Search results for "Cyber Attacks"
-

 133Cyber Crime
133Cyber CrimeBanks “ignore early warnings” of cyber attacks, says Australian security chief
Banks should look to spam emails and their own server errors as a source of information, says Nicholas Scott of National Australia...
-
 216Hacking
216HackingChina has “mountains of data” on U.S. cyber attacks, top official claims
A top internet security official in China has said that his organization has “mountains of data” on U.S. cyber attacks against the...
-

 428Cyber Crime
428Cyber CrimeSilicon Valley “needs to lead” battle against cyber attacks, says ex‑Homeland Security chief
Silicon Valley technology firms should take the lead in defending the private sector against cyber attacks, says Paul Rosenzweig, a former Department...
-

 98Cyber Crime
98Cyber CrimeElectrical grids “woefully prepared” for cyber attacks, warns analyst
Electrical grids worldwide have become more susceptible to cyber attacks, due to the use of industrial control systems, according to market analysts...
-

 102Cyber Crime
102Cyber CrimeCyber attacks on America “will get worse”, warns NSA director
Cyber attacks on America will continue to escalate, according to National Security Director Keith Alexander, speaking to the Reuters Cybersecurity Summit in...
-

 88Cyber Crime
88Cyber CrimeFBI shares information on cyber attacks with US banks
The FBI has offered temporary security clearances to security officers from U.S. banks in order to share information into repeated cyber attacks...
-

 87Cyber Crime
87Cyber CrimeObama issues order on defense against cyber attacks
U.S. President Barack Obama plans to release a long-awaited executive order aimed at improving cyber security were realised Tuesday. The order is...
-

 287News
287NewsIncapsula Security Firm Analyze Reality Behind Recent U.S. Cyber Attacks
If you remember our article on a wave of DDoS attacks on several American banks, this news is the continual of that...
-

 313Cyber Events
313Cyber EventsIran Blamed for Cyber Attacks on US Banks and Financial Giants
U.S.A has been one of the prime centers of cyber crimes in recent times and we this time around came to know...
-

 358Cyber Crime
358Cyber CrimeUS Navy Facing 110,000 Cyber Attacks Every Hour
The internal IT & server system of US Navy is facing 110,000 cyber attacks every hour, 1,833 attacks a minute. According to...
-
 251Cyber Crime
251Cyber CrimeAmerica’s infrastructure still exposed to cyber attacks despite recent threats
A common man when thinks about cyber terrorism or cyber crime, they think it may be just an illegal activity over some...
-
Cyber Crime
US Pentagon: it’s official, military response to cyber attacks
Awhile back we noticed signals from the US Pentagon that they were considering the possibility of a traditional military response to cyber...
-

 1.6KMalware
1.6KMalwareChina-Linked Hackers Suspected in ArcaneDoor Cyberattacks Targeting Network Devices
The recently uncovered cyber espionage campaign targeting perimeter network devices from several vendors, including Cisco, may have been the work of China-linked...
-

 1.4KData Breach
1.4KData BreachUnmasking the True Cost of Cyberattacks: Beyond Ransom and Recovery
Cybersecurity breaches can be devastating for both individuals and businesses alike. While many people tend to focus on understanding how and why...
-
 1.7KMalware
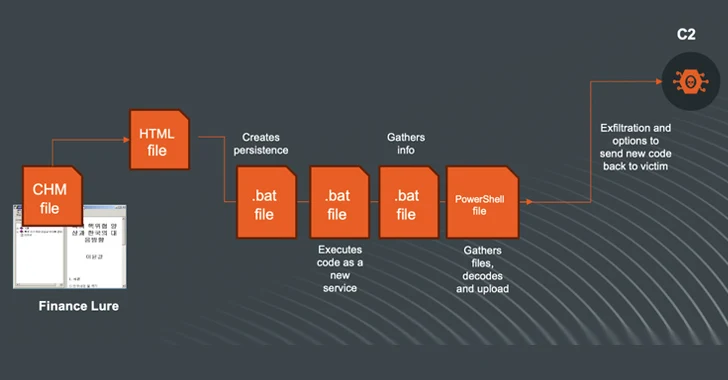
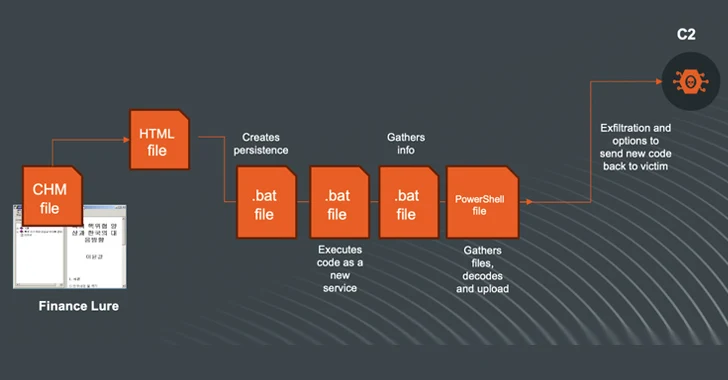
1.7KMalwareN. Korea-linked Kimsuky Shifts to Compiled HTML Help Files in Ongoing Cyberattacks
The North Korea-linked threat actor known as Kimsuky (aka Black Banshee, Emerald Sleet, or Springtail) has been observed shifting its tactics, leveraging...
-

 798Malware
798MalwareCybercriminals Weaponizing Open-Source SSH-Snake Tool for Network Attacks
A recently open-sourced network mapping tool called SSH-Snake has been repurposed by threat actors to conduct malicious activities. “SSH-Snake is a self-modifying...
-
 5.1KVulnerabilities
5.1KVulnerabilitiesNew Findings Challenge Attribution in Denmark’s Energy Sector Cyberattacks
The cyber attacks targeting the energy sector in Denmark last year may not have had the involvement of the Russia-linked Sandworm hacking...
-

 3.9KMalware
3.9KMalwareHamas-Linked Cyberattacks Using Rust-Powered SysJoker Backdoor Against Israel
Cybersecurity researchers have shed light on a Rust version of a cross-platform backdoor called SysJoker, which is assessed to have been used...
-

 1.8KVulnerabilities
1.8KVulnerabilitiesRussian Cyber Espionage Group Deploys LitterDrifter USB Worm in Targeted Attacks
Russian cyber espionage actors affiliated with the Federal Security Service (FSB) have been observed using a USB propagating worm called LitterDrifter in...
-
 1.8KCyber Attack
1.8KCyber AttackCERT-UA Reports: 11 Ukrainian Telecom Providers Hit by Cyberattacks
The Computer Emergency Response Team of Ukraine (CERT-UA) has revealed that threat actors “interfered” with at least 11 telecommunication service providers in...
-

 2.7KMalware
2.7KMalwareRansomware Attacks Double: Are Companies Prepared for 2024’s Cyber Threats?
Ransomware attacks have only increased in sophistication and capabilities over the past year. From new evasion and anti-analysis techniques to stealthier variants...






