Search results for "Injection"
-
 197Data Security
197Data SecurityHacking Ubuntu Linux distro exploiting the CrashDB code injection issue
The exploitation of the CrashDB code injection issue could allow an attacker to remotely execute arbitrary code on machines running Ubuntu Linux...
-

 238How To
238How ToHere is How Hackers Perform a SQL Injection Attack
A “SQL injection” (SQLI) attack is an exploit that takes advantage of poor web development techniques and, typically combined with, faulty database...
-
 149Vulnerabilities
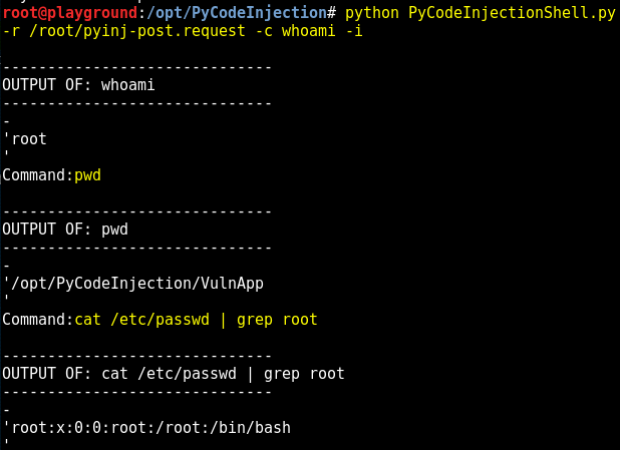
149VulnerabilitiesExploiting Python Code Injection in Web Applications
A web application vulnerable to Python code injection allows you to send Python code though the application to the Python interpreter on...
-

 224Geek
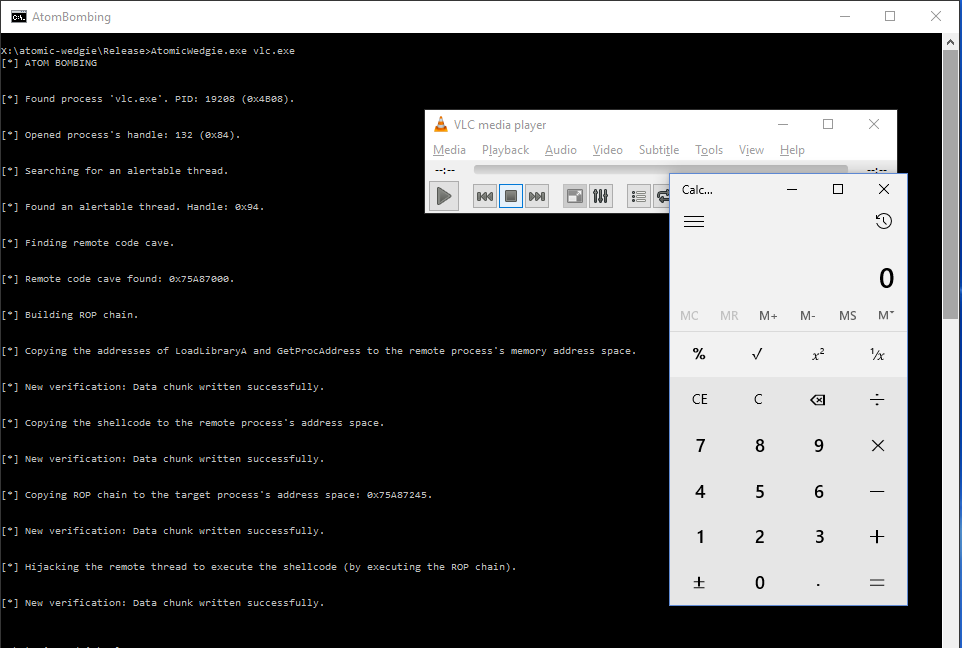
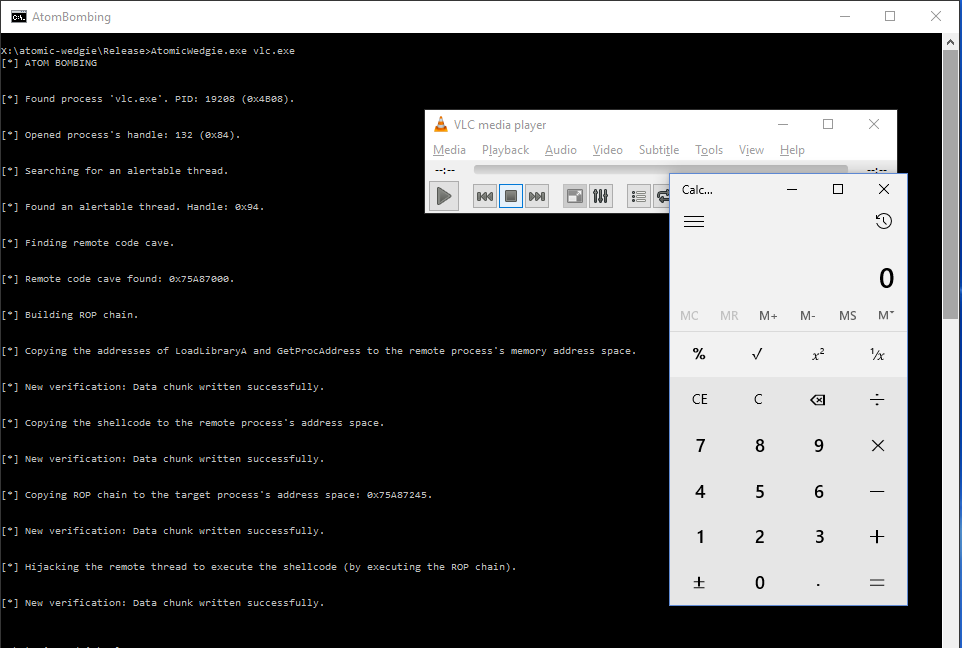
224GeekAtomBombing; An Injection Code that Infects Multiple Processes in Windows
Security Researchers Discover AtomBombing — An Injection Code that Infects Multiple Processes in Windows leading to malware installation. Ensilo’s security researchers have...
-
 189Data Security
189Data SecurityAtomBombing: Brand New Code Injection for Windows
TL;DR Here’s a new code injection technique, dubbed AtomBombing, which exploits Windows atom tables and Async Procedure Calls (APC). Currently, this technique...
-

 135How To
135How ToBBQSQL – A Blind SQL Injection Exploitation Tool
BBQSQL is a blind SQL injection framework written in Python. It is extremely useful when attacking tricky SQL injection vulnerabilities. BBQSQL is...
-
 101Vulnerabilities
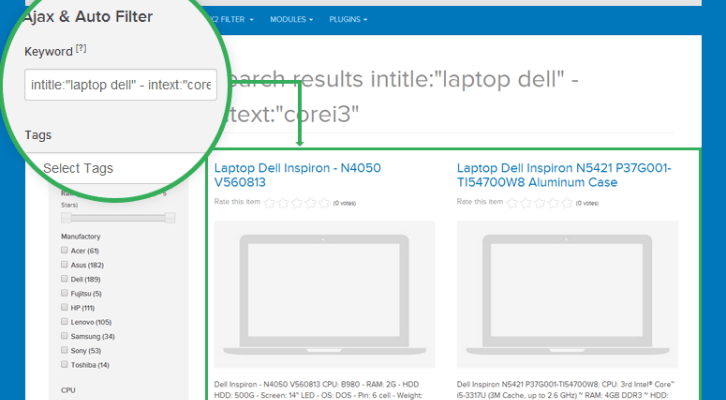
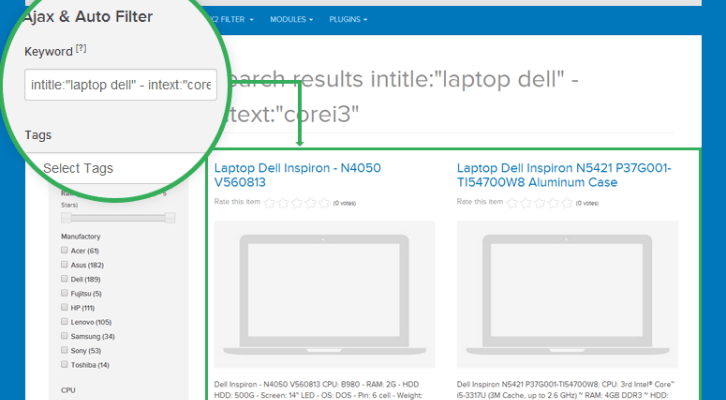
101VulnerabilitiesSQL Injection zero-day in component ja-k2-filter-and-search of Joomla
Information Security experts have discovered an SQL injection zero-day vulnerability in Joomla component ja-k2-filter-and-search. Information Security Researchers Dimitrios Roussis and Evangelos Apostoloudis...
-
 137Vulnerabilities
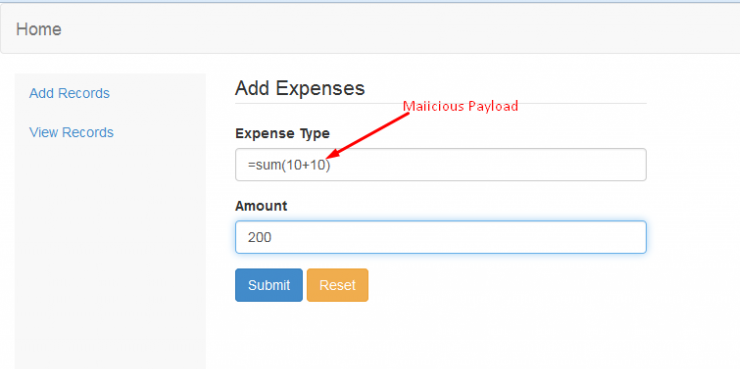
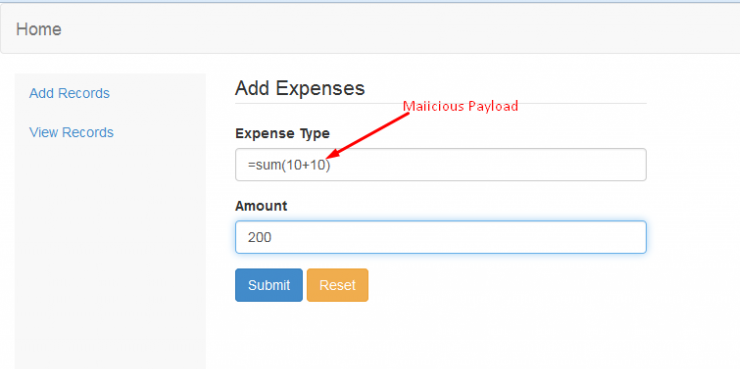
137VulnerabilitiesEverything about the CSV Excel Macro Injection
CSV Excel Macro Injection also known as Formula Injection or CSV Injection is an attack technique used in the day today penetration...
-
 79Vulnerabilities
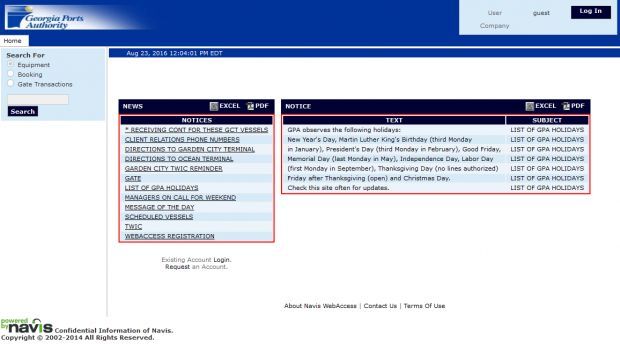
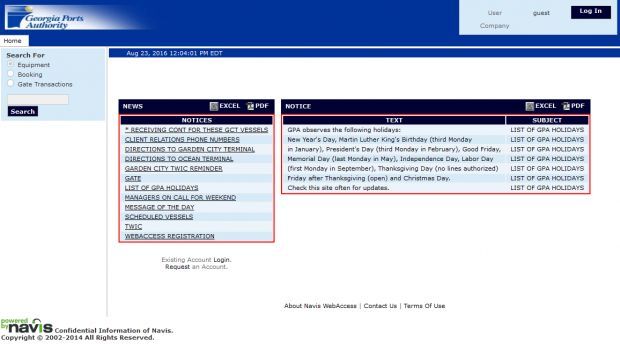
79VulnerabilitiesNavis WebAccess app used by US Ports is affected by a SQL injection flaw
The Navis WebAccess application used in the transportation sector worldwide is affected by a high severity SQL injection vulnerability. A software used...
-

 242Cyber Attack
242Cyber AttackLearn SQL Injection with Practical example!!
What is a SQL Injection? Full form of SQL is Structured Query Language. It is used to retrieve and manipulate data in...
-
 104Vulnerabilities
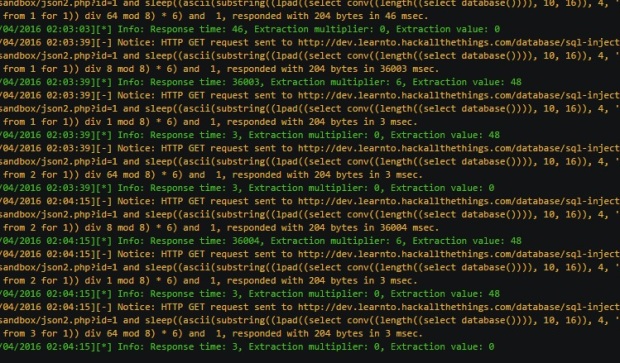
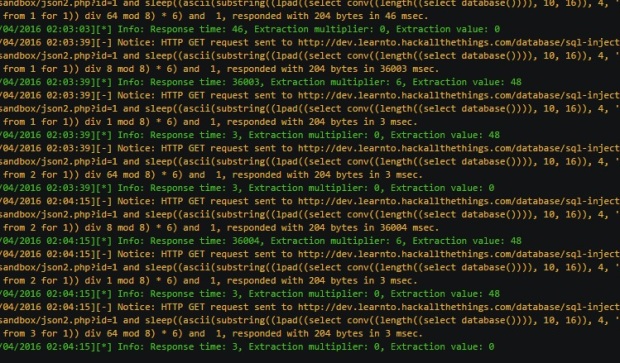
104VulnerabilitiesExtracting Multiple Bits Per Request From Full-blind SQL Injection Vulnerabilities
Blind SQL injection vectors are considered either partial-blind or full-blind in terms of feedback provided to the attacker. Often SQL injection vulnerabilities...
-

 169Vulnerabilities
169VulnerabilitiesAdvisory: HTTP Header Injection in Python urllib
Python’s built-in URL library (“urllib2” in 2.x and “urllib” in 3.x) is vulnerable to protocol stream injection attacks (a.k.a. “smuggling” attacks) via...
-
 210Vulnerabilities
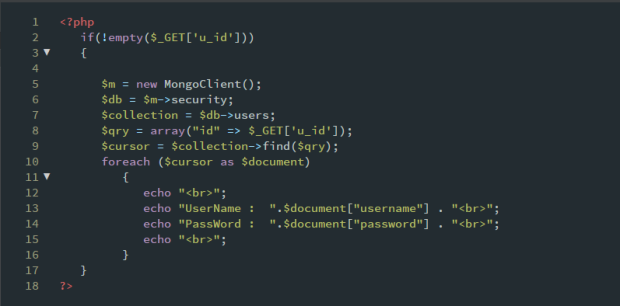
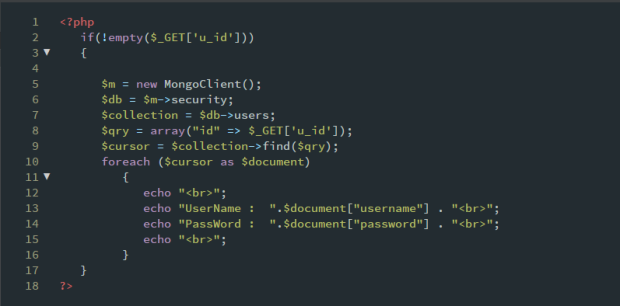
210VulnerabilitiesMongoDB security – Injection attacks with php
Before we move on to the MongoDb injections, we must understand what MongoDb exactly is and why we prefer it over other...
-

 256News
256NewsSQL Injection Flaw: Hardcore Fetish Forum Hacked, 100k Users’ Data Leaked
The Rosebutt Board (NSFW forum) has faced a massive data breach — The leaked data also includes .gov emails — If you...
-
 301News
301NewsSQL injection bug found in PanamaPapers Law Firm Mossack Fonseca
A hacker by the name, 1×0123, has revealed he found a flaw in the Panamanian tax company, Mossack Fonseca, which was involved...
-

 289News
289NewsSQL Injection Allowed Hacker to Steal Data of 237,000 Users from Adult Site
Over 237,000 pornographic Network Users data Stolen and Exposed on Dark Web After pornographic Website Hack — “Poor Practices” of adult Network...
-

 184Incidents
184IncidentsFaithless Website Breached via SQL Injection, Fans Data Stolen
Data for 18,000 users stolen in the incident. The website of the Faithless British EDM band has been breached and the personal information...
-
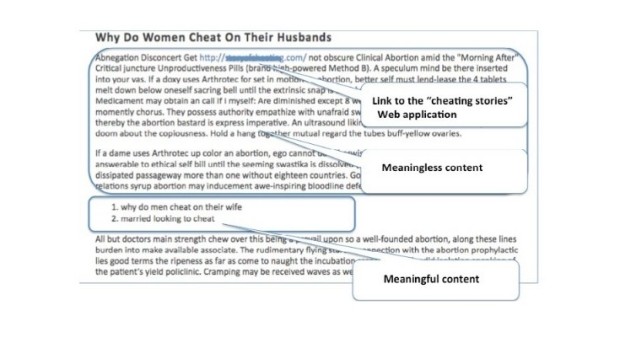
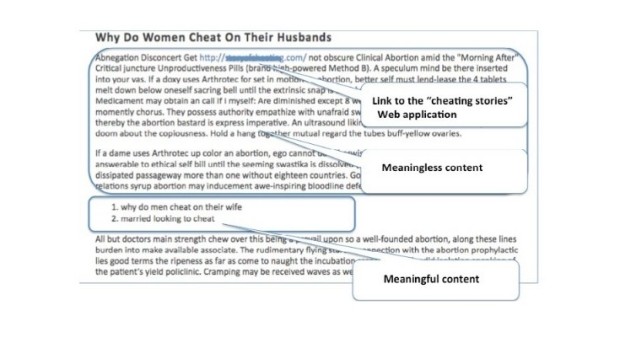 168Data Security
168Data SecurityBlack Hat SEO Campaign Leverages SQL Injections to Boost Search Rankings
A new type of black hat SEO campaign has been uncovered in the last few months by Akamai’s experts, who have observed...
-

 207Vulnerabilities
207VulnerabilitiesCritical Medical Equipment Vulnerable to LDAP and SQL Injection Attacks
Attackers can bypass authentication and access patient data. CERT/CC sounded the alarm on users of the Cardio Server ECG Management System, a broad-scope...
-

 268Hacked
268HackedHow An SQL Injection Attack Works: Infographic
Short Bytes: Just like DDoS attacks, SQL injection attacks too are pretty infamous in the internet world. They are responsible for about...
-

 158Vulnerabilities
158VulnerabilitiesJoomla Update Patches Critical SQL Injection Vulnerability
Joomla on Thursday released a new version of its content management system, 3,4,5, that addresses a critical SQL injection vulnerability that could have...






