Search results for "Injection"
-

 2.1KVulnerabilities
2.1KVulnerabilitiesCritical remote code injection and DoS vulnerabilities in Juniper’s Junos OS. Secure your network
Cybersecurity specialists report the discovery of a remote code execution (CER) vulnerability in the Steel-Belted Radius (SBR) Carrier Edition, a device developed...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesUnpatched zero-day argument injection vulnerability in the open source text editor Etherpad. Don’t open any unknown file
Cybersecurity specialists reported the detection of at least two vulnerabilities in Etherpad, a popular online text editor. According to the report, the...
-

 4.8KVulnerabilities
4.8KVulnerabilitiesCVE-2021-20026: Command injection vulnerability residing in SonicWall Network Security Manager patched. Update now
Nikita Abramov, a researcher at security firm Positive Technologies, issued an alert regarding CVE-2021-20026, a command injection vulnerability in Network Security Manager...
-

 1.4KVulnerabilities
1.4KVulnerabilitiesSQL injection, deserialization and other remotely exploitable vulnerabilities in Red Hat JBoss Web Server
Cybersecurity specialists report the detection of at least four critical vulnerabilities in JBoss Web Server, the open source Java EE application server...
-
 2.8KVulnerabilities
2.8KVulnerabilitiesBuffer overflow and code injection vulnerabilities in CODESYS
Cybersecurity specialists reported the finding of at least 4 critical vulnerabilities in CODESYS V2 Runtime Toolkit, a set of tools for CODESYS,...
-

 802Vulnerabilities
802VulnerabilitiesDangerous input validation and code injection vulnerabilities in PHPMailer. Patch now
Cybersecurity specialists reported the detection of at least two security vulnerabilities in PHPMailer, the popular code library to send emails securely via...
-

 4.9KTutorials
4.9KTutorialsAutomating SQL Injection Attacks with LAZYSQLMAP. Test Your Web Application Security
This time, information security experts from the International Institute of Cyber Security (IICS) will show you how to use LazySQLMap, a tool...
-
 492Hack Tools
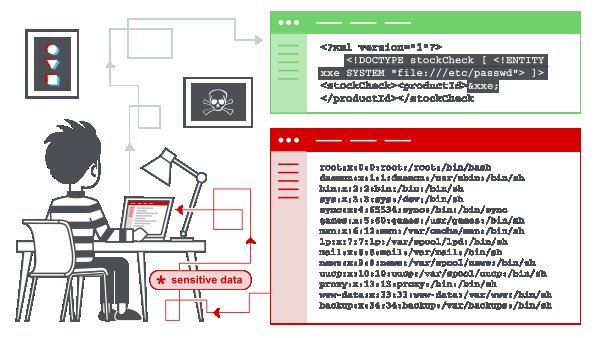
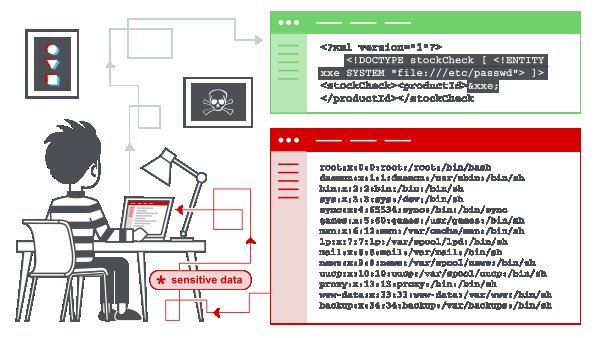
492Hack ToolsXML External Entity (XXE) Injection Payload List
In this section, we’ll explain what XML external entity injection is, describe some common examples, explain how to find and exploit various...
-

 3.4KVulnerabilities
3.4KVulnerabilitiesCritical SQL injection vulnerability affecting phpMyAdmin
Vulnerability testing specialists reported the finding of a security flaw in phpMyAdmin, one of the world’s most widely used MySQL database management...
-
 2.2KHack Tools
2.2KHack ToolsSQL Injection Payload List
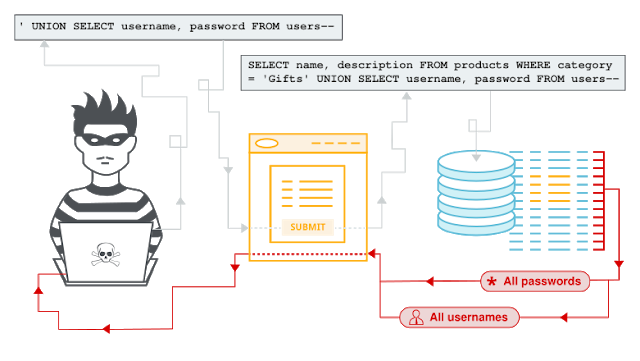
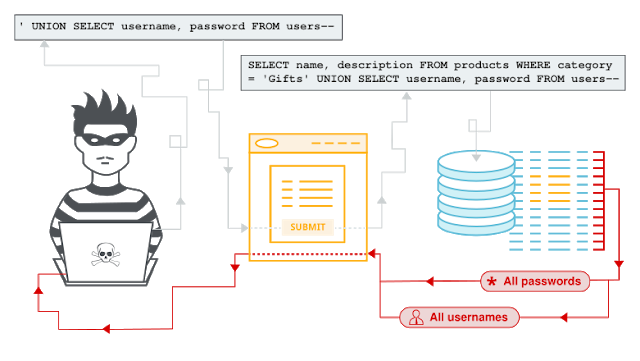
SQL InjectionIn this section, we’ll explain what SQL injection is, describe some common examples, explain how to find and exploit various kinds...
-
 706Hack Tools
706Hack ToolsAndor – Blind SQL Injection Tool With Golang
Blind SQL Injection Tool with Golang.UsageDownload andor.go and go to the folder where the file andor.go located. And type this to command...
-
 2.8KPrivilege Escalation
2.8KPrivilege EscalationTikiTorch – Process Injection Tool
TikiTorch was named in homage to CACTUSTORCH by Vincent Yiu. The basic concept of CACTUSTORCH is that it spawns a new process,...
-
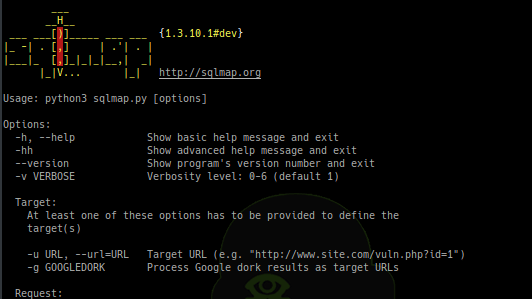
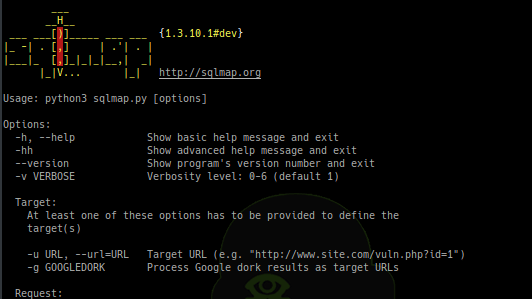 482Exploitation Tools
482Exploitation ToolsSQLMap v1.3.10 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking...
-

 367Vulnerabilities
367VulnerabilitiesCritical SQL injection vulnerability in a Starbucks enterprise database
A website security specialist dedicated to the bug reporting helped fix a critical SQL injection flaw affecting an enterprise database in the...
-

 447News
447NewsFacebook has Sued Two App Developers for Click Injection Fraud Using Facebook Ads
Today, Facebook has documented a complaint against two developers to click injection fraud. The developers have created apps available in the Google...
-
 432Infosec
432InfosecNew Google Dorks List Collection for SQL Injection – SQL Dorks 2019
Google helps you with Google Dorks to find Vulnerable Websites that Indexed in Google Search Results. Here is the latest collection of...
-

 287News
287NewsProtect Your WordPress Website from SQL Injection
WordPress websites need to be protected against SQL injection threats. SQL (Structured Query Language) is a widely used database language, a domain...
-
 309Vulnerabilities
309VulnerabilitiesCritical SQL injection vulnerability in Magento; update please
Magento, an Adobe-owned platform, announced the launching of an update patch to correct some critical SQL injection vulnerabilities; according to the authors...
-
 493Pentest
493PentestHow to Perform Manual SQL Injection While Pentesting With Single quote Error Based Parenthesis Method
If you are trying to hack the databases with methods like single quotes error based injection, Integer based injection or double quotes method...
-
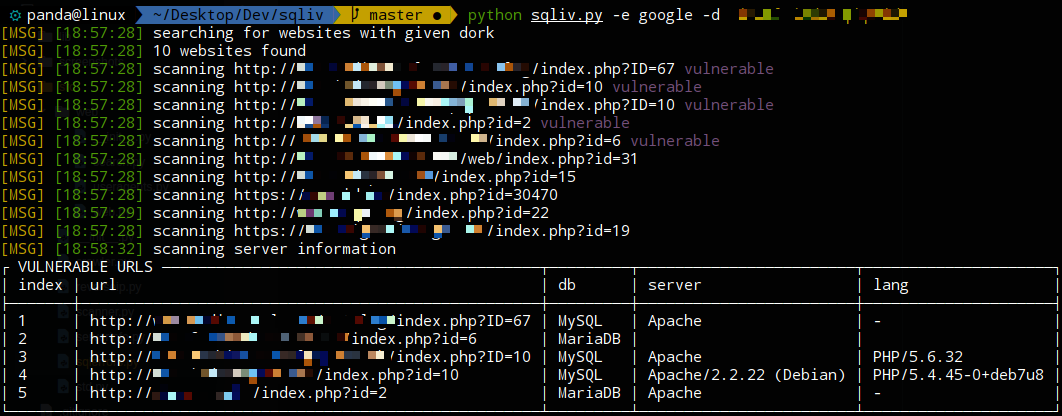
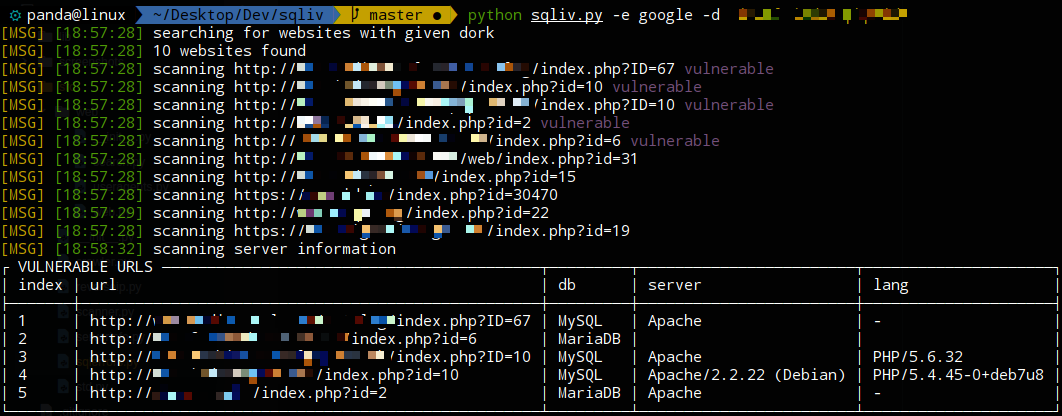 223Hackers Repository
223Hackers RepositorySQLiv – Massive SQL injection scanner
SQLiv – Massive SQL injection scanner SQLiv Massive SQL injection scanner Features multiple domain scanning with SQL injection dork by Bing, Google,...
-

 279Sql Injection
279Sql InjectionList of Best Open Source SQL Injection Tools – 2019
SQL injection is a standout amongst the most widely recognized attacks against web applications. Here is the list of Best SQL Injection...






