Search results for "Library"
-

 225Vulnerabilities
225VulnerabilitiesCritical vulnerability in a popular PHP library
An ethical hacker from the International Institute of Cyber Security reports the discovery of critical security vulnerability in TCPDF, one of the...
-

 272Hacked
272HackedPopular JavaScript Library Infected By Malicious Code To Steal Cryptocurrency
A malicious code has infected Event-stream JavaScript library with the intention of stealing cryptocurrency from digital wallets. The popular JavaScript library is...
-

 1.9KCryptocurrency
1.9KCryptocurrencyHacker Compromised JavaScript Library to Steal Bitcoin funds
Event-stream Node.js module called is used in millions of web applications, including BitPay’s open-source bitcoin wallet, Copay. This module was reportedly compromised thanks to the...
-
 290Data Security
290Data SecurityApache Struts developers beg users to update library
The team behind Apache Struts has strongly requested users to install the necessary updates to mitigate the risks generated by an old...
-
 218Vulnerabilities
218VulnerabilitiesLIVE555 Streaming library affected by remote code execution vulnerability
This library is used by popular media players, along with a series of integrated devices with streaming capacities Cybersecurity and digital forensics...
-

 223Articles
223ArticlesCritical Code Execution Flaw Found in LIVE555 Streaming Library
Security researchers have discovered a serious code execution vulnerability in the LIVE555 streaming media library—which is being used by popular media players,...
-

 225Data Security
225Data SecurityLIVE555 media streaming library hit by remote code execution flaw
This article has been updated with a statement from Live Networks, Inc explaining that the flaw only affected their implementation of RTSP server,...
-
 295Exploitation
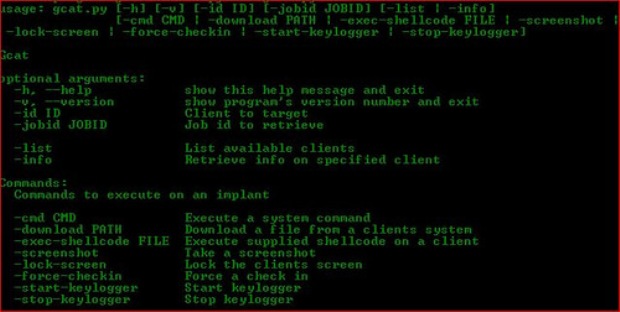
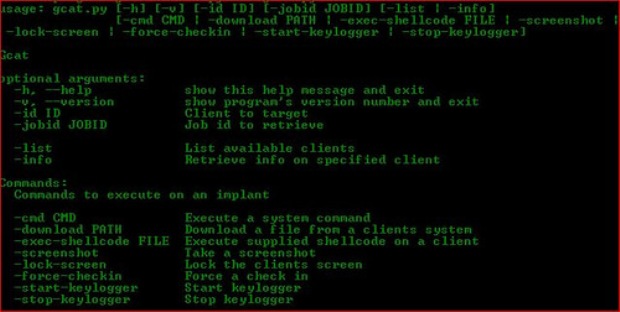
295ExploitationSharpSploit – A .NET Post-Exploitation Library Written in C#
SharpSploit is a .NET post-exploitation library written in C# that aims to highlight the attack surface of .NET and make the use...
-
 302Malware
302MalwareResearchers Found Backdoor in Python Library That Steal SSH Credentials
Recently we saw an attempt to hide a back door in a code library, and today there is a new case. This...
-

 282Reverse Engineering
282Reverse EngineeringPortEx – Java library to analyse Portable Executable files with a special focus on malware analysis and PE malformation robustness
PortEx is a Java library for static malware analysis of Portable Executable files. Its focus is on PE malformation robustness, and anomaly...
-
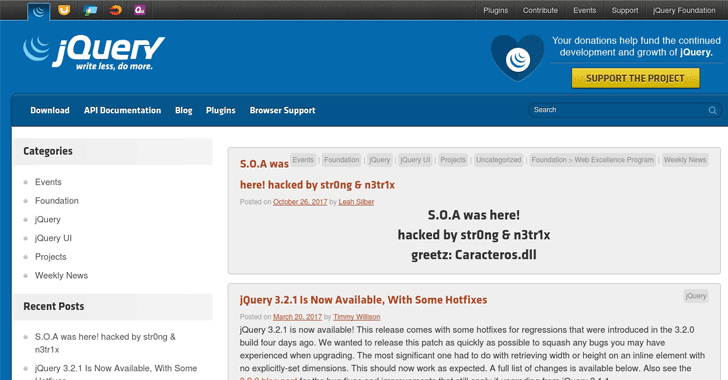
 208Articles
208ArticlesjQuery hacked: Site was hit, but not the library
The official blog of jQuery—most popular JavaScript library used by millions of websites—has been hacked by some unknown hackers, using the pseudonym...
-
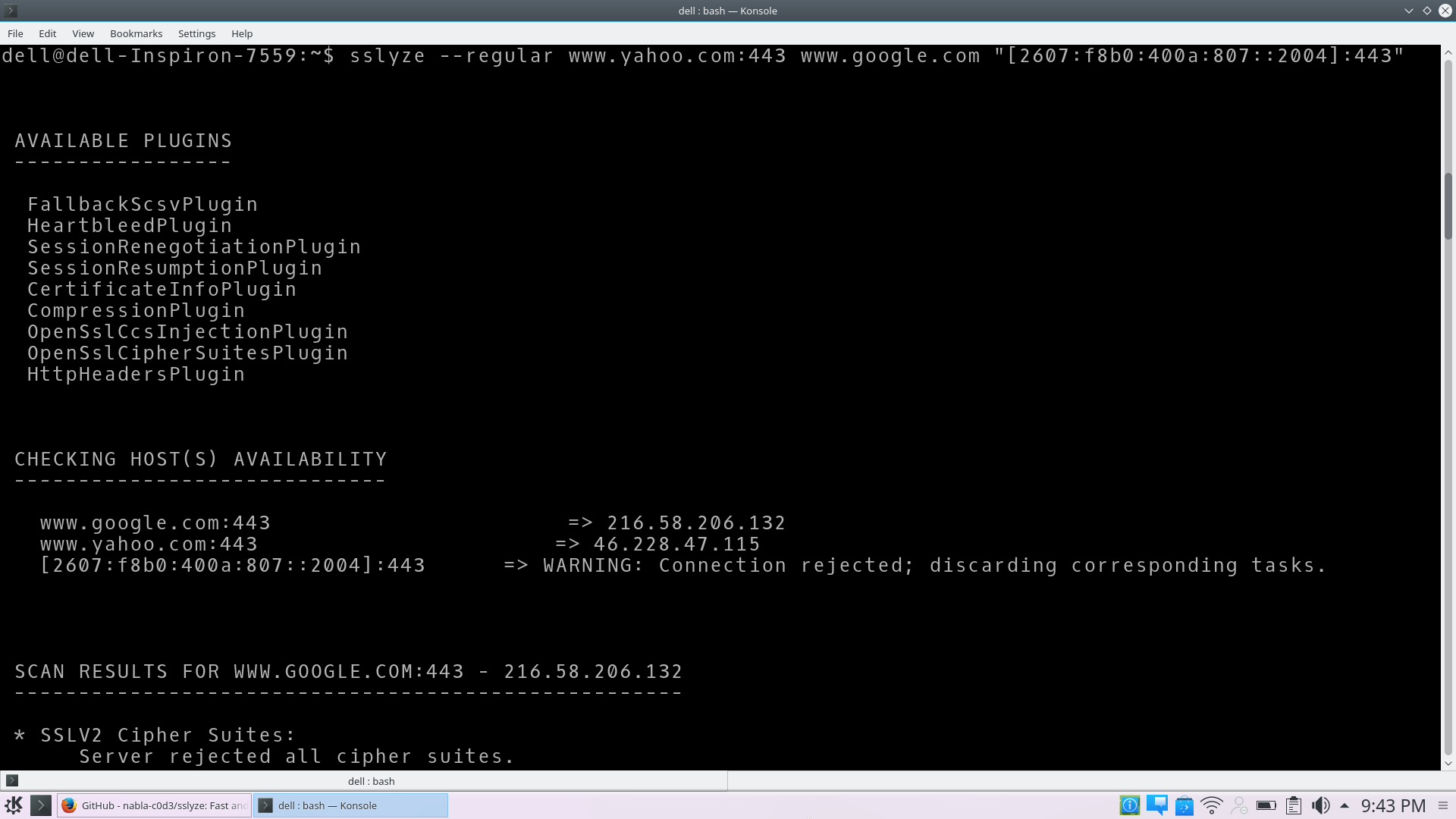
 247Hackers Repository
247Hackers RepositorySSLyze – Fast and powerful SSL/TLS server scanning library
Fast and powerful SSL/TLS server scanning library for Python 2.7 and 3.3+. Description SSLyze is a Python library and a CLI tool...
-

 182Vulnerabilities
182VulnerabilitiesCoding Library Vulnerability May Trickle Down to Thousands of IoT Devices
A vulnerability codenamed Devil’s Ivy is putting thousands of Internet-connected devices at risk of hacking. Discovered by security researchers from Senrio, the...
-

 246Vulnerabilities
246VulnerabilitiesYahoo retires ImageMagick library after 18-byte exploit leaks user email content
The simple line of code made it possible for attackers to view private Yahoo Mail images. Yahoo has decided to retire the...
-
 215Vulnerabilities
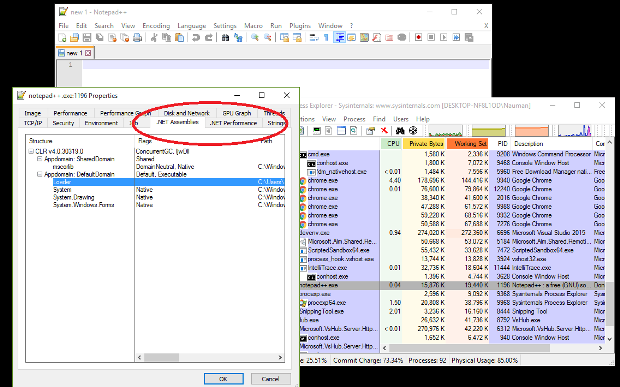
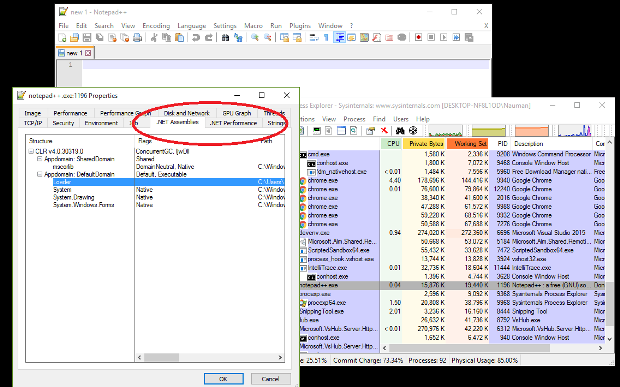
215VulnerabilitiesDLL Injection Using LoadLibrary in C
Tutorials on Windows DLL injections in C have noticable gaps in what they explain. This blog post plus the comments on my...
-
 188Geek
188GeekFAISS: Facebook Just Released A New Open Source Library For Clustering Big Data
Short Bytes: FAISS is an open-source library released by Facebook for similarity search and clustering high-dimensional data. This library finds application in...
-
 150Malware
150MalwareRansomware attack hits St Louis Public library
If you were trying to use the public computers at St Louis Public Library this week you may have experienced more than...
-
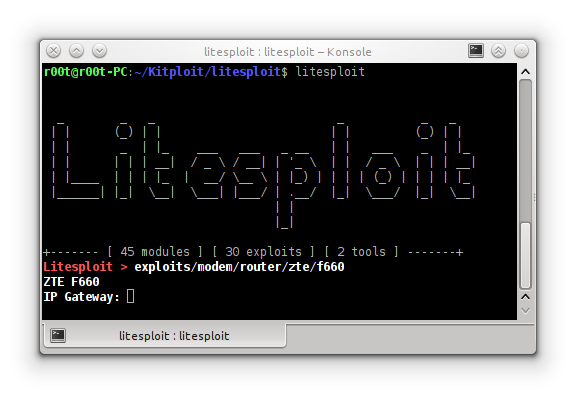
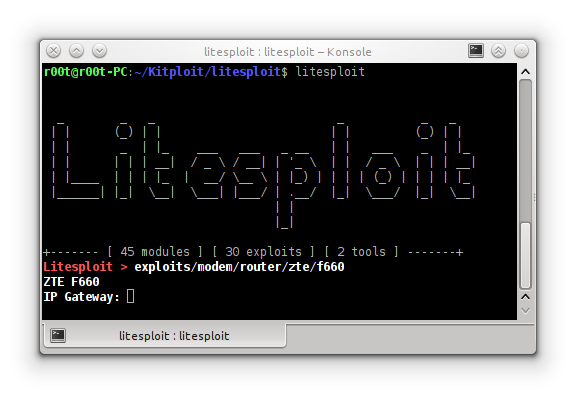 230Hack Tools
230Hack ToolsLitesploit – Library and Intepreter for Penetration Testing Tools
Litesploit is a library and intepreter for penetration testing tools. This includes exploits, tools and litepreter. Litesploit support for Linux like ubuntu...
-

 274News
274NewsAnonymous Hacks National Agriculture Library Domain for OpMonsanto
The online hacktivist Anonymous breached into the subdomain of the National Agriculture Library (NAL) and leaked personal details of staff and other...
-
 151Data Security
151Data SecurityFirst library to support anonymous Internet browsing effort stops after DHS e-mail
Since Edward Snowden exposed the extent of online surveillance by the US government, there has been a surge of initiatives to protect...
-

 237Data Security
237Data SecuritySecure Phone App Library Highly Vulnerable
People who are using a different telephone apps on their cell phones need to be cautious, as a researcher has indicated vulnerabilities...






