Search results for "Bluetooth"
-
 286Video Tutorials
286Video TutorialsHow to Enable/Fix Bluetooth Problem in Kali Linux 2017.3
If you are running Kali Linux and your Bluetooth is not working. Let’s fix that. It will be up and running in...
-

 232Security Tools
232Security ToolsBlueMaho v090417 – Bluetooth Security Testing Suite
BlueMaho is GUI-shell (interface) for suite of tools for testing security of bluetooth devices. It is freeware, opensource, written on python, uses...
-

 287Man-In-The-Middle
287Man-In-The-MiddleBtleJuice Framework – Bluetooth Smart (LE) Man-in-the-Middle Framework
BtleJuice is a complete framework to perform Man-in-the-Middle attacks on Bluetooth Smart devices (also known as Bluetooth Low Energy). It is composed...
-
 271Hack Tools
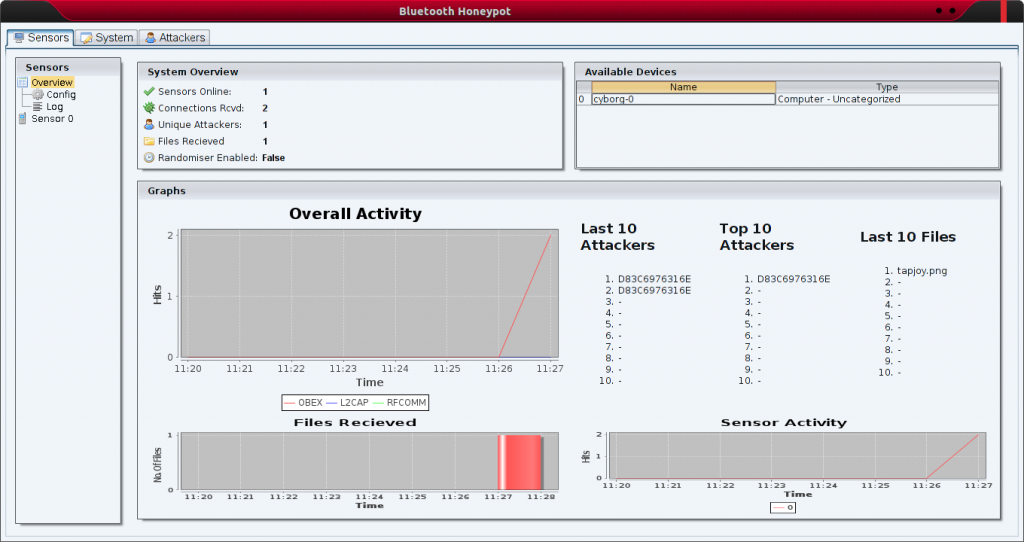
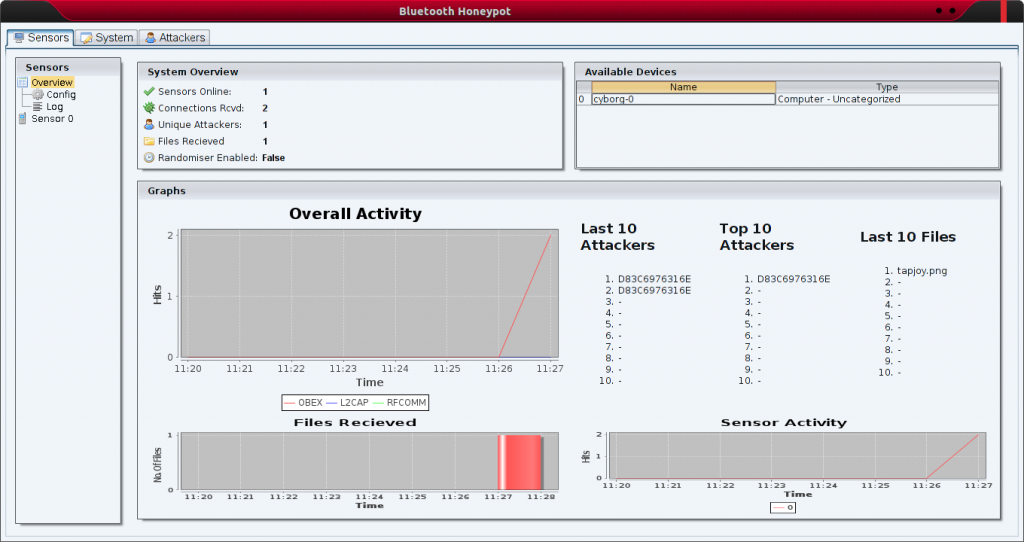
271Hack ToolsBluepot – Bluetooth Honeypot
Bluepot was a third year university project attempting to implement a fully functional Bluetooth Honeypot. A piece of software designed to accept...
-

 186Vulnerabilities
186VulnerabilitiesRemotely Cracking Bluetooth Enabled Gun Safes
In this blog post, we will detail BlueSteal, or the ability to exploit multiple security failures in the Vaultek VT20i. These...
-

 280Vulnerabilities
280VulnerabilitiesAmazon Echo and Google Home were vulnerable to Bluetooth exploit
Don’t worry, these vulnerabilities have already been patched out. Back in September, Bluetooth-connected device owners got a little scare when security firm...
-

 260Articles
260ArticlesBluetooth Hack Affects 20 Million Amazon Echo and Google Home Devices
A series of recently disclosed critical Bluetooth flaws that affect billions of Android, iOS, Windows and Linux devices have now been discovered...
-

 309Hackers Repository
309Hackers RepositoryBlueBorne Bluetooth Vulnerability Can Hack a SmartPhone In Seconds
Bluetooth technology is not a new thing but its starting to become very popular. Bluetooth is now seen in a lot of...
-
 232Hackers Repository
232Hackers Repositoryblueborne-scanner – Bluetooth scanner for blueborne-vulnerable devices
Bluetooth scanner for local devices that may be vulnerable to Blueborne exploit VPN Gate auto-grabber Greetz shouts to sh3llg0d, an0n_l1t3, daemochi, akatz!!!!...
-

 216Vulnerabilities
216VulnerabilitiesBlueBorne – 8 Zero Day Bugs Threaten 8.2 Billion Bluetooth-Enabled Devices
Asecurity firm Armis has identified a set of 8 zero-day bugs, collectively known as BlueBorne, which put Bluetooth-capable devices at the risk...
-

 452Geek
452GeekBlueBorne Bluetooth Flaw Affects Millions of Smartphones, IoT and PCs
A Palo Alto based Internet of Things (IoT) security company Armis has discovered critical vulnerabilities in Bluetooth that if exploited can allow...
-
 360Vulnerabilities
360VulnerabilitiesCritical BlueBorne Vulnerability Puts More Than 5 Billion Bluetooth Enabled Devices Under Attack
Bluetooth is the leading and most widespread protocol for short-range communications.It is the backbone of short range connectivity in the vast majority...
-

 283Geek
283GeekBluetooth-enabled Fidget Spinners are Blowing Up
A fidget spinner is a toy device which in 2017 has become increasingly popular among teens and adults. It consists of a bearing...
-

 109Hackers Repository
109Hackers RepositoryGattacker – A Node.js package for BLE (Bluetooth Low Energy) security assessment
A Node.js package for BLE (Bluetooth Low Energy) security assessment using Man-in-the-Middle and other attacks DOWNLOAD GATTACK http://www.gattack.io Install npm install gattacker...
-

 517News
517NewsCars with Vulnerable WIFI Dongle can be Hacked via Bluetooth
We have already seen a massive growth in the connected-car technology market over the past few years, and it is going to...
-

 462How To
462How ToHack Someone’s Bluetooth And Other Wireless Tools Using Kali Linux
Blooover is performing the Bluebug attack(Bluetooth sniffer Linux). Whilst you intend to install the software, you have to be using a phone...
-

 89Vulnerabilities
89VulnerabilitiesBluetooth Bug Lets Burglars Disable Google Nest Cams
Burglars can use a recently disclosed security flaw affecting several Google Nest cams to make vulnerable cameras go offline for approximately 60...
-

 329Cyber Crime
329Cyber CrimeHackers can crash Google’s Nest Dropcams by exploiting Bluetooth flaws
Last year Google found some critical security flaws in Microsoft’s Edge browser and urged the company to fix these flaws within nine...
-
 60Incidents
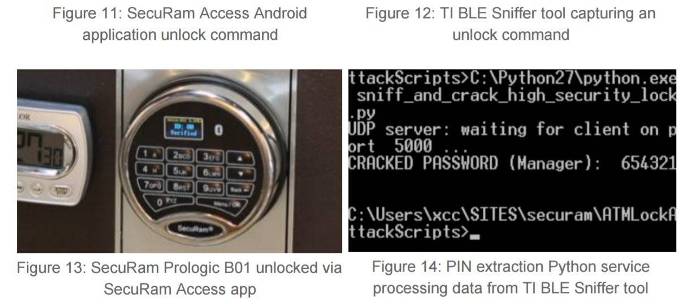
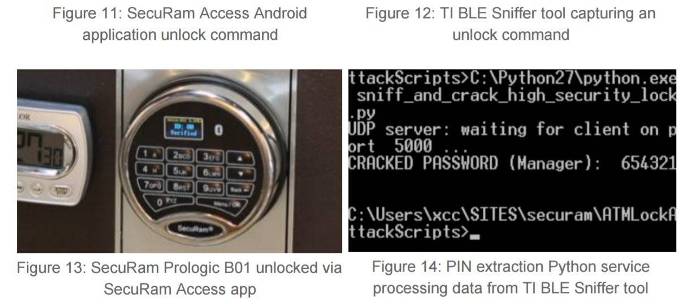
60IncidentsBluetooth-enabled safe lock popped after attackers win PINs
If you use one, stop now. If you write heist movies, write safe-crackers out of your script. Attackers can locate and pop...
-
 251Incidents
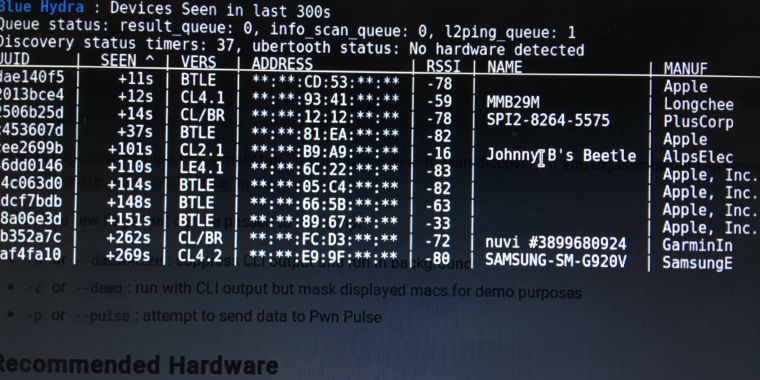
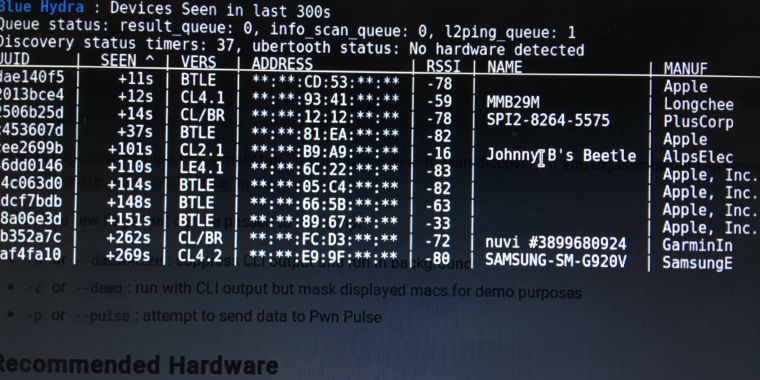
251IncidentsHands-on: Blue Hydra can expose the all-too-unhidden world of Bluetooth
Bluetooth Low Energy devices like smart watches, “wearables,” give you up all day. My new neighbor was using AirDrop to move some files...
-

 204Vulnerabilities
204VulnerabilitiesBLUETOOTH HACK LEAVES MANY SMART LOCKS, IOT DEVICES VULNERABLE
Sławomir Jasek with research firm SecuRing is sounding an alarm over the growing number of Bluetooth devices used for keyless entry and...






