Search results for "Malware Analysis"
-

 285How To
285How ToNoriben – Simple, Portable, Malware Analysis Sandbox
Noriben is a Python-based script that works in conjunction with Sysinternals Procmon to automatically collect, analyze, and report on run time indicators...
-

 250How To
250How ToNoriben – A Python Based Sandbox For Malware Analysis
Noriben is a python based script that works in conjunction with Sysinternals Procmon to automatically collect, analyze, and report on runtime indicators of...
-
 150Data Security
150Data SecurityCode of destruction – malware analysis
We should always think twice before running an unknown program downloaded from the Internet. Of course not every application is dangerous, but...
-
 174Malware
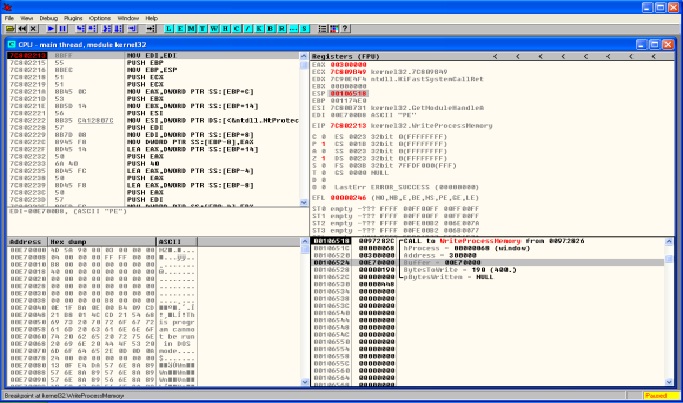
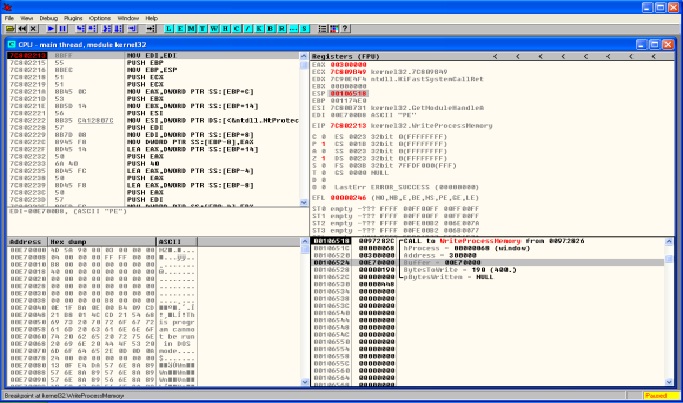
174MalwareMALWARE ANALYSIS – DRIDEX & PROCESS HOLLOWING
Lately the threat actors behind Dridex malware have been very active. Across all the recent Dridex phishing campaigns the technique is the same....
-

 4.3KVulnerabilities
4.3KVulnerabilitiesSystemBC Malware’s C2 Server Analysis Exposes Payload Delivery Tricks
Cybersecurity researchers have shed light on the command-and-control (C2) server workings of a known malware family called SystemBC. “SystemBC can be purchased...
-

 3.9KMalware
3.9KMalwareResearchers Unveal GuLoader Malware’s Latest Anti-Analysis Techniques
Threat hunters have unmasked the latest tricks adopted by a malware strain called GuLoader in an effort to make analysis more challenging....
-

 4.8KMalware
4.8KMalwareAnalysis and Config Extraction of Lu0Bot, a Node.js Malware with Considerable Capabilities
Nowadays, more malware developers are using unconventional programming languages to bypass advanced detection systems. The Node.js malware Lu0Bot is a testament to...
-
 3.1KMalware
3.1KMalwareGuLoader Malware Uses Advanced Anti-Analysis Techniques to Evade Detection
An advanced malware downloader named GuLoader has recently been exposed by cybersecurity researchers at CrowdStrike. This advanced downloader has the capability to...
-

 2.0KMalware
2.0KMalwareNerbian RAT: New malware with advanced anti-analysis and anti-reversing capabilities uses information about WHO and COVID-19 for its spreading
Proofpoint researchers report the detection of a new variant of remote access Trojan (RAT) characterized by the use of multiple techniques and...
-

 1.6KRansomware
1.6KRansomwareResearchers Perform An Analysis on Chinese Malware Used Against Russian Government
Security researchers from the threat hunting and intelligence company Group-IB have revealed that in 2020, at least two espionage groups from China...
-

 225Hack Tools
225Hack ToolsAMIRA – Automated Malware Incident Response & Analysis
AMIRA is a service for automatically running the analysis on the OSXCollector output files. The automated analysis is performed via OSXCollector Output...
-
 307Malware Analysis
307Malware AnalysisPEframe – Tool To Perform Static Analysis On Malware
PEframe is an open source tool to perform static analysis on Portable Executable malware and generic suspicious file. It can help malware...
-

 264Malware
264MalwareUrsnif Malware Variant Performs Malicious Process Injection in Memory using TLS Anti-Analysis Evasion Trick
A Sophisticated Ursnif Malware variant using manipulated TLS call back Anti-Analysis Technique while injecting the Child Process for changing the entry point....
-

 303Malware
303MalwareEMOTET Malware Hijacking the Windows API & Evade the Sandbox Analysis
A wide Spread EMOTET malware emerging again with new stealthy capabilities to hijack the Windows API and evade the sandbox detection which also gives...
-
 106Malware
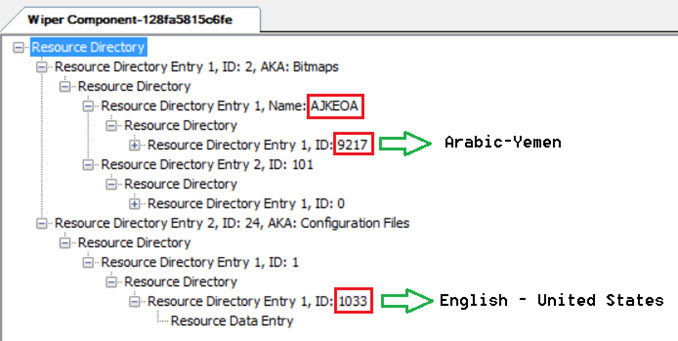
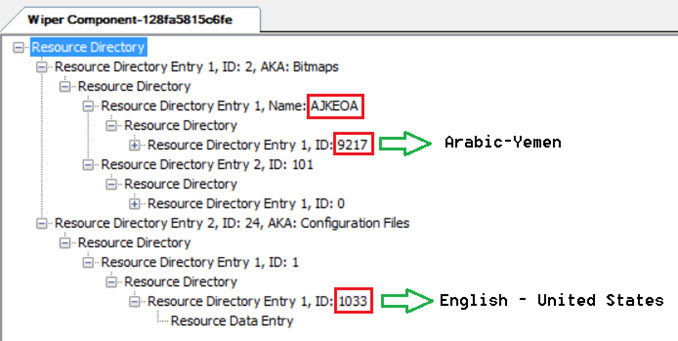
106MalwareDetailed threat analysis of Shamoon 2.0 Malware
Our Previous post talked about the initial overview of the Shamoon 2.0 sample .This analysis is a continuation of our last post...






