Search results for "Detection"
-
 266Geek
266GeekNew SystemBC malware targets Windows PCs by evading detection
A new Windows malware in Play – SystemBC. While finding and removing malware on your computer system may indeed be a joyous...
-
 212Malware
212MalwarePopular Malware Families Using ‘Process Doppelgänging’ to Evade Detection
The fileless code injection technique called Process Doppelgänging is actively being used by not just one or two but a large number...
-
 244Malware
244MalwareAPT15 Hackers Using Steganography Technique to Drop Okrum Backdoor Via PNG File to Evade Detection
Researchers discovered a previously unseen malware called Okrum that distributed from APT15 threat group via a hidden PNG file with steganography technique to...
-
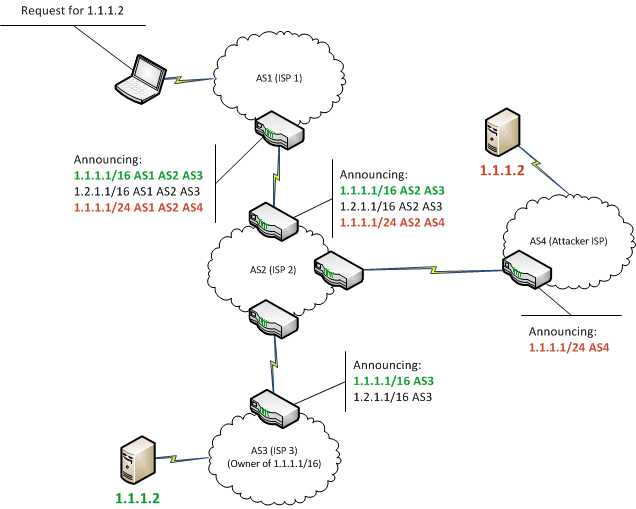
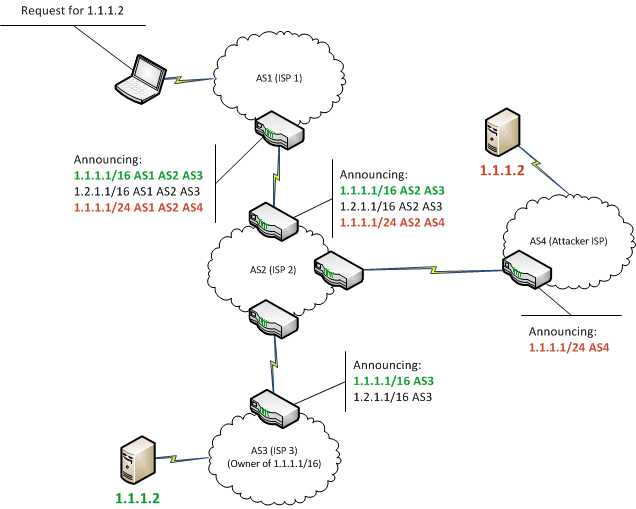 232MITM
232MITMTabi – BGP Hijack Detection Tool
Developed since 2011 for the needs of the French Internet Resilience Observatory, TaBi is a framework that ease the detection of BGP...
-

 262News
262NewsWhat Is a Rootkit? Detection and Prevention
Rootkits are secret computer programs that allow continuous and privileged access to a computer and actively hide its existence. The term rootkit...
-

 352Infosec
352InfosecIntrusion Detection System (IDS) and Its Detailed Working Function – SOC/SIEM
Detection Methods An IDS can only detect an attack. It cannot prevent attacks. In contrast, an IPS prevents attacks by detecting them...
-
 310Malware
310MalwareMuddyWater APT’s BlackWater Malware Campaign Install Backdoor on Victims PC to Gain Remote Access & Evade Detection
Researchers discovered a “Blackwater” malware campaign that suspected to associated with well known MuddyWater APT bypass the security control and install a...
-
 4.5KMalware
4.5KMalwareEmotet Trojan Now Uses IoT And Router Devices To Evade Detection
The Emotet malware has been frequently covered here in Hackercombat since July last year. It is not uncommon for a cyber security-centered...
-

 435Malware
435Malware138 Android Anti Virus Apps are Frauds in Play Store – Only 23 Apps Performed 100% Malware Detection
Recent In-depth analysis against Android Antivirus in Google play store reveals that, 138 Android antivirus products are completely fake and potentially harmful...
-

 207News
207NewsHackers Used Slack To Avoid Network and Endpoint Detection
Notoriety is what hackers thrive on, no matter if it fetches them money or their dirty deeds flash on the news headlines....
-

 395Data Security
395Data SecurityBypass antivirus detection With Phantom Payloads
According to ethical hacking courses, metasploit is the most popular tool used in pentesting. Metasploit tries to find weakness across your local...
-

 237Infosec
237InfosecInsider Threat Detection Software: Protecting Against the Insider Threat – What You Should Know
Insider Threat is one of the dangerous threat actors for many organization and keeping your business protected from outside threats is hard...
-

 332Geek
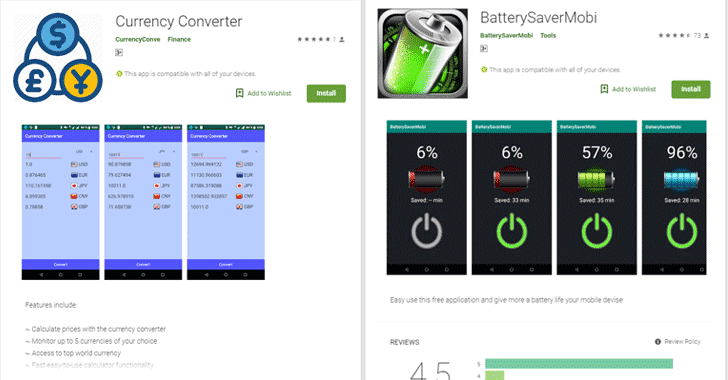
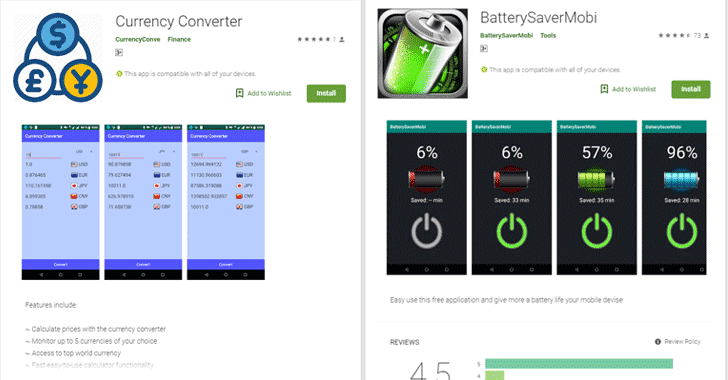
332GeekMalicious apps deploy Anubis banking trojan using motion detection
Google has left no stone unturned in preventing malware and banking trojan from invading the applications uploaded on its official Play Store....
-
 184Articles
184ArticlesNew Android Malware Apps Use Motion Sensor to Evade Detection
Even after so many efforts by Google for preventing its Play Store from malware, shady apps somehow managed to fool its anti-malware...
-

 171Malware
171MalwareMicrosoft Launchs a New Windows machine Malware Detection Competition for $25K Cash Prize
Microsoft launches Malware Detection Competition with AI to test whether the participants AI malware detection models can accurately predict malware from the...
-
 263Vulnerability Analysis
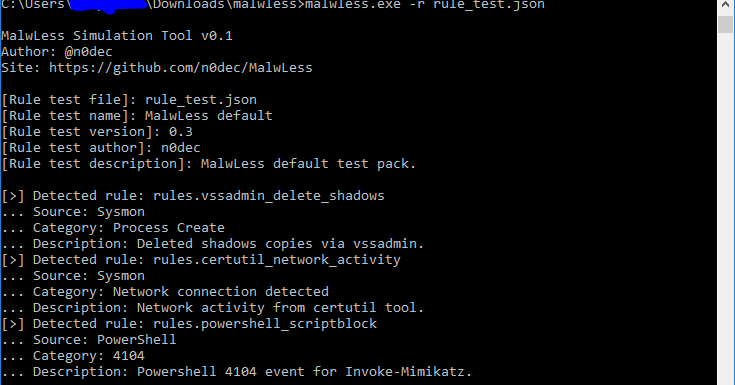
263Vulnerability AnalysisMalwLess – Test Blue Team Detections Without Running Any Attack
MalwLess is an open source tool that allows you to simulate system compromise or attack behaviours without running processes or PoCs. The...
-
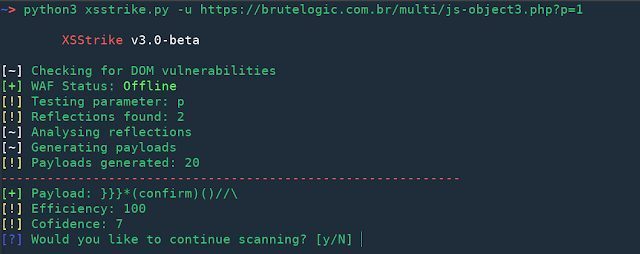
 236Exploitation Tools
236Exploitation ToolsXSStrike v3.0 – Most Advanced XSS Detection Suite
Why XSStrike? Every XSS scanner out there has a list of payloads, they inject the payloads and if the payload is reflected...
-

 260Security Tools
260Security ToolsNameles – Open Source Entropy Based Invalid Traffic Detection And Pre-Bid Filtering
Nameles provides an easy to deploy, scalable IVT detection and filtering solution that is proven to detect at a high level of...
-

 244Evasion & Obfuscation
244Evasion & ObfuscationCoffeeShot: Avoid Detection with Memory Injection
CoffeeShot is an evasion framework that injects payload from Java-based programs into designated processes on Microsoft Windows. It assists blue team members...
-
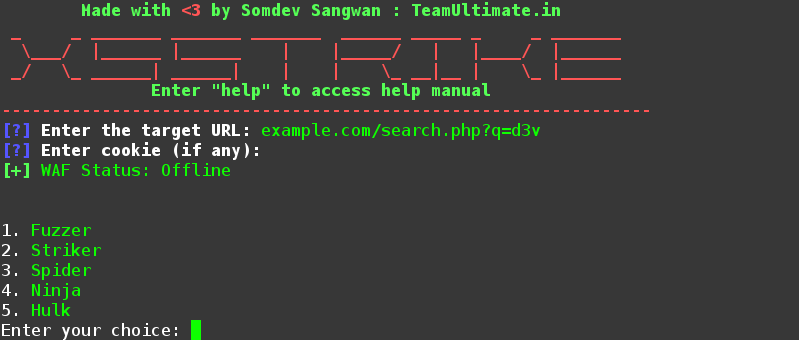
 227Hacking Tools
227Hacking ToolsXSStrike – XSS Detection and Exploitation Suite
XSStrike is an open source tool that detects Cross Site Scripting vulnerabilities and exploits them. The tool is equipped with a powerful...
-

 251Hacking Tools
251Hacking ToolsCMSeek – CMS Detection and Information Gathering
CMSeek is a python tool that is used to detect Content Management System (CMS) within a target website, it can extract useful information...






