A new Email campaign spotted by Trustwave spreading HERMES Ransomware through password protected word document to encrypt the system files and lock the victim’s computer. Hermes Ransomware distributed in wild nowadays with newly updated features and targets various countries.
The attachment named “Invoice.doc” contains the password protected macro if the user has security setting is Low then the macro will be launched automatically.

Once the macro is triggered it downloads a file from the Command and control server[hxxp://209[.]141[.]59[.]124/azo.exe] and the downloaded file save to temp folder and executed. The [azo.exe] downloads the final payload which is the HERMES 2.1 Ransomware.

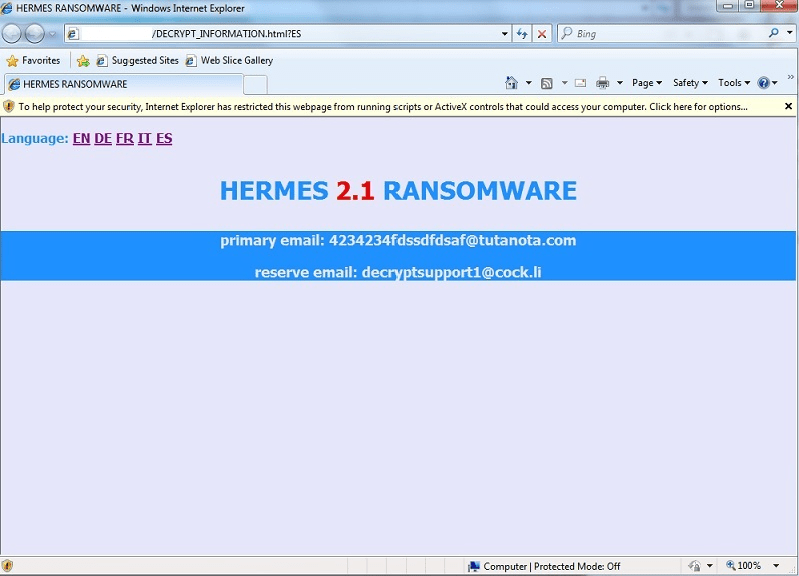
Hermes doesn’t append its own file extension as like any other ransomware it used symmetric algorithm AES to encrypt files and RSA to protect AES key. Once the infection completed it launches DECRYPT_INFORMATION.html which shows the ransom note.
Ransom note indicates that the victim’s files are encrypted using an RSA2048 algorithm and asks victim’s to pay through Bitcoin or other cryptocurrencies. Also, attackers added “you can decrypt one file for free” to make victims believe they can decrypt the files.
Trustwave also spotted the same email sample contains attachment as XPS file “invoice.xps” and it has FixedPage.NavigateUri property which directs users to “hxxp://rainbowrealty[.]com/ads/herewego.html” when it was clicked. The page appears to be removed now and it doesn’t exist.
Unfortunately, the decrypter tool is available only for variants of Hermes 1.0 and it is not available for Hermes 2.x variants. The best options are to restore data from the backups.
Also Read
Cyber Criminals Launch Hermes Ransomware Via Password Protected Word Documents