Search results for "Injection"
-

 235News
235NewsLatest Joomla Security Update Patches Critical SQL Injection Attack
Latest Joomla Security Update Joomla Security Update 3.7.1 is now available. this is a security release for the 3.x series of Joomla! Which...
-
 135Vulnerabilities
135VulnerabilitiesNew Joomla SQL Injection Flaw Is Ridiculously Simple to Exploit
The Joomla CMS project released today Joomla 3.7.1 to fix an SQL injection flaw that allows attackers to execute custom SQL code...
-

 119Cyber Crime
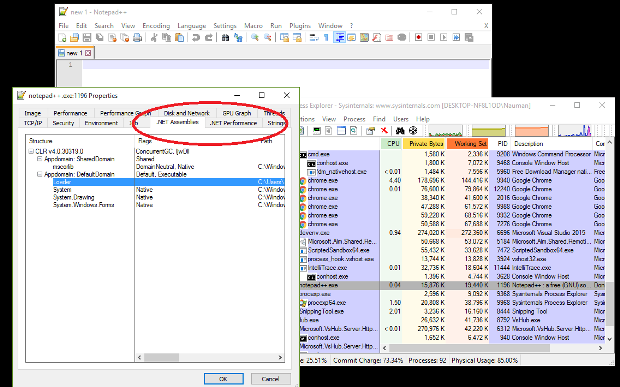
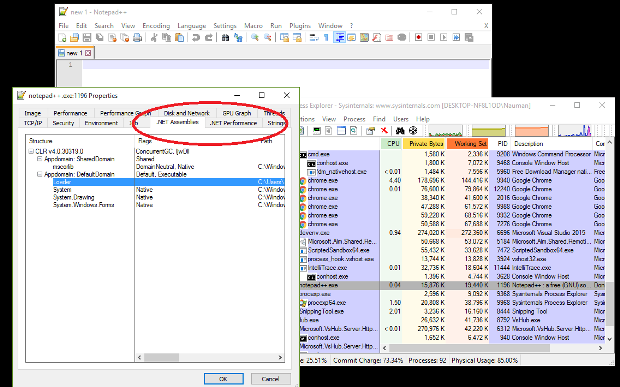
119Cyber CrimeMalicious registry keys: Reflective injection
In recent months, we have started to receive various reports about suspicious and malicious registry keys that had been created on users’...
-

 194Vulnerabilities
194VulnerabilitiesPowerShell Injection with Diskless Payload Persistence and Bypass Techniques
PowerShell continues to be the tool of choice for defenders, IT administrators, and hackers. The extensibility, support, and ability to have a...
-
 213Vulnerabilities
213VulnerabilitiesDLL Injection Using LoadLibrary in C
Tutorials on Windows DLL injections in C have noticable gaps in what they explain. This blog post plus the comments on my...
-

 104Vulnerabilities
104VulnerabilitiesANALYZING THE DOUBLEPULSAR KERNEL DLL INJECTION TECHNIQUE
Like many in the security industry, we’ve been busy investigating the implications of the Shadow Brokers leak, with the DOUBLEPULSAR payload in...
-
 219Vulnerabilities
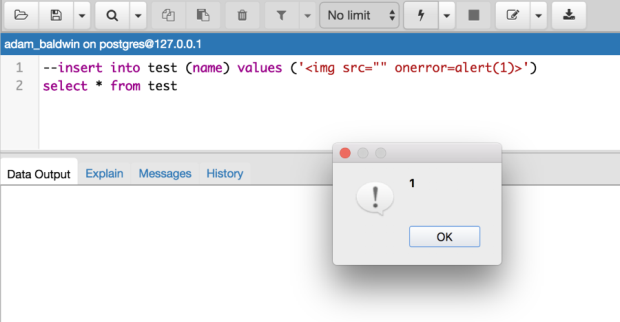
219VulnerabilitiesSQL Injection & more via XSS in pgAdmin 4
This is the story of how I found and exploited XSS (content injection) in the pgAdmin4 1.3 desktop client. (Before I get...
-

 187Hackers Repository
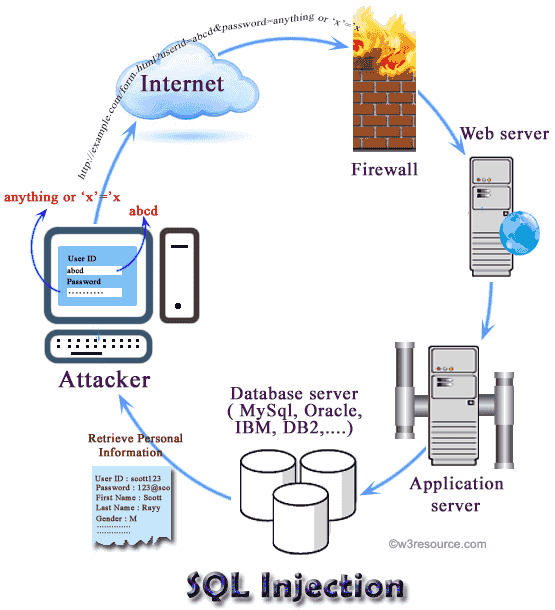
187Hackers RepositorySQLMap Tutorial SQL Injection to hack a website and database in Kali Linux
Hi, today I will demonstrate how an attacker would target and compromise a MySQL database using SQL Injection attacks. SQL Injection attacks...
-

 203Hackers Repository
203Hackers RepositoryGoogle Dorks for SQL Injection 2017 – HackingVision
Google Dorks for SQL Injection Google Dorks, Google Dorks List, Find SQL Injectable Websites, Hack Websites using Google Dorks, Google Dorks List...
-
 185Hackers Repository
185Hackers RepositorySQL Inject Me -Firefox Extension used to test for SQL Injection vulnerabilities
SQL Inject Me is a Firefox addon created by Security Compass it is used for finding SQL vulnerabilities in Web applications. SQL...
-
 285Data Security
285Data SecurityWordPress Plugin NextGEN Gallery Vulnerable to SQL Injection Attack
The NextGen gallery has been plagued with a severe security flaw for the second time in consecutive years, and this time it...
-

 240Vulnerabilities
240VulnerabilitiesCritical SQL Injection Vulnerability Found in NextGEN Gallery WordPress Plugin
The vulnerability can lead to attackers grabbing data from website database or user sensitive information. A new SQL Injection vulnerability was discovered...
-

 280Vulnerabilities
280VulnerabilitiesWordPress Team Secretly Fixed A Zero-Day Critical Content Injection Vulnerability
The WordPress security team revealed that they’ve secretly fixed a zero-day vulnerability in the WordPress CMS REST API.The vulnerability in this case...
-

 184Vulnerabilities
184VulnerabilitiesContent Injection Vulnerability in WordPress 4.7.0 or 4.7.1
As part of a vulnerability research project for our Sucuri Firewall (WAF), we have been auditing multiple open source projects looking for...
-

 264Data Security
264Data SecurityWordPress Websites Exposed to Severe Content Injection Vulnerability
WordPress is one of the most used content management system (CMS) in the world. So when there is a security flaw in...
-

 248How To
248How Toreversemap – Analyse SQL Injection Attempts In Web Server Logs
SQL CHAR encoding SQL CAST encoding Case encoding of SQL keywords Substring(Experimental – Disabled by default as it will fail with nested...
-

 336Vulnerabilities
336VulnerabilitiesWordPress Publishes Critical Security Update XSS, SQL Injection vulnerabilities
WordPress 4.7.1 and earlier forms are influenced by various vulnerabilities. A remote attacker could exploit some of these vulnerabilities to take control...
-

 189Vulnerabilities
189VulnerabilitiesWORDPRESS 4.7.2 UPDATE FIXES XSS, SQL INJECTION BUGS
Developers with WordPress fixed three security issues this week, including a cross-site scripting and a SQL injection vulnerability, with the latest version...
-

 250Vulnerabilities
250VulnerabilitiesGoogle Forms WordPress Plugin unauthenticated PHP Object injection vulnerability
Introduction The Google Forms WordPress Plugin fetches a published Google Form using a WordPress custom post or shortcode, removes the Google wrapper...
-

 301Cyber Attack
301Cyber AttackSQL Injection Used By Hackers To Get Access Of Websites
There are numerous strategies by way of which you can hack the web sites but sq. Injection method is the one of...
-

 298How To
298How ToCommix – Automated All-In-One OS Command Injection And Exploitation Tool
Commix, other wise known as [ comm ]and [ i ]njection e[ x ]ploiter is an automated tool written by that can...






