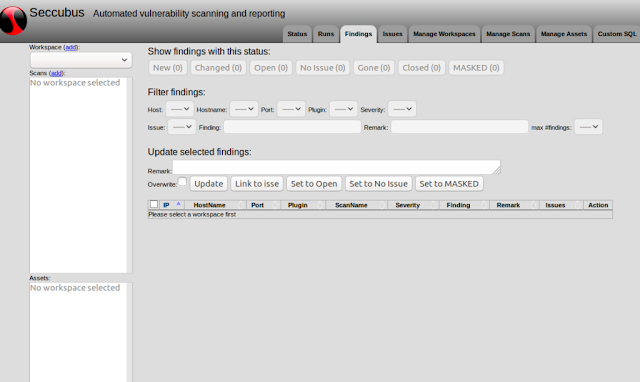
Seccubus automates regular vulnerability scans with various tools and aids security people in the fast analysis of its output, both on the first scan and on repeated scans.
On repeated scan delta reporting ensures that findings only need to be judged when they first appear in the scan results or when their output changes.
Seccubus 2.x is the only actively developed and maintained branch and all support for Seccubus V1 has officially been dropped.
Seccubus V2 works with the following scanners:
- Nessus
- OpenVAS
- Skipfish
- Medusa (local and remote)
- Nikto (local and remote)
- NMap (local and remote)
- OWASP-ZAP (local and remote)
- SSLyze
- Medusa
- Qualys SSL labs
- testssl.sh (local and remote)
For more information visit [www.seccubus.com]
BoomER – Framework for Exploiting Local Vulnerabilities
Docker
Available images.
Information about the docker containers is in [README-docker.md]
Vault Scanner – Swiss Army Knife for Hackers
Default password, changinge it!!!!!
After installation the default username and paswword for seccubus is:
admin / GiveMeVulns!
It is highly recommended you change this after installation.
/bin/seccubus_passwd -u admin