Search results for "Memory"
-
 300Forensics Tools
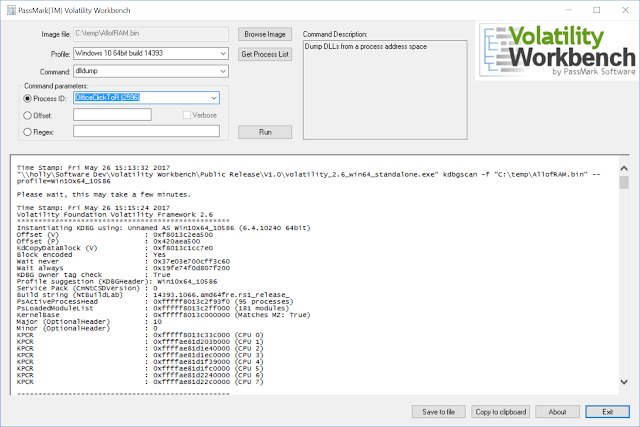
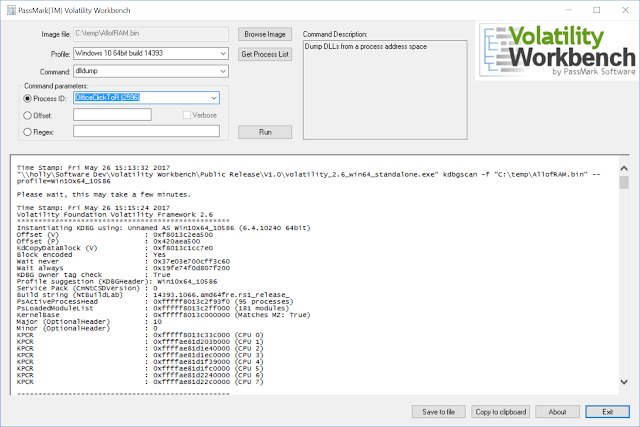
300Forensics ToolsVolatility Workbench – A GUI For Volatility Memory Forensics
Volatility Workbench is a graphical user interface (GUI) for the Volatility tool. Volatility is a command line memory analysis and forensics tool...
-

 194Incidents
194IncidentsFine for Heathrow Airport for missing memory stick
Heathrow Airport has been fined with £120k by the Information Commissioner Office for serious deficiencies in data protection The fact arose after...
-

 224Hack Tools
224Hack ToolsXenoscan – Open source memory scanner written in C++
XenoScan is a memory scanner which can be used to scan the memory of processes to locate the specific locations of important...
-

 251Evasion & Obfuscation
251Evasion & ObfuscationCoffeeShot: Avoid Detection with Memory Injection
CoffeeShot is an evasion framework that injects payload from Java-based programs into designated processes on Microsoft Windows. It assists blue team members...
-
 252Malware
252MalwareMost Important USB Memory Sticks based Cyber Attack Mitigation Steps for Your Organization
Among the ten major cyber threats identified by BSI in 2016, the use of portable peripheral devices ranks second. While the same agency suggests engaging...
-
 243Geek
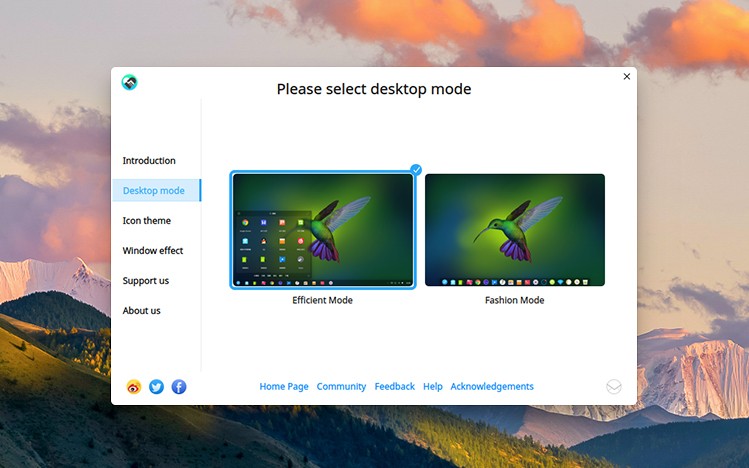
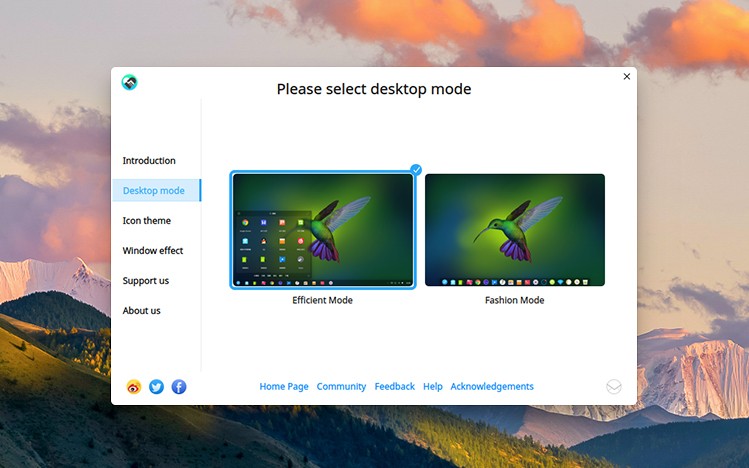
243Geekdeepin 15.7 Linux Distro Released With Size Reduction And Memory Optimization
deepin desktop edition is known to often preferred by the users who love to use a system that’s easy to use and...
-

 237Hack Tools
237Hack ToolsUnicorn – Downgrade Attack & Inject Shellcode Straight into Memory
Unicorn is a simple tool for using a PowerShell downgrade attack and inject shellcode straight into memory. Based on Matthew Graeber’s PowerShell...
-
 251Exploitation Tools
251Exploitation ToolsLinux Screenshot XWindows – Volatility Plugin To Extract X Screenshots From A Memory Dump
The goal of this volatility plugin is to extract a screenshot of all open X windows from a memory dump. Overview The...
-
 389Computer Forensics
389Computer ForensicsLive Forensics Analysis with Computer Volatile Memory
The field of computer Forensics Analysis involves identifying, extracting, documenting, and preserving information that is stored or transmitted in electronic or magnetic...
-
 244Geek
244GeekBig Memory Leak Bug Found In GNOME Shell; Might Remain Unpatched In Ubuntu 18.04
Gnome has been Ubuntu’s default desktop environment for a while. Recently, some Ubuntu 17.10 users have started to observe a memory leak...
-

 137Incidents
137IncidentsHow Memory Leaks Happen in a Java Application
Introduction to Memory Leaks In Java Apps One of the core benefits of Java is the JVM, which is an out-of-the-box memory management....
-
 230Computer Forensics
230Computer ForensicsDAMM – An Open Source Memory Analysis Tool
DAMM (Differential Analysis of Malware in Memory) is an open source memory analysis tool built on top of Volatility. It is meant as...
-
 219Forensics Tools
219Forensics ToolsCryKeX – Linux Memory Cryptographic Keys Extractor
Some work has been already published regarding the subject of cryptograhic keys security within DRAM. Basically, we need to find something that looks like...
-

 427Malware
427MalwareESET malware researchers awarded prize in open‑source memory forensics competition
The Volatility Foundation, the non-profit organization behind the Volatility Framework, sponsors the yearly Volatility Plugin Contest to acknowledge the best forensic tools...
-

 264Malware
264MalwareUrsnif Malware Variant Performs Malicious Process Injection in Memory using TLS Anti-Analysis Evasion Trick
A Sophisticated Ursnif Malware variant using manipulated TLS call back Anti-Analysis Technique while injecting the Child Process for changing the entry point....
-
 134Vulnerabilities
134VulnerabilitiesAttacking a co-hosted VM: A hacker, a hammer and two memory modules
Row-hammer is hardware bug that can cause bit-flips in physical RAM. Mark Seaborn and Thomas Dullien were the first to exploit the DRAM row-hammer bug to...
-
 245Vulnerabilities
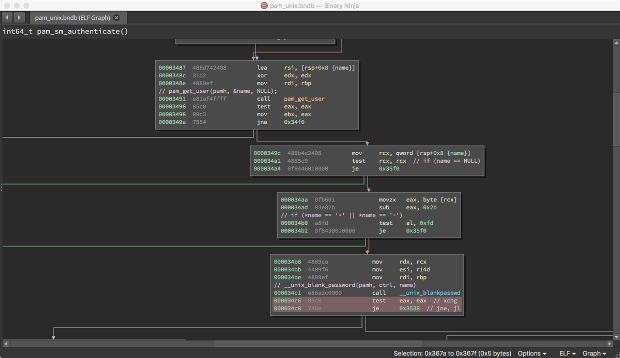
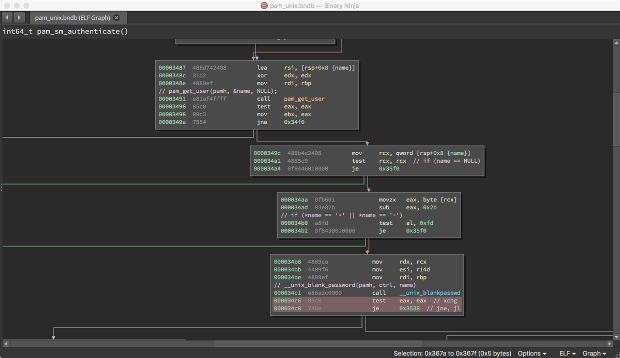
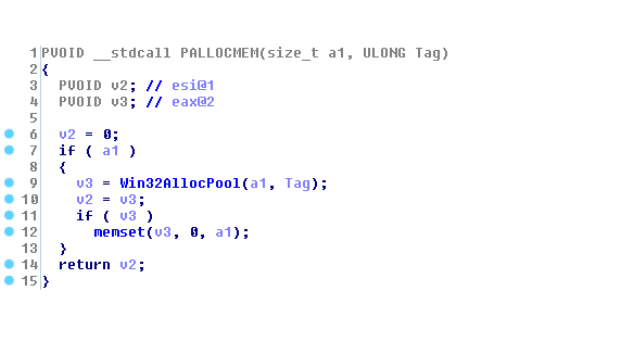
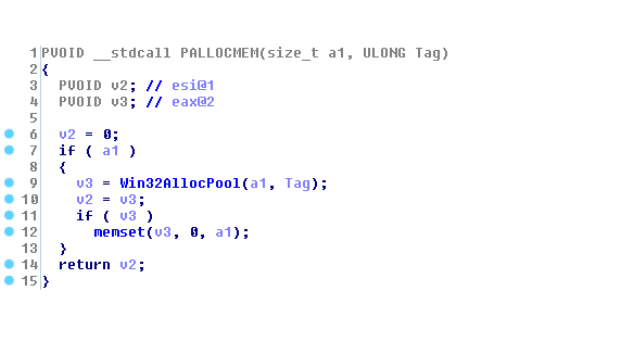
245VulnerabilitiesUsing Binary Diffing to Discover Windows Kernel Memory Disclosure Bugs
Patch diffing is a common technique of comparing two binary builds of the same code – a known-vulnerable one and one containing...
-
 280Computer Forensics
280Computer ForensicsMemoryze – Memory Forensics Tool
Memoryze is a free memory forensic software that helps incident responders find evil in live memory. It can acquire and/or analyze memory images...
-
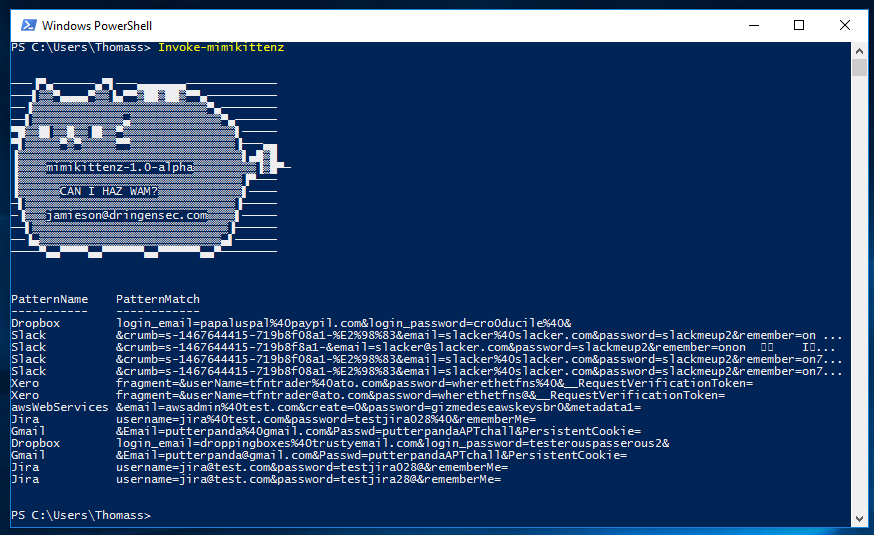
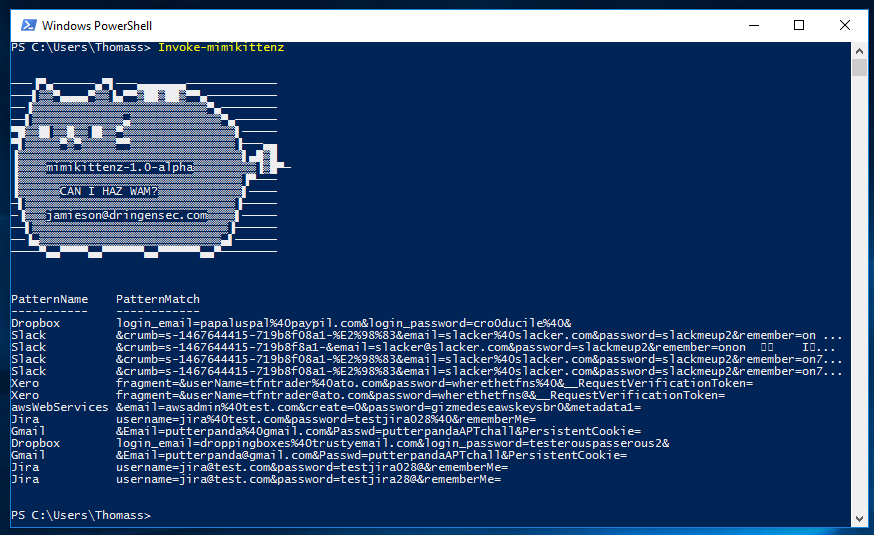 98Hackers Repository
98Hackers Repositorymimikittenz – Powershell Tool for Extracting Juicy info from Memory RAM
A post-exploitation powershell tool for extracting juicy info from memory. mimikittenz mimikittenz is a post-exploitation powershell tool that utilizes the Windows function...
-
 117Vulnerabilities
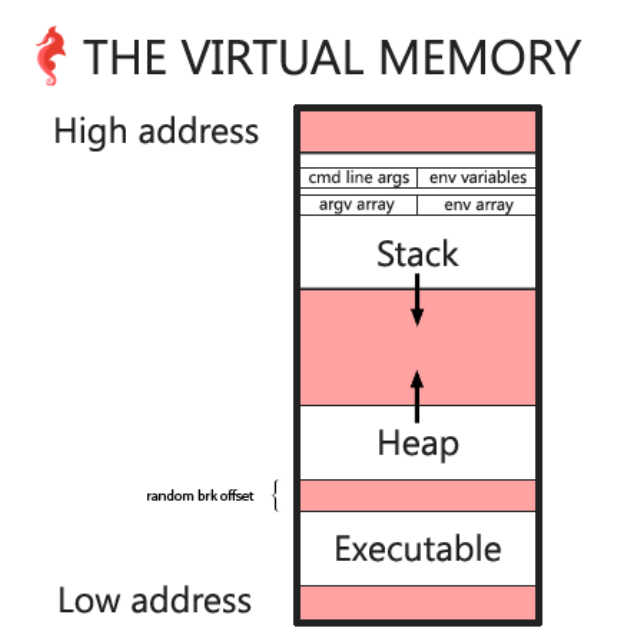
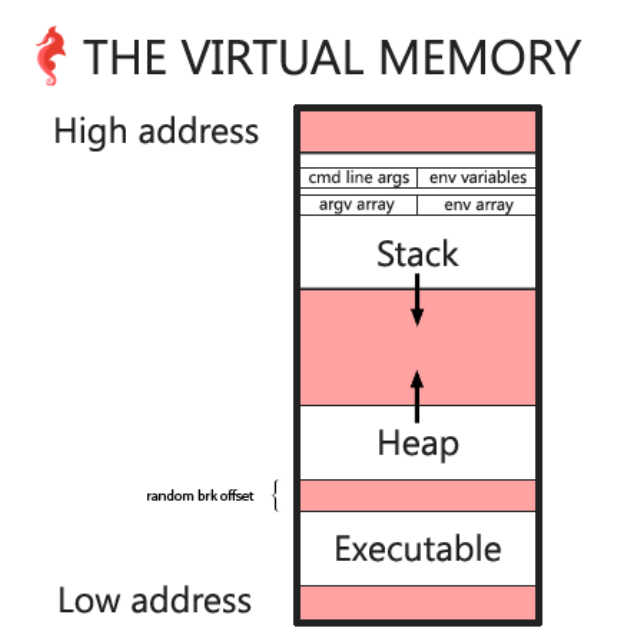
117VulnerabilitiesHack the Virtual Memory: malloc, the heap & the program break
The heap In this chapter we will look at the heap and malloc in order to answer some of the questions we...
-

 173Vulnerabilities
173VulnerabilitiesGoogle Project Zero team the worst Windows RCE vulnerability in recent memory
Hackers at the Google Project Zero team have discovered another critical Windows RCE vulnerability, the worst Windows RCE in recent memory. Security...






