Search results for "Injection"
-
 251Exploitation Tools
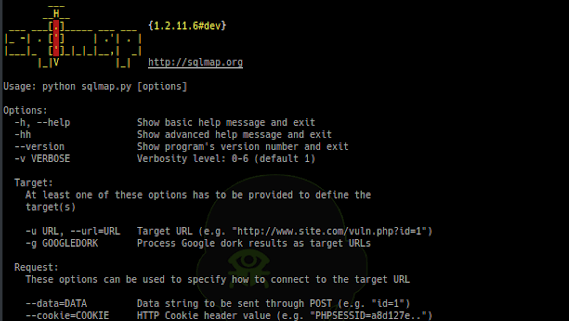
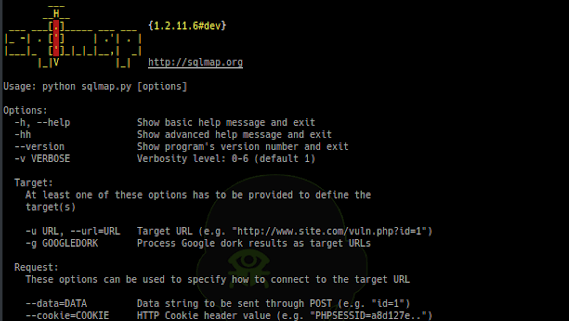
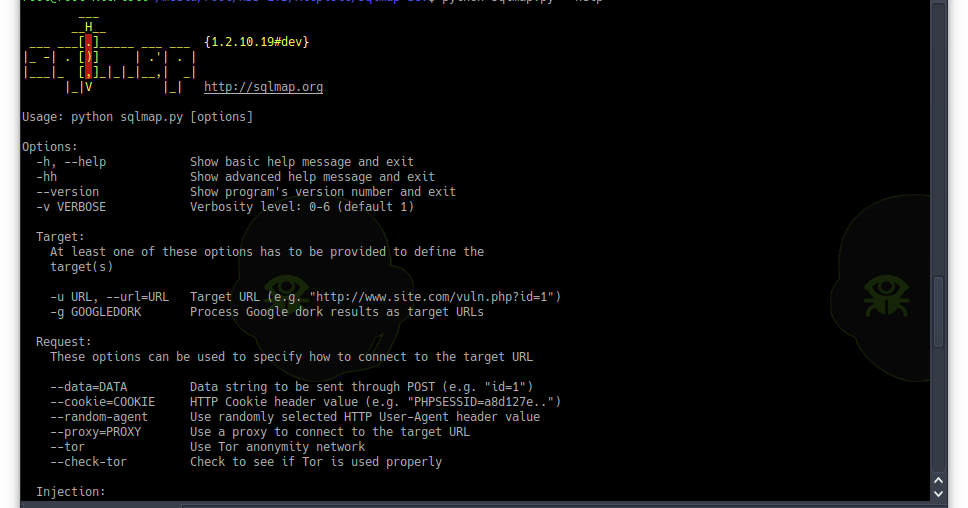
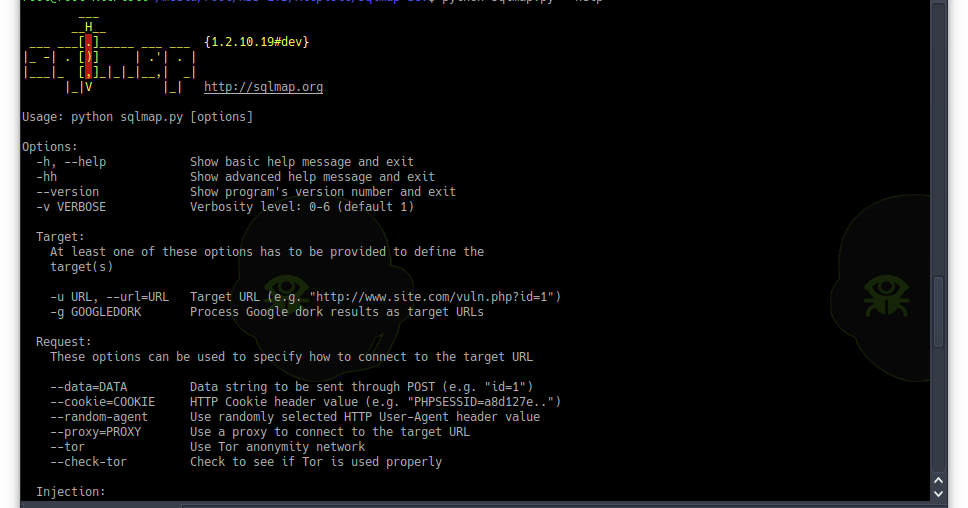
251Exploitation ToolsSQLMap v1.2.11 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over...
-
 202Malware
202MalwareOutlaw Hacking Group Using Command Injection Flow To Attack Organizations Network using Botnet via C&C Server
Outlaw Hacking group uses command injection vulnerability in IoT devices and Linux servers to distribute botnets. The threat actors compromised the FTP...
-
 204Exploitation Tools
204Exploitation ToolsSQLMap v1.2.10 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over...
-
 209Exploitation
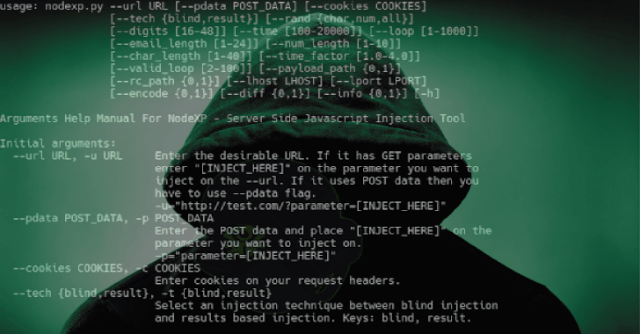
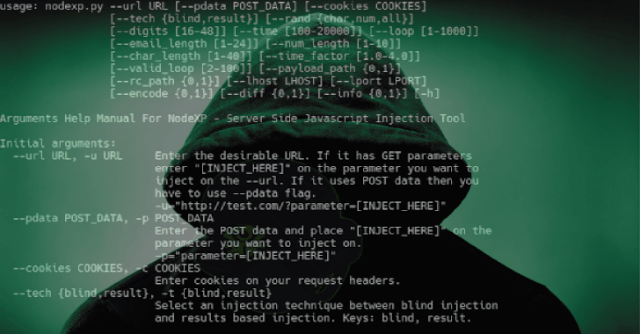
209ExploitationNodexp – A Server Side Javascript Injection Tool
NodeXP is an intergrated tool, written in Python 2.7, capable of detecting possible vulnerabilities on Node.js services as well as exploiting them...
-

 244Evasion & Obfuscation
244Evasion & ObfuscationCoffeeShot: Avoid Detection with Memory Injection
CoffeeShot is an evasion framework that injects payload from Java-based programs into designated processes on Microsoft Windows. It assists blue team members...
-
 411Malware
411MalwareNew Adwind RAT Attack Linux, Windows and Mac via DDE Code Injection Technique by Evading Antivirus Software
New Adwind 3.0 RAT (Remote access Trojan) Evolving with new sophisticated capabilities, unlike old version it mainly attacks desktop version of Linux,...
-
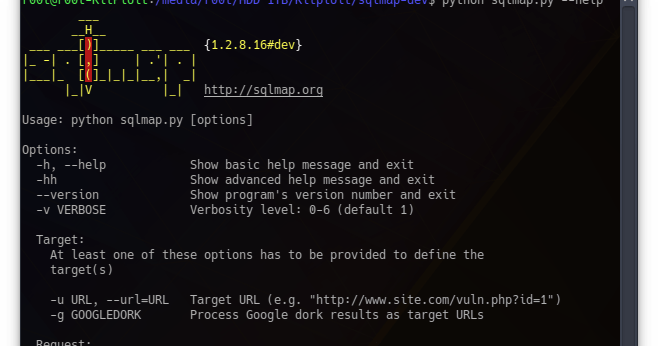
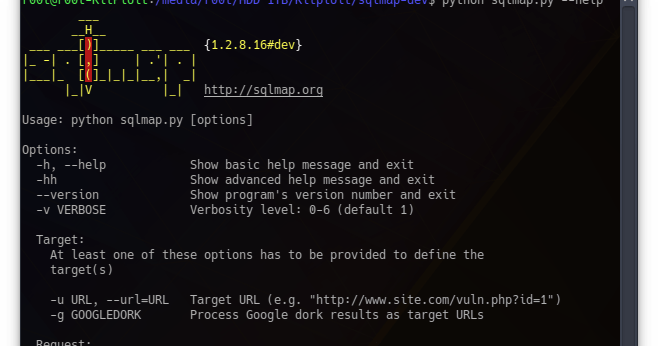 236Exploitation Tools
236Exploitation ToolsSQLMap v1.2.8 – Automatic SQL Injection And Database Takeover Tool
SQLMap is an open source penetration testing tool that automates the process of detecting and exploiting SQL injection flaws and taking over...
-

 364Hacking Tools
364Hacking ToolsTplmap – Open Source Tool to Scan For Server Side Template Injection Vulnerabilities
Tplmap is a python tool that can find code injection and Server Side Templates Injection (SSTI) vulnerabilities by using sandbox escape techniques....
-
 270Malware
270MalwareTrickbot Malware Re-emerging via MS Word Documents with Powerful Code-Injection Technique
Trickbot malware is one of the widely known Banking Trojan emerging again with sophisticated techniques to at target the various financial institutions and...
-

 256Sql Injection
256Sql InjectionBSQLinjector – Blind SQL Injection Exploitation Tool
BSQLinjector is a Blind SQL injection exploitation tool written in ruby. It uses blind method to retrieve data from SQL databases. I...
-

 290Hacking Tools
290Hacking ToolsSqlmap – Free Tool for SQL Injection Discovery And Exploitation
Sqlmap is an open source tool used to test the SQL injection vulnerabilities within web applications. The tool requires Python 2.6.x and...
-
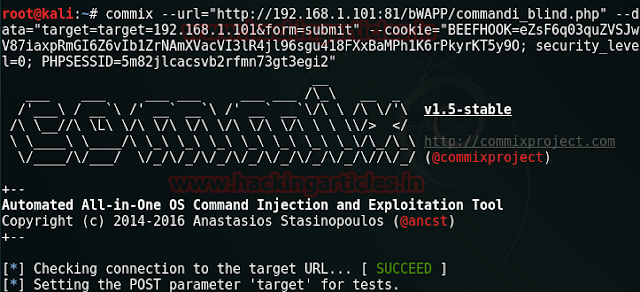
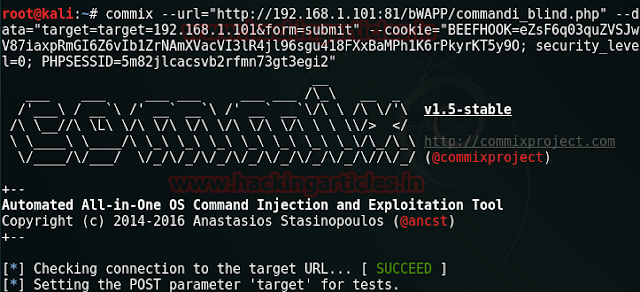 234Hacking Tools
234Hacking ToolsCommix – The OS Command Injection and Exploitation Tool
Commix is a command injection exploitation tool used for testing command injection vulnerabilities in web applications. Command injection, also known as shell...
-

 258Sql Injection
258Sql InjectionSleuthQL – SQL Injection Discovery Tool
SleuthQL is a python3 script to identify parameters and values that contain SQL-like syntax. Once identified, SleuthQL will then insert SQLMap identifiers...
-

 295Vulnerabilities
295VulnerabilitiesHow to safeguard your databases from SQL injections
SQL (Structured Query Language) is a popular programming language for managing data kept in relational databases. However, the databases can be breached...
-
 179Vulnerabilities
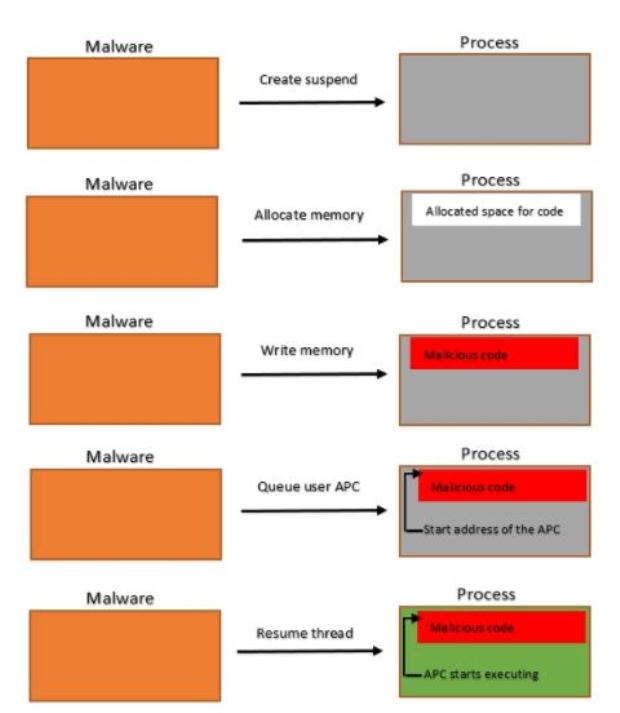
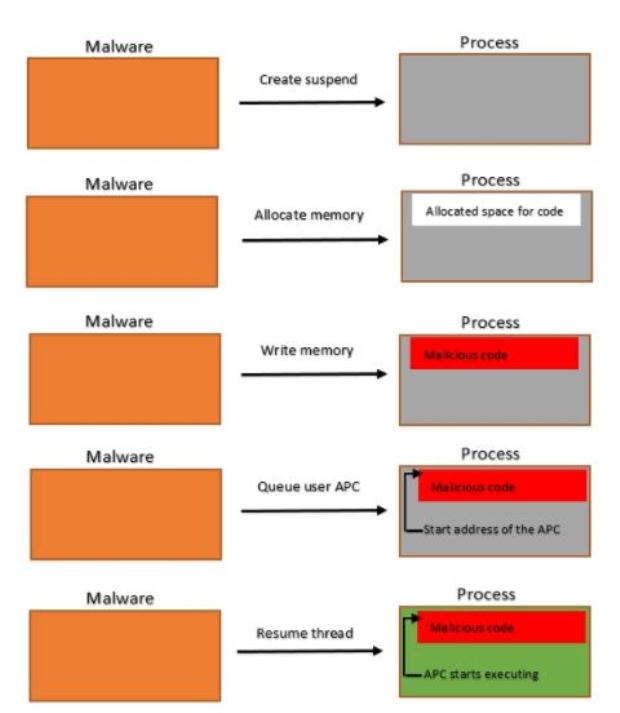
179VulnerabilitiesNew ‘Early Bird’ Code Injection Technique
This injection technique allows the injected code to run before the entry point of the main thread of the process, thereby allowing...
-
 236Malware
236MalwareEarly Bird – A Malware Code Injection Technique to Evade the Detection by Anti-Malware
Advanced Malware threats nowadays using powerful Code Injection Technique called “Early Bird” that helps to evade the detection by Anti-Malware software. Code...
-

 276Hack Tools
276Hack ToolsCommix – Automated Command Injection and Exploitation Tool
Commix (short for [comm]and [i]njection e[x]ploiter) is an automated tool that you can use to test web-based applications with the view to...
-

 187Malware
187MalwareLinux.ProxyM used to Launch Numerous Hacking Attempts against Websites through Various Methods (SQL injections, XSS, LFI)
Linux.ProxyM malware was well known for infecting almost any Linux devices which include routers, set-top boxes, and other equipment. It affects the...
-

 193Malware
193MalwareURSNIF TROJAN ADOPTS NEW CODE INJECTION TECHNIQUE
Hackers are testing a new variation of the Ursnif Trojan aimed at Australian bank customers that utilizes novel code injection techniques. Since...
-

 262Malware
262MalwareUrsnif Malware Variant Performs Malicious Process Injection in Memory using TLS Anti-Analysis Evasion Trick
A Sophisticated Ursnif Malware variant using manipulated TLS call back Anti-Analysis Technique while injecting the Child Process for changing the entry point....
-
 145Hack Tools
145Hack ToolsThe Mole – Automatic SQL Injection Exploitation Tool
The Mole is an automatic SQL Injection exploitation tool. Only by providing a vulnerable URL and a valid string on the site...






