Search results for "Credentials"
-

 333Trojan / Worms
333Trojan / WormsCross-platform Remote Access Trojan “Adwind” Steal Credentials, Record and Harvest keystrokes the Aerospace Industries Data
Remote Access Trojan(RAT) Called “Adwind”(Adwind/jRAT) Targeting Aerospace Industries to steal credentials, record and harvest keystrokes, take pictures or screenshots, film and retrieve...
-

 312News
312NewsCIA Implants Steal SSH Credentials From Linux & Windows Devices: WikiLeaks
The whistleblowing platform WikiLeaks is back with another batch of Vault 7 related documents exposing the alleged hacking tools and programs used by...
-

 226Hacked
226HackedBothanSpy & Gyrfalcon: CIA Malware To Steal SSH Credentials From Windows & Linux PCs
Short Bytes: WikiLeaks has recently published new documents, revealing new CIA malware implants. The first implant, named BothanSpy, targets SSH client Xshell...
-

 118Incidents
118IncidentsCIA Malware Can Steal SSH Credentials, Session Traffic
WikiLeaks dumped today the documentation of two CIA hacking tools codenamed BothanSpy and Gyrfalcon, both designed to steal SSH credentials from Windows...
-
 302Malware
302MalwareVault 7 Leaks : CIA Hacking Tools “BothanSpy” and “Gyrfalcon” Steals SSH Credentials From Windows and Linux Computers – WikiLeaks
WikiLeaks Revealed Another CIA Cyber Weapons called “BothanSpy” and “Gyrfalcon” steals the SSH Credentials from both Windows and Linux Platform and both...
-

 358Hacking Tutorials
358Hacking TutorialsUsing BeEF to Hack Facebook Credentials
Are you trying to know the Username and Password of any FB Account but you don’t want to hack their Account? It’s...
-

 174Vulnerabilities
174VulnerabilitiesFreeRADIUS allows hackers to log in without credentials
The security researcher Stefan Winter has discovered a TLS resumption authentication bypass in FreeRADIUS, the world’s most popular RADIUS Server. The security...
-

 315News
315NewsHackers Claim Leaking Thousands of Spotify Login Credentials
Amidst the recent series of attacks launched on various computers through the WannaCry Malware, a relatively minor incident occurred in which Spotify...
-

 318Data Security
318Data SecurityChrome vulnerability can allow attackers to steal user credentials
Google Chrome may not be as safe as it was thought to be. Recently, a security engineer, Bosko Stankovic, found a vulnerability...
-
 204Vulnerabilities
204VulnerabilitiesYou Can Steal Windows Login Credentials via Google Chrome and SCF Files
Just by accessing a folder containing a malicious SCF file, a user will unwittingly share his computer’s login credentials with an attacker...
-

 303Incidents
303IncidentsEdge Security Flaw Allows Theft of Facebook and Twitter Credentials
Argentinean security researcher Manuel Caballero has discovered another vulnerability in Microsoft’s Edge browser that can be exploited to bypass a security protection...
-

 225News
225NewsHyundai Blue Link app vulnerable; login credentials and GPS data at risk
Hyundai Blue Link apps on Android and Apple app stores are vulnerable to cyber attacks which if exploited can allow attackers to steal...
-

 320Mobile Security
320Mobile SecurityMobile spyware that steal Twitter credentials uses sandbox to Evade antivirus detections
[jpshare]Security Experts from Avast came through a Malware that uses a sandbox(DroidPlugin) to dynamically load and run an app, without actually installing...
-
 180Vulnerabilities
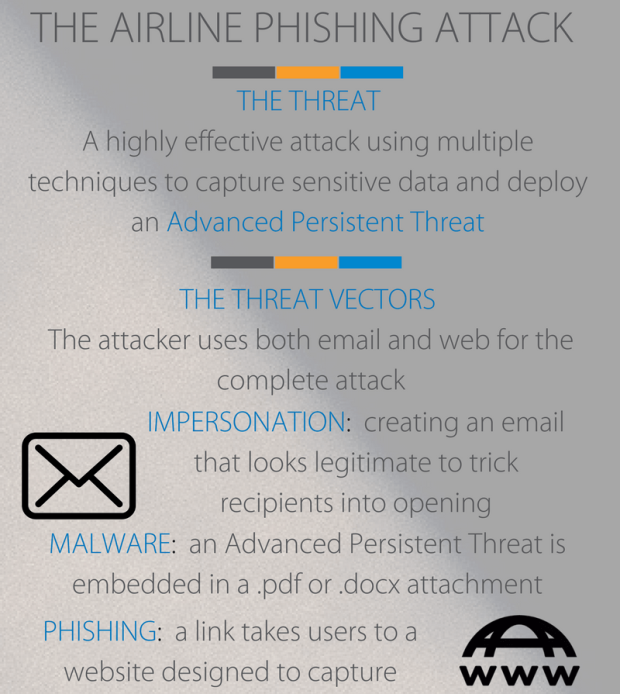
180VulnerabilitiesPhishing campaigns target airline consumers seeking business credentials
A series of phishing campaigns is targeting airline consumers with messages crafted to trick victims into handing over personal or business credentials....
-

 182Vulnerabilities
182VulnerabilitiesEXPERTS DOUBT HACKERS’ CLAIM OF MILLIONS OF BREACHED APPLE CREDENTIALS
Security experts say they are skeptical that a group of hackers called Turkish Crime Family actually possess a cache of hundreds of...
-

 282Data Security
282Data SecurityFlaws in LastPass Password Manager Allowed Hackers to Steal Credentials
Travis Ormandy, a researcher at Google project zero, found some critical security flaws in the famous password manager LastPass which could allow...
-

 298Data Security
298Data SecurityTwitter Verify Account Phishing Scam Steals Credentials, Credit Card Data
Twitter is now the target of a phishing attack that uses methods to trick brand managers and social influencers into fake account...
-

 172Vulnerabilities
172VulnerabilitiesCritical Vulnerability with NETGEAR WNR2000 Discloses admin credentials
Critical Vulnerability with NETGEAR WNR2000 was disclosed by security experts from Agile Information Security. SUMMARY NETGEAR WNR2000 permits a administrator to play out...
-

 305Geek
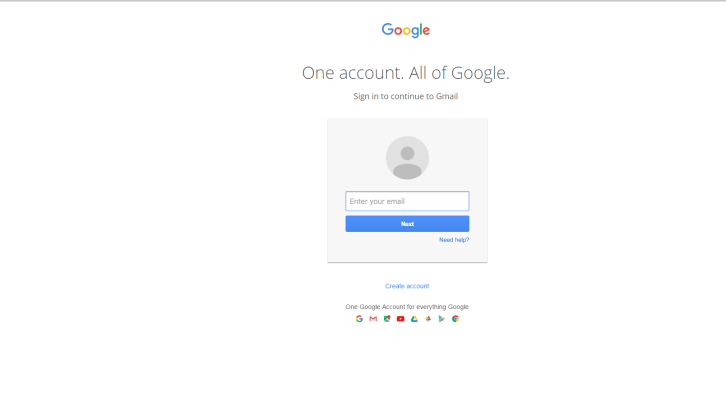
305GeekGmail Phishing Scam Stealing Credentials Through Infected Attachment
Malicious threat actors are using exclusively designed URLs to deceive users into providing their Gmail credentials. This latest phishing campaign, discovered by...
-
 119Vulnerabilities
119VulnerabilitiesInsidious phishing attack leverages on fake attachments to steal Gmail credentials
Cybercriminals are adopting specially crafted URLs to trick users into entering their Gmail credentials in a new sophisticated phishing campaign. Security experts...
-

 201Data Security
201Data SecurityThe Oracle of Delphi Will Steal Your Credentials
It was one of those warm summer nights, no clouds, just a bright full moon lighting the way. Someone had unknowingly stumbled...






