Search results for "Bypassing"
-

 885Data Security
885Data SecurityBypassing pfSense firewall and hacking into application server and firewall itself
Recent cybersecurity research has unveiled a critical vulnerability impacting over 1,450 pfSense servers, exposing them to potential remote code execution (RCE) attacks....
-
 999Data Security
999Data SecurityHow to create undetectable malware via ChatGPT in 7 easy steps bypassing its restrictions
There is evidence that ChatGPT has helped low-skill hackers generate malware, which raises worries about the technology being abused by cybercriminals. ChatGPT...
-
 1.6KMalware
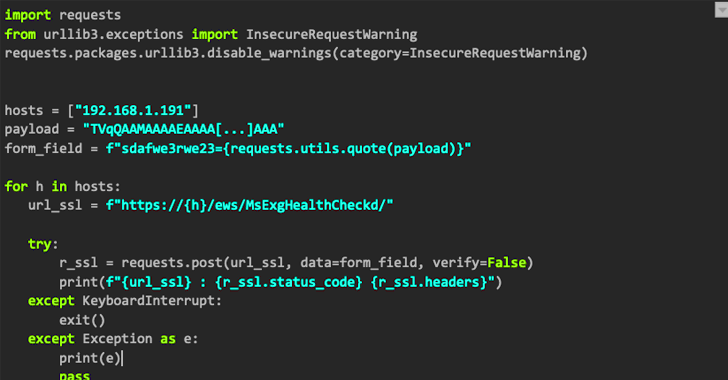
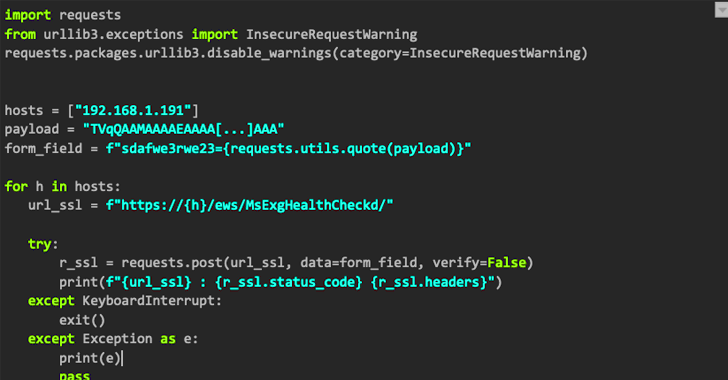
1.6KMalwareNAPLISTENER: New Malware in REF2924 Group’s Arsenal for Bypassing Detection
The threat group tracked as REF2924 has been observed deploying previously unseen malware in its attacks aimed at entities in South and...
-
 3.6KData Security
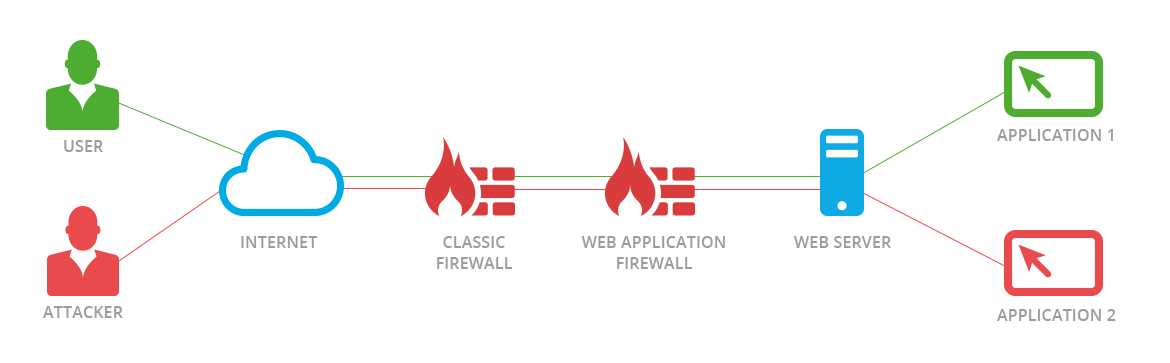
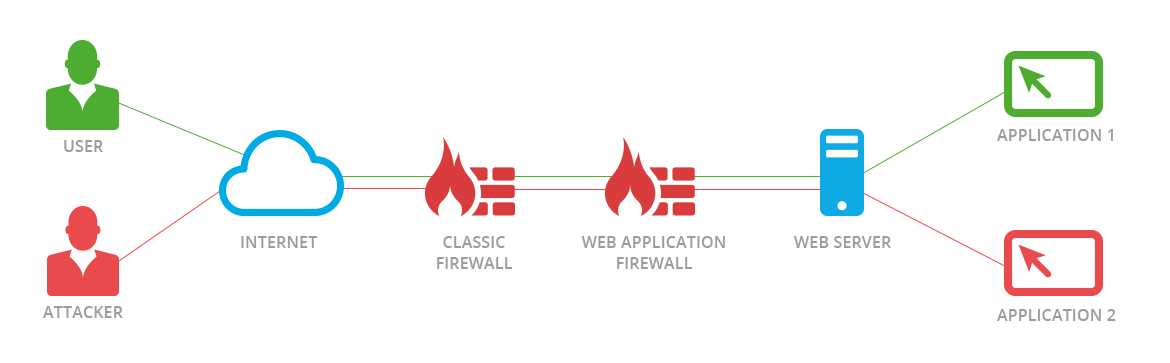
3.6KData SecurityNew JSON-Based SQL Injection attacks allow bypassing Palo Alto, F5, AWS, Cloudflare, and Imperva WAF
Web application firewalls, also known as WAFs, are intended to protect web-based applications and application programming interfaces (APIs) from malicious HTTPS traffic...
-

 2.7KData Security
2.7KData Security3 Techniques that allow bypassing phishing emails through Cisco Secure Email Gateway and are being actively used by ransomware gangs
The following techniques have been made public by a researcher who wishes to remain anonymous. They can be used to bypass certain of...
-

 999Vulnerabilities
999VulnerabilitiesCVE-2021-1810: Vulnerability in macOS allows bypassing Gatekeeper feature. Proof of concept available
Security researcher Rasmus Sten published a proof of concept (PoC) code to exploit a critical vulnerability in macOS Gatekeeper updated a few...
-

 2.7KVulnerabilities
2.7KVulnerabilitiesResearchers discover technique that allows bypassing Let’s Encrypt domain validation and allows fake SSL certificates
Researcher Haya Shulman of the Fraunhofer Institute for Secure Information Technology in Germany reported the discovery of a critical vulnerability in Let’s...
-

 2.8KVulnerabilities
2.8KVulnerabilitiesBypassing WAF in Azure, Cloudflare Access via H2C smuggling attack
A group of specialists has detailed a method for abusing a well-known “H2C smuggling” technique in order to authenticate and bypass some...
-
 334Tutorials
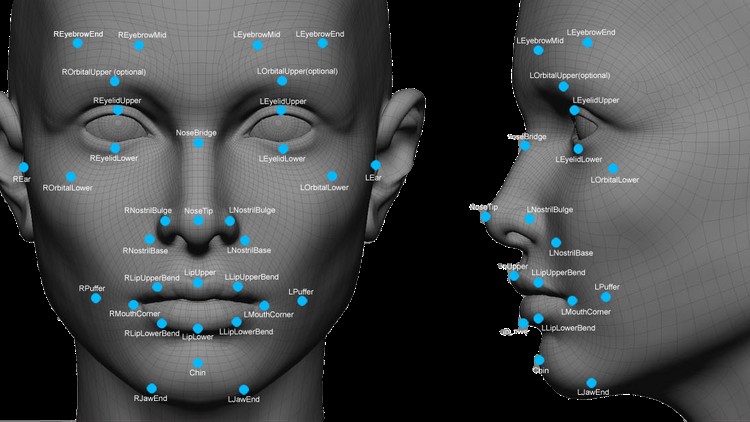
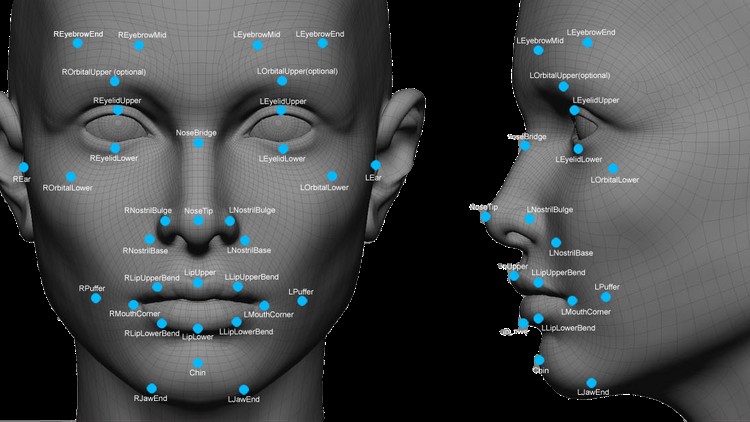
334Tutorials8 methods for bypassing surveillance cameras and facial recognition software
Facial recognition systems are becoming more sophisticated. When we post a photo on Facebook accompanied by our closest friend, it is almost...
-
 525Malware
525MalwareMalicious Apps from Google PlayStore Bypassing SMS-Based Two-Factor Authentication and Steal OTPs in SMS
Researchers discovered new malicious Android apps from Google Play Store bypassing SMS-based two-factor authentication (2FA) mechanisms and steal the OTP without SMS’s...
-

 347Data Security
347Data SecurityPhishing attacks capable of bypassing multi-factor authentication increase
Gmail, from Google, is one of the main services that use this login method Network security and ethical hacking specialists from the International...
-
 252Password Attacks
252Password AttacksBypassing BIOS Passwords
There might be a time where you picked up an old laptop and had a bios password lock enabled but no clue...
-

 226Malware
226MalwareMalicious hackers and their interest in bypassing CAPTCHA
Hackers are looking for ways to bypass this security measure The topic is being discussed in multiple hacking forums hosted on deep...
-
 231Vulnerabilities
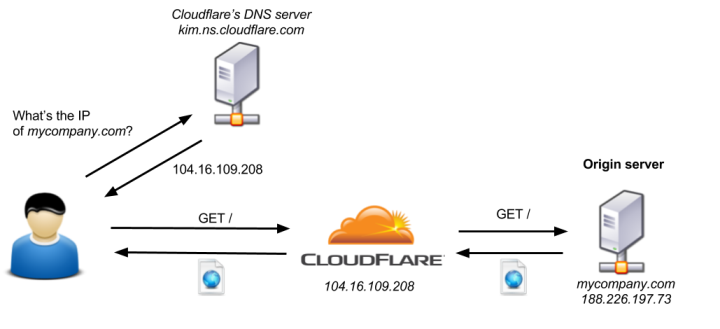
231VulnerabilitiesCloudFlair: Bypassing Cloudflare using Internet-wide scan data
Cloudflare is a service that acts as a middleman between a website and its end users, protecting it from various attacks. Unfortunately,...
-

 268Exploitation Tools
268Exploitation ToolsSpookFlare – Meterpreter Loader Generator With Multiple Features For Bypassing Client-Side And Network-Side Countermeasures
SpookFlare has a different perspective to bypass security measures and it gives you the opportunity to bypass the endpoint countermeasures at the...
-
 229Evasion & Obfuscation
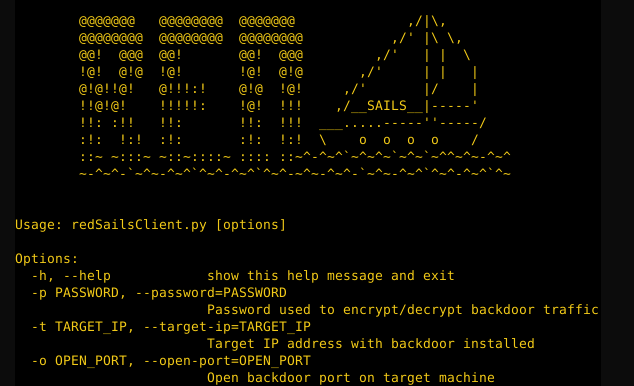
229Evasion & ObfuscationRedSails – Bypassing host based security monitoring and logging
A post-exploitation tool capable of maintaining persistence on a compromised machine, subverting many common host event logs (both network and account logon)...
-
 206Vulnerabilities
206VulnerabilitiesBypassing AMSI via COM Server Hijacking
Microsoft’s Antimalware Scan Interface (AMSI) was introduced in Windows 10 as a standard interface that provides the ability for AV engines to...
-
 180Incidents
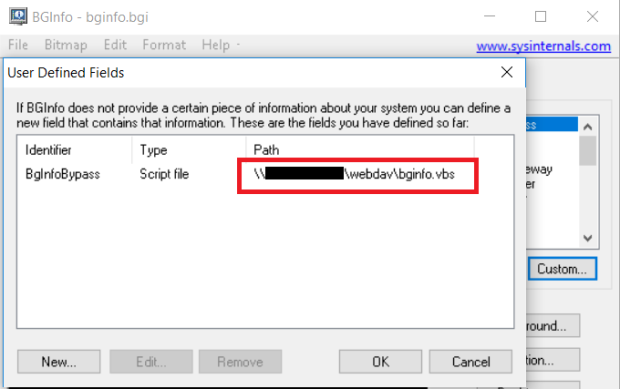
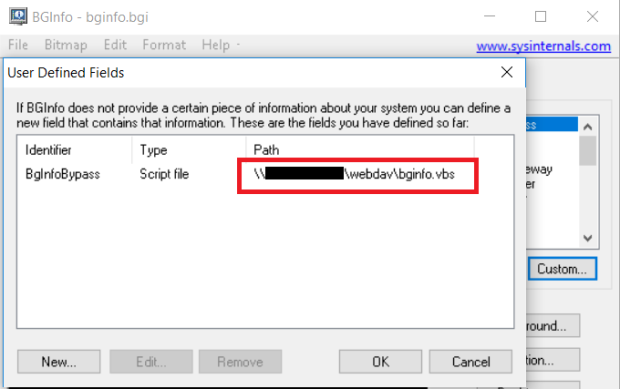
180IncidentsBypassing Application Whitelisting with BGInfo
BGinfo.exe older than version 4.22 can be used to bypass application whitelisting using vbscript inside a bgi file. This can run directly...
-
 278Vulnerabilities
278VulnerabilitiesCVE-2017-2636: exploit the race condition in the n_hdlc Linux kernel driver bypassing SMEP
This driver provides HDLC serial line discipline and comes as a kernel module in many Linux distributions, which have CONFIG_N_HDLC=m in the...
-
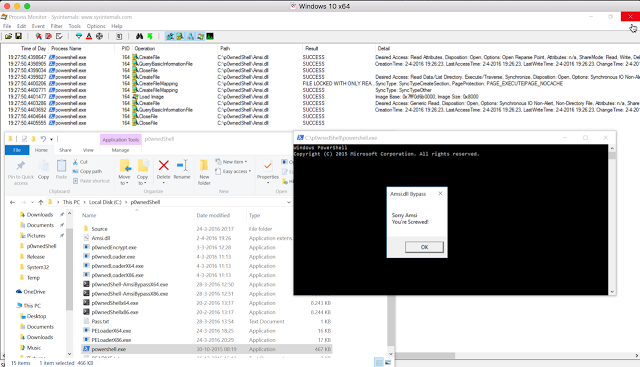
 254Data Security
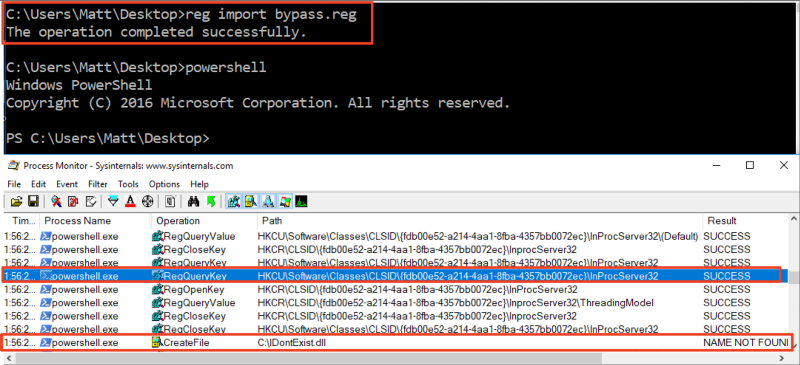
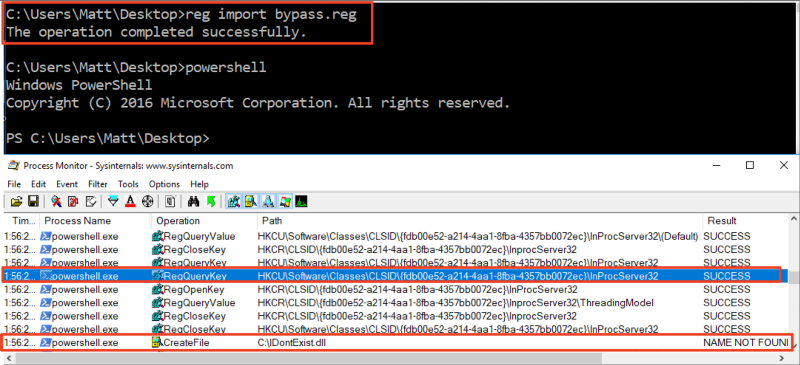
254Data SecurityBypassing Amsi using PowerShell 5 DLL Hijacking
While doing some research on the inner workings of Microsofts new Antimalware Scan Interface technology within Windows 10, i found a DLL...
-

 275Cyber Crime
275Cyber CrimeBypassing LastPass’s Security? A phishing Attack Would Serve Just Right
LastPass Password Manager – renowned for being a secure vault for user’s passwords, has recently demonstrated vulnerabilities that could expose many users’...






