A new ransomware group known as ‘Rhysida’ has been operating since May 2023, posing a huge danger to the healthcare industry.
Rhysida ransomware gang has been connected to several significant attacks, including an assault on the Chilean Army.
Recently, the organization was also implicated in an attack on Prospect Medical Holdings that had an impact on 166 clinics and 17 hospitals around the country.
“This threat is delivered through a variety of mechanisms which can include phishing and being dropped as secondary payloads from command and control (C2) frameworks like Cobalt Strike”, Cisco Talos.
“These frameworks are commonly delivered as part of traditional commodity malware, so infection chains can vary widely”.
Unique Techniques, Tactics, and Tools (TTPs) of Ransomware
Check Point Incident Response Team (CPIRT) report says this ransomware was found to have a lot in common with Vice Society’s TTPs, another ransomware group. Since 2021, Vice Society has been one of the most active and aggressive ransomware gangs, primarily focusing on the healthcare and education industries.
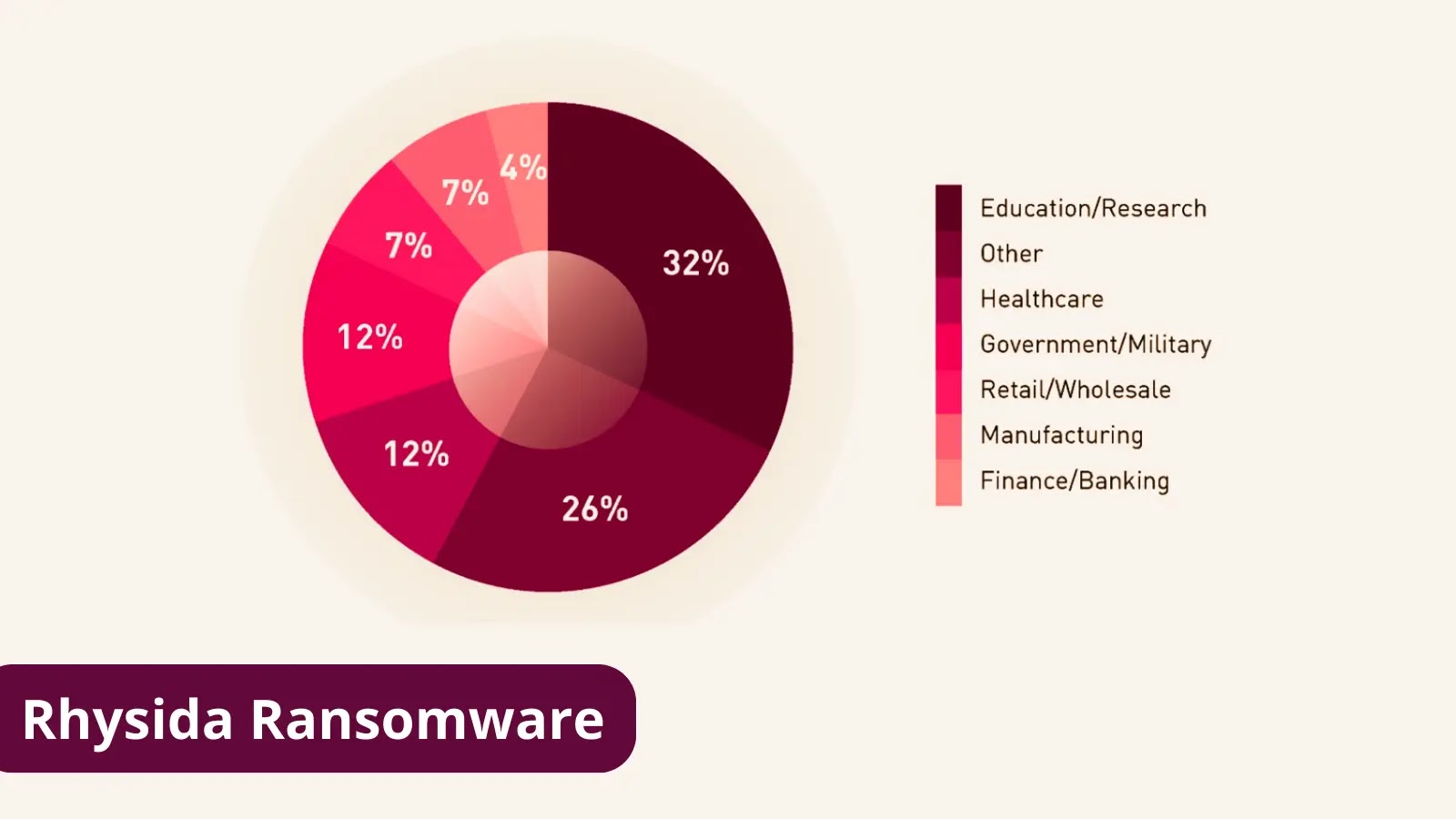
The two groups focused on the education and healthcare industries, which are distinctive in the ransomware ecosystem.
The research focused on the TTPs that led to its deployment, specifically Lateral Movement, Credential Access, Defence Evasion, Command and Control, and Impact.
To conduct lateral movement, the attackers employed a range of techniques, including:
- Remote Desktop Protocol (RDP) – Throughout the intrusion, the threat actor initiated RDP connections and took further steps to erase related logs and registry items to harden detection and analysis attempts (as mentioned in the Defence Evasion section).
- Remote PowerShell Sessions (WinRM) – The threat actor was spotted starting remote PowerShell connections to systems inside the environment while connecting remotely through RDP.
- PsExec – The ransomware payload was distributed from a server within the environment using PsExec.
Notably, for accessing credentials, the threat actor utilized ntdsutil.exe to build a backup of NTDS.dit under the temp_l0gs folder.
Researchers say this path was used by the actor several times. In addition, the threat actor identified Domain Administrator accounts and attempted to log in using some of them.
For persistence, threat actors have used a variety of backdoors and technologies, including SystemBC and AnyDesk.
Threat actors deleted logs and forensic artifacts regularly, including deleting the history of recently used files and directories, the list of recently executed programs, the recent path history in File Explorer, the PowerShell console history file, and all files and folders in the current user’s temporary folder.
Wrap Up
There has been significant development in the ransomware and extortion market, which might be attributed to the number of leaked builders and source codes associated with numerous ransomware cartels.