Search results for "Distributed"
-

 236Malware
236MalwareGandCrab ransomware distributed by RIG and GrandSoft exploit kits
Late last week saw the appearance of a new ransomware called GandCrab. Surprisingly, it is distributed via two exploit kits: RIG EK...
-

 285Cyber Crime
285Cyber CrimeCan you believe Distributed Grid is Vulnerable to Cyber-attack?
One of the major concerns for the US economy is to deal with Cyber security. The critical infrastructure like the energy system,...
-
 348OSINT
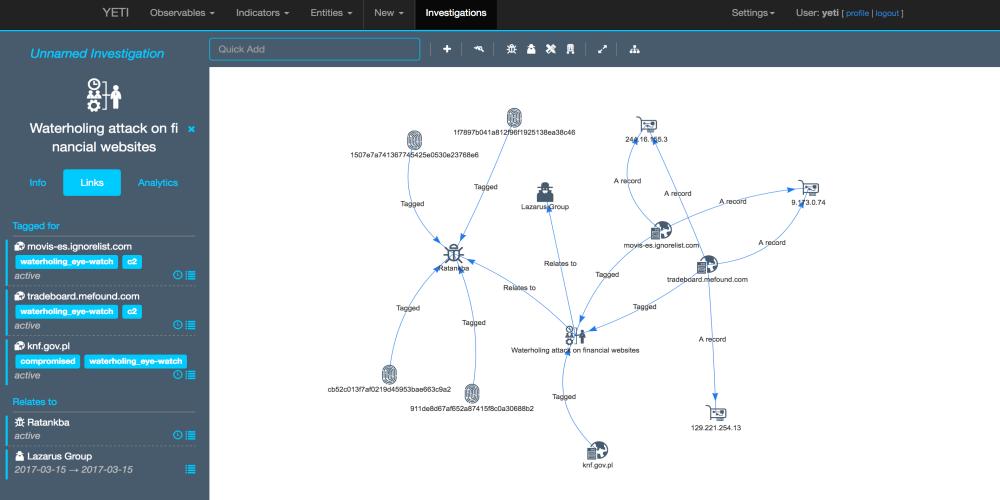
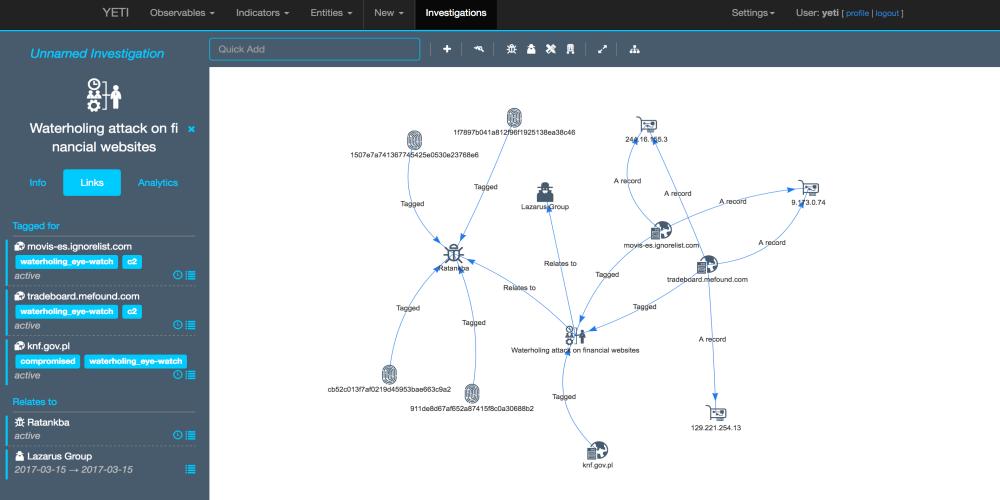
348OSINTYeti – Open Distributed Threat Intelligence
Yeti is a platform meant to organize observables, indicators of compromise, TTPs, and knowledge on threats in a single, unified repository. Yeti...
-

 330Data Security
330Data SecurityPolice distributed malware infected USBs as cybersecurity quiz prizes
The Police are supposed to protect and serve but Taiwanese police in the news for distributing malware-infected USB sticks to the winners of a cybersecurity-related quiz during...
-
 255System Administration
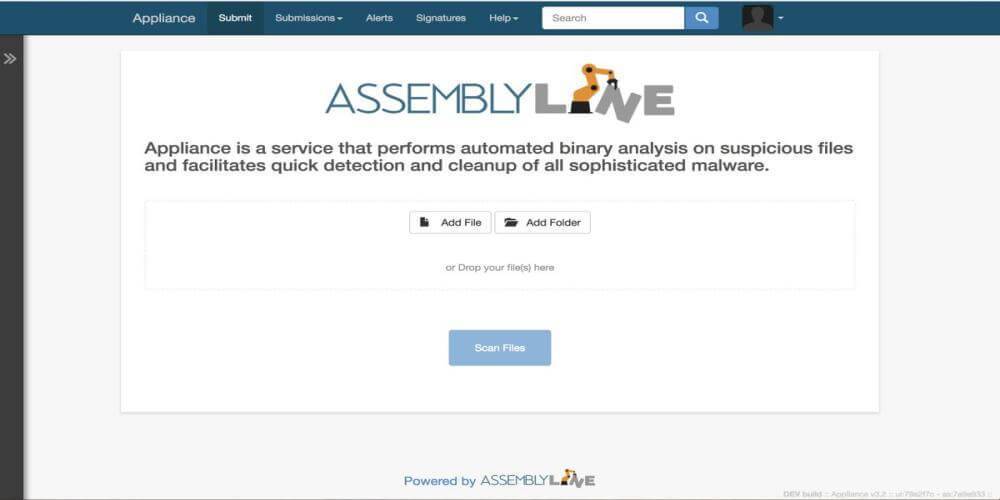
255System AdministrationAssemblyline – Distributed File Analysis Framework
Assemblyline is a scalable distributed file analysis framework. It is designed to process millions of files per day but can also be installed...
-
 257Information Gathering
257Information GatheringScannerl – Modular Distributed Fingerprinting Engine
Scannerl is a modular distributed fingerprinting engine implemented by Kudelski Security. Scannerl can fingerprint thousands of targets on a single host, but can...
-

 322Ransomware
322RansomwareRansomware Back in Action-JAFF Distributed using malicious PDF documents
[jpshare]Ransomware JAFF Back in action this late April, circulating through malicious PDF files.Necurs, one of the biggest botnets, went disconnected amid the...
-
 184Malware
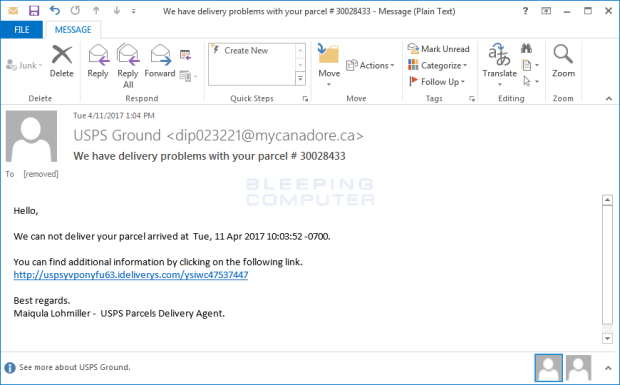
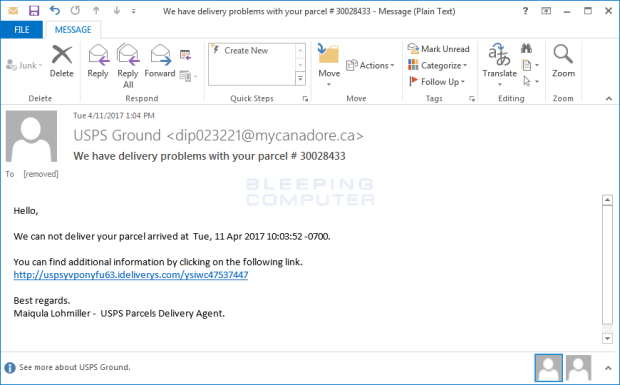
184MalwareMole Ransomware Distributed Through Fake online Word Docs
A new ransomware called Mole was found by security researcher Brad Duncan while he was analyzing a new SPAM campaign. After examining this sample, I feel...
-
 192Data Security
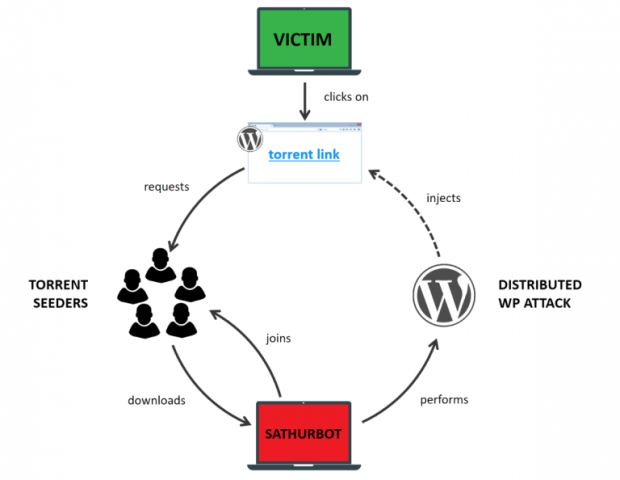
192Data SecuritySathurbot: Distributed WordPress password attack
This article sheds light on the current ecosystem of the Sathurbot backdoor trojan, in particular exposing its use of torrents as a...
-

 188Malware
188MalwareRevenge Ransomware, a CryptoMix Variant, Being Distributed by RIG Exploit Kit
A new CryptoMix, or CryptFile2, variant called Revenge has been discovered by Broad Analysis that is being distributed via the RIG exploit kit. This...
-
 134News
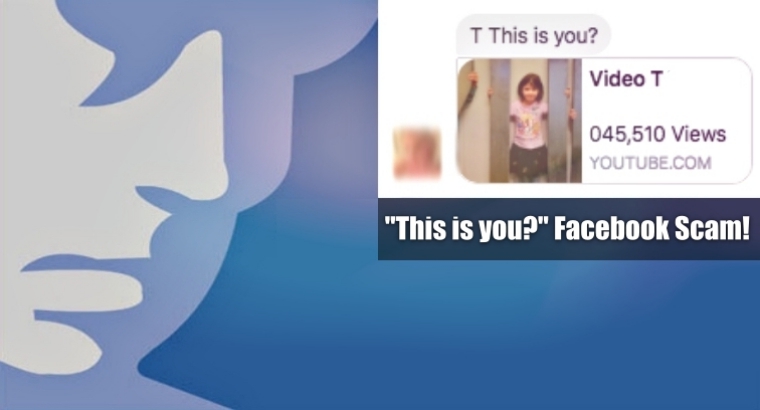
134News“This is you?” message is the latest scam to be distributed via Facebook
Facebook is one of the most used social media platforms in the world, and that makes it an attractive target for cyber...
-

 68Malware
68MalwareResearcher finds the Karma Ransomware being distributed via Pay-per-Install Network
A security researcher named slipstream/RoL has discovered the Karma Ransomware, which pretends to be a Windows optimization program called Windows-TuneUp. What is worse is...
-
DDOS
Distributed Denial Of Service attacks has doubled over the last 12 months as per the Akamai’s second quarter 2016 state of the internet / security report
Akamai Technologies, Inc. (NASDAQ: AKAM), the global leader in content delivery network (CDN) services, today released its Second Quarter, 2016 State of...
-
 191Vulnerabilities
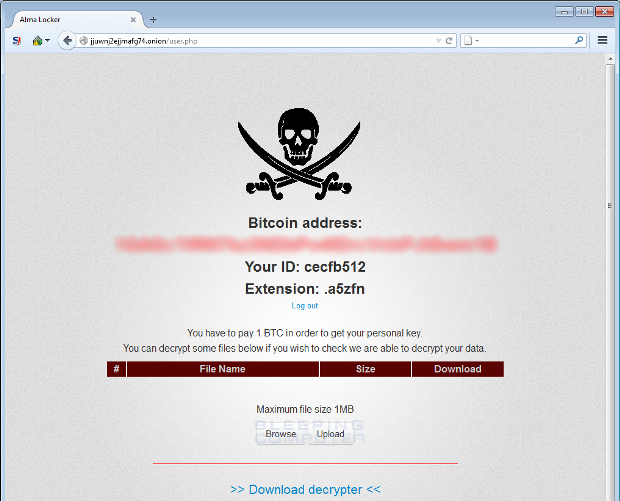
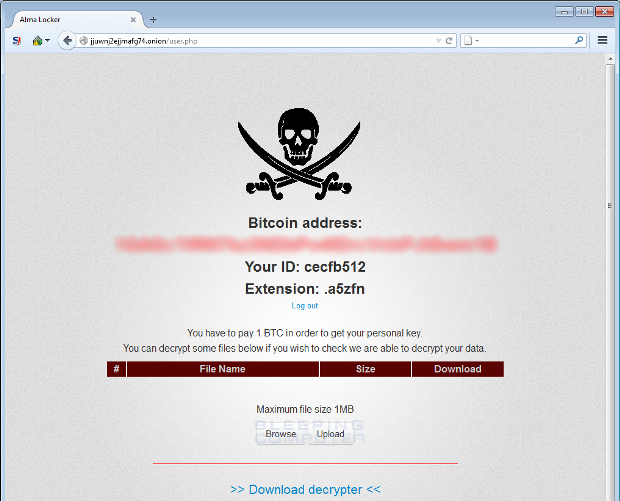
191VulnerabilitiesNew Alma Locker Ransomware being distributed via the RIG Exploit Kit
A new ransomware called Alma Locker has been discovered by Proofpoint researcher Darien Huss that encrypts a victim’s data and then demands a ransom of 1...
-

 114Data Security
114Data SecurityNext-gen Tor to use distributed RNG, 55-character addresses
Numbers so random no one can predict how random they’ll be. The Tor project has cooked up a new way to generate random...






