Search results for "Container"
-
 867Tutorials
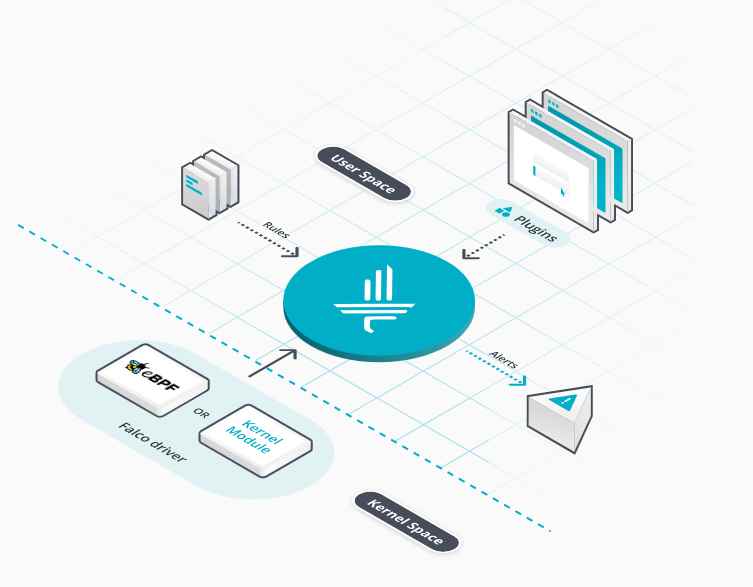
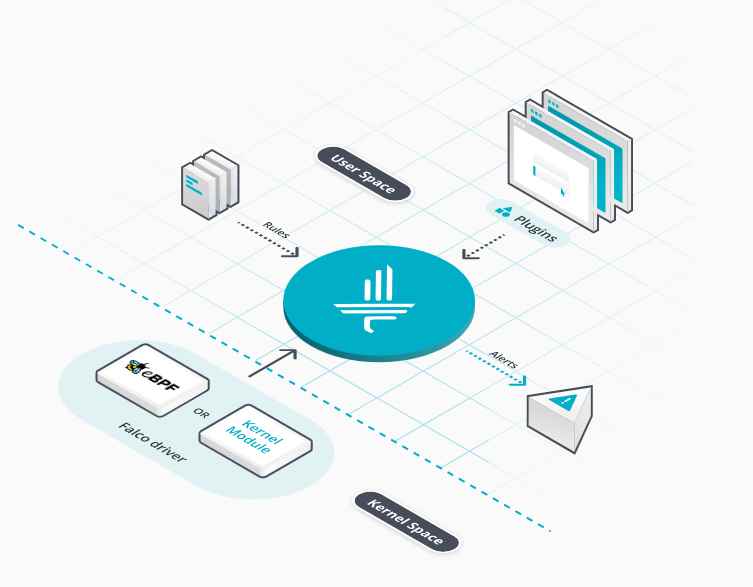
867TutorialsThe 11 Essential Falco Cloud Security Rules for Securing Containerized Applications at No Cost
In the evolving landscape of container orchestration, Kubernetes has emerged as the de facto standard due to its flexibility, scalability, and robust...
-

 4.7KMalware
4.7KMalwareHackers Can Exploit Windows Container Isolation Framework to Bypass Endpoint Security
New findings show that malicious actors could leverage a sneaky malware detection evasion technique and bypass endpoint security solutions by manipulating the...
-
 1.2KData Security
1.2KData SecurityEasily hack into Azure Bastion and Azure Container Registry via XSS vulnerabilities
Microsoft Azure Bastion and Azure Container Registry have each been found to have one potentially “dangerous” security flaw that, if taken advantage...
-
 3.7KData Security
3.7KData SecurityHow to Secure containers images with open source Bazel tool plugin Rules_oci from Google
Rules_oci, an open-sourced Bazel plugin (“ruleset”) that makes it easier and more secure to create container images using Bazel, has been made...
-
 4.7KMalware
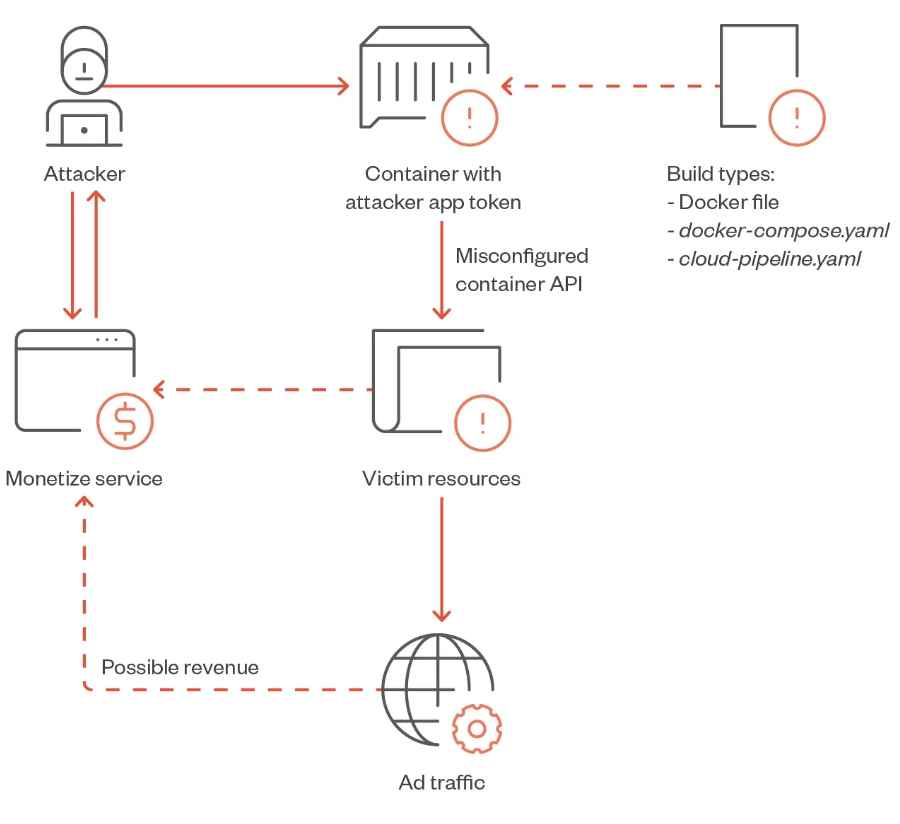
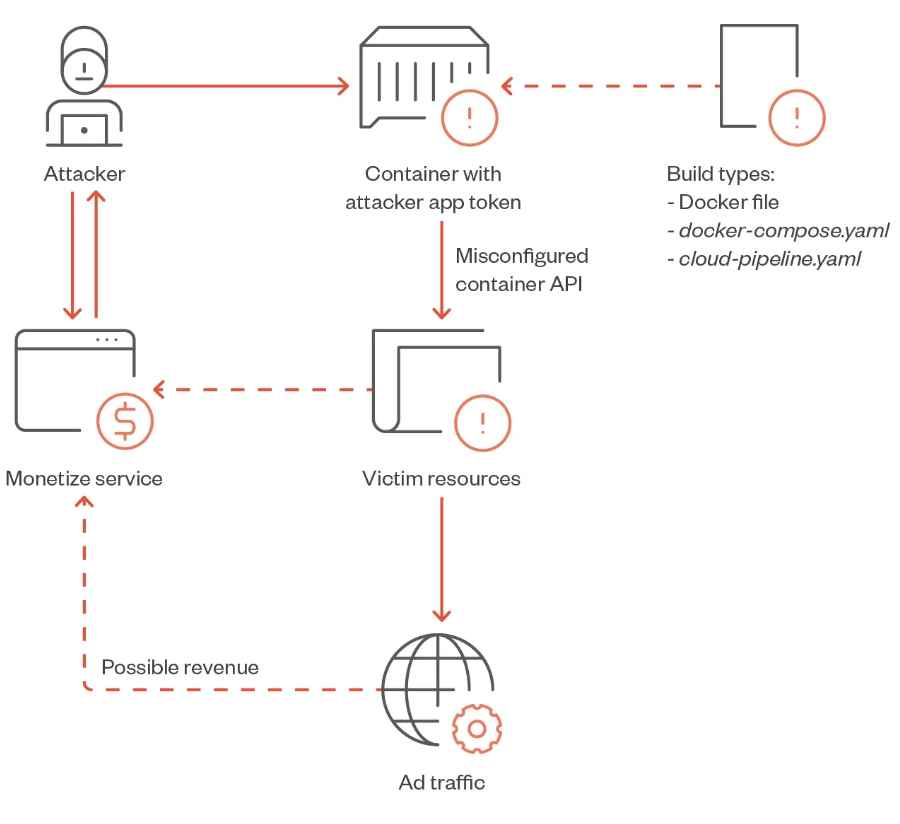
4.7KMalwareHow TrafficStealer utility allows anyone to earn money via vulnerable Docker containers
Researchers at TrendMicro have uncovered a new risk to Docker containers, a piece of malware that they have called “TrafficStealer.” The purpose...
-
 4.7KMalware
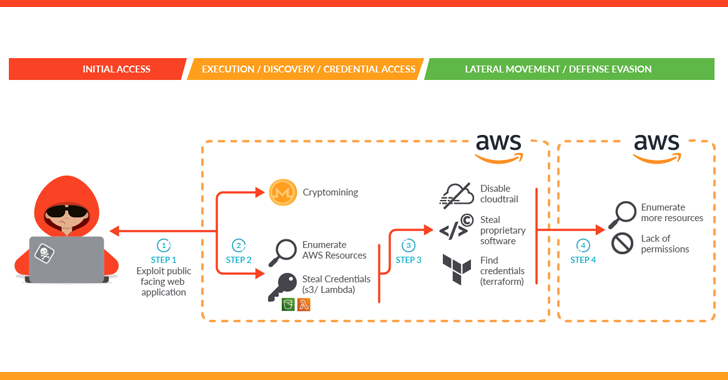
4.7KMalwareHackers Exploit Containerized Environments to Steal Proprietary Data and Software
A sophisticated attack campaign dubbed SCARLETEEL is targeting containerized environments to perpetrate theft of proprietary data and software. “The attacker exploited a...
-

 2.4KVulnerabilities
2.4KVulnerabilitiesAWS patches to fix Log4j vulnerabilities could be exploited for privilege escalation or container escape attacks
Cybersecurity specialists from Palo Alto Networks mention that patches released by Amazon Web Services (AWS) to address vulnerabilities in Log4j could be...
-

 3.6KNews
3.6KNewsSevere Vulnerability Patched in CRI-O Container Engine for Kubernetes
A report by CrowdStrike reveals that an extreme weakness affecting the CRI-O container engine for Kubernetes could be utilized to break free...
-

 1.3KVulnerabilities
1.3KVulnerabilitiesSevere vulnerability in Linux kernel allows hackers to escape from a container to execute arbitrary commands on the affected host. CVSS 7.0/10
Cybersecurity specialists report the detection of a severe vulnerability in the Linux kernel whose exploitation would allow threat actors to escape from...
-
 4.3KVulnerabilities
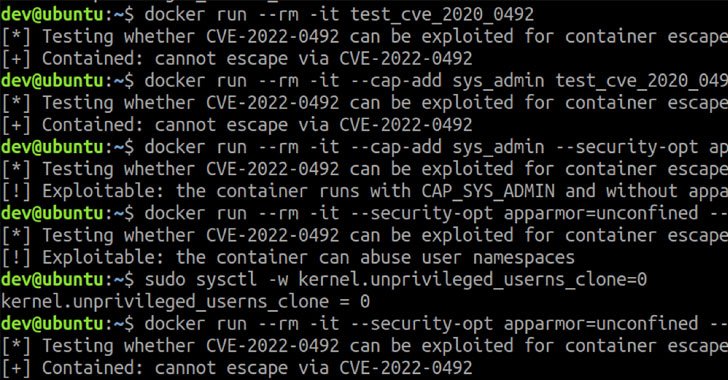
4.3KVulnerabilitiesNew Linux Kernel cgroups Vulnerability Could Let Attackers Escape Container
Details have emerged about a now-patched high-severity vulnerability in the Linux kernel that could potentially be abused to escape a container in...
-
 2.8KData Security
2.8KData SecurityGoogle shares details of unpatched Windows AppContainer vulnerability
Microsoft was informed about the vulnerability by Google but the company claimed it to be a “non-issue” and that it “will not...
-
 5.1KVulnerabilities
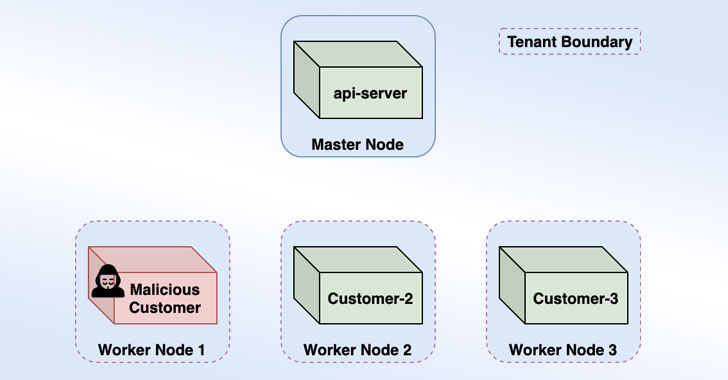
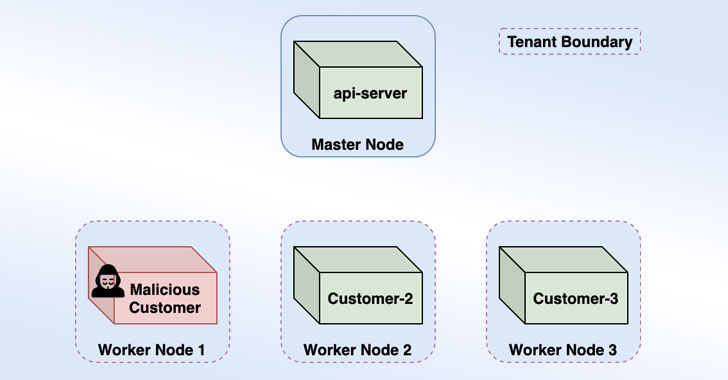
5.1KVulnerabilitiesMicrosoft Warns of Cross-Account Takeover Bug in Azure Container Instances
Microsoft on Wednesday said it remediated a vulnerability in its Azure Container Instances (ACI) services that could have been weaponized by a...
-

 4.9KVulnerabilities
4.9KVulnerabilitiesGoogle publishes zero-day vulnerability in Windows firewall and AppContainer affecting every version. Patch not available
Project Zero, Google’s cybersecurity unit, published research detailing its analysis of the Windows firewall and AppContainer, Microsoft’s runtime environment that restricts applications...
-

 3.7KMalware
3.7KMalwareSiloscape: First Known Malware Targeting Windows Containers to Hack Cloud Environments
Using Windows Server in a “Windows container”? Then beware of it, as recently, it has been confirmed that highly sophisticated malware has...
-
 4.0KMalware
4.0KMalwareSiloscape: the new malware to compromise Windows containers and Kubernetes clusters
A group of researchers has found a new malware variant designed to breach the security of Windows containers in order to reach...
-
 2.6KMalware
2.6KMalwareResearchers Discover First Known Malware Targeting Windows Containers
Security researchers have discovered the first known malware, dubbed “Siloscope,” targeting Windows Server containers to infect Kubernetes clusters in cloud environments. “Siloscape...
-
 1.5KSystem Administration
1.5KSystem AdministrationCDK – Zero Dependency Container Penetration Toolkit
CDK is an open-sourced container penetration toolkit, designed for offering stable exploitation in different slimmed containers without any OS dependency. It...
-

 1.1KVulnerabilities
1.1KVulnerabilitiesMicrosoft’s Anzure cloud-container technology allows hackers to directly update your files
Cybersecurity specialists from Intezer report the finding of a privilege escalation vulnerability in Microsoft Azure Functions whose exploitation would allow threat actors...
-

 2.3KHack Tools
2.3KHack ToolsCCAT – Cloud Container Attack Tool For Testing Security Of Container Environments
Cloud Container Attack Tool (CCAT) is a tool for testing security of container environments. Quick reference Where to get help: the Pacu/CloudGoat/CCAT...
-
 1.0KVulnerabilities
1.0KVulnerabilitiesMost Critical Docker Vulnerability Let Hackers To Take Complete Control Over Host & All Containers Within It
Researchers discovered a critical vulnerability in Docker that allows an attacker to take complete control of the host and the containers associated...
-
 389Security Tools
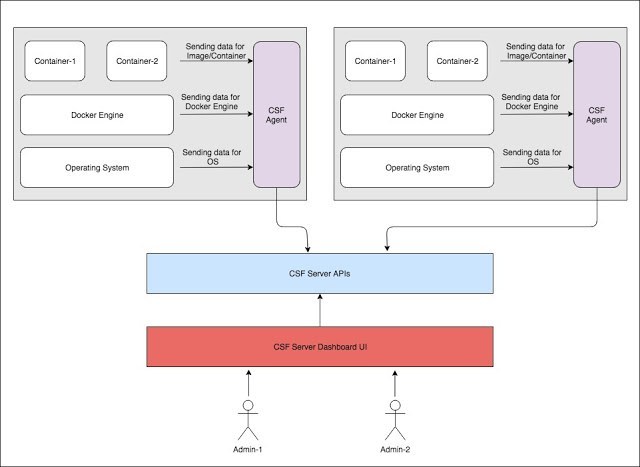
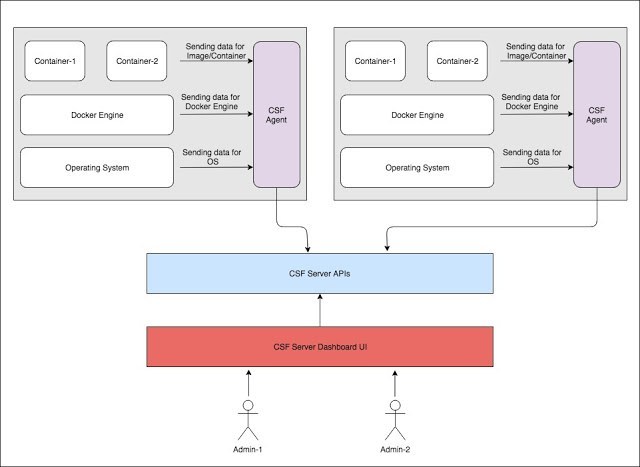
389Security ToolsArmourBird CSF – Container Security Framework
ArmourBird CSF – Container Security Framework is an extensible, modular, API-first framework build for regular security monitoring of docker installations and...






