Search results for "Amazon"
-
Information Gathering
Bucket Stream – Find interesting Amazon S3 Buckets by watching certificate transparency logs
Some quick tips if you use S3 buckets: Randomise your bucket names! There is no need to use company-backup.s3.amazonaws.com. Set appropriate permissions...
-

 302Incidents
302IncidentsPentagon contractor leaves social media spy archive wide open on Amazon
Trove included more than 1.8 billion posts spanning eight years, many from US people. A Pentagon contractor left a vast archive of...
-

 404News
404NewsMisconfigured Amazon S3 Buckets Exposed US Military’s Social Media Spying Campaign
UpGuard’s security researcher Chris Vickery has discovered three misconfigured AWS S3 buckets that are available for public access on the internet. The...
-

 219Geek
219GeekResearchers demonstrate Amazon Key system can be hacked
Rhino Security Labs’ researchers have discovered a vulnerability in Amazon’s Key delivery service and Cloud Cam security camera. This vulnerability allows an...
-

 158Articles
158ArticlesThird Party People can Disable your Amazon Key’s Camera allowing couriers to reenter into your home
Now security researchers have discovered that the camera can be silenced and frozen from a script run from any machine within Wi-Fi...
-

 311Data Breach
311Data BreachABC Company Massive Data Leaked online from Amazon S3 Bucket
The Australian Broadcasting Corporation (ABC) Sensitive data leaked online from AWS S3 repositories that included usernames, email addresses, password hashes, and other user...
-

 276Vulnerabilities
276VulnerabilitiesAmazon Echo and Google Home were vulnerable to Bluetooth exploit
Don’t worry, these vulnerabilities have already been patched out. Back in September, Bluetooth-connected device owners got a little scare when security firm...
-

 257Articles
257ArticlesBluetooth Hack Affects 20 Million Amazon Echo and Google Home Devices
A series of recently disclosed critical Bluetooth flaws that affect billions of Android, iOS, Windows and Linux devices have now been discovered...
-

 381Geek
381GeekAmazon Echo and Google Home Devices Vulnerable to BlueBorne Attack
In September 2017, the IT security researchers at Armis found eight zero-day vulnerabilities in Bluetooth protocol. Dubbed BlueBorne by researchers, these vulnerabilities affected...
-

 251How To
251How ToWhat is Echo And Alexa? How To Set Up Amazon Echo And Use It?
What is Amazon Echo? Amazon Echo is a popular hands-free smart speaker that you can control using your voice. As it’s “smart,”...
-
 172Vulnerabilities
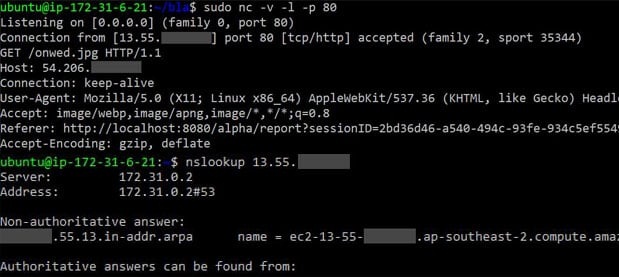
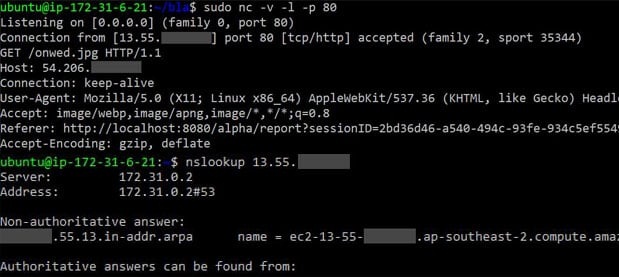
172VulnerabilitiesStealing Amazon EC2 Keys via an XSS Vulnerability
On a recent engagement, our testers were faced with a single page web application which was used to generate PDF documents. This...
-

 97Vulnerabilities
97VulnerabilitiesAmazon-owned grocery chain Whole Foods Market suffered payment card breach
News of the day is that another big company suffered a security breach, the victim is the Amazon-owned grocery chain Whole Foods...
-

 204Geek
204GeekWhich Programming Language Should I Learn To Get A Job At Google, Facebook, or Amazon?
The choice of programming language acts as a big factor for a novice in the world of programming. If one stumbles upon...
-

 339News
339NewsMassive Viacom Data Exposed Through Amazon Web Services
Database on Amazon Web Services Containing Sensitive Data of Viacom Is Publicly Available. Amazon Web Services S3 is in the news for...
-

 356Data Security
356Data SecurityAmazon Echo Can Be Hacked to act as a Surveillance device
Taking over an IoT (Internet of Things) device is nothing new for hackers, but since users have become increasingly dependent on smart devices,...
-

 195Data Security
195Data SecurityIs Amazon working on a new messaging app called Anytime?
Messaging apps today are one of the most popular ways consumers communicate today, not just with each other but, increasingly, with businesses...
-

 250News
250NewsUS Security Contractors Left Confidential Files On Amazon Servers Without Password
According to the new report, the US news agency for the US Security Contractors without a password on the file sensitive to...
-
 374News
374NewsSecret Pentagon Files Left Unprotected on the Amazon Server
Accidents happen to everyone but according to a recent report, this one is a pretty big one. Apparently, some of the confidential...
-

 297News
297NewsThird-Party Sellers From Amazon Hacked by Cyber Criminals
A new wave of cybercrime was reported on the biggest online marketplace, Amazon. Hackers have started using third-party sellers to scam buyers...
-

 154Vulnerabilities
154VulnerabilitiesTwitter app spams Fappening bait and Amazon surveys
With news of another so-called Fappening (nude photos of celebrities distributed without permission) doing the rounds, it was inevitable that scammers would look...
-

 380News
380NewsHow An easy Command Typo Took Down Amazon S3 Cloud & Huge Chew of the Internet
The predominant net outage across America earlier this week turned into no longer due to any virus or malware or country-sponsored cyber...






