Search results for "Analysis"
-
 208Hacking Tools
208Hacking ToolsA2SV – SSL Vulnerability Analysis Tool
A2SV is an open source tool used for scanning SSL vulnerabilities in web applications. A2SV performs vulnerability scanning for CCS injection, Heartbleed,...
-
 301Incident Response
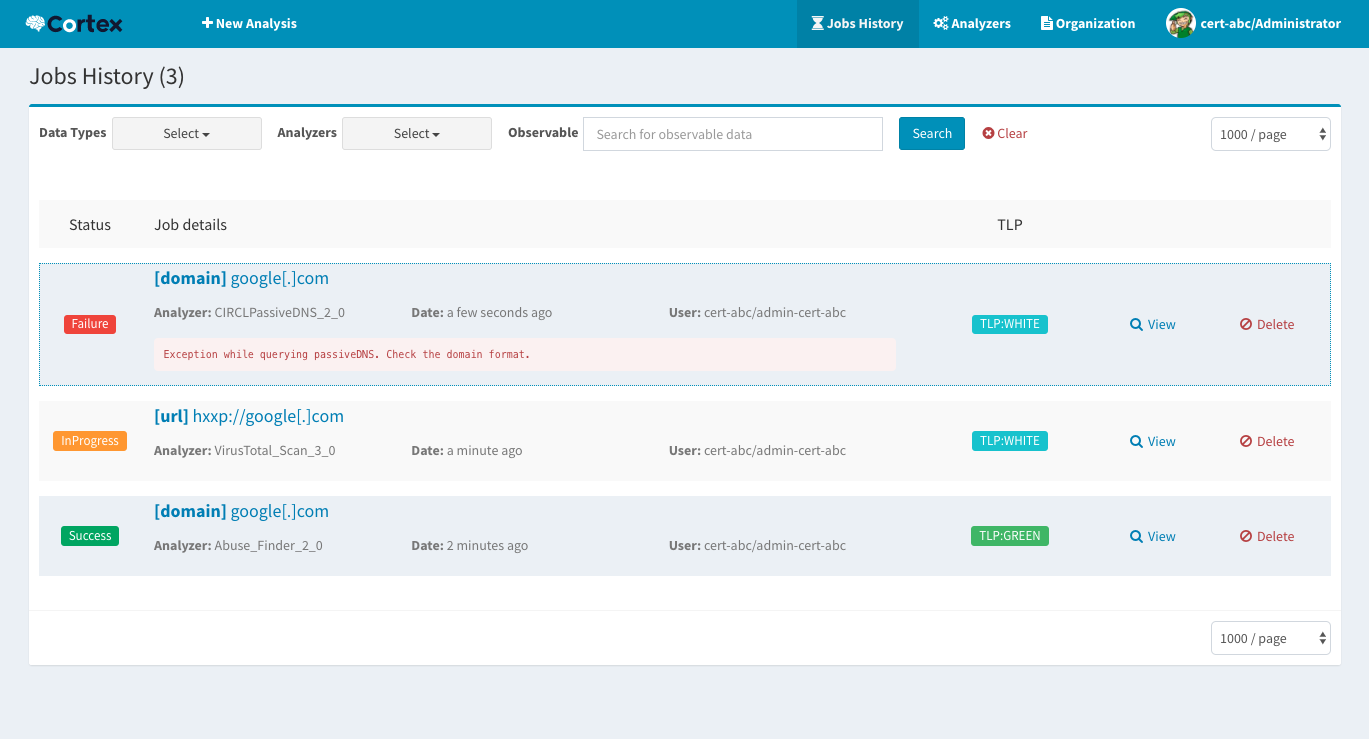
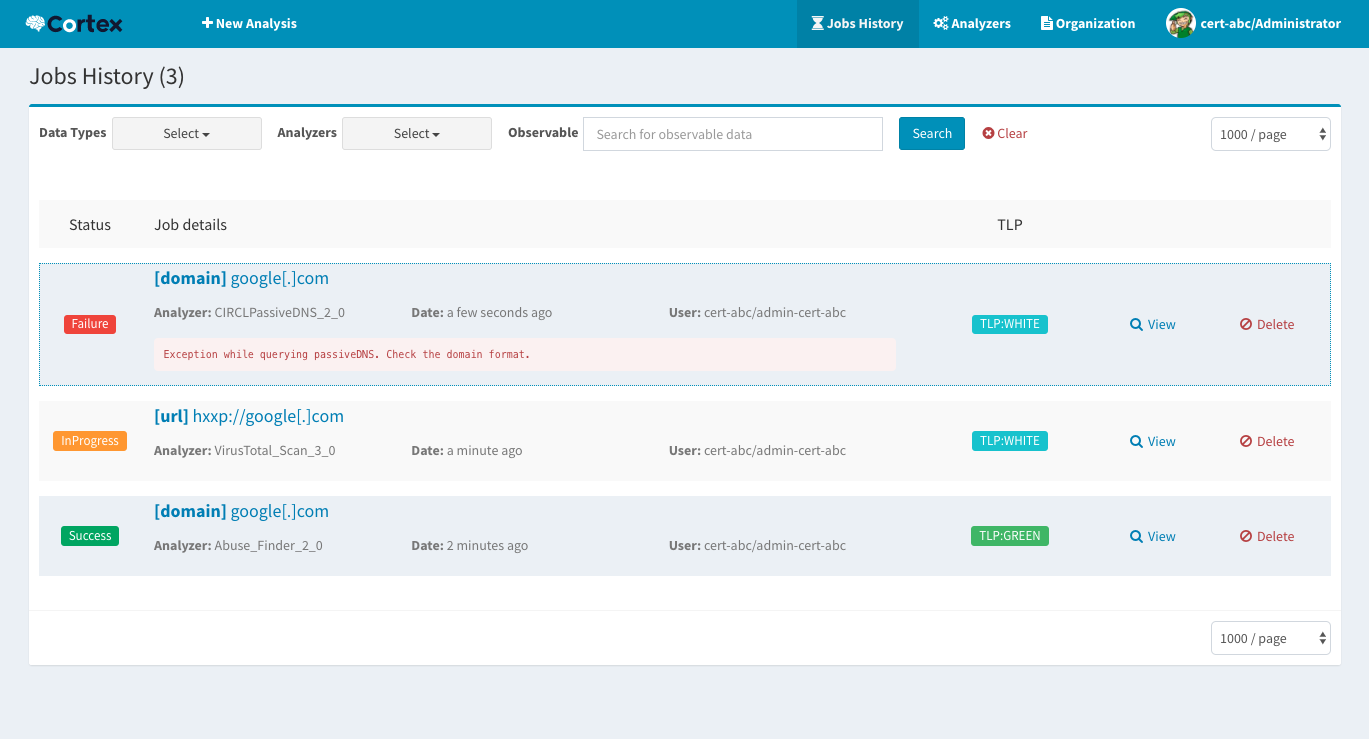
301Incident ResponseCortex 2.1.0 released: Powerful Observable Analysis Engine
Cortex tries to solve a common problem frequently encountered by SOCs, CSIRTs and security researchers in the course of threat intelligence, digital forensics,...
-

 153Data Security
153Data SecurityThe role of human factor in the analysis of computer risks
Digital security concept The human element has to be considered when evaluating this type of risk in an organization According to a...
-
 330Cryptography
330CryptographyCyberChef – A web App For Encryption, Encoding, Compression & Data Analysis
CyberChef is a simple, intuitive web app for carrying out all manner of “cyber” operations within a web browser. These operations include...
-

 265Vulnerabilities
265VulnerabilitiesThe changing environment of vulnerability analysis
Cybersecurity reports reveal the most frequently exploited vulnerabilities Shortly after the launch of its second annual report called “Under the Hoodie: Lessons...
-

 271Binary Analysis
271Binary AnalysisManticore – Dynamic Binary Analysis Tool
Manticore is a prototyping tool for dynamic binary analysis, with support for symbolic execution, taint analysis, and binary instrumentation. Manticore comes with...
-

 417Malware
417MalwareSednit update: Analysis of Zebrocy
Zebrocy heavily used by the Sednit group over last two years
-
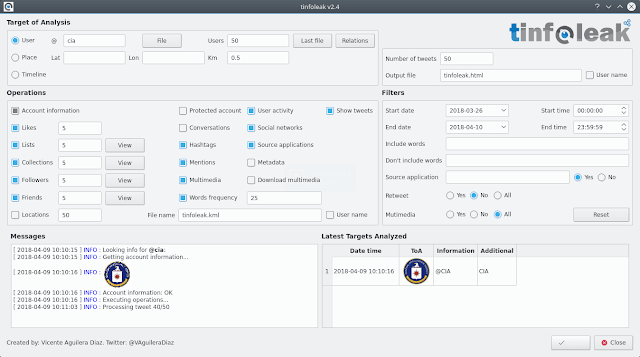
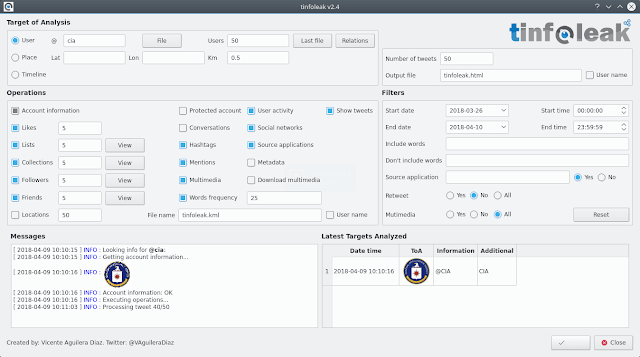 217Information Gathering
217Information GatheringTinfoleak v2.4 – The Most Complete Open-Source Tool For Twitter Intelligence Analysis
The most complete open-source tool for Twitter intelligence analysis Introduction tinfoleak is an open-source tool within the OSINT (Open Source Intelligence) and SOCMINT (Social Media Intelligence) disciplines,...
-
 382Computer Forensics
382Computer ForensicsLive Forensics Analysis with Computer Volatile Memory
The field of computer Forensics Analysis involves identifying, extracting, documenting, and preserving information that is stored or transmitted in electronic or magnetic...
-
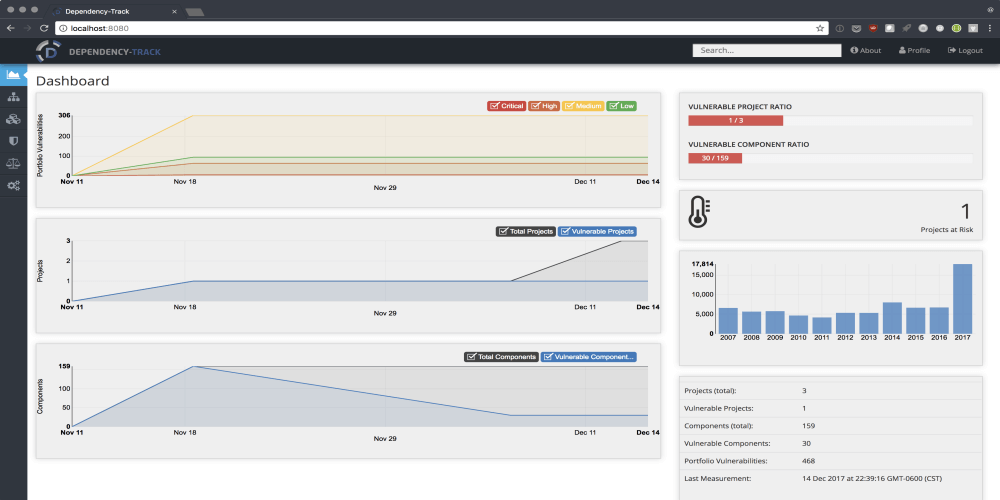
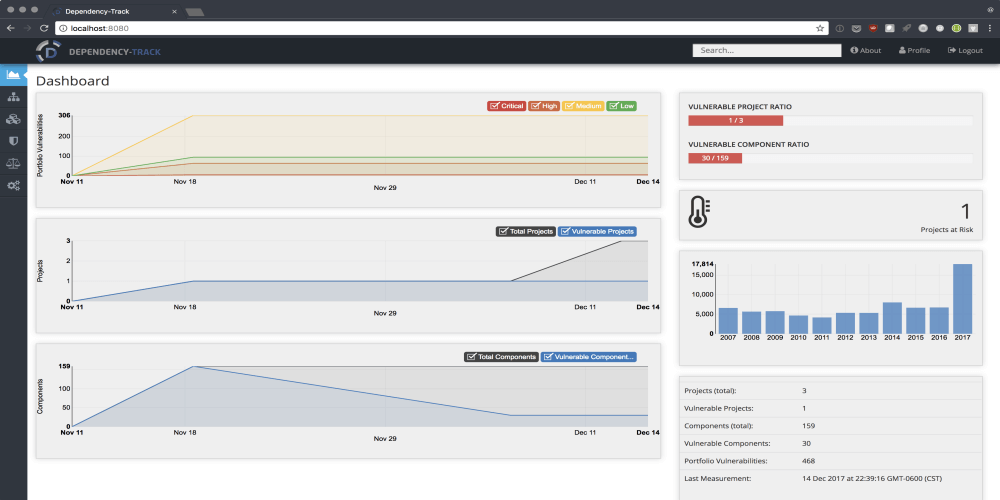 162Vulnerability Analysis
162Vulnerability AnalysisDependency-Track – Intelligent Software Composition Analysis Platform
Modern applications leverage the availability of existing components for use as building blocks in application development. By using existing components, organizations can...
-
 299Malware Analysis
299Malware AnalysisPEframe – Tool To Perform Static Analysis On Malware
PEframe is an open source tool to perform static analysis on Portable Executable malware and generic suspicious file. It can help malware...
-

 274Android Hacking
274Android HackingCuckooDroid – Automated Android Malware Analysis
CuckooDroid is an extension of Cuckoo Sandbox the Open Source software for automating analysis of suspicious files. CuckooDroid brigs to cuckoo the...
-
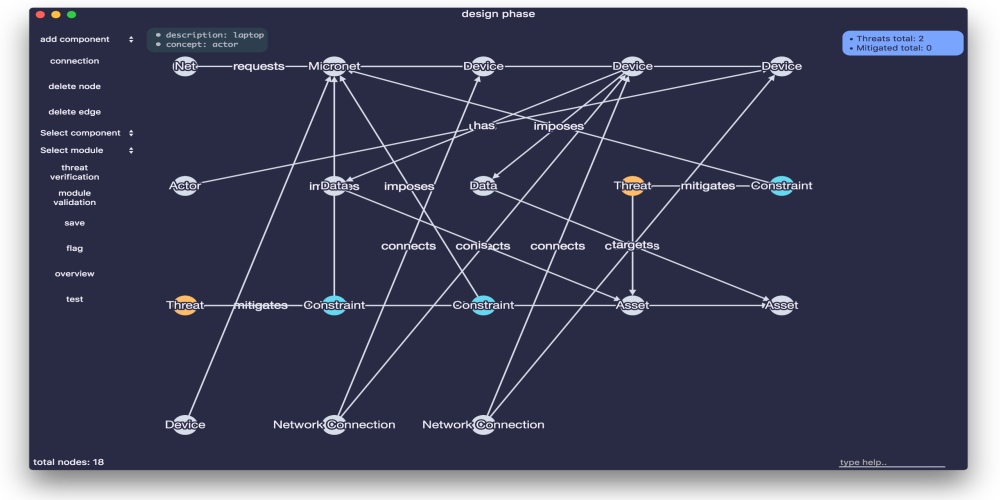
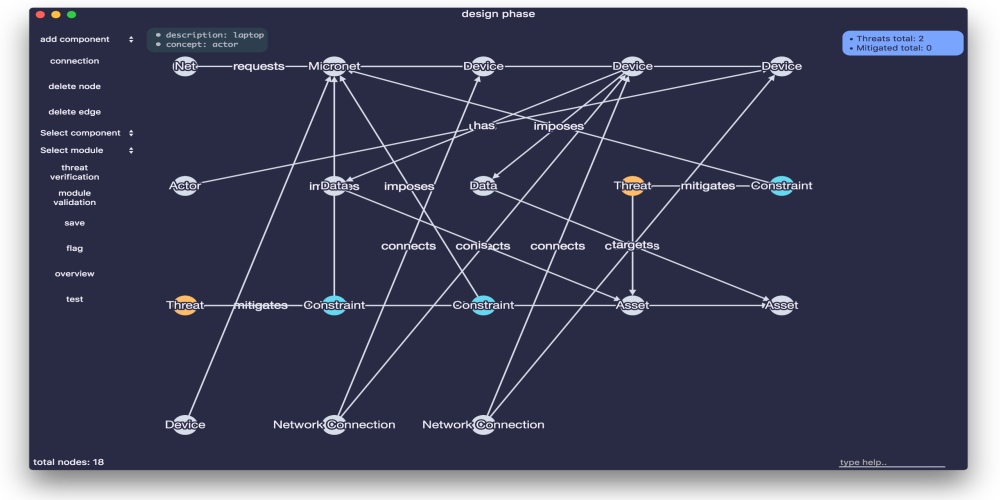 195IOT Hacking
195IOT HackingASTo – IoT Network Security Analysis Tool
Apparatus is a security framework to facilitate security analysis in IoT systems. To make the usage of the Apparatus framework easier the...
-
 188Hack Tools
188Hack ToolsShellCheck – Static Analysis Tool for Shell Scripts
ShellCheck is a static analysis tool that gives warnings and suggestions for bash/sh shell scripts. How To Use ShellCheck There are a number...
-

 284Infosec
284InfosecRisk with Steganography and Importance of running Steganalysis with Network Systems
Steganography is an art of hiding messages covert way so that exclusive the sender and recipient know the original message. This technique...
-

 291Data Security
291Data Security8 Best WiFi Hacking Software And Analysis Tools You Should Use In 2018
Security analysis and penetration testing is an integral part of creating any kind of secure network. This brings us to the WiFi...
-

 235Malware Analysis
235Malware AnalysisProcDOT – Visual Malware Analysis
There are plenty of tools for behavioral malware analysis. The defacto standard ones, though, are Sysinternals’s Process Monitor (also known as Procmon)...
-
 260Vulnerability Analysis
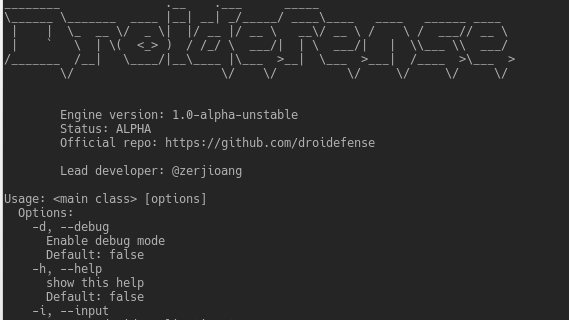
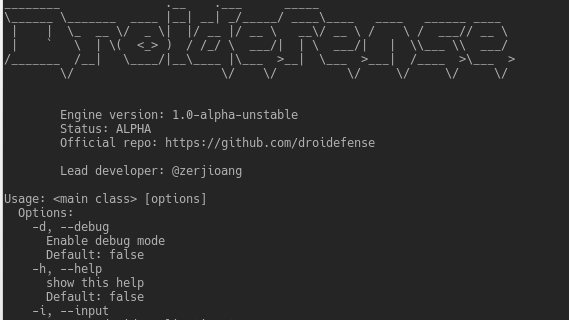
260Vulnerability AnalysisDroidefense – Advance Android Malware Analysis Framework
Droidefense (originally named atom: analysis through observation machine)* is the codename for android apps/malware analysis/reversing tool. It was built focused on security...
-
 258Cryptography and Encryption
258Cryptography and EncryptionAletheia – Machine Learning Image Steganalysis
Aletheia is a steganalysis tool for the detection of hidden messages in images. The goal of steganalysis is to identify suspected packages,...
-
 224Computer Forensics
224Computer ForensicsDAMM – An Open Source Memory Analysis Tool
DAMM (Differential Analysis of Malware in Memory) is an open source memory analysis tool built on top of Volatility. It is meant as...
-

 262Malware
262MalwareUrsnif Malware Variant Performs Malicious Process Injection in Memory using TLS Anti-Analysis Evasion Trick
A Sophisticated Ursnif Malware variant using manipulated TLS call back Anti-Analysis Technique while injecting the Child Process for changing the entry point....






