Search results for "Hacking"
-

 306News
306News10 Most Notorious Hacking Groups
Here are top 10 hacking and hacktivist groups that changed the world like no one else. Hacking has grown massively in the...
-
 400News
400NewsRe-Booted Hell Hacking Forum on Dark Web Hacks Car Breathalyzers Manufactures
It has now been proven that almost anyone and any company can get hacked including the firm that manufactures car breathalyzers. A...
-

 100Cyber Crime
100Cyber CrimeWhat does Fitbit hacking mean for wearables and IoT?
Wearable activity tracking devices like those made by Fitbit were one of the hottest gifts this past holiday season and it appears...
-

 89Data Security
89Data SecurityApple, Google, Microsoft attack government hacking plans
Tech industry hits back at plans to create legal framework for hacking by spies, military and police. Tech companies including Apple, Microsoft,...
-

 173Data Security
173Data SecurityThe Dark Web Hacking Forum ‘Hell’ Has Returned Online
Look who’s back? The Dark Web Hacking Forum ‘Hell’ Just months after users speculated that the infamous dark web hacking forum, ‘Hell’ was...
-

 279Incidents
279IncidentsDHS: Drug Traffickers are hacking surveillance drones on the border
The U.S. Department of Homeland Security and local law enforcement confirmed that Drug Traffickers are hacking surveillance drones on the border. Small...
-

 235Incidents
235IncidentsGCHQ admits for the first time to ‘persistent’ hacking in the UK and abroad
The UK’s digital spy agency, GCHQ, has admitted for the first time in court that it hacks computers, smartphones, and networks in the...
-
 94Data Security
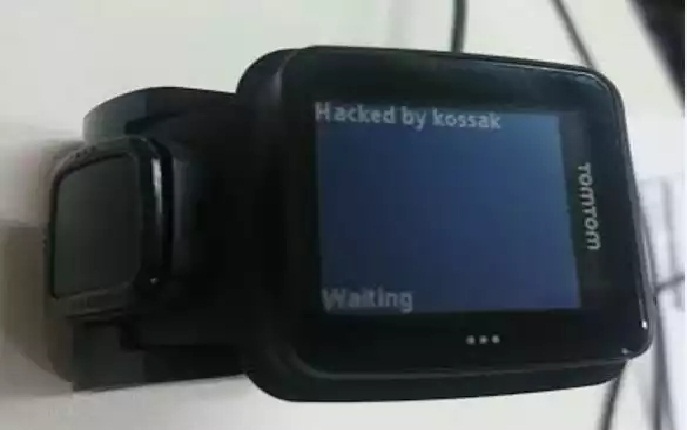
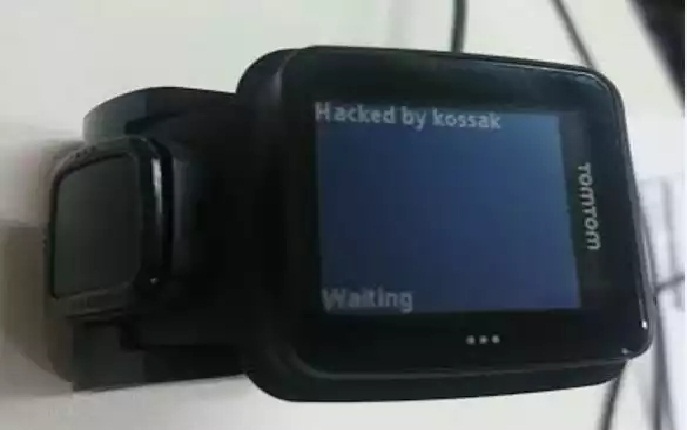
94Data SecurityHacking Smartwatches – the TomTom Runner
I intended originally for this series to contain only three posts, and in order to achieve that, this post is longer than...
-

 141Hacked
141HackedMedical Devices Ransomware Is The Biggest Hacking Threat of 2016
Short Bytes: As we are making progress on the front of online security, the cybercriminals are competing head-to-head to target every device connected...
-

 286Hacked
286HackedAnonymous Now Plans to Start Offensive Hacking To Kill ISIS Online
Short Bytes: After facing backlash over the “wildly inaccurate” accounts reported to Twitter, Anonymous has decided to switch to their area of...
-

 102Data Security
102Data Security‘Spying’ on Islamic State instead of hacking them
In the wake of the Paris attacks, the vigilante hacker group Anonymous has declared war on so-called Islamic State using the internet...
-
 188Data Security
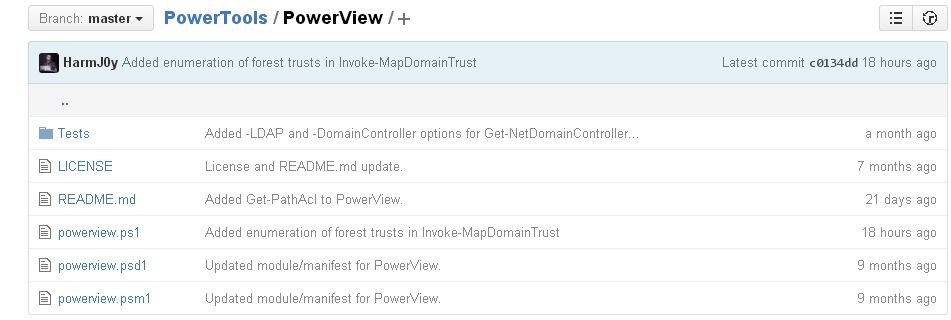
188Data SecurityHacking and exploiting Active Directory Permissions
PowerView is a PowerShell tool to achieve network information on Windows domains for cyber security services and ethical hacking training professionals. It...
-
 192News
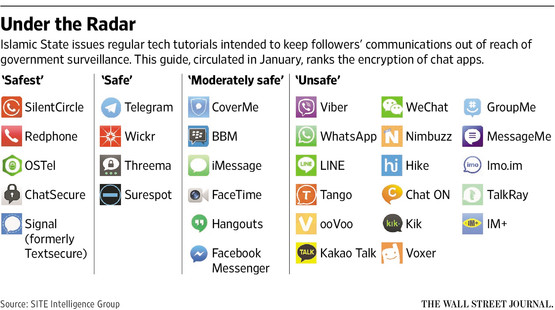
192NewsISIS issues anti-hacking guidelines for its online supports after Anonymous threats
After calling Anonymous ‘Idiots’ ISIS issues guidelines to its cronies to protect from hackers like Anonymous The Islamic State militant ISIL who...
-

 156Data Security
156Data SecurityCSI: CYBER SOMEHOW DIDN’T GET CAR HACKING TOTALLY WRONGCSI: CYBER SOMEHOW DIDN’T GET CAR HACKING TOTALLY WRONG
CSI: Cyber is known more for absurd drama than technical coherence, but it’s a big deal that hacking’s become so visible that...
-

 74Cyber Crime
74Cyber Crime7 things you need to know about car hacking
Car hacking may sound like something out of the latest Die Hard or James Bond film, but it’s newsworthy, real and likely...
-
 107Data Security
107Data SecurityThe Infernal-Twin tool, easy hacking wireless networks
The Infernal-Twin is an automated tool designed for penetration testing activities, it has been developed to automate the Evil Twin Attack. The Infernal-Twin...
-

 348Hacked
348HackedHackers Win $1 Million Bounty for Remotely Hacking iPhones Running iOS 9
Short Bytes: Zerodium’s million dollar iOS 9 jailbreak bounty program has expired and it has resulted in a new iOS jailbreak. But,...
-

 328Vulnerabilities
328VulnerabilitiesHow to Build a Portable Hacking Station with a Raspberry Pi and Kali Linux
Cracking Wi-Fi passwords, spoofing accounts, and testing networks for exploits is all fun enough, but if you want to take the...
-

 138Cyber Crime
138Cyber CrimeThe great car hacking debate
Can cars be hacked remotely or is the idea of remotely hackable cars still only a hypothetical threat? Evidence is presented to...
-

 279Hacked
279HackedWhich Antivirus Software Protect Themselves From Hacking Attacks?
Short Bytes: Even though the number of users aware about the basic security practices is increasing day-by-day, most of us are unaware...
-

 244Hacked
244Hacked15-year-old Boy Arrested Over the TalkTalk Hacking Attack
Short Bytes: A 15-year-old has been arrested in Northern Ireland in connection with the cyber-attack on the TalkTalk’s website. This news of 15-year-old...






