Search results for "Brute"
-
 384Bruteforcing
384BruteforcingPassword Cracking and Login Brute-force [Stats]
People are frequently misguided and look at the password brute-forcing (password cracking) as on a miracle approach to gain access to something,...
-

 280Password Attacks
280Password AttacksBruteX v1.9 – Automatically Brute Force All Services Running On A Target
Automatically brute force all services running on a target Open ports Usernames Passwords INSTALL: ./install.sh USAGE: brutex target <port> DOCKER: docker build...
-
 378Bruteforcing
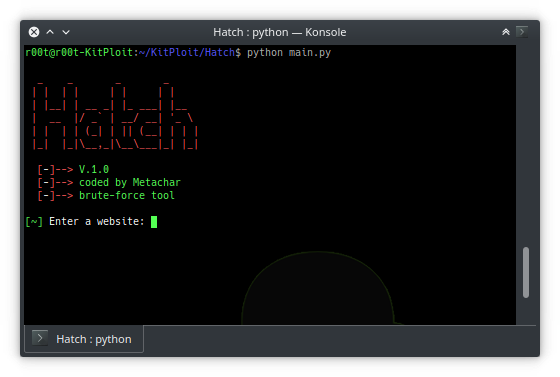
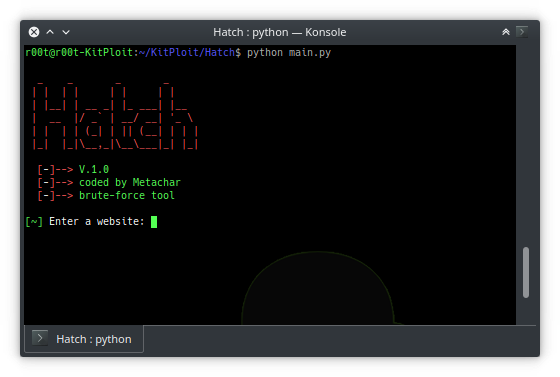
378BruteforcingHatch – Tool To Brute Force Most Websites
Hatch is a brute force tool that is used to brute force most websites Installation Instructions git clone https://github.com/MetaChar/Hatch python2 main.py Requirements...
-

 519Password Attacks
519Password AttacksW3Brute – Automatic Web Application Brute Force Attack Tool
w3brute is an open source penetration testing tool that automates attacks directly to the website’s login page. w3brute is also supported for...
-
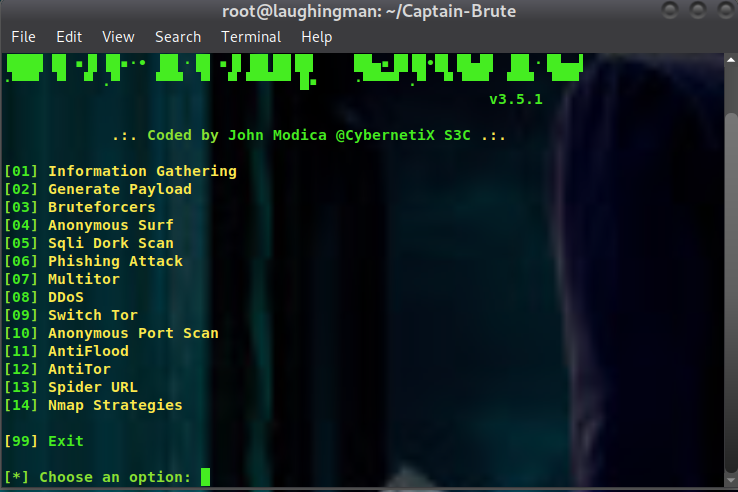
 280Hackers Repository
280Hackers RepositoryCaptain-Brute
Captain brute is a all in one hacking tool by John Modica CybernetiX-S3C it writing in bash with wide range of tools ...
-

 343Password
343PasswordStegCracker – Brute-force Utility to Uncover Hidden Data Inside Files
Steganography is an art of hiding messages covert way so that exclusive the sender and recipient know the original message.This technique permits...
-
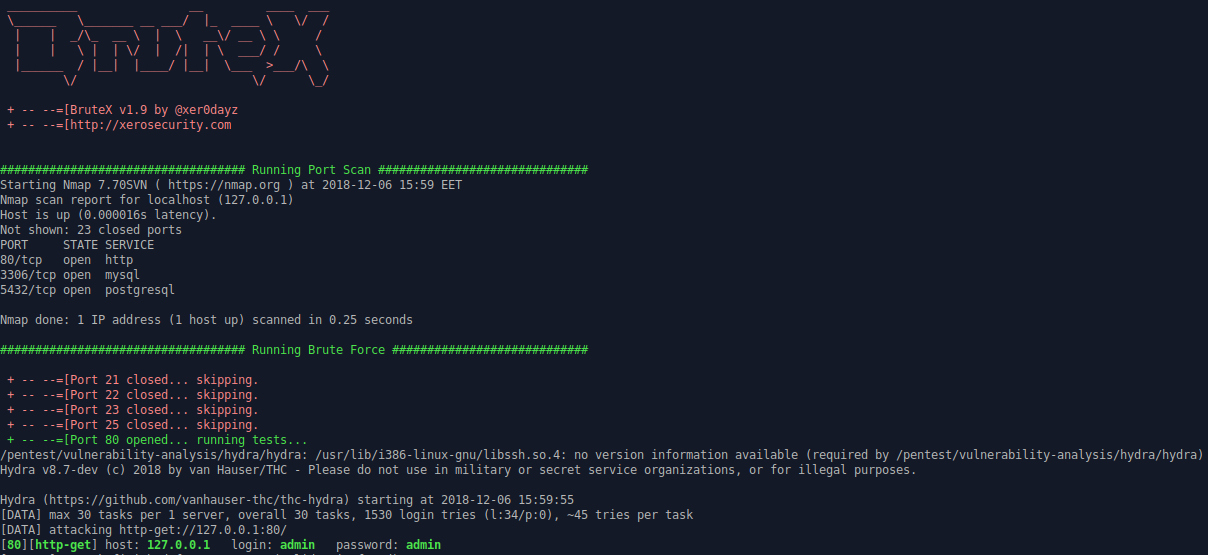
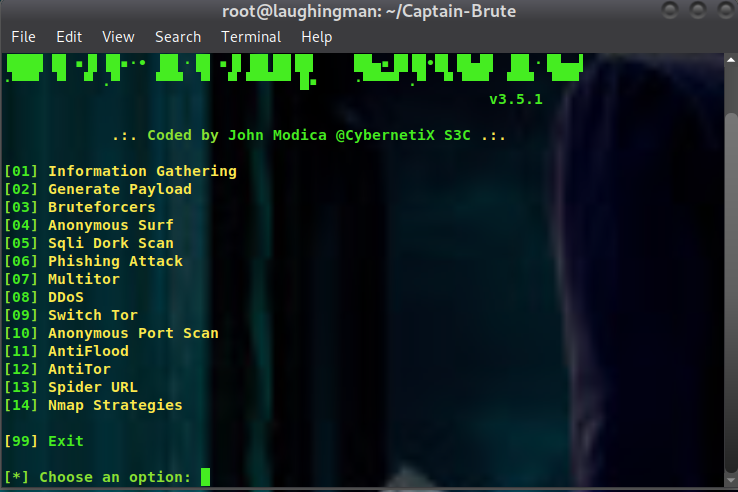
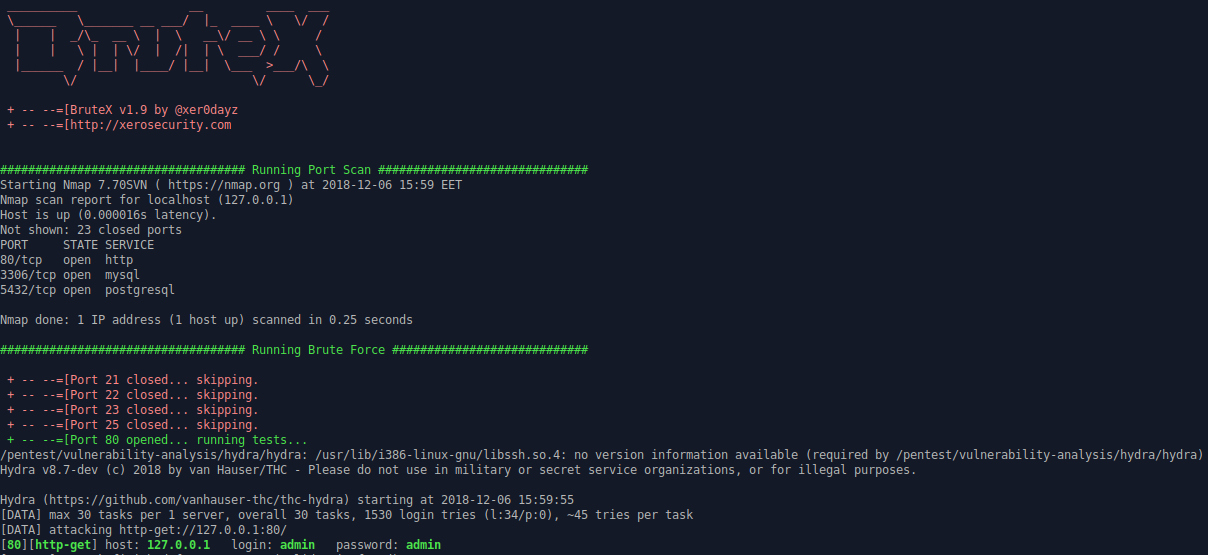 517Hacking Tools
517Hacking ToolsBrutex – Open Source Tool for Brute Force Automation
Brutex is a shell based open source tool to make your work faster. It combines the power of Nmap, Hydra and DNSenum....
-
 361Hacking Tools
361Hacking ToolsBlazy – Open Source Modern Login Brute-forcer
I know what you are thinking, bruteforce doesn’t work anymore in many cases. However, Blazy is not just another brute-force tool. It...
-
 247Information Gathering
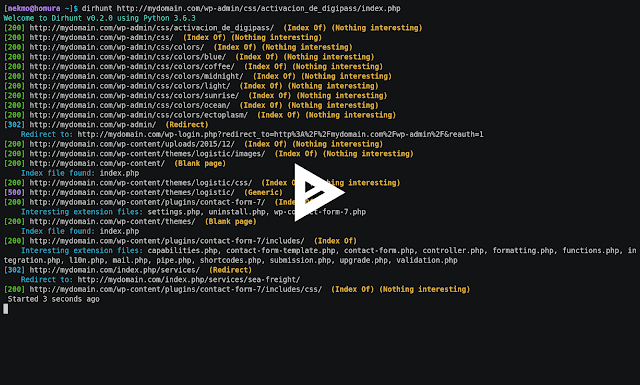
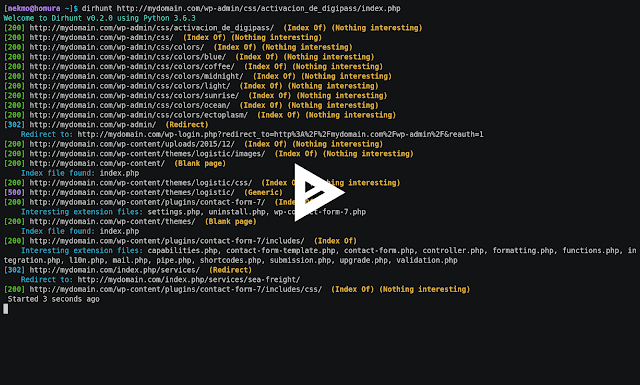
247Information GatheringDirhunt v0.6.0 – Find Web Directories Without Bruteforce
DEVELOPMENT BRANCH: The current branch is a development version. Go to the stable release by clicking on the master branch. Dirhunt is...
-
 326Bruteforcing
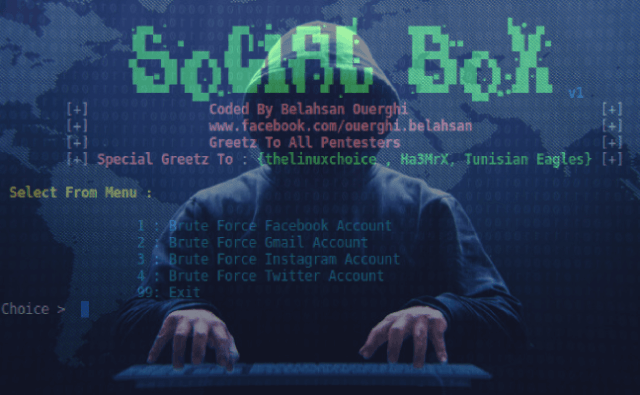
326BruteforcingSocialBox – A Bruteforce Attack Framework[ Facebook , Gmail , Instagram ,Twitter]
SocialBox is a Bruteforce Attack Framework [ Facebook , Gmail , Instagram ,Twitter ]. SocialBox Installation sudo apt-get install git sudo git...
-
 194Ransomware
194RansomwareTroldesh Ransomware Spreading Via Weaponized Word Document and RDP Brute-force Attack
Troldesh Ransomware emerges again and spreads all over the world. The crypto-ransomware variant was created in Russia, the previous variant of the...
-

 438Incidents
438IncidentsA very simple hack evades iOS password entry limit, possibilities of brute force attacks
A researcher specialized in information security training recently discovered an Apple operating system failure that allows anyone with a Lightning cable the...
-

 367Hacked
367HackediPhone Brute Force Hack: Researcher Finds How To Bypass iPhone’s Passcode Limit
Over the past years, Apple has been playing cat and mouse with the security researchers and hackers who keep trying to develop...
-

 316Data Security
316Data SecurityA hacker figured out how to brute force iPhone passcodes
The attack allows any would-be-hacker to run as many passcodes as they want, without destroying the data. A security researcher has figured...
-
 313Data Security
313Data SecurityCountering a Brute Force Attack
Detecting the attack Of course, before we fight a brute force attack, we must first detect it. Specialists from the International Institute...
-
 266Data Security
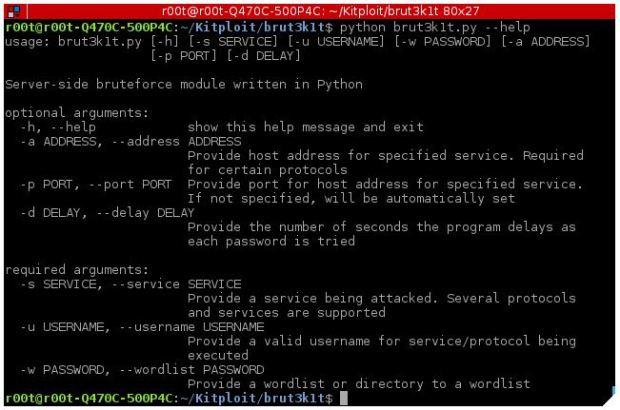
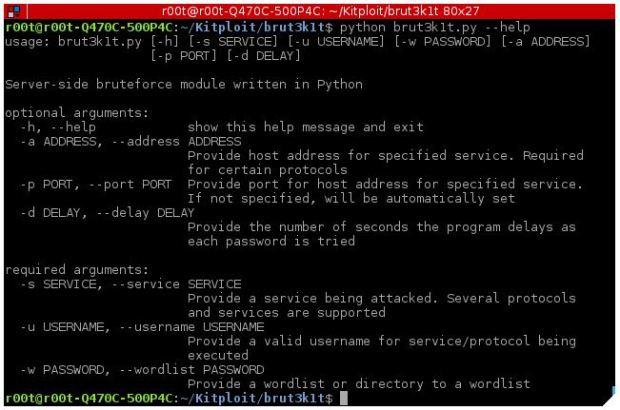
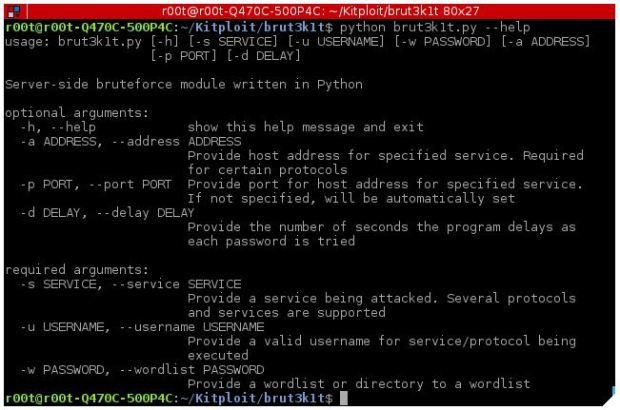
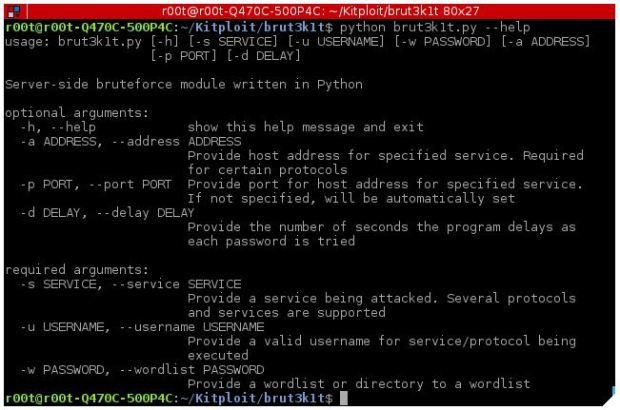
266Data SecurityTool to perform brute force attacks on ssh, smtp, facebook and Instagram- brut3k1t
As an introduction, brut3k1t is a bruteforce module on the server side that supports dictionary attacks for various protocols, information security experts say. Some...
-

 315Bruteforcing
315Bruteforcing0d1n – Tool For Bruteforcing Web Applications
0d1n is a tool for automating customized attacks against web applications. It is an Open Source web application bruteforcer and Fuzzer, its...
-

 342Bruteforcing
342BruteforcingWordBrutePress – A Multithreaded WordPress Bruteforcing Tool
WordBrutePress is a Python-based Multithreaded WordPress bruteforcing tool. Features: Multithreading XML-RPC brute force mode HTTP and https protocols support Random User Agent...
-

 313Bruteforcing
313BruteforcingiCloudBrutter – AppleID Bruteforce
iCloudBrutter is a simple python (3.x) script to perform basic bruteforce attack againts AppleID. Usage of iCloudBrutter for attacking targets without prior...
-

 412Incidents
412IncidentsNorthern Irish Parliament Hit by Brute Force Attack
The email service at the Northern Ireland Parliament, Stormont has been hit by a brute force attack allowing unknown attackers to access...
-

 254Data Security
254Data SecurityDumb – Domain Bruteforce , A tool to bruteforce domains
How DUMB works Dumb works with a masked dumain for substitution. The dumain can have as many masks as you want as...






