Search results for "Malware"
-
 191Data Security
191Data SecurityRussian Hacker Pleads Guilty for Role in Infamous Linux Ebury Malware
The US Department of Justice announced yesterday that Maxim Senakh, 41, of Velikii Novgorod, Russia, pleaded guilty for his role in the...
-
 148Malware
148MalwareHumbled Malware Author Leaks His Own Source Code to Regain Community’s Trust
The author of the Nuclear Bot banking trojan has leaked the source code of his own malware in a desperate attempt to...
-

 151Malware
151Malware16 years of Mac OS X: Secure but not invincible to malware
Mac OS X is still secure 16 years after its creation, but increasingly being targeted by cybercriminals. No operating system is 100%...
-

 170Malware
170MalwareWord Document Spreads Macro Malware Targeting Both Windows and macOS
After last month security researchers discovered the first-ever Word document spreading macro malware on macOS, last week, researchers from Fortinet spotted a...
-

 154Hacked
154HackedDoubleAgent Attack Turns Your Antivirus Into Malware And Hijacks Your PC (Updated)
Short Bytes: Cybellum security researchers have uncovered a new attack mechanism that can be used to take control of your antivirus and turn...
-

 100Malware
100MalwareMost Industrial Control Systems Get Infected with Malware by Accident
The vast majority of malware incidents that take place at industrial facilities around the world are just accidental infections, albeit a very...
-

 147Malware
147MalwareChinese Crooks Use Fake Cellular Telephony Towers to Spread Android Malware
Malware authors in China are using fake base transceiver stations (BTSs), which is equipment usually installed on cellular telephone towers, to send...
-

 316Vulnerabilities
316VulnerabilitiesAttackers Leverage Excel, PowerShell and DNS in Latest Non-Malware Attack
Increasingly, cyberattackers have been leveraging “non-malware” attack methods to target vulnerable organizations. Recently, the Carbon Black Threat Research Team was alerted about...
-

 135Malware
135MalwareRansomware operators are hiding malware deeper in installer packages
We are seeing a wave of new NSIS installers used in ransomware campaigns. These new installers pack significant updates, indicating a collective...
-

 281Malware
281MalwareMajikPOS Dual malware targeting businesses across North America and Canada
A new group of POS malware family made its presence targeting business systems around North America and Canada.The objective of PoS malware...
-
 196Malware
196MalwareNew MajikPOS Malware targets users in across North America and Canada
Trend Micro has discovered a new PoS malware, tracked as MajikPOS, that is targeting business in North America and Canada. Security experts...
-

 249Geek
249GeekBeware; 36 Android Devices Shipped with Preinstalled Malware
Android devices have remained the center of attraction for malicious cyber criminals since forever. Not only do they churn out fake, infected...
-
 267Malware
267Malware“Super Malware” Steals Encryption Keys From Intel SGX Isolated Memory Fields
A scientist’s Team from Graz University of Technology revealed the method that leaking the encryption data from Intel SGX (Software Guard Extensions...
-

 259Malware
259MalwareHancitor Makes First Appearance in Top Five Most wanted malware – February 2017
Hancitor has grown into the main five of the ‘most wanted’ malware families worldwide for the first time, reported by Checkpoint Threat Intelligence...
-

 189Data Security
189Data Security“Super Malware” Steals Encryption Keys from Intel SGX Enclaves
In a research paper published at the end of February, a team of five scientists from the Graz University of Technology has...
-
 170Vulnerabilities
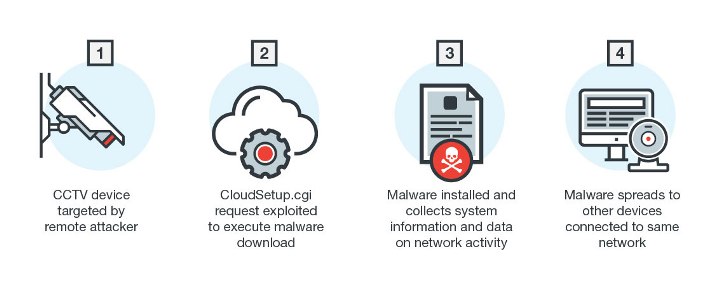
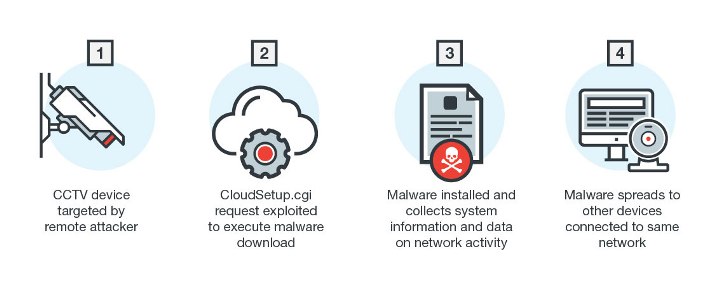
170VulnerabilitiesNew Linux Malware Exploits CGI Vulnerability
Linux has long been the preferred operating system for enterprise platforms and Internet of Things (IoT) manufacturers. Linux-based devices are continually being...
-

 234Cyber Attack
234Cyber AttackAttention!! Pre-Installed Android Malware Found High End Smartphones
Own a modern-day Android phone? Do not expect it to be an easy slate. As a minimum 36 high-end smartphone fashions belonging...
-
 280Malware
280MalwarePre-Installed Malware Discovered in 38 Well-Known Android Devices Including Samsung , Lenovo , Nexus
Mobile Threat prevention Team from Checkpoint Software Discovered Pre-Installed malware in more than 30 android smartphone models belonging to popular Mobile companies...
-

 113Malware
113MalwareMalware found preinstalled on 38 Android phones used by 2 companies
Malicious apps were surreptitiously added somewhere along the supply chain. A commercial malware scanner used by businesses has recently detected an outbreak...
-

 219Malware
219MalwareMobile security: The reality of malware … augmented
Originally, it was expected that mobile devices would evolve to become handheld computers with capabilities similar to any desktop. It is clear...
-

 175Vulnerabilities
175VulnerabilitiesMicrosoft Excel Files Increasingly Used To Spread Malware
Over the last few years we have received a number of emails with attached Word files that spread malware. Now it seems...






