Search results for "Forensic"
-
 303Forensics Tools
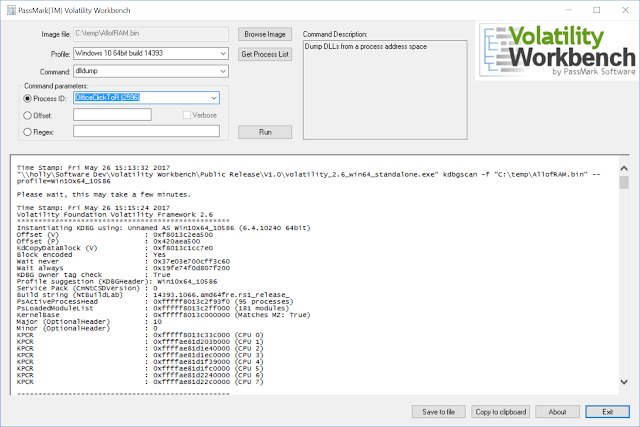
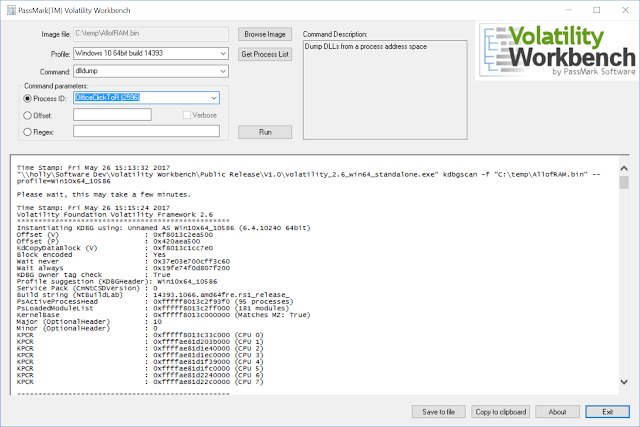
303Forensics ToolsVolatility Workbench – A GUI For Volatility Memory Forensics
Volatility Workbench is a graphical user interface (GUI) for the Volatility tool. Volatility is a command line memory analysis and forensics tool...
-
 412Tutorials
412TutorialsBest forensic tools to hide secrets passwords and recover files
Steganography is common term which is used in hiding or encrypting any personal information. The information can be anything which you don’t...
-
 207eBooks
207eBookscomputer hacking forensic investigator
Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to...
-
 225eBooks
225eBooksHacking Exposed Computer Forensics,2nd edition
Disclaimer The contributor(s) cannot be held responsible for any misuse of the data. This repository is just a collection of URLs to...
-

 274Pentest Linux Distributions
274Pentest Linux DistributionsCAINE 10.0 – GNU/Linux Live Distribution For Digital Forensics Project, Windows Side Forensics And Incident Response
CAINE (Computer Aided INvestigative Environment) is an Italian GNU/Linux live distribution created as a Digital Forensics project. Currently, the project manager is Nanni Bassetti...
-

 255Data Security
255Data SecurityHow to become an expert in digital forensics
A review of the interesting work of the experts in digital forensics What exactly does a professional in digital forensics do? In general, experts in digital forensics are computer detectives that...
-

 303Cyber Crime
303Cyber CrimeWindows-based Forensic Tools Available for Everyone
Forensic investigations became the “new normal”, as cybercriminals increased their activities at the expense of users and businesses alike. It is sad...
-
 293Forensics Tools
293Forensics ToolsHindsight – Internet History Forensics For Google Chrome/Chromium
Hindsight is a free tool for analyzing web artifacts. It started with the browsing history of the Google Chrome web browser and...
-
 236Computer Forensics
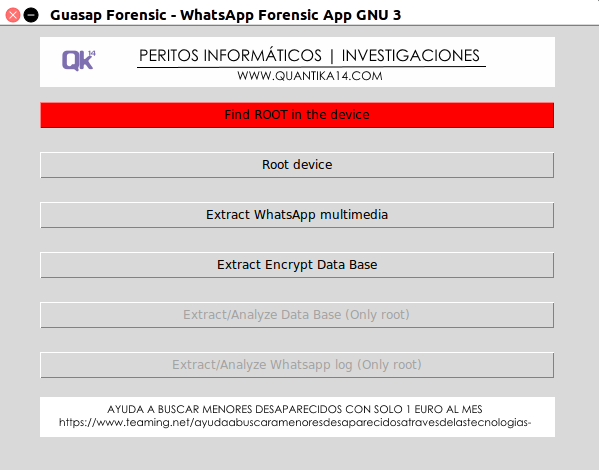
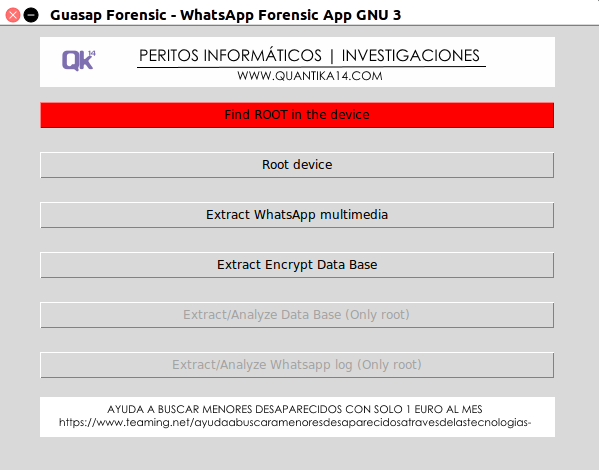
236Computer ForensicsGuasap – WhatsApp Forensic Tool
The Guasap Forensic implemented in Python under the GNU General Public License, for the extraction and analysis of files, data bases and...
-
 269Information Gathering
269Information GatheringGuasap – WhatsApp Forensic Tool
The Guasap Forensic implemented in Python under the GNU General Public License, for the extraction and analysis of files, data bases and...
-

 323Geek
323GeekTop 7 Most Popular and Best Cyber Forensics Tools
We often watch experts in movies using forensic tools for their investigations but what cyber forensic tools are used by experts? Well,...
-
 150Data Security
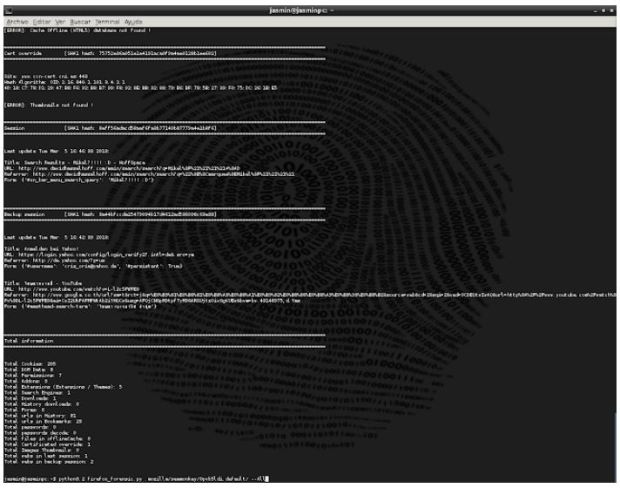
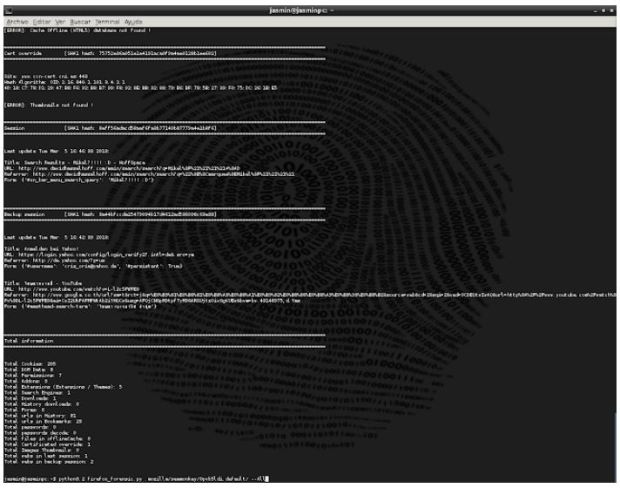
150Data SecurityExtract Forensic Information of Browsers with this Tool Dumpzilla
A team of security experts explained; that this application, Dumpzilla, is developed in Python 3.x and is used with the aim of...
-
 204Data Security
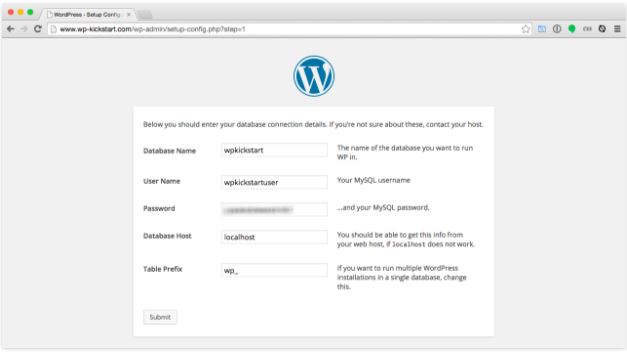
204Data SecurityForensics report of WordPress hacked site
This post details the forensics performed by Information security trainingprofessional during the clean-up operation. The expert also note specific WordPress security recommendations based...
-
 390Computer Forensics
390Computer ForensicsLive Forensics Analysis with Computer Volatile Memory
The field of computer Forensics Analysis involves identifying, extracting, documenting, and preserving information that is stored or transmitted in electronic or magnetic...
-
 295Computer Forensics
295Computer Forensicsusbkill – An Anti-Forensic Kill Switch
usbkill is an anti-forensic kill-switch that waits for a change on your USB ports and then immediately shuts down your computer. To run:...
-

 403Computer Forensics
403Computer ForensicsTop 7 Cyber Forensic Tools
We often watch experts in movies using forensic tools for their investigations but what cyber forensic tools are used by experts? Well,...
-
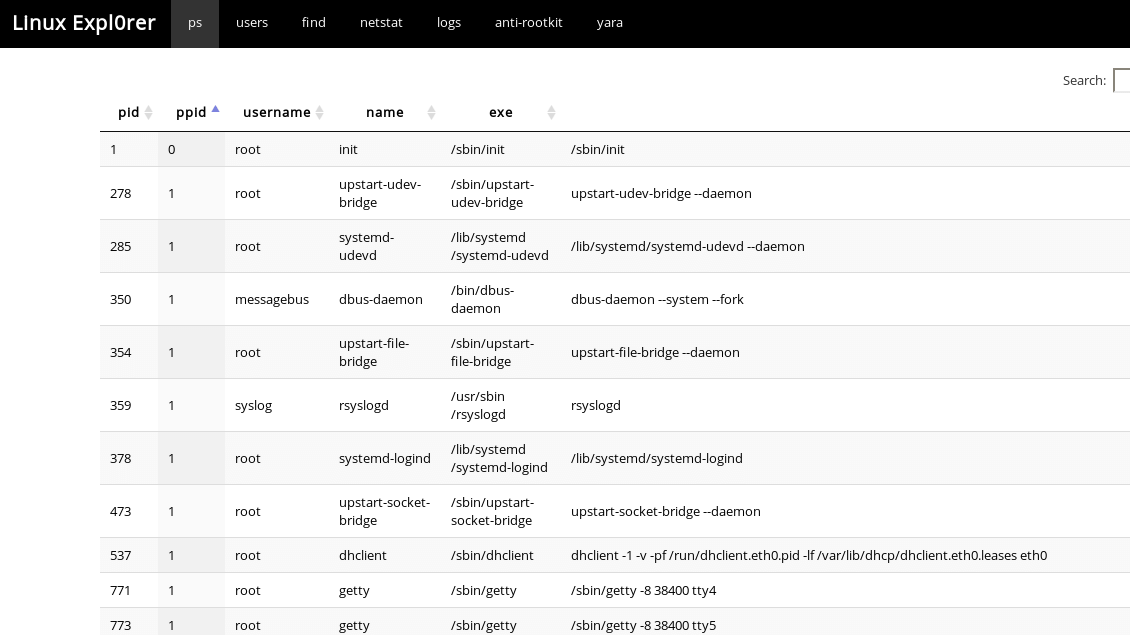
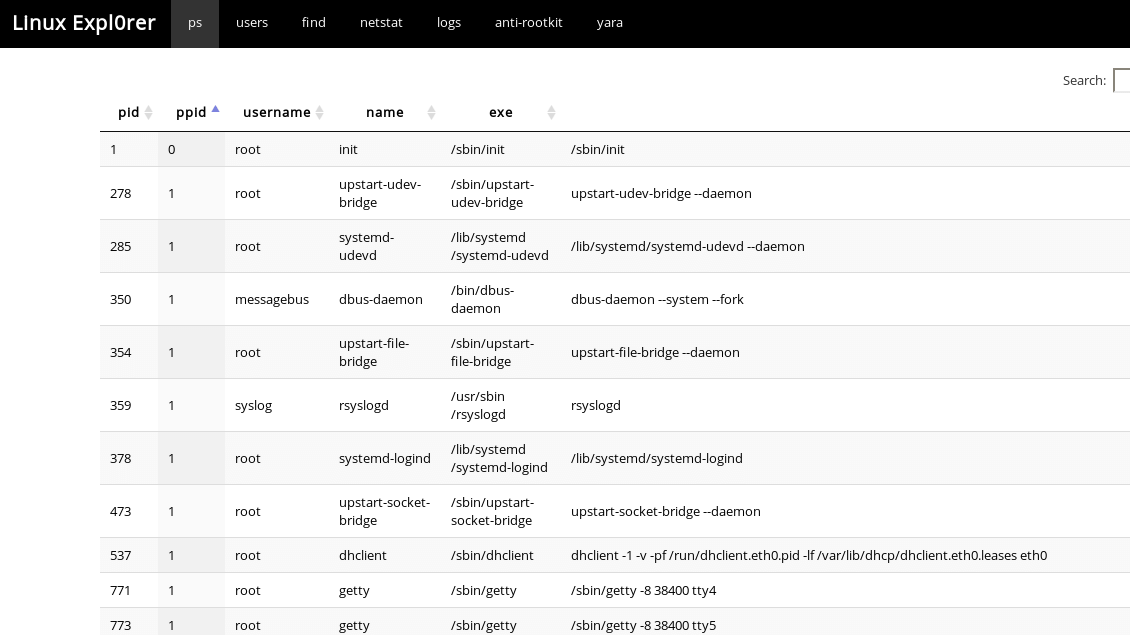 309Forensics Tools
309Forensics ToolsLinux Expl0rer – Easy-To-Use Live Forensics Toolbox For Linux Endpoints
Easy-to-use live forensics toolbox for Linux endpoints written in Python & Flask. Capabilities ps View full process list Inspect process memory map...
-
 211Malware
211MalwareProcess Doppelgänging Attack Works on all version of Windows Evade AV products and Forensics tools
Security researchers from Endpoint Security firm Ensilo discovered a new Evasion technique dubbed Process Doppelgänging which works with all the versions of...
-

 429Malware
429MalwareESET malware researchers awarded prize in open‑source memory forensics competition
The Volatility Foundation, the non-profit organization behind the Volatility Framework, sponsors the yearly Volatility Plugin Contest to acknowledge the best forensic tools...
-
 231Computer Forensics
231Computer ForensicsAutopsy – A Digital Forensic Tool
The Autopsy is a forensic tool which is used by the military, law enforcement, and corporate examiners to investigate what had happened...
-
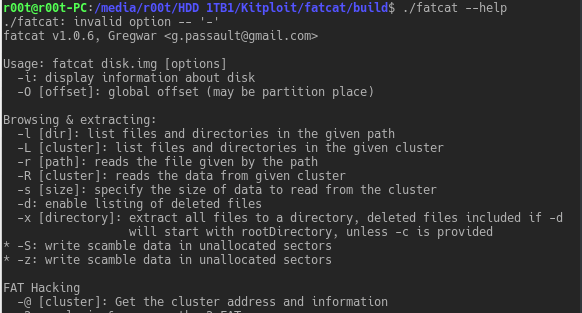
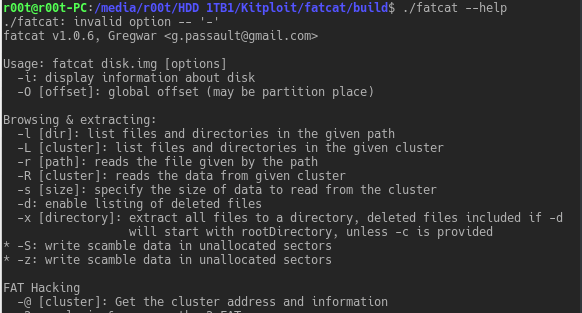 260Forensics Tools
260Forensics Toolsfatcat – FAT Filesystems Explore, Extract, Repair, And Forensic Tool
This tool is designed to manipulate FAT filesystems, in order to explore, extract, repair, recover and forensic them. It currently supports FAT12,...






