Search results for "AWS"
-
 230Articles
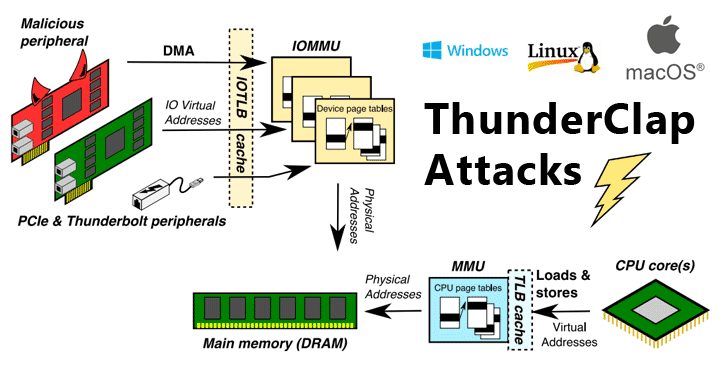
230ArticlesNew Flaws Re-Enable DMA Attacks On Wide Range of Modern Computers
Security researchers have discovered a new class of security vulnerabilities that impacts all major operating systems, including Microsoft Windows, Apple macOS, Linux,...
-
 173Articles
173ArticlesSevere Flaws in SHAREit Android App Let Hackers Steal Your Files
Security researchers have discovered two high-severity vulnerabilities in the SHAREit Android app that could allow attackers to bypass device authentication mechanism and...
-

 338Data Security
338Data SecurityCellular networks flaws expose 4G & 5G devices to IMSI capturing attacks
A team of researchers has disclosed their findings at the NDSS (Network and Distributed System Security) symposium 2019 held in San Diego,...
-
 242News
242NewsGoogle Says Spectre Flaws Cannot Be Defeated By Software Alone
Spectre and Meltdown attacks were initially discovered in early 2018. Following which, many security researchers have tried and tested different methods to...
-
 260Data Security
260Data SecuritySevere flaws in password managers let hackers extract clear-text passwords
Password Managers aren’t as secure as you might assume – Security researchers claim that hackers can steal master passwords in PC memory....
-

 176News
176NewsFacebook Is Incapable Of Governing Itself; Strict Laws Underway: UK Govt
After 18 months of an investigation against Facebook, probing the social media platform’s privacy practice, the UK government has published a detailed...
-

 228Articles
228ArticlesMicrosoft Patch Tuesday — February 2019 Update Fixes 77 Flaws
Microsoft has issued its second Patch Tuesday for this year to address a total of 77 CVE-listed security vulnerabilities in its Windows...
-
 345Geek
345GeekFlaws in RDP protocols leaving machines prone to remote code execution
Major Security Flaws Identified in RDP Protocols making Machines Prone to Remote Code Execution and Reverse RDP Attacks. Check Point researchers have...
-
 204Articles
204ArticlesFlaws in Popular RDP Clients Allow Malicious Servers to Reverse Hack PCs
You’ve always been warned not to share remote access to your computer with any untrusted people for many reasons—it’s basic cyber security...
-

 254Cyber Crime
254Cyber CrimeEthical hacker may get 8 years in prison for reporting flaws in Magyar Telekom
Hungary’s Prosecution Service has accused an ethical hacker and computer specialist of infiltrating the Magyar Telekom database. The office found him involved...
-

 225News
225NewsApple Faces Lawsuit Over The FaceTime Eavesdropping Bug
Just yesterday, we reported the massive Facetime bug in iOS 12.1 devices that allowed people to eavesdrop a conversation, even before the recipient picks up a call....
-
 167Articles
167Articles5 Popular Web Hosting Services Found Vulnerable to Multiple Flaws
A security researcher has discovered multiple one-click client-side vulnerabilities in the some of the world’s most popular and widely-used web hosting companies...
-
 215Articles
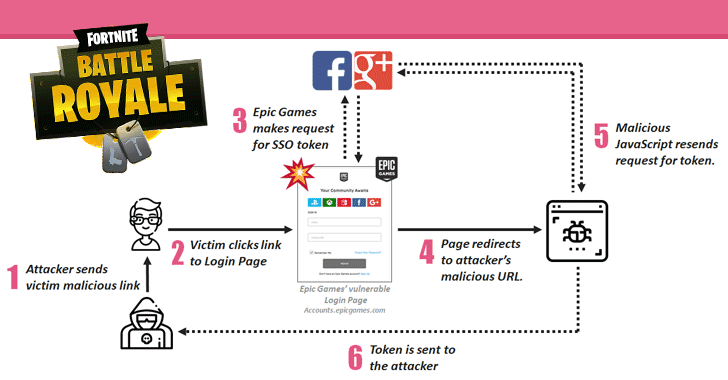
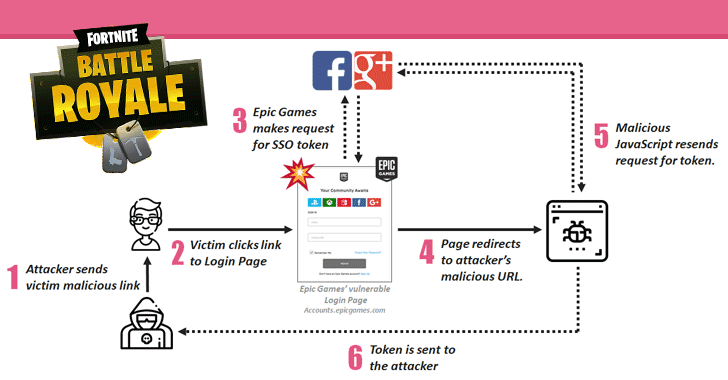
215ArticlesFortnite Flaws Allowed Hackers to Takeover Gamers’ Accounts
Check Point researchers have discovered multiple security vulnerabilities in Fortnite, a massively popular online battle game, one of which could have allowed...
-
 153Articles
153Articles36-Year-Old SCP Clients’ Implementation Flaws Discovered
A set of 36-year-old vulnerabilities has been uncovered in the Secure Copy Protocol (SCP) implementation of many client applications that can be...
-
 167Articles
167ArticlesNew Systemd Privilege Escalation Flaws Affect Most Linux Distributions
Security researchers have discovered three vulnerabilities in Systemd, a popular init system and service manager for most Linux operating systems, that could...
-
 188Articles
188ArticlesAdobe Issues Emergency Patches for Two Critical Flaws in Acrobat and Reader
I hope you had biggest, happiest and craziest New Year celebration, but now it’s time to come back at work and immediately...
-

 246News
246NewsIndia Could Change IT Laws To Shutdown Apps And Sites That Spread Fake News
The Indian Government has suggested that amendments to the Information Technology (IT) Act should be made to curb the spreading of fake...
-
 193Articles
193ArticlesAdobe’s Year-End Update Patches 87 Flaws in Acrobat Software
Adobe is closing out this year with its December Patch Tuesday update to address a massive number of security vulnerabilities for just...
-
 156Articles
156Articles3 New Code Execution Flaws Discovered in Atlantis Word Processor
This is why you should always think twice before opening innocent looking email attachments, especially word and pdf files. Cybersecurity researchers at...
-
 243Exploitation Tools
243Exploitation ToolsPacu – The AWS Exploitation Framework, Designed For Testing The Security Of Amazon Web Services Environments
Pacu is an open source AWS exploitation framework, designed for offensive security testing against cloud environments. Created and maintained by Rhino Security...
-

 275News
275NewsUsed Data Storage Devices Have Security Flaws
According to Researchers at Radboud University in the Netherlands ‘data storage devices with self-encrypting drives don’t provide the expected level of data...






