Search results for "Malware"
-
 550Cyber Attack
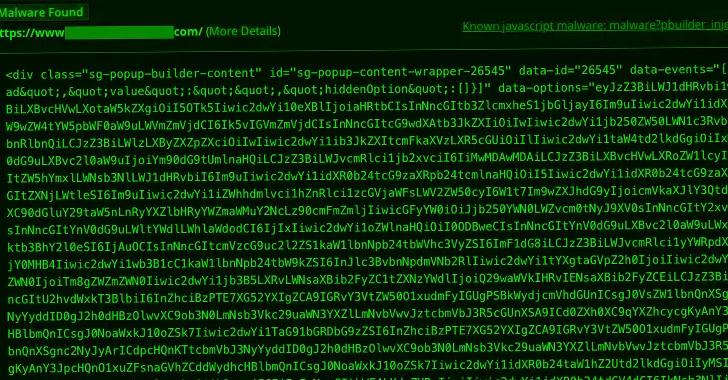
550Cyber AttackMalware Campaign Exploits Popup Builder WordPress Plugin to Infect 3,900+ Sites
A new malware campaign is leveraging a high-severity security flaw in the Popup Builder plugin for WordPress to inject malicious JavaScript code....
-
 4.4KTutorials
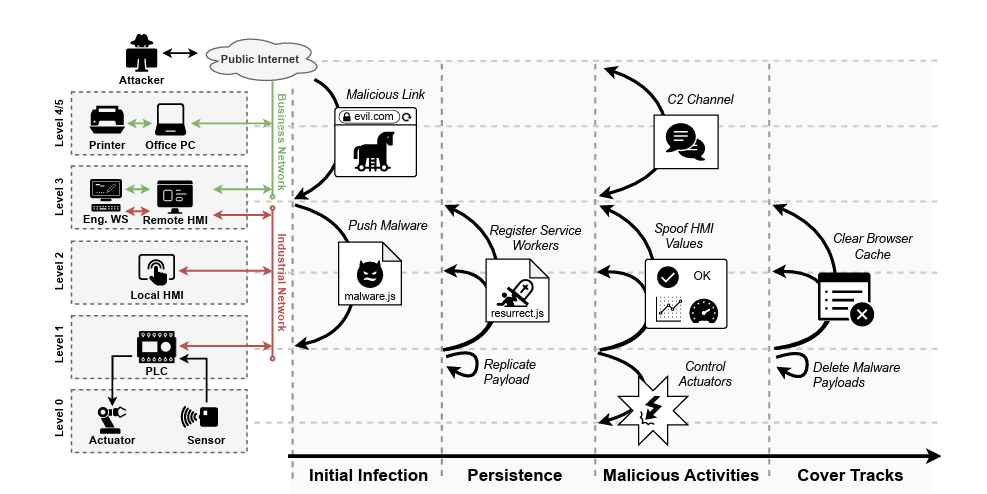
4.4KTutorialsWeb-Based PLC Malware: A New Technique to Hack Industrial Control Systems
In a significant development that could reshape the cybersecurity landscape of industrial control systems (ICS), a team of researchers from the Georgia...
-
 4.2KMalware
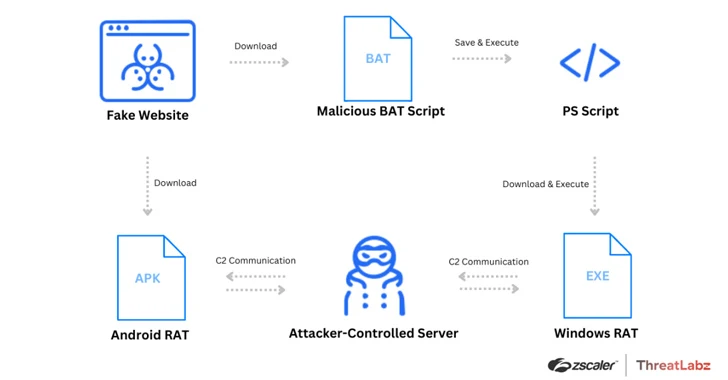
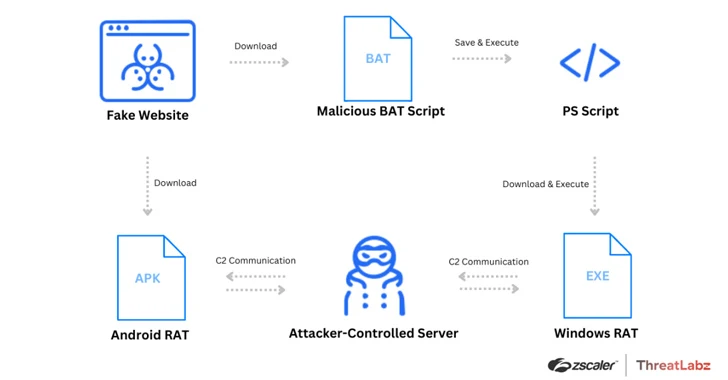
4.2KMalwareWatch Out for Spoofed Zoom, Skype, Google Meet Sites Delivering Malware
Threat actors have been leveraging fake websites advertising popular video conferencing software such as Google Meet, Skype, and Zoom to deliver a...
-

 3.4KMalware
3.4KMalwareHackers Exploit ConnectWise ScreenConnect Flaws to Deploy TODDLERSHARK Malware
North Korean threat actors have exploited the recently disclosed security flaws in ConnectWise ScreenConnect to deploy a new malware called TODDLERSHARK. According...
-

 5.0KMalware
5.0KMalwareNew BIFROSE Linux Malware Variant Using Deceptive VMware Domain for Evasion
Cybersecurity researchers have discovered a new Linux variant of a remote access trojan (RAT) called BIFROSE (aka Bifrost) that uses a deceptive...
-
 148Malware
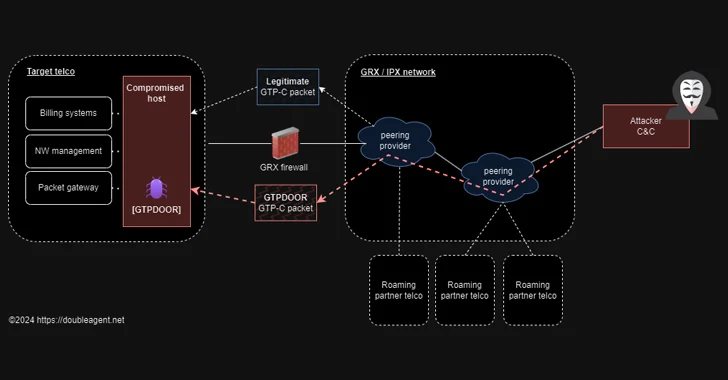
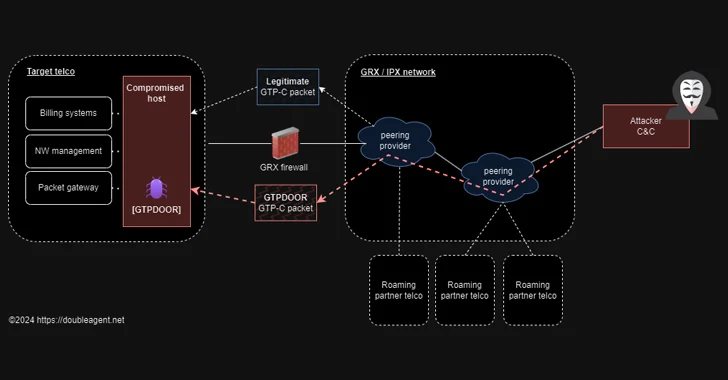
148MalwareGTPDOOR Linux Malware Targets Telecoms, Exploiting GPRS Roaming Networks
Threat hunters have discovered a new Linux malware called GTPDOOR that’s designed to be deployed in telecom networks that are adjacent to...
-
 3.8KMalware
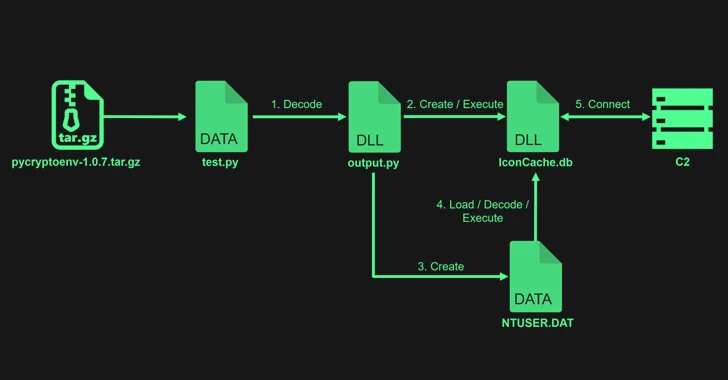
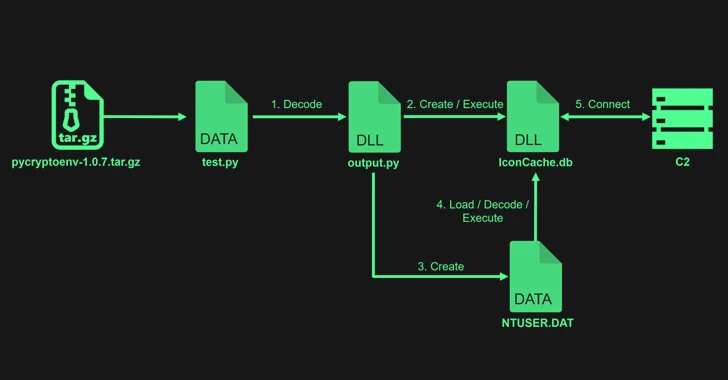
3.8KMalwareLazarus Exploits Typos to Sneak PyPI Malware into Dev Systems
The notorious North Korean state-backed hacking group Lazarus uploaded four packages to the Python Package Index (PyPI) repository with the goal of...
-

 2.3KVulnerabilities
2.3KVulnerabilitiesChinese Hackers Exploiting Ivanti VPN Flaws to Deploy New Malware
At least two different suspected China-linked cyber espionage clusters, tracked as UNC5325 and UNC3886, have been attributed to the exploitation of security...
-

 3.9KCyber Attack
3.9KCyber AttackTimbreStealer Malware Spreading via Tax-themed Phishing Scam Targets IT Users
Mexican users have been targeted with tax-themed phishing lures at least since November 2023 to distribute a previously undocumented Windows malware called...
-

 2.5KMalware
2.5KMalwareDormant PyPI Package Compromised to Spread Nova Sentinel Malware
A dormant package available on the Python Package Index (PyPI) repository was updated nearly after two years to propagate an information stealer...
-
 2.8KMalware
2.8KMalwareRussian Government Software Backdoored to Deploy Konni RAT Malware
An installer for a tool likely used by the Russian Consular Department of the Ministry of Foreign Affairs (MID) has been backdoored...
-

 3.8KMalware
3.8KMalwareNew Migo Malware Targeting Redis Servers for Cryptocurrency Mining
A novel malware campaign has been observed targeting Redis servers for initial access with the ultimate goal of mining cryptocurrency on compromised...
-

 4.0KMalware
4.0KMalwareFBI’s Most-Wanted Zeus and IcedID Malware Mastermind Pleads Guilty
A Ukrainian national has pleaded guilty in the U.S. to his role in two different malware schemes, Zeus and IcedID, between May...
-
 1.2KMalware
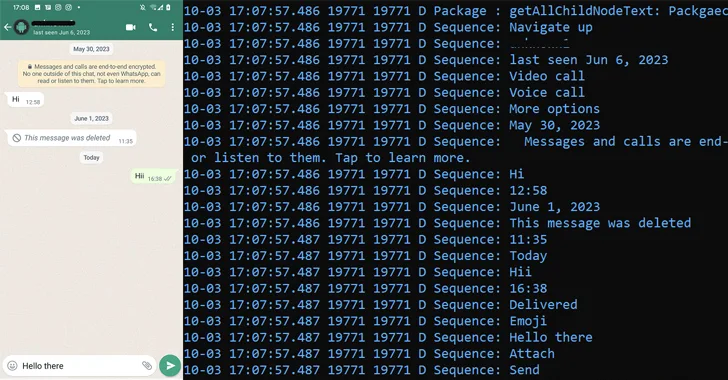
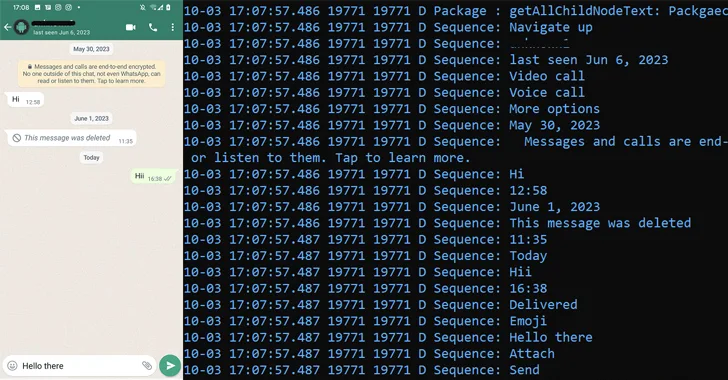
1.2KMalwareChinese Hackers Using Deepfakes in Advanced Mobile Banking Malware Attacks
A Chinese-speaking threat actor codenamed GoldFactory has been attributed to the development of highly sophisticated banking trojans, including a previously undocumented iOS...
-

 586Malware
586MalwareBumblebee Malware Returns with New Tricks, Targeting U.S. Businesses
The infamous malware loader and initial access broker known as Bumblebee has resurfaced after a four-month absence as part of a new...
-

 2.2KMalware
2.2KMalwareDarkMe Malware Targets Traders Using Microsoft SmartScreen Zero-Day Vulnerability
A newly disclosed security flaw in the Microsoft Defender SmartScreen has been exploited as a zero-day by an advanced persistent threat actor...
-

 4.9KMalware
4.9KMalwareRaspberry Robin Malware Upgrades with Discord Spread and New Exploits
The operators of Raspberry Robin are now using two new one-day exploits to achieve local privilege escalation, even as the malware continues...
-

 2.8KMalware
2.8KMalwareMoqHao Android Malware Evolves with Auto-Execution Capability
Threat hunters have identified a new variant of Android malware called MoqHao that automatically executes on infected devices without requiring any user...
-
 1.9KMalware
1.9KMalwarePatchwork Using Romance Scam Lures to Infect Android Devices with VajraSpy Malware
The threat actor known as Patchwork likely used romance scam lures to trap victims in Pakistan and India, and infect their Android...
-

 2.6KMalware
2.6KMalwareDirtyMoe Malware Infects 2,000+ Ukrainian Computers for DDoS and Cryptojacking
The Computer Emergency Response Team of Ukraine (CERT-UA) has warned that more than 2,000 computers in the country have been infected by...
-

 2.9KVulnerabilities
2.9KVulnerabilitiesFritzFrog Returns with Log4Shell and PwnKit, Spreading Malware Inside Your Network
The threat actor behind a peer-to-peer (P2P) botnet known as FritzFrog has made a return with a new variant that leverages the...






