Search results for "Intelligence"
-
Information Gathering
Hackertarget – Tools And Network Intelligence To Help Organizations With Attack Surface Discovery
Use open source tools and network intelligence to help organizations with attack surface discovery and identification of security vulnerabilities. Identification of an...
-
 268Hacking Tools
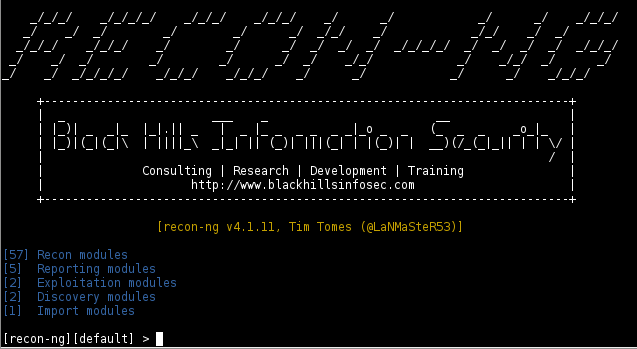
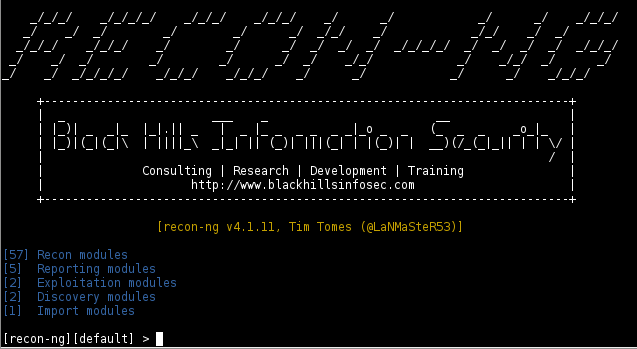
268Hacking ToolsRecon-ng – Open Source Intelligence (OSINT) Reconnaissance Framework
Recon-ng is a reconnaissance framework that can perform open source web based information gathering for a given target. Recon-ng is loaded with...
-
 332Information Gathering
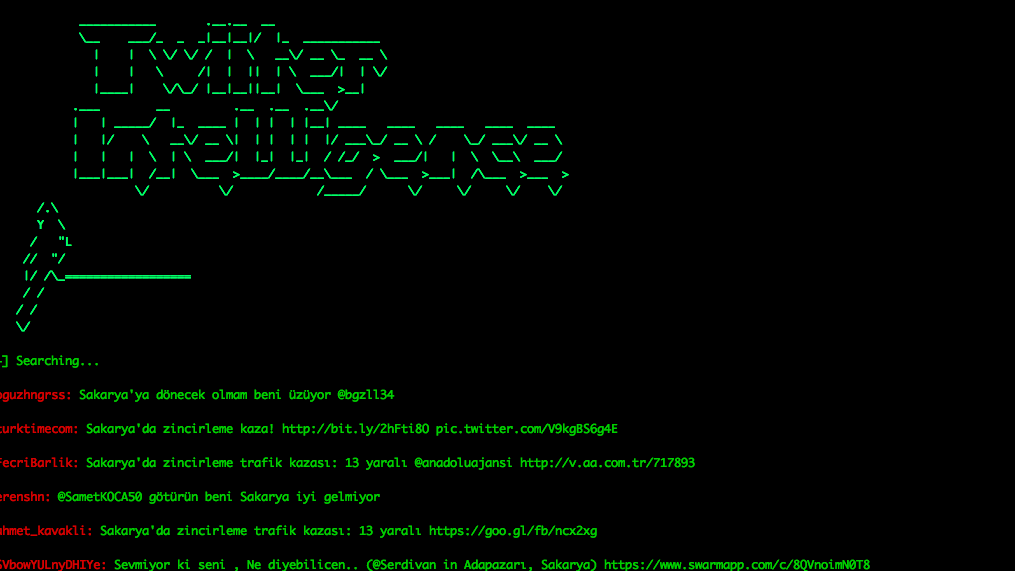
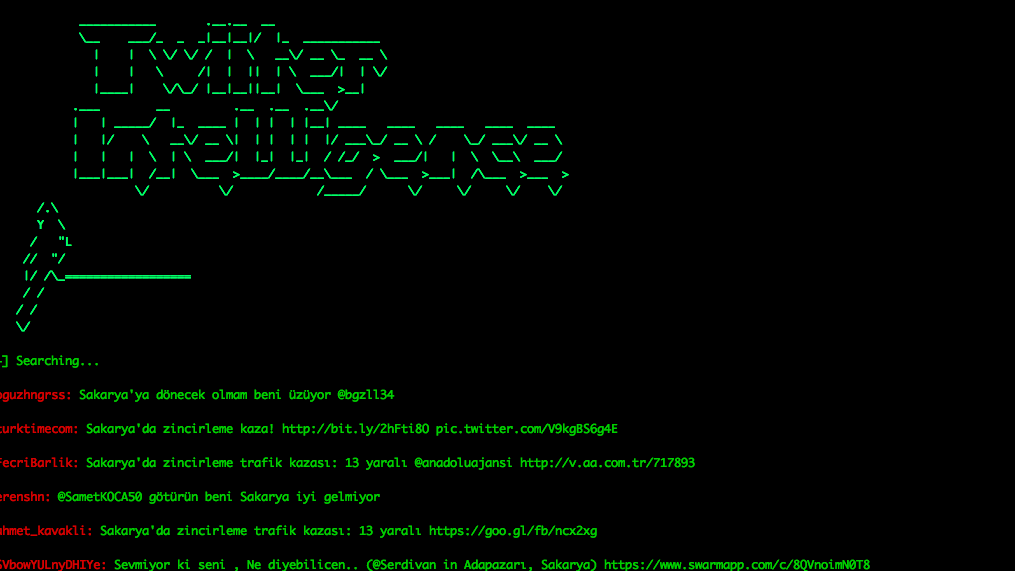
332Information GatheringTwitter-Intelligence – Twitter Intelligence OSINT Project Performs Tracking And Analysis Of The Twitter
A project written in Python to twitter tracking and analysis without using Twitter API. Prerequisites This project is a Python 3.x application....
-
 266Hacking Tools
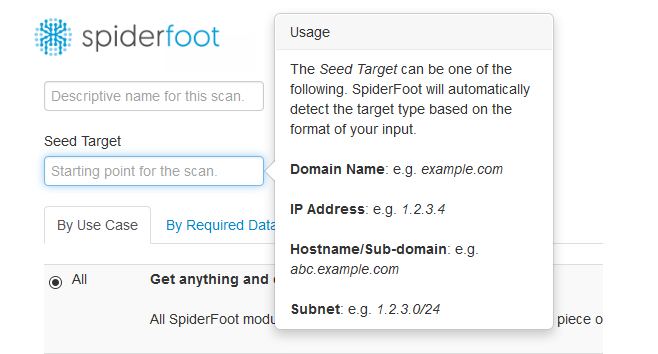
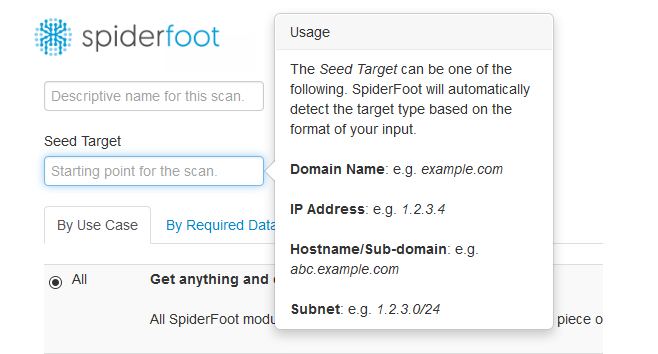
266Hacking ToolsSpiderfoot – Open Source Intelligence and Information Gathering Tool
Spiderfoot is an open source tool used for reconnaissance purpose. The tool is capable of gathering useful information about the target host...
-
 204Hacking Tools
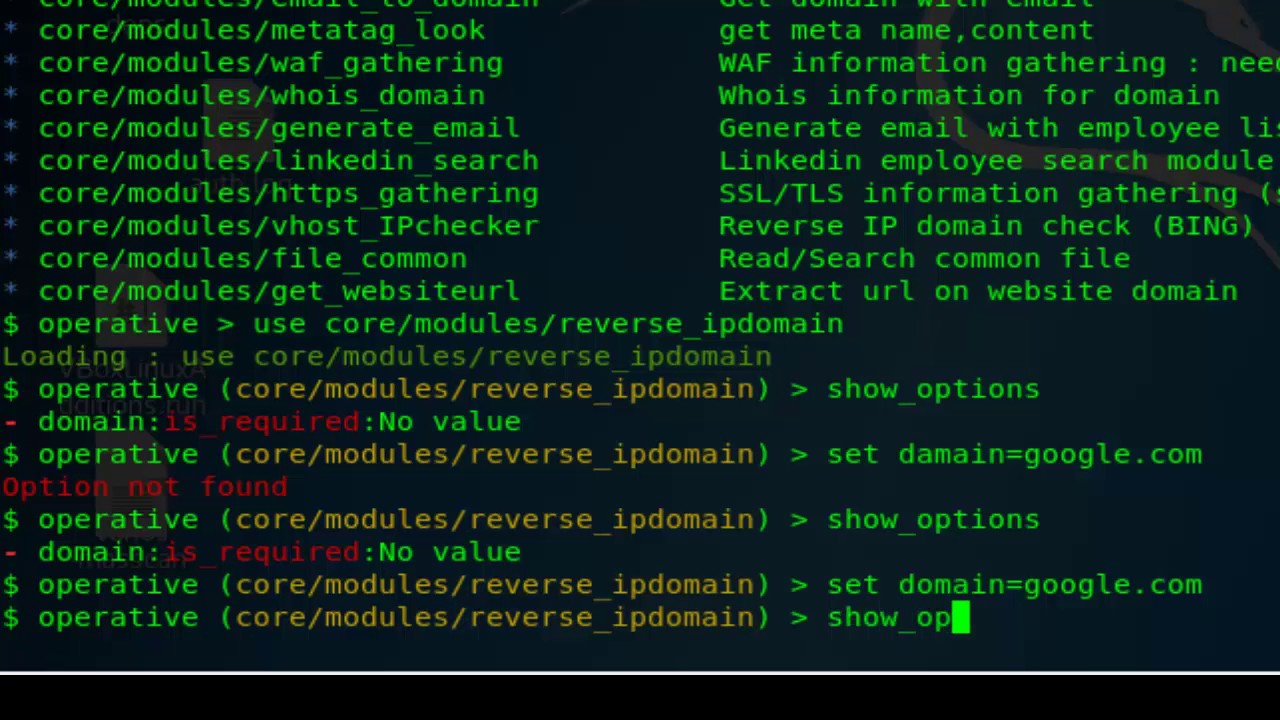
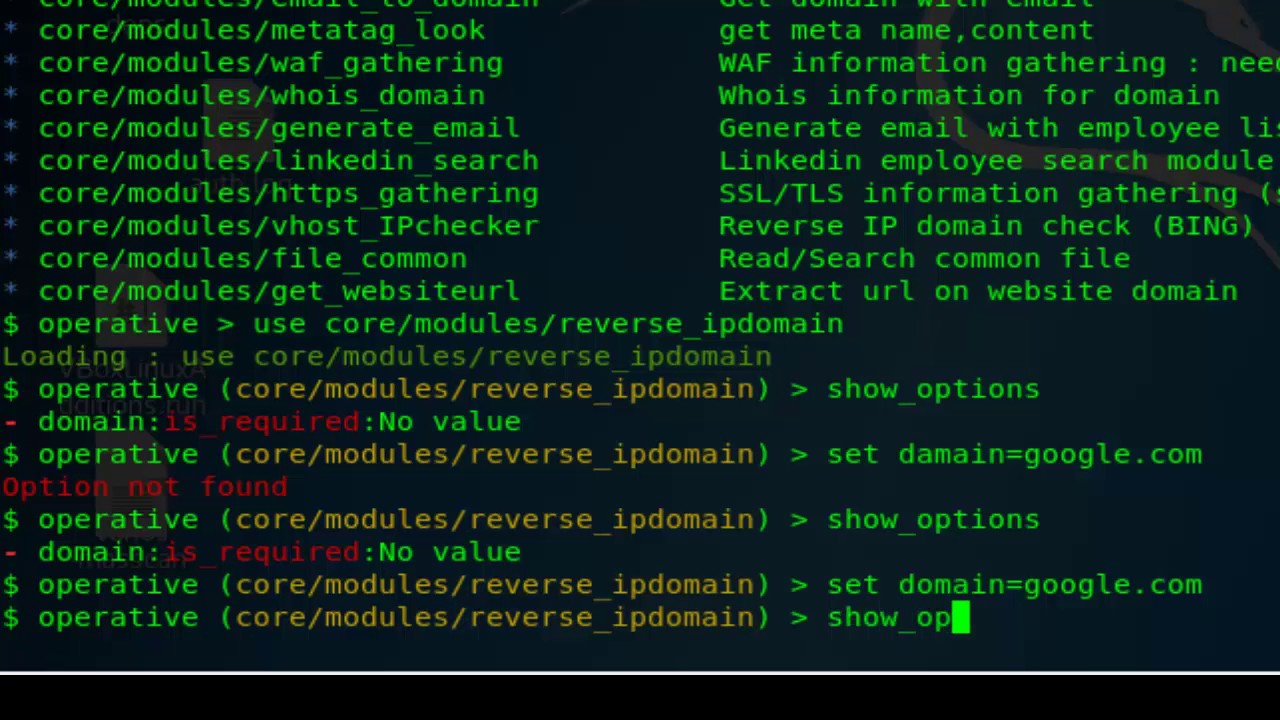
204Hacking ToolsOperative Framework – Open Source Intelligence Gathering Tool
The Operative Framework tool can be used within a red team/social engineering engagement to collect information regarding websites and enterprises. The tool...
-
 244News
244NewsResearchers Developed DeepLocker Artificial Intelligence- Powered Stealthy Malware
DeepLocker Artificial intelligence (AI) is seen as a potential solution to automatically detect malware and combat and stop cyber attacks before it...
-
 221Malware
221MalwareDangerous malware powered by artificial intelligence
Researchers developed this stealth-attacking software Enterprise network security researchers have worked with artificial intelligence to automatically detect and fight malware attacks, as well as...
-

 190Articles
190ArticlesWhat is Cindicator? A Beginner’s Guide to Hybrid Intelligence Forecasting
What is Cindicator? Cindicator fuses together machine learning and market analysis for asset management and financial analytics. The Cindicator team dubs this...
-
 223Information Gathering
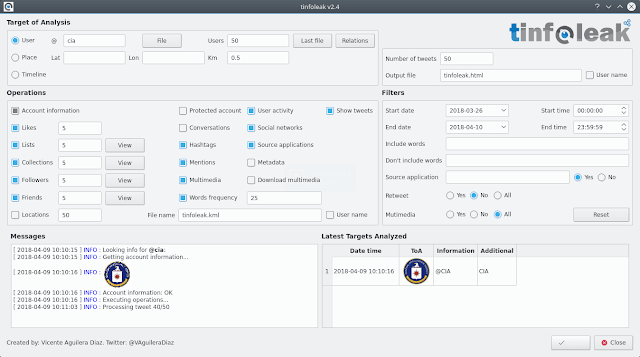
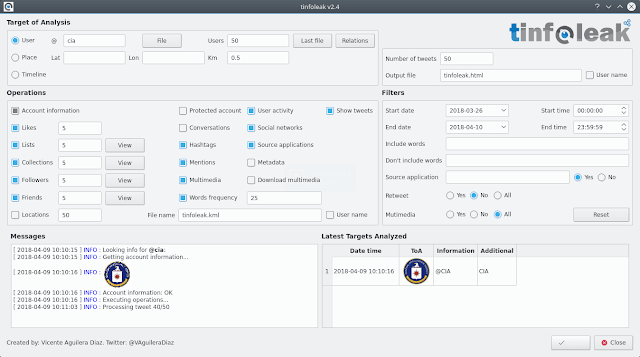
223Information GatheringTinfoleak v2.4 – The Most Complete Open-Source Tool For Twitter Intelligence Analysis
The most complete open-source tool for Twitter intelligence analysis Introduction tinfoleak is an open-source tool within the OSINT (Open Source Intelligence) and SOCMINT (Social Media Intelligence) disciplines,...
-
 296Information Gathering
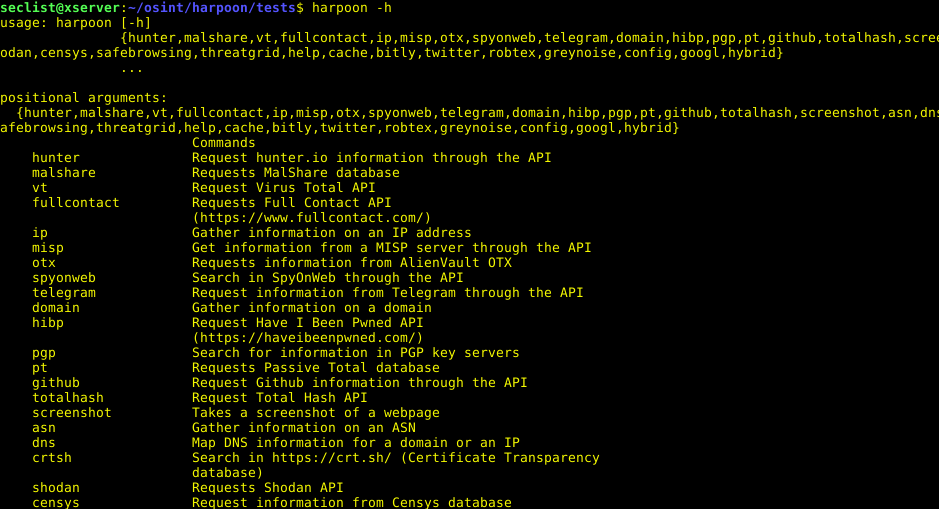
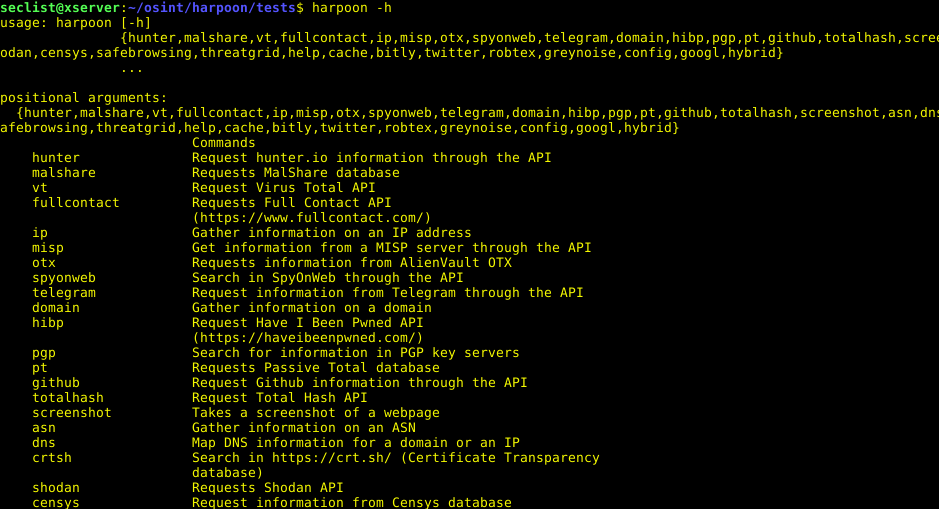
296Information GatheringHarpoon – CLI Tool For Open Source And Threat Intelligence
OSINT tool, CLI Tool For Open Source And Threat Intelligence Install You can simply pip install the tool: pip3 install git+http://[email protected]/Te-k/harpoon --process-dependency-links Optionally...
-

 428Hacked
428HackedHow Did Google Wipe Out 700,000 Malicious Android Apps From Play Store? Using Artificial Intelligence
It’s a common habit of humans and companies to flaunt their achievements every new year. Google has just announced that it managed to wipe...
-

 304Threat Intelligence
304Threat IntelligenceCyBot – Open Source Threat Intelligence Chat Bot
Threat intelligence chat bots are useful friends. They perform research for you and can even be note takers or central aggregators of...
-
 221Information Gathering
221Information GatheringgOSINT – Open Source Threat Intelligence Gathering & Processing Framework
gOSINT is a small OSINT framework in golang, it’s actually in development and still not ready for production if you want, feel free to...
-
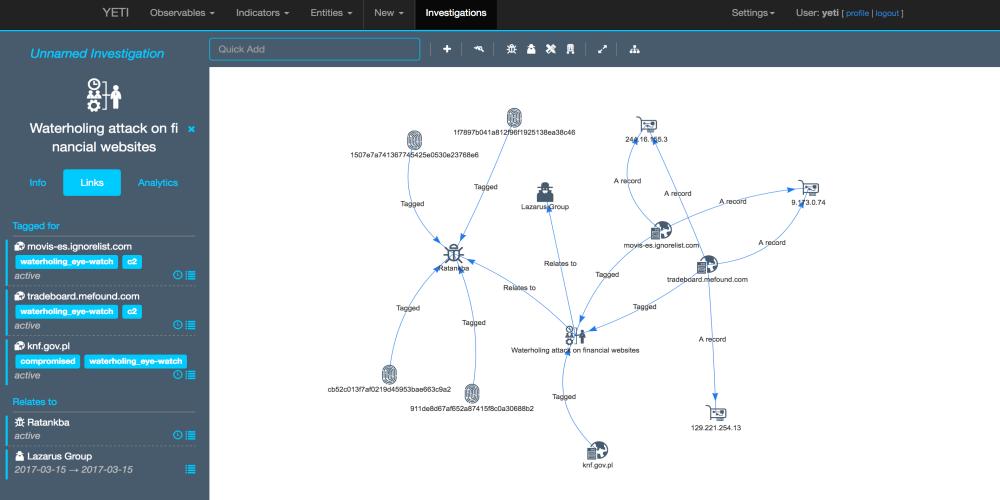
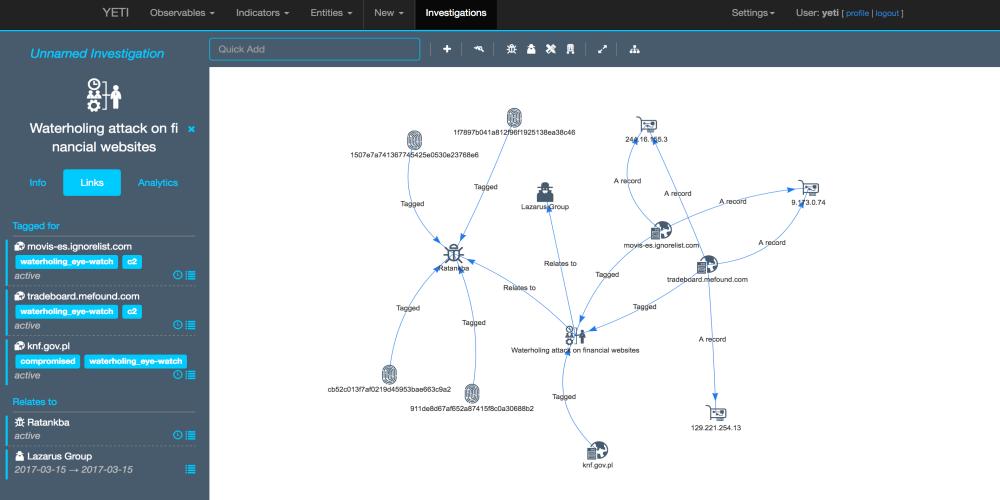 349OSINT
349OSINTYeti – Open Distributed Threat Intelligence
Yeti is a platform meant to organize observables, indicators of compromise, TTPs, and knowledge on threats in a single, unified repository. Yeti...
-
 230Information Gathering
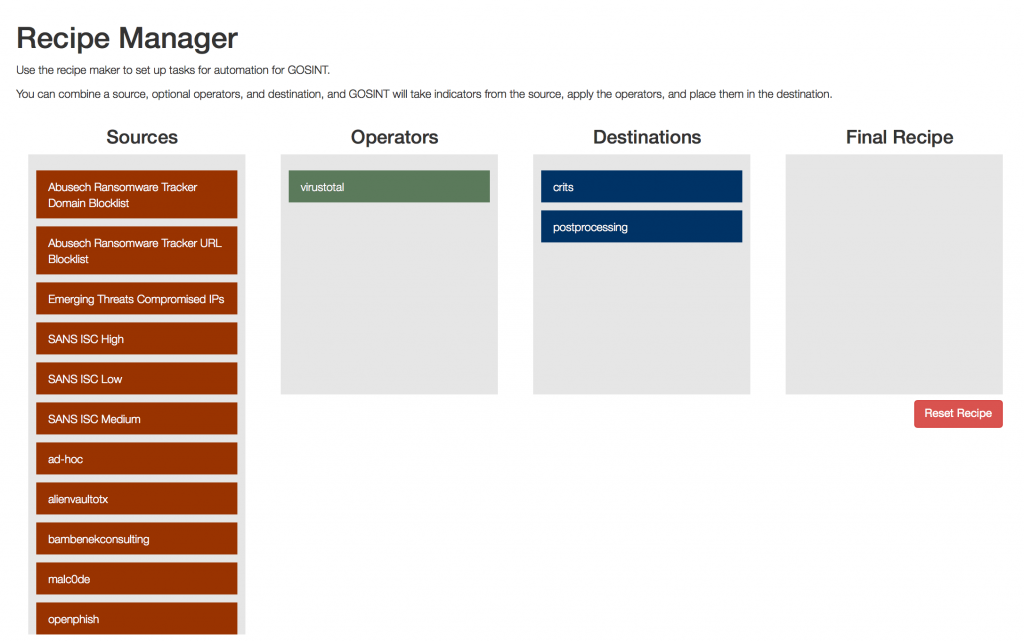
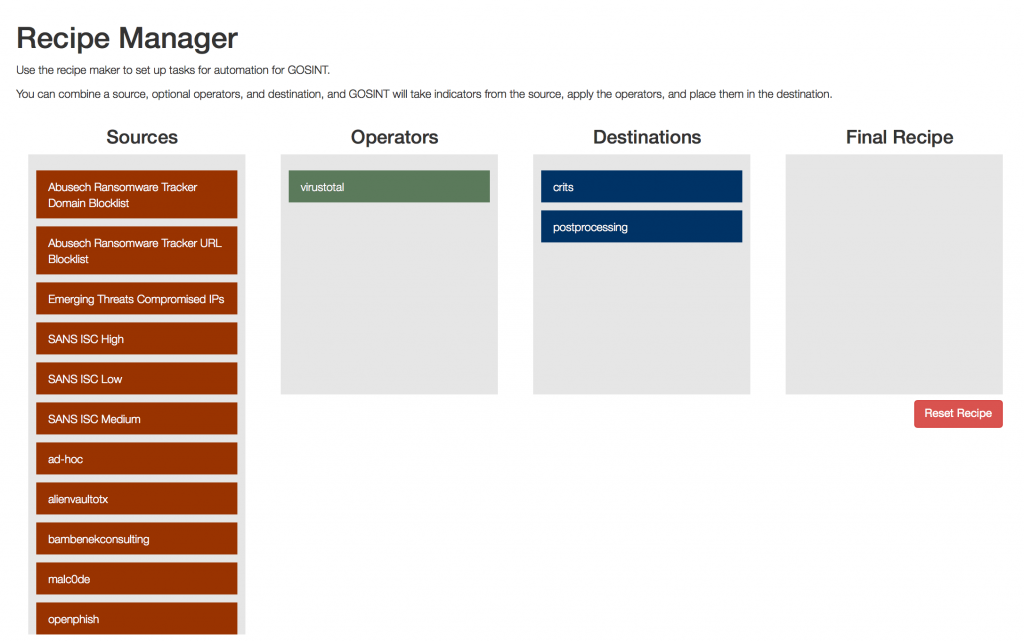
230Information GatheringGOSINT – Open Source Threat Intelligence Gathering and Processing Framework
The GOSINT framework is a project used for collecting, processing, and exporting high quality indicators of compromise (IOCs). GOSINT allows a security...
-
 550Information Gathering
550Information GatheringGOSINT – Open Source Threat Intelligence Gathering & Processing Framework
The GOSINT framework is a project used for collecting, processing, and exporting high quality indicators of compromise (IOCs). GOSINT allows a security...
-
 204Malware
204MalwareAssemblyline – Canada’s CSE intelligence Agency releases its malware analysis tool
Canada’s Communications Security Establishment (CSE) intel agency has released the source code for one of its malware analysis tools dubbed Assemblyline. The...
-
Information Gathering
IntRec-Pack – Intelligence and Reconnaissance Package/Bundle installer
Intelligence and Reconnaissance Package/Bundle installer. IntRec-Pack is a Bash script designed to download, install and deploy several quality OSINT, Recon and Threat...
-
 222Information Gathering
222Information GatheringtheHarvester – Easy Intelligence Gathering
The objective of this program is to gather emails, subdomains, hosts, employee names, open ports and banners from different public sources like...
-

 391Data Breach
391Data BreachVault 7 Leaks: CIA Conducts Secret Cyber Operation “ExpressLane” Against Their Intelligence Partners -WikiLeaks
WikiLeaks Revealed a new document of CIA Secret operations called “ExpressLane” that conducts against CIA’s information sharing Service Partners (liaison services) like NSA,DHS ,and FBI....
-

 349Cyber Crime
349Cyber CrimeBritish Intelligence Knew WannaCry Hero Would be Arrested by FBI
By now you might be aware of Marcus Hutchins, the hero who halted WannaCry ransomware and was arrested by the FBI at Las...






