Search results for "Exploitation"
-

 2.6KHack Tools
2.6KHack ToolsFDsploit: File Inclusion & Directory Traversal fuzzing, enumeration & exploitation tool
FDsploit FDsploit is a File inclusion & Directory Traversal fuzzer, enumeration & exploitation tool. Features The LFI-shell interface provides only the output...
-

 408Exploitation Tools
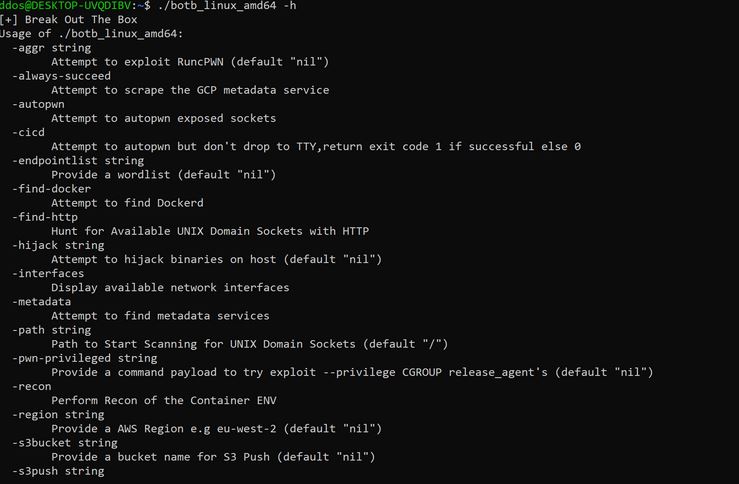
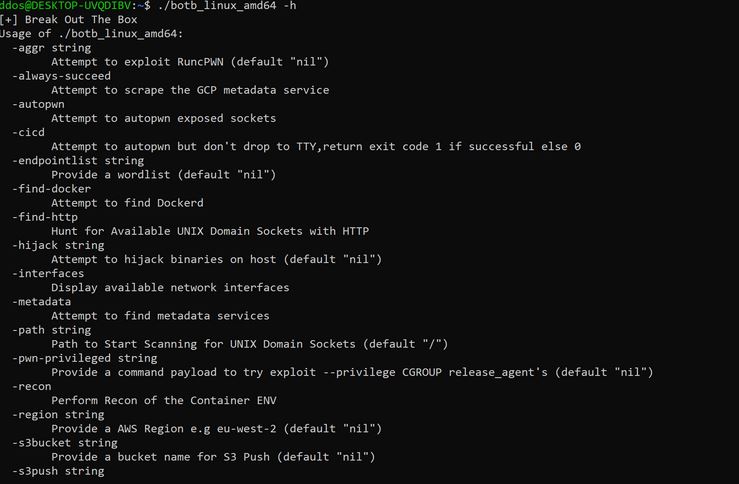
408Exploitation ToolsBotb – A Container Analysis And Exploitation Tool
BOtB is a container analysis and exploitation tool designed to be used by pentesters and engineers while also being CI/CD friendly...
-
 689Hacking Tools
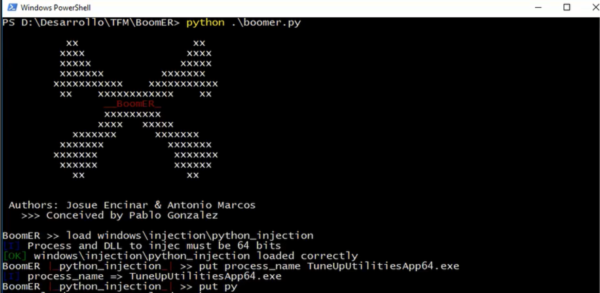
689Hacking ToolsBoomER | An Open Source Post-Exploitation Tool To Exploit Local Vulnerabilities
BoomER is a Command-line interface python open-source framework fully developed in Python 3.X for post-exploitation of targets with the objective to exploit...
-
 348Post Exploitation
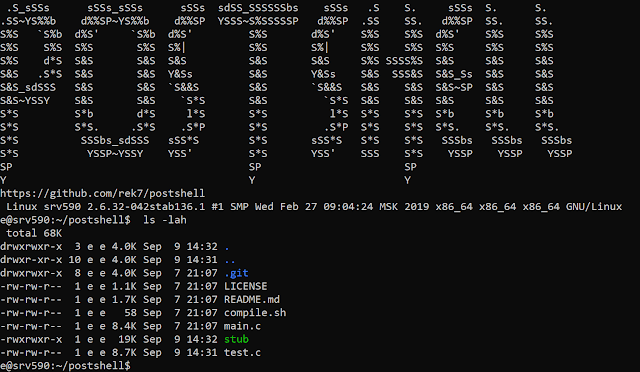
348Post ExploitationPostShell – Post Exploitation Bind/Backconnect Shell
PostShell is a post-exploitation shell that includes both a bind and a back connect shell. It creates a fully interactive TTY...
-
 408Exploitation
408ExploitationBotB – A container analysis and exploitation tool for pentesters and engineers.
BOtB (Break out the Box) is a container analysis and exploitation tool designed to be used by pentesters and engineers while also...
-
 458Hacking Tools
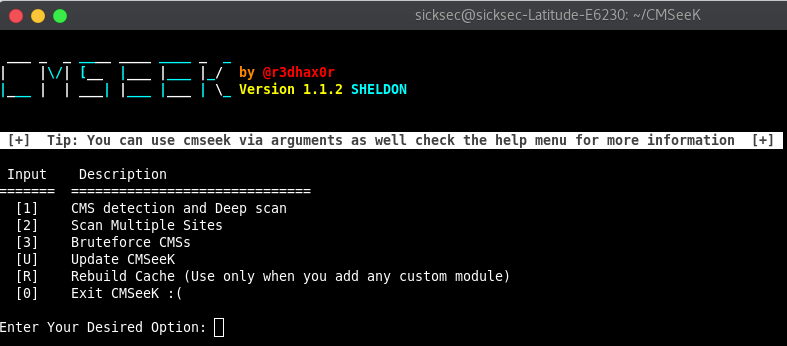
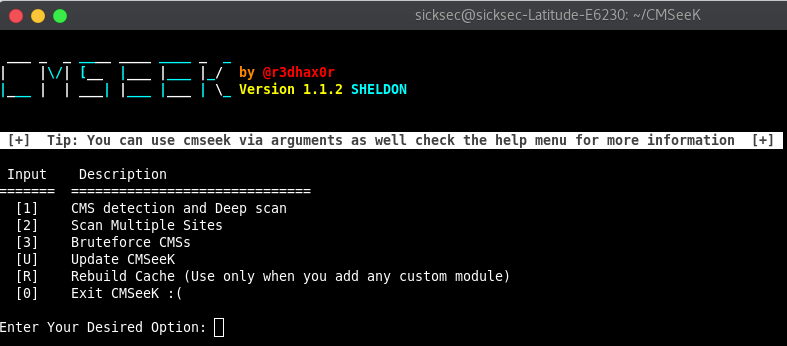
458Hacking ToolsCMSeeK | An Open Source Content Management System Detection and Exploitation Tool
CMSeek is an open-source tool that analyzes the regex of websites in order to detect flaws and content management system used like...
-
 266Exploitation
266ExploitationTheo – Ethereum Recon and Exploitation Tool
Theo aims to be an exploitation framework and a blockchain recon and interaction tool. Features: Automatic smart contract scanning which generates a...
-

 385Hacking Tools
385Hacking ToolsTheFatRat – A Convenient Exploitation Tool
TheFatRat is an easy to use tool which helps in generating backdoors, system exploitation, post exploitation attacks, browser attacks, DLL files, FUD...
-
 475Hacking Tools
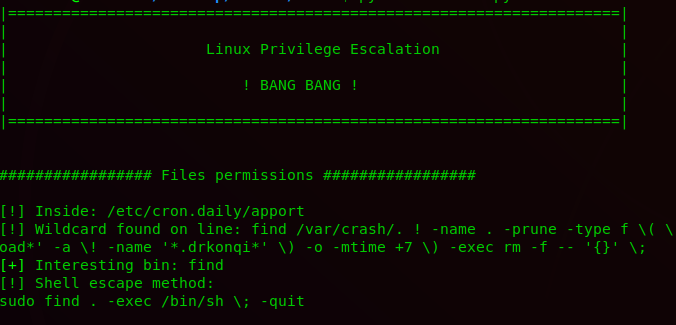
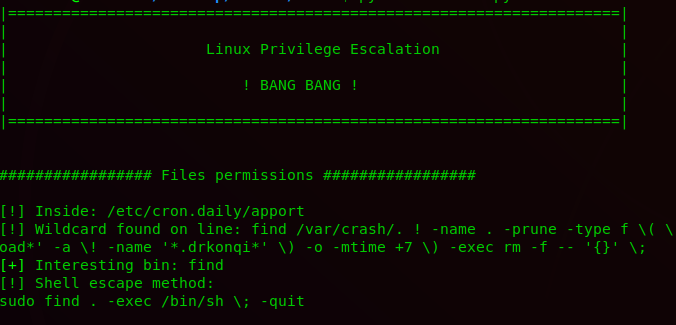
475Hacking ToolsBeRoot – A Post Exploitation Privilege Escalation Tool
BeRoot is a post-exploitation tool to check for common misconfigurations which can allow an attacker to escalate their privileges. The main goal...
-
 485Repositories
485RepositoriesLinux Kernel Exploitation Repository
A bunch of resources related to Linux kernel exploitation. Exploitation techniques 2019: “Leak kernel pointer by exploiting uninitialized uses in Linux kernel”...
-
 267Hack Tools
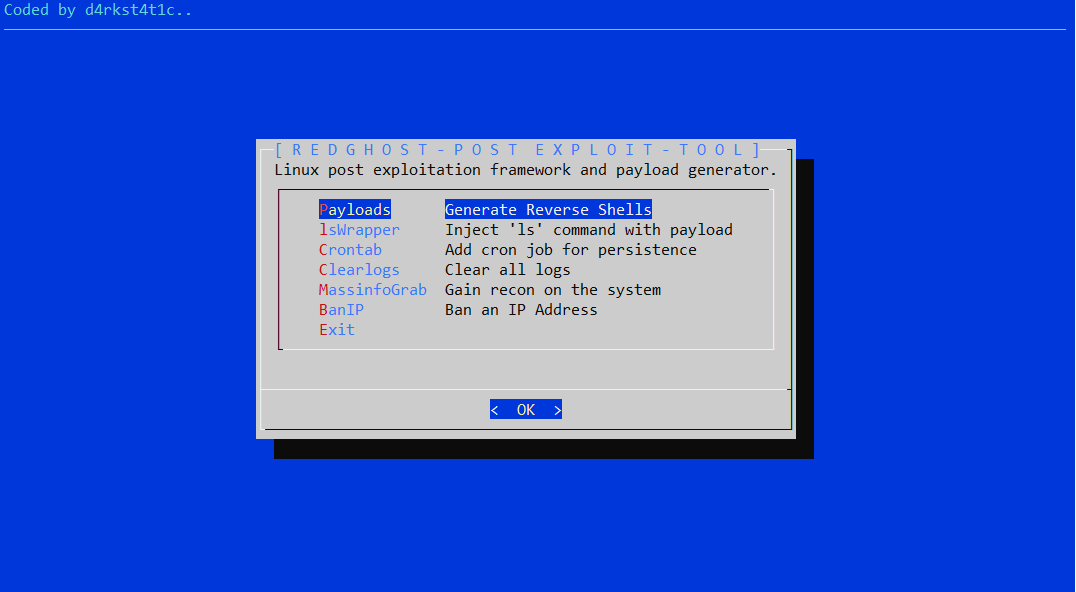
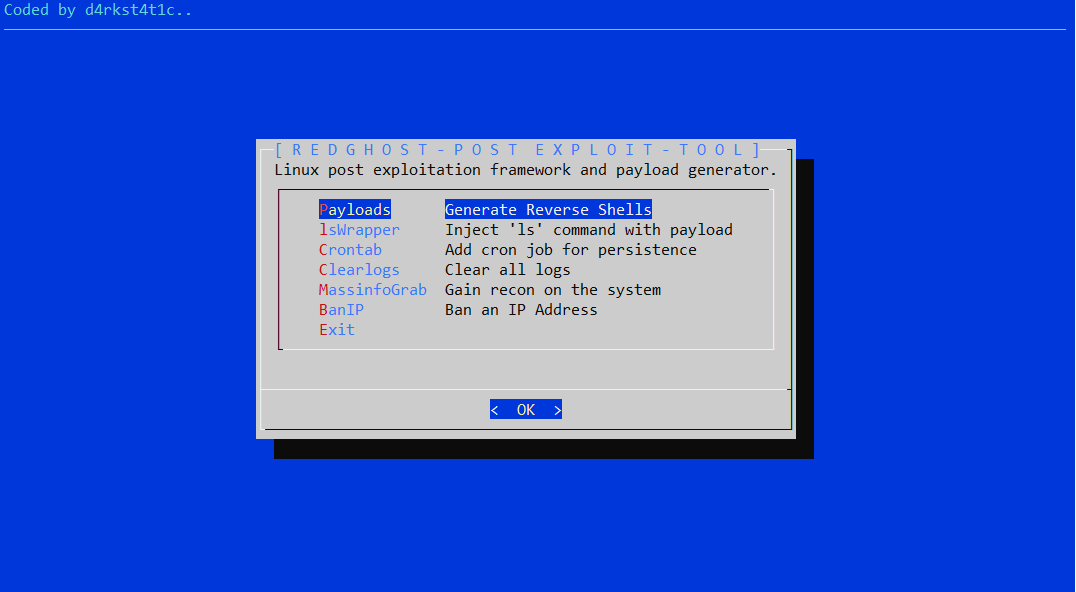
267Hack ToolsRedGhost – Linux Post Exploitation Framework
Linux post exploitation framework designed to assist red teams in gaining persistence, reconnaissance and leaving no trace. RedGhost Features Payloads Function to...
-

 203Hack Tools
203Hack ToolsPacu – AWS Exploitation Framework
Pacu is an open source AWS exploitation framework created and maintained by Rhino Security Labs to assist in offensive security testing against...
-

 329Hack Tools
329Hack ToolsBeemka – Electron Exploitation Toolkit
Beemka shows how vulnerabilities in the Electron Framework could allow an attacker to inject malicious code inside a legitimate application without raising...
-
 319Hack Tools
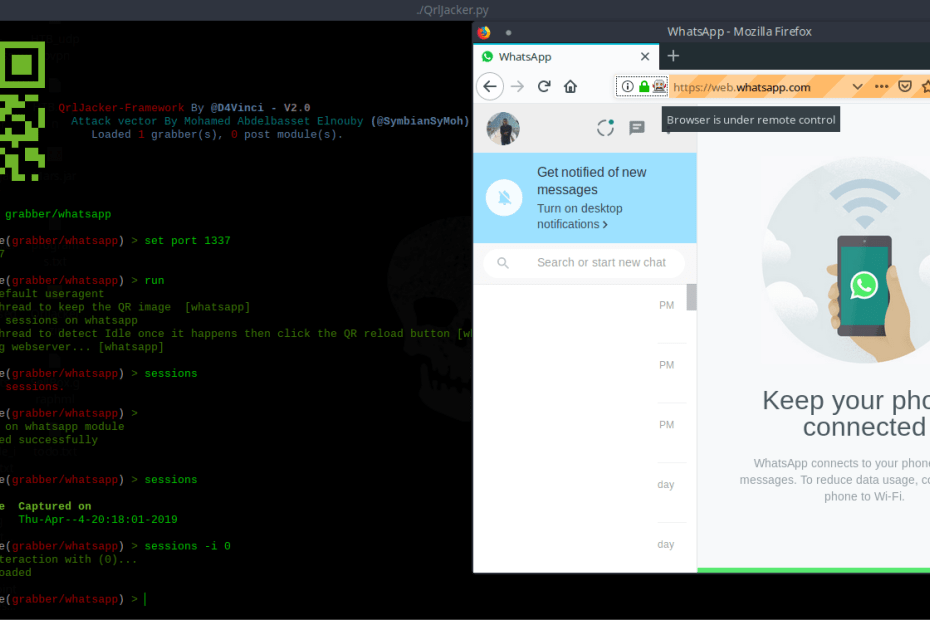
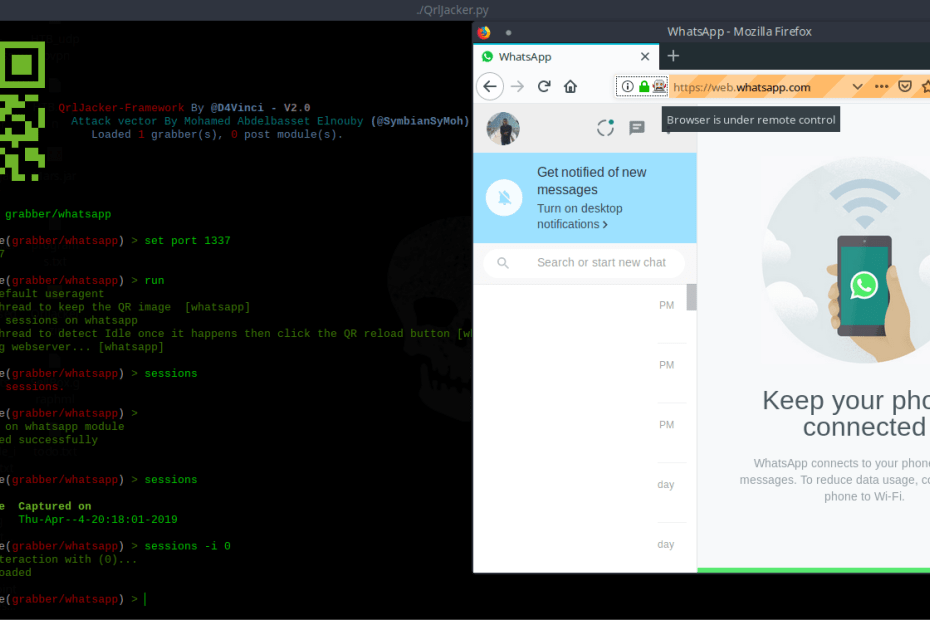
319Hack ToolsQRLJacker v2.0 – QRLJacking Exploitation Framework
QRLJacking or Quick Response Code Login Jacking is a simple-but-nasty attack vector affecting all the applications that relays on “Login with QR...
-
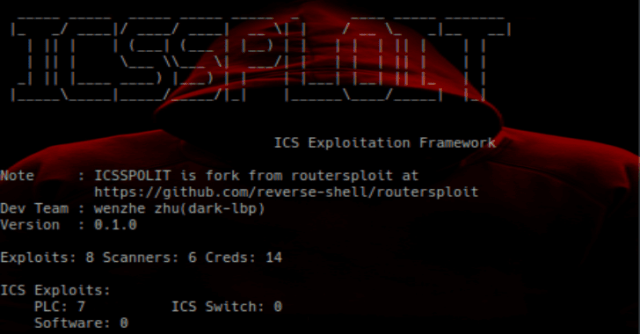
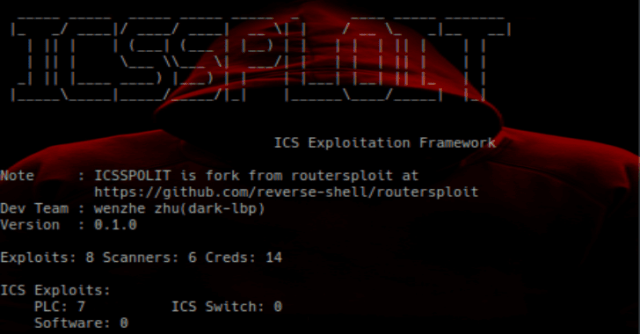 318Hack Tools
318Hack ToolsISF – Industrial Control System Exploitation Framework
ISF(Industrial Exploitation Framework) is a exploitation framework based on Python, it’s similar to metasploit framework. ICS Protocol Clients Name Path Description modbus_tcp_client...
-

 306Hack Tools
306Hack ToolsZeebsploit – Web Scanner, Exploitation and Information Gathering Framework
zeebsploit is a tool for hacking, searching web information and scanning vulnerabilities on the web. Installation $ apt-get install git python $...
-
 333Infosec
333InfosecMalicious Payload Evasion Techniques with Advanced Exploitation Frameworks
Sophisticated threats are Evolving with much more advanced capabilities and giving more pain for analysis even evade the advanced security software such...
-

 294Fuzzing
294FuzzingSSRFmap – Automatic SSRF Fuzzer And Exploitation Tool
SSRF are often used to leverage actions on other services, this framework aims to find and exploit these services easily. SSRFmap takes...
-
 228Exploitation Tools
228Exploitation ToolsXSRFProbe – The Prime Cross Site Request Forgery Audit And Exploitation Toolkit
XSRFProbe is an advanced Cross Site Request Forgery (CSRF/XSRF) Audit and Exploitation Toolkit. Equipped with a Powerful Crawling Engine and Numerous Systematic...
-

 312Hack Tools
312Hack ToolsScavenger – A Post-Exploitation Scanning/Mapping Tool
SCAVENGER is a multi-threaded post-exploitation scanning tool for mapping systems and finding “interesting” and most frequently used files, folders and services. Once...
-
 200eBooks
200eBooksMobile Device Exploitation Cookbook
Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to...






