Search results for "Antivirus"
-

 3.0KMalware
3.0KMalwareFileless Malware, The Archilles Hill Of Traditional Antivirus Software
A typical antivirus products and End Point services today generally speaking comes with two ways of detecting malware: Signature-based Heuristics The signature-based...
-

 397Data Security
397Data SecurityBypass antivirus detection With Phantom Payloads
According to ethical hacking courses, metasploit is the most popular tool used in pentesting. Metasploit tries to find weakness across your local...
-

 262News
262NewsEndpoint Security or Antivirus Software for Small Businesses?
Most small businesses just rely on an antivirus tool to mitigate cyber risks, despite the fact that hackers show an increasing tendency...
-
 224Malware
224MalwareAstaroth Trojan Disguises as JPEG, GIF File Abuses OS and Antivirus Process to Steal Data
A new unique campaign abuses system native OS process and security software to steal passwords and personal information. Threat actors disguise the...
-

 337News
337NewsThis Trojan Steals Credentials By Exploiting Antivirus Software
In a blog post, Cybereason’s Nocturnus Research Team has uncovered a new strain of Astaroth Trojan which infects systems by exploiting processes...
-
 282Malware
282MalwareMalware changes host files so users can’t update their antivirus
Company customers ignore whether this flaw brings more serious consequences According to network security and ethical hacking experts from the International Institute...
-

 642Data Security
642Data SecurityTop 10 Best Antivirus software for 2019
Open the Internet and your screen will be flooded with hacking news and exploits carried out through the use of sophisticated techniques. It is...
-

 468Hacked
468Hacked11 Best Free Android Antivirus Apps For 2019 [Keep Your Device Secure]
As smartphones have become an inherent part of our lives, people no longer use their phones just for communication. Instead, they store...
-

 4.0KCyber Attack
4.0KCyber AttackNew Trend? Antivirus Software Exploited To Launch Privilege Escalation Attack
How can cybercriminals penetrate a network or computer if there are security software in place to prevent it? Some cyber criminals have...
-

 274Data Security
274Data SecurityLinux mining software could steal passwords and disable antivirus
The trojan also installs a rootkit and another malware variant that can lead to denial-of-service conditions Perhaps the malware variants that affect...
-

 258Exploitation Tools
258Exploitation ToolsArmor – Tool Designed To Create Encrypted macOS Payloads Capable Of Evading Antivirus Scanners
Armor is a simple Bash script designed to create encrypted macOS payloads capable of evading antivirus scanners. Below is an example gif...
-
 206Articles
206ArticlesWindows Built-in Antivirus Gets Secure Sandbox Mode – Turn It ON
Microsoft Windows built-in anti-malware tool, Windows Defender, has become the very first antivirus software to have the ability to run inside a...
-

 300Hacked
300HackedWindows Defender Is The First Antivirus To Run Inside Sandbox: Here’s How To Enable It
When it comes to defending Windows, Microsoft has never been able to catch up with some of the best antivirus software in the market. However,...
-
 412Malware
412MalwareNew Adwind RAT Attack Linux, Windows and Mac via DDE Code Injection Technique by Evading Antivirus Software
New Adwind 3.0 RAT (Remote access Trojan) Evolving with new sophisticated capabilities, unlike old version it mainly attacks desktop version of Linux,...
-

 266Malware
266MalwareNSS Labs sues antivirus developers
The company claims that developers conspire to bypass product testing NSS Labs has ignited the controversy in the ever-challenging and obscure world...
-

 170How To
170How ToDoes Your Antivirus Software Work? – How To Test it Securely
In a world bombarded with malware threats, you never know what’s lurking around the corner. Viruses are always looking for an opportunity...
-

 403Lists
403Lists10 Best Free Antivirus Software For 2018 To Protect Your PC
If you’re using Windows operating system and you have a rough idea of what’s happening in the cybersecurity world, you must be...
-

 143Incidents
143IncidentsAPT28 Hack LoJack Software and Antivirus Cannot Detect It
Recently, researchers found corrupt versions of legitimate LoJack software that seems to have been secretly modified to allow hackers inside the companies...
-
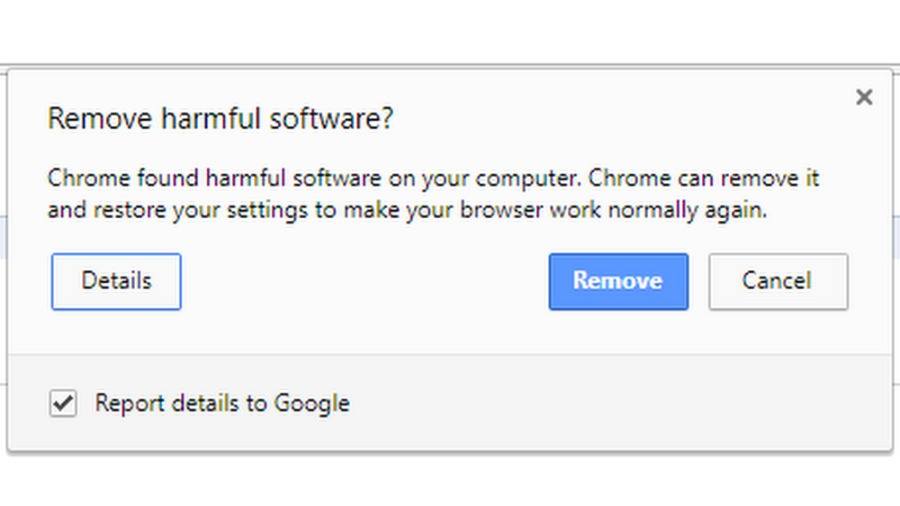
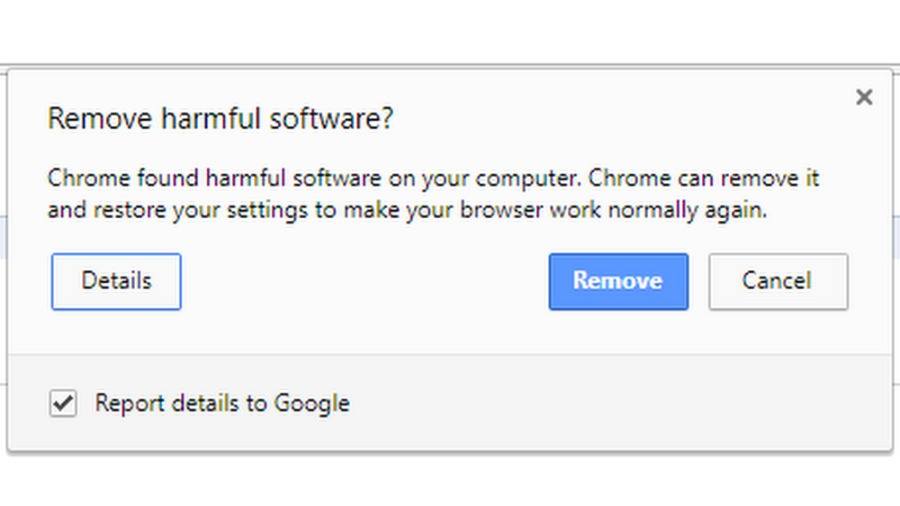 232Hacked
232HackedChrome’s Built-In Antivirus Is Secretly Scanning Files, And…. People Are Freaking Out
After the Facebook Cambridge Analytica scandal, it’s hard for the netizens to trust almost anyone on the internet. Be it Google or...
-

 145Vulnerabilities
145VulnerabilitiesA single NULL character could hide malware from Windows 10 antivirus
Microsoft has worked hard to create and implement new security measures, from anti-exploit shields that prevent the exploitation of vulnerabilities, to the...
-

 219Hacked
219HackedSlow Computer? Feel Free To Blame Your Antivirus Software
You might be blaming and cursing Intel CPU bug patches for the slowness of your computer or frequent reboots. But there is a...






