Search results for "Kali Linux"
-

 188Hackers Repository
188Hackers RepositorySQLMap Tutorial SQL Injection to hack a website and database in Kali Linux
Hi, today I will demonstrate how an attacker would target and compromise a MySQL database using SQL Injection attacks. SQL Injection attacks...
-

 131How To
131How ToHow To Hack WiFi WPA2 Password Using Fluxion Tool In Kali Linux
Fluxion tool has been to be had for a while and is most apt for security researchers and pen testers to test...
-

 460How To
460How ToHack Someone’s Bluetooth And Other Wireless Tools Using Kali Linux
Blooover is performing the Bluebug attack(Bluetooth sniffer Linux). Whilst you intend to install the software, you have to be using a phone...
-
Hackers Repository
Kali Linux Man in the Middle Attack Arpspoofing/Arppoisoning
Welcome back today we will talk about Man-in-the-middle attacks. In computer security, a man-in-the-middle attack (often abbreviated mitm, or the same using all...
-
Hackers Repository
Hack Android Mobile Phone using MSFVenom Kali Linux
In this tutorial you will learn how to Hack any Android mobile phone using MSFVenom. Requirements Linux Based Operating System (In this...
-
 344How To
344How ToHow to Crack Passwords in Kali Linux Using John The Ripper
John The Ripper is a free password cracking tool that runs on a many platforms. It has become one of the best...
-

 295How To
295How ToHow to Use Doona Bruteforce Exploit Detector Tool in Kali Linux
Doona is a forked version of the Bruteforce Exploit Detection tool or simply BED. The Bruteforce Exploit Detection tool is designed to...
-

 226Data Security
226Data SecurityHacking WPA Enterprise with Kali Linux
Admittedly, that’s somewhat of a click-bait blog post title but bear with us, it’s for a good reason. Lots of work goes...
-
How To
How To Spoof MAC Address Using Macchanger in Kali Linux
MAC address spoofing is a technique for temporarily changing your Media Access Control (MAC) address on a network device. A MAC Address...
-
How To
How to Scan for Heartbleed bug using Nmap on Kali Linux
In this tutorial we will be scanning a target for the well known Heartbleed SSL Bug using the popular Nmap tool on Kali Linux. The...
-
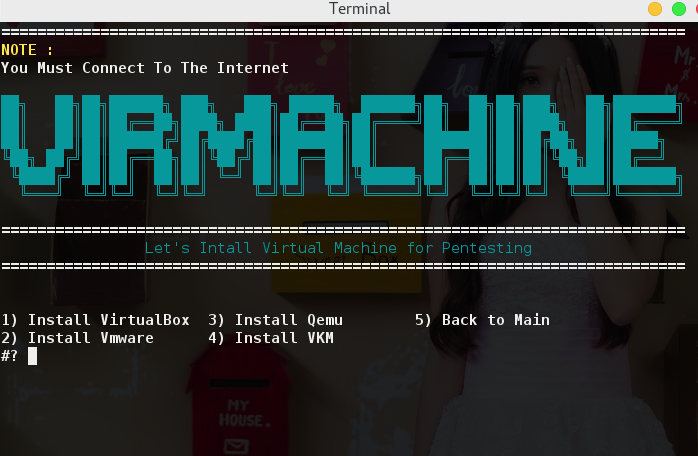
 268How To
268How ToLalin – Hackpack & Kali Linux Tools
Lalin, remake of Lazykali by bradfreda with fixed bugs, new features and updated tools. Lain is compatible with the latest Kali Linux...
-
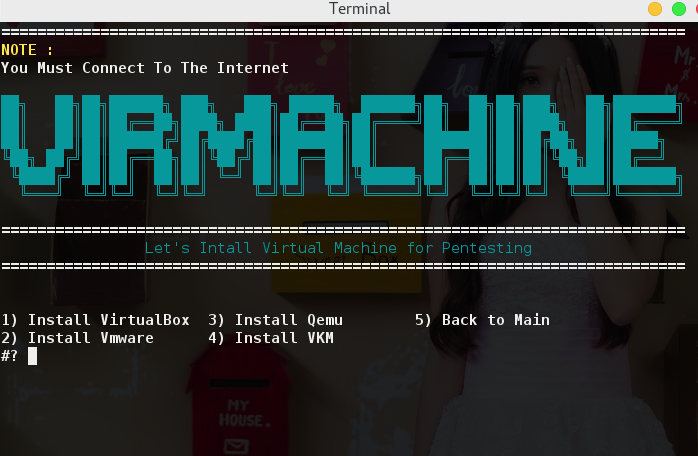
How To
How To Install VMware Tools In Kali Linux 2
Welcome back guys and today we will learn how to install official VMware Tools in Kali Linux 2.0 Sana. There are many articles online...
-
 206Geek
206GeekKali Linux 2016.2 Released — KDE, MATE, LXDE, Xfce, And e17 Flavors Available
Short Bytes: Developers of Kali Linux, one of the best ethical hacking distribution, have announced the second rolling release i.e. Kali Linux...
-

 193Hacked
193HackedParrot Security OS 3.0 “Lithium” — Best Kali Linux Alternative Coming With New Features
Short Bytes: The Release Candidate of Parrot Security OS 3.0 ‘Lithium’ is now available for download. The much-anticipated final release will come...
-
 277Geek
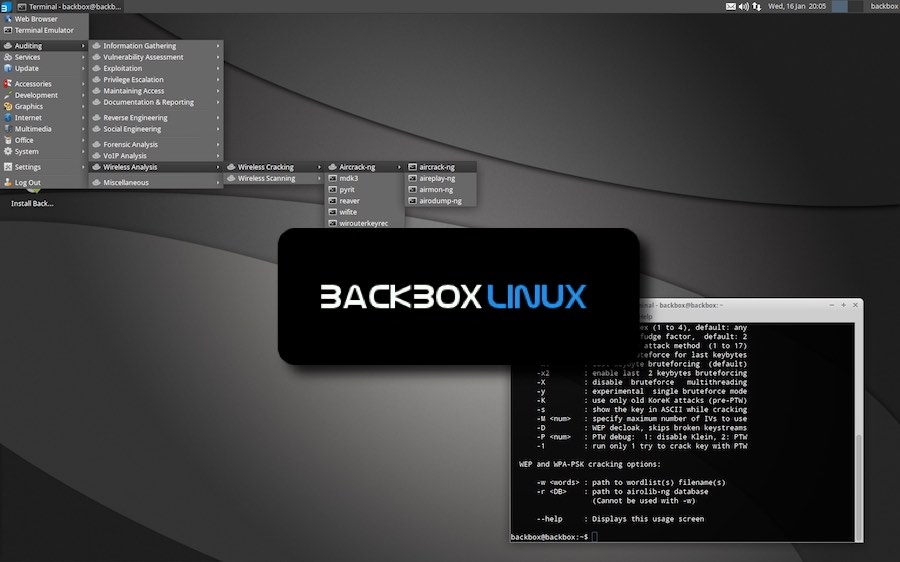
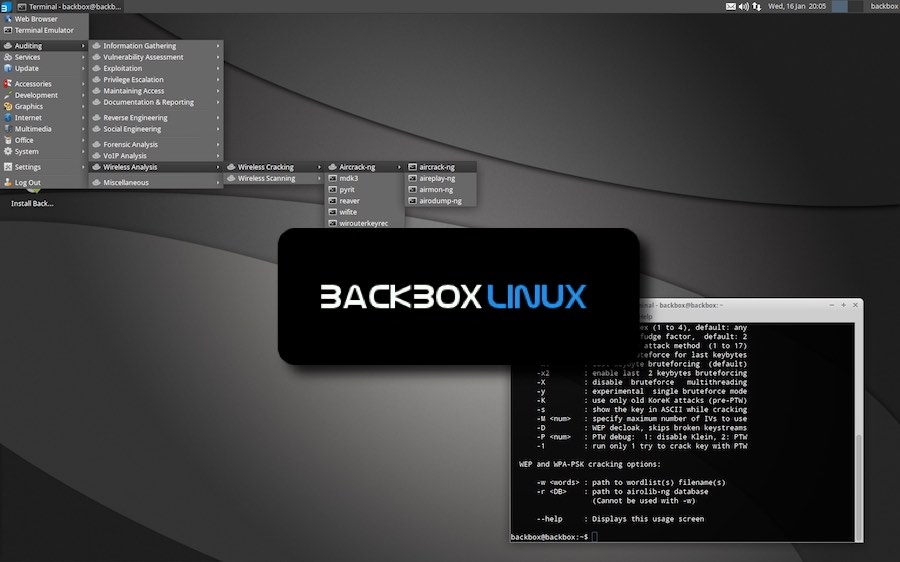
277GeekKali Linux Alternative: BackBox Linux 4.6 Released With Updated Hacking Tools
Short Bytes: BackBox Linux, a Kali Linux alternative, is here with its latest version i.e. BackBox Linux 4.6. Based on Ubuntu Linux,...
-

 403How To
403How ToHow To Install All Kali Linux Tools On Ubuntu Using “Katoolin” Script?
Short Bytes: Many Ubuntu Linux users are willing to use the tools of Kali Linux but they don’t want to install another...
-

 296Anonymity
296AnonymityHow To Setup VPN On Kali Linux For Anonymity
Virtual Private Networks (vpn) create an encrypted ‘tunnel’ between your computer and the host server, with the internet traffic going in and...
-

 280Hacked
280HackedKali Linux Rolling Release — Best Features That Make It The Best OS For Ethical Hackers
Image | Kali.org Short Bytes: Kali Linux, a hacker’s favorite operating system, is now available with first Rolling release. This release ensures...
-

 337Android Hacking
337Android HackingHow to Install Kali Linux on Android
Hacking with Kali Linux on your android device, hacking becomes much easier since you have all the tools (more than 300 pre-installed tools)...
-

 312Vulnerabilities
312VulnerabilitiesHow to Build a Portable Hacking Station with a Raspberry Pi and Kali Linux
Cracking Wi-Fi passwords, spoofing accounts, and testing networks for exploits is all fun enough, but if you want to take the...
-
 221How To
221How ToCrack WPA & WPA2 with Cowpatty and Negpmk on Kali Linux
In this tutorial we are going to teach you How to crack WPA & WPA 2 with cowpatty and negpmk on Kali Linux. We...






