Search results for "AWS"
-

 213News
213NewsCathay Pacific Breach Exposes Gap in Hong Kong Laws: Experts
Experts point out that the recent data breach that had impacted Cathay Pacific exposes a gap in Hong Kong laws. The Hong...
-

 160Articles
160ArticlesCritical Flaws Found in Amazon FreeRTOS IoT Operating System
A security researcher has discovered several critical vulnerabilities in one of the most popular embedded real-time operating systems—called FreeRTOS—and its other variants,...
-
 238Malware Analysis
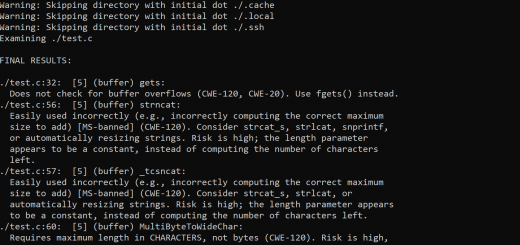
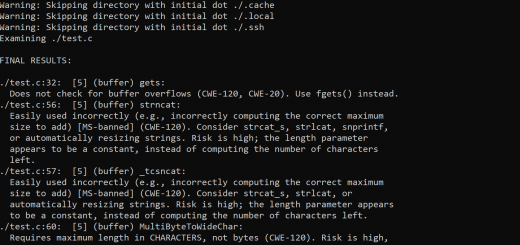
238Malware AnalysisFlawfinder v2.0.7 – Searches through C/C++ source code looking for potential security flaws
To run flawfinder, simply give flawfinder a list of directories or files. For each directory given, all files that have C/C++ filename...
-

 295Cloud Computing
295Cloud Computingsandcastle: AWS S3 bucket enumeration
A Python script for AWS S3 bucket enumeration. Inspired by a conversation with Instacart’s @nickelser on HackerOne, I’ve optimized and published Sandcastle – a...
-

 161Data Security
161Data SecurityEstonia sues Gemalto for €152M for the flaws in the identification cards issued by the company
The lawsuit is due to the flaws in the identification cards issued by the company The Estonian authorities have taken legal action against the security company Gemalto, filing a lawsuit for €152M after security failures in citizen identification cards issued...
-

 391Geek
391GeekPakistani hacker reports address bar spoofing flaws in Edge & Safari browser
Rafay Baloch has reported Vulnerability in Edge and Safari Browsers that Allows Address Bar Exploitation. Nowadays the phishing attacks have become increasingly...
-

 338News
338NewsGoogle Faces Lawsuit, Accused Of Tracking Locations
A lawsuit has been filed against tech giant Google, accusing Google of tracking locations even when the “Location History” setting is turned...
-

 355Hacked
355Hacked25 Smartphone Models Found Shipping With Severe Firmware Flaws: Defcon 2018
This year’s Defcon witnessed many interesting events, including the hacking of voting machines by 11-year-olds and macOS’s vulnerabilities to grant permissions to...
-

 359Data Security
359Data SecurityNew WhatsApp flaws let attackers hack chats to spread fake news
Spreading fake news through WhatsApp was never so easy before. According to the latest research from Check Point security firm, WhatsApp users...
-

 277Data Security
277Data SecurityMultiple flaws found in Samsung SmartThings Hub
Enterprise network security researchers found dozens of flaws that could expose smart home devices to attacks Enterprise network security experts discovered 20...
-
 279System Administration
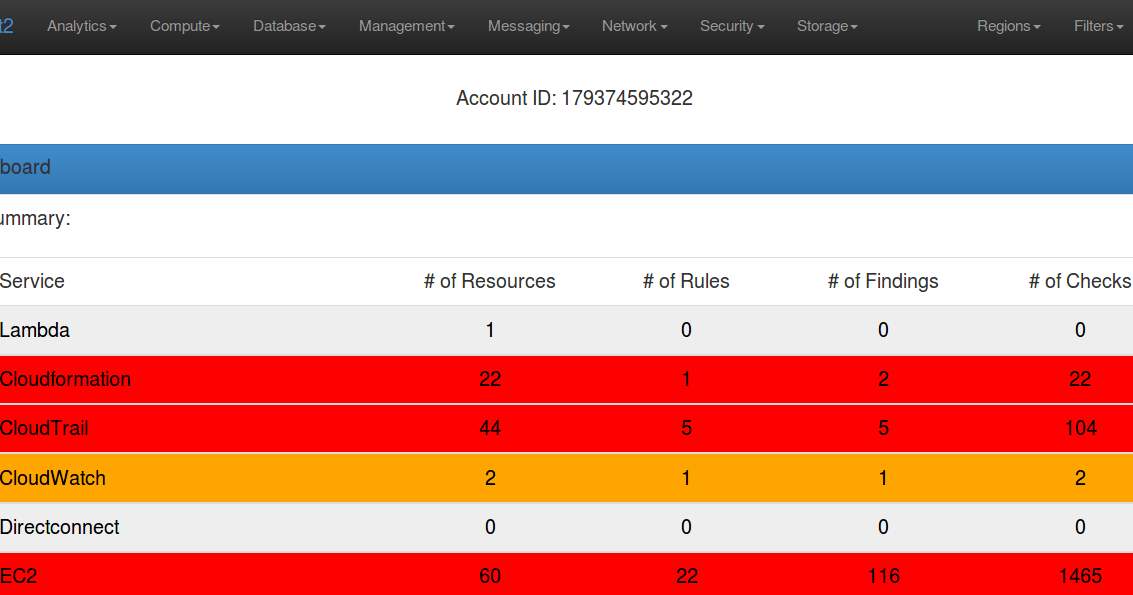
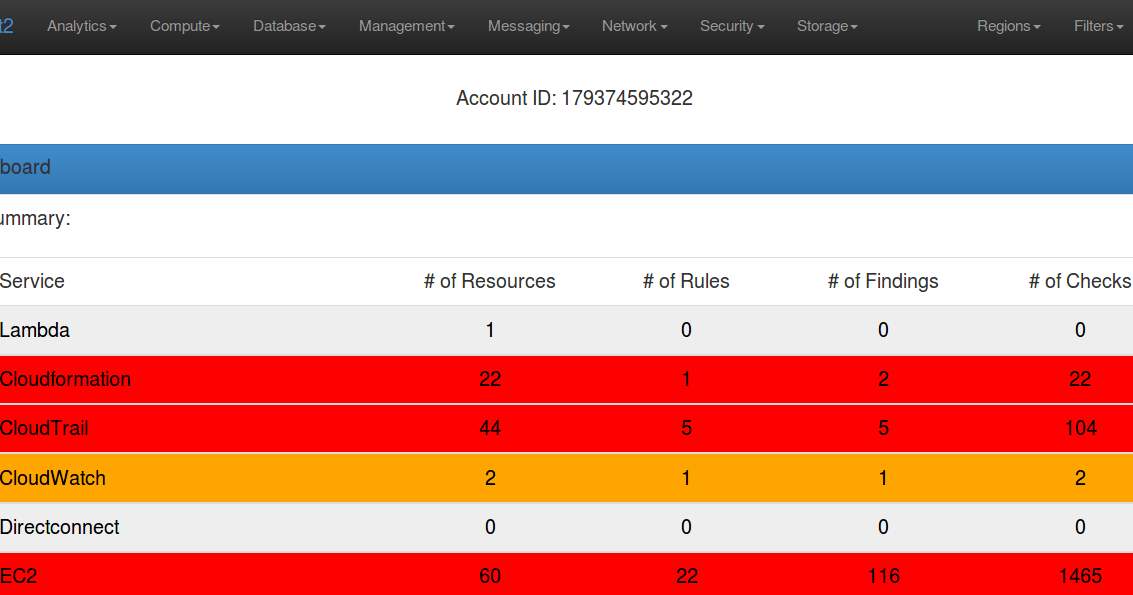
279System AdministrationScout2 – Security Auditing Tool For AWS Environments
Scout2 is a security tool that lets AWS administrators assess their environment’s security posture. Using the AWS API, Scout2 gathers configuration data...
-

 279Hacked
279HackedIntel Patches New ME Flaws That Could Let Hackers Run Arbitrary Code: Check For Patches
Another day, another security fix released by Intel. In a blog post, Positive Technologies has detailed four different vulnerabilities found in the...
-
 209Hacked
209HackedCritical PGP Flaws Can Expose Encrypted Emails In “Plaintext” — Disable It Right Now
Email users who use PGP (based on OpenPGP) and S/MIME to encrypt and decrypt their communications are at “immediate risk.” The reason...
-

 211Data Security
211Data SecurityResearchers find critical security flaws in popular car models
Modern-day vehicles have become overly digitized for the sake of offering advanced technicality to drivers. However, being digital cannot ensure optimal security...
-

 231Geek
231GeekIntel removes remote keyboard app for Android rather than fixing its flaws
Critical Flaws in Intel’s Remote Keyboard App for Android Lead to its Discontinuation. As is the norm with security researchers, when bugs...
-

 200Hacked
200HackedAMD Processors Flaws: Firmware Patches Coming Soon, Won’t Affect Performance
Last week, the Isreal-based security company CTS labs was trending in the news for disclosing 13 critical vulnerabilities in AMD’s Ryzen and...
-
 316Geek
316GeekMicrosoft bug bounty program: $250k for reporting Meltdown & Spectre type flaws
The bug bounty program will remain open until December 31st, 2018. Recently, the identification of serious CPU flaws called Spectre and Meltdown shook...
-

 337Data Security
337Data SecurityHackers can Send Fake Emergency Alerts by Exploiting 4G LTE Protocol Flaws
Researchers at the Purdue University and the University of Iowa, USA, have managed to break the key 4G LTE protocols for generation...
-

 224Incidents
224IncidentsLTE security flaws could be used for spying, spreading chaos
A flight of new research papers show 4G LTE networks can be exploited for all sorts of badness. There have been lots...
-

 301Incidents
301IncidentsAWS Bucket Exposes 50.4 GB of Financial Giant’s Data
Another AWS Bucket exposed to the public. This time the AWS Bucket belonged to Birst. A cyber security team have discovered a...
-
 323Data Security
323Data Security139 Malware Samples Identified that Exploit Meltdown & Spectre Flaws
Hackers could be close to developing malware that exploits flaws, suggests a German cybersecurity firm. AV-Test, an independent German antivirus testing and...






