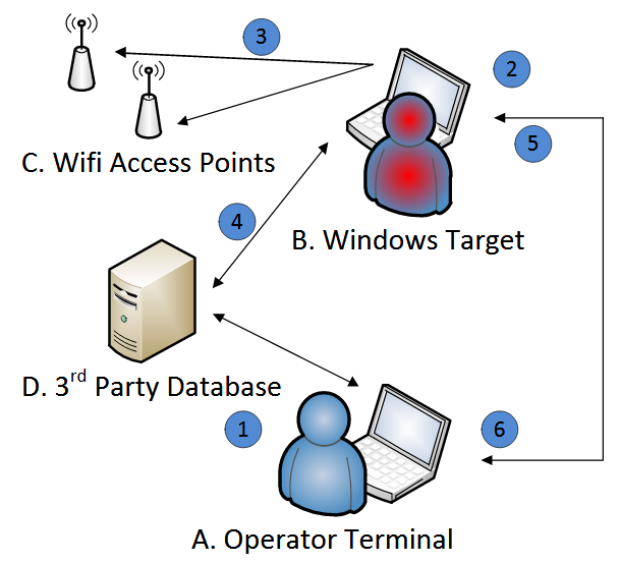
203IncidentsVault 7: CIA Malware for Tracking Windows Devices via WiFi Networks
Today, WikiLeaks has published the documentation manual for an alleged CIA tool that can track users of WiFi-capable Windows devices based on...
-
 130Malware
130MalwareNSA Malware Used to Infect Windows PCs with Cryptocurrency Miner
Malware authors are using an NSA hacking tool to infect Windows computers with a new cryptocurrency miner. Detected under the generic name...
-

 327News
327NewsHackers Using Chinese Malware to Rob ATMs Using Outdated Windows XP
As technology progresses, it seems that hackers and hacking methods do too. It wasn’t that long ago when hackers had to steal...
-
 320Geek
320GeekA Malware That can Bypass Windows Firewall Using Intel’s Management Tech
A unique and perhaps a very practical way of injecting malware into an entire network has been discovered in which the hacking...
-
 368Malware
368MalwareNSA Malware “EternalBlue” Successfully Exploit and Port into Microsoft Windows 10
A Malware called “EternalBlue” Vulnerability Successfully port the exploit to Microsoft Windows 10 by the Security Researchers which has been only affected...
-

 298Geek
298Geek‘Fireball’ Malware Infected 250 Million Mac and Windows Devices
Since the spread of WannaCry ransomware attack the cyber security community is doing whatever it takes to identify new threats against unsuspecting users....
-

 309News
309NewsWikileaks reveals pandemic malware for Windows developed by the CIA
In its latest release as part of the Vault 7 series, WikiLeaks has apparently leaked a document which consists information regarding a...
-

 248Hacked
248HackedVault 7: Wikileaks Exposes CIA’s Athena Malware, Hijacks Every Windows Version
On Friday, Wikileaks published a CIA malware project known as Athena. According to the leaked documents, the Athena malware is capable of hijacking all...
-

 116Vulnerabilities
116VulnerabilitiesSnake malware ported from Windows to Mac
Snake, also known as Turla and Uroburos, is backdoor malware that has been around and infecting Windows systems since at least 2008....
-

 174Hacked
174HackedPopular Antivirus Flags Windows As Malware And Facebook As Phishing Site By Mistake
Short Bytes: The users of Webroot antivirus witnessed a strange problem recently when the software started flagging Windows system files as malware....
-

 259Geek
259GeekWebroot Antivirus Marked Facebook as Phishing Site and Windows as Malware
You may remember Google’s Safe Browsing Site Status mistakenly marking Google.com as a potentially dangerous domain to visit or the Google Maps mistakenly labeling...
-
 186Malware
186MalwareWebroot antivirus mistakenly flags Windows as malware
Windows’ system files were flagged as malicious, and Facebook was marked as a phishing site. A malware signature update issued by the...
-
 350Cyber Events
350Cyber EventsFake News Site Targeting Android, Windows Users with Malware Scam
A group of hackers is performing highly sophisticated cyber-attacks against high-profile organizations of Middle East – Cyber security firms Palo Alto Networks...
-

 169Malware
169MalwareWord Document Spreads Macro Malware Targeting Both Windows and macOS
After last month security researchers discovered the first-ever Word document spreading macro malware on macOS, last week, researchers from Fortinet spotted a...
-
 380Data Security
380Data SecuritySomeone from China is Distributing Mirai Malware Through Windows Botnet
Mirai malware was discovered in 2016 when it was used the Internet’s largest DDoS attack on DYN DNS and OVH hostings. A...
-
 72Malware
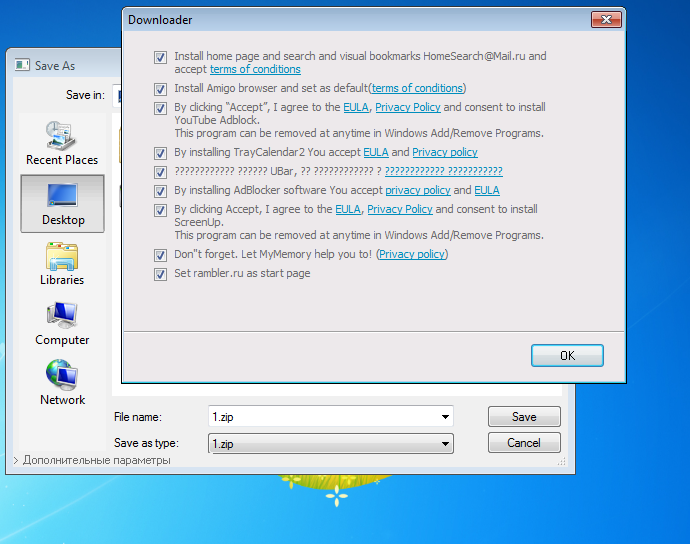
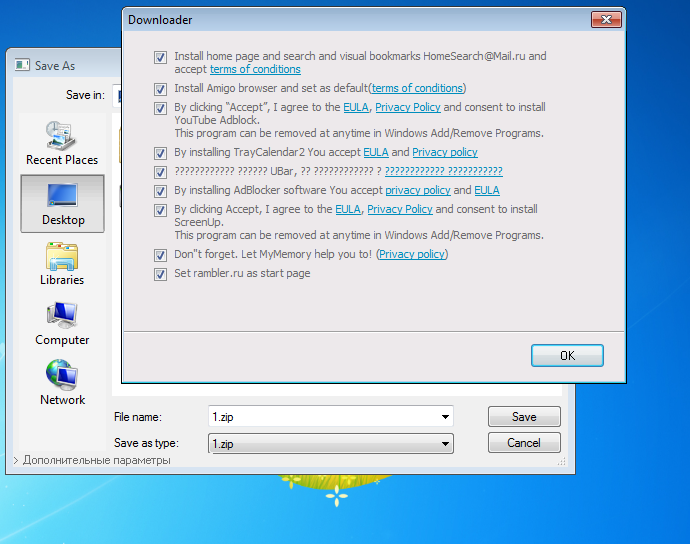
72MalwareMalware Disguises Installer as Windows “Save As” Dialog Box
Malware distributed via affiliate programs and bundled with other applications is using a devious tactic to fool users into installing it on...
-
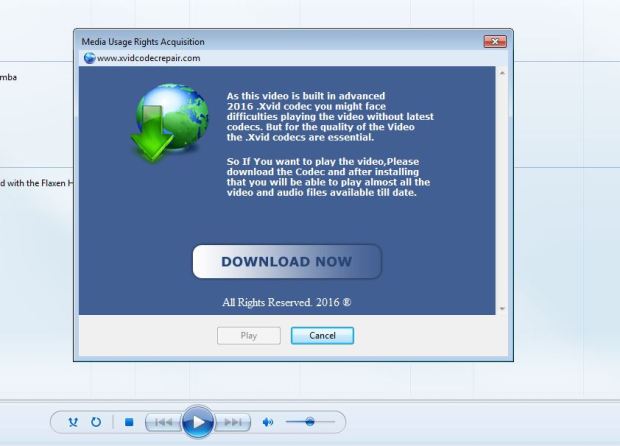
 106Malware
106MalwareWINDOWS MEDIA PLAYER DRM USED FOR MALWARE
Movie and TV watchers who download pirated content have long been warned of the potential for malware that might accompany their chosen...
-

 194Hacked
194HackedMokes: This Single Malware Creates “Backdoor” In Windows, Linux, Mac OS X
Short Bytes: A cross-platform malware family has been reported by a security researcher from Kaspersky Lab. The malware can create a backdoor...
-

 135Data Security
135Data SecurityMalware Finds New Trick to Hide Rogue DNS Settings on Windows
DNS Unlocker finds a way to hide hijacked DNS servers from human operators via one “special” character. A Potentially Unwanted Application (PUA) named...
-

 233Geek
233GeekWindows ‘God Mode’ Feature Exploited by New Malware to Avoid Identification
Researchers have identified a new malware taking advantage of Windows God Mode and infecting users. Malware in a Window OS is not...
-
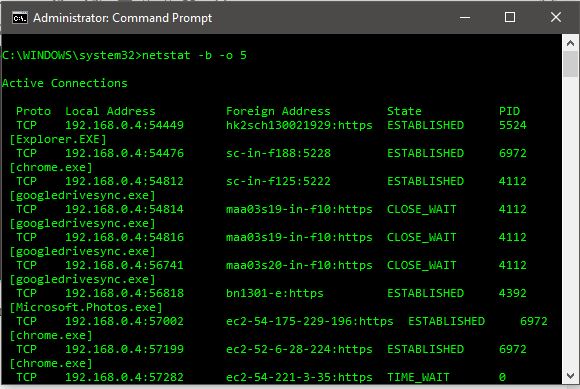
 438How To
438How ToHow To Find And Kill A Remote Connecting Malware On Windows 10
Short Bytes: Here are the simple and easy steps on how to find, kill and delete a remote connecting malware using command prompt...






