Search results for "Opera"
-

 353Cyber Crime
353Cyber CrimeRussian Cybercriminal Pleads Guilty to Operating Kelihos Botnet
A Russian national namely Peter Yuryeich Levashov has pleaded guilty to operating the Kelihos botnet, which was used to launch a huge...
-
 349Malware
349MalwareLazarus APT Group Attack Cryptocurrency Exchange using macOS Malware Under the Operation AppleJeus
A cyber espionage APT group called Lazarus hits the cryptocurrency exchanges using fake installer and macOS malware using variously sophisticated techniques. Lazarus...
-

 171Malware
171MalwareOperation Red Signature Deliver’s Malware to Target Organizations Through Outside Partner Network
Supply Chain Attacks occurs is an advanced threat that determines the weak link in the supply chain to infiltrate into the organization...
-

 316Data Security
316Data SecurityBattle against fraudulent online operations in Australia
Fraud events in e-commerce are increasing Bad news for Australian online shoppers: the number of online scams increases steadily. According to cyber...
-
 209Hacking Tools
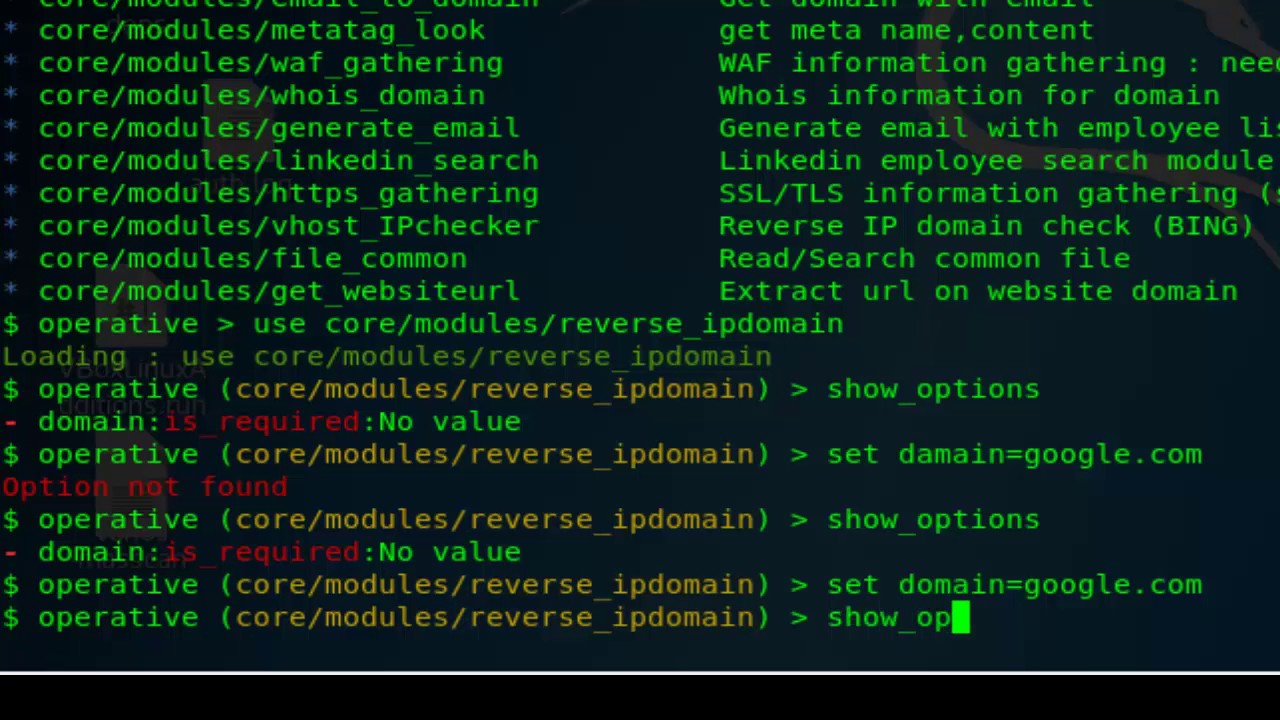
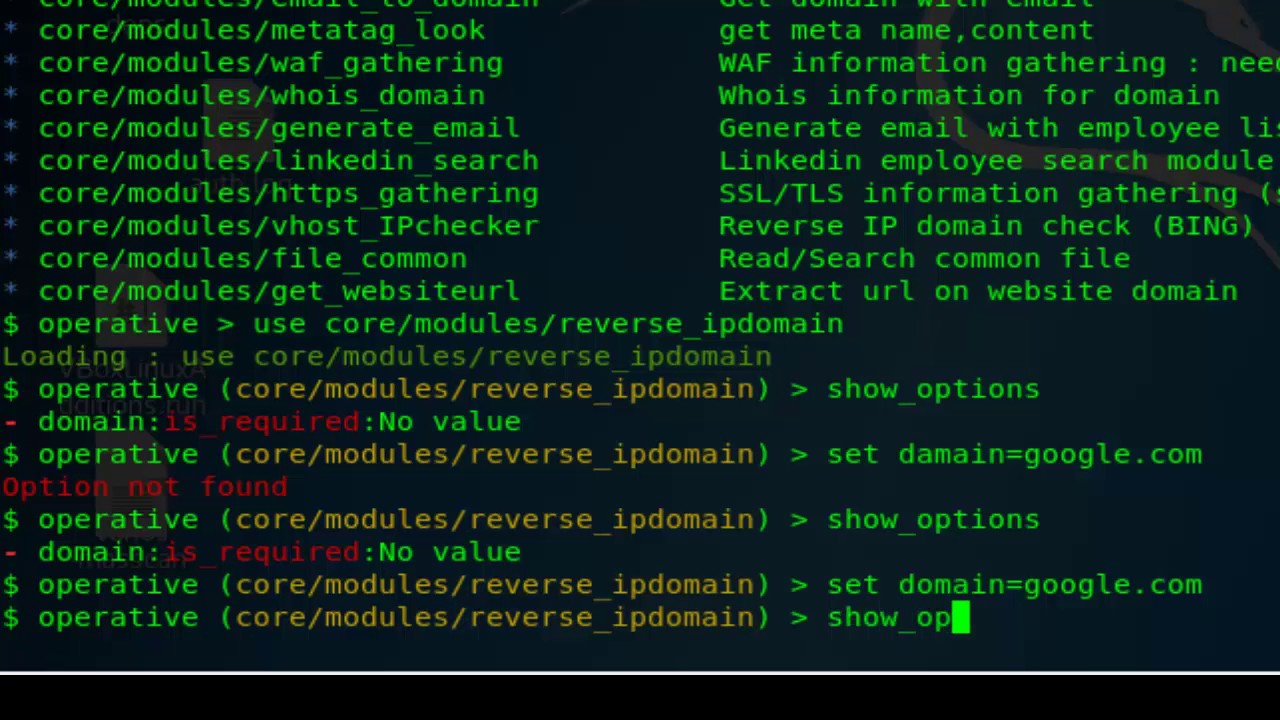
209Hacking ToolsOperative Framework – Open Source Intelligence Gathering Tool
The Operative Framework tool can be used within a red team/social engineering engagement to collect information regarding websites and enterprises. The tool...
-

 309Information Gathering
309Information GatheringBlack Owl – Tool To Gather Information, Based On Operative-Framework
This is a simple tool to gather information, based on Operative-Framework. Requirements requests pythonwhois beautifulsoup4 Install requirements $ pip install -r requirements.txt...
-
 190Hacked
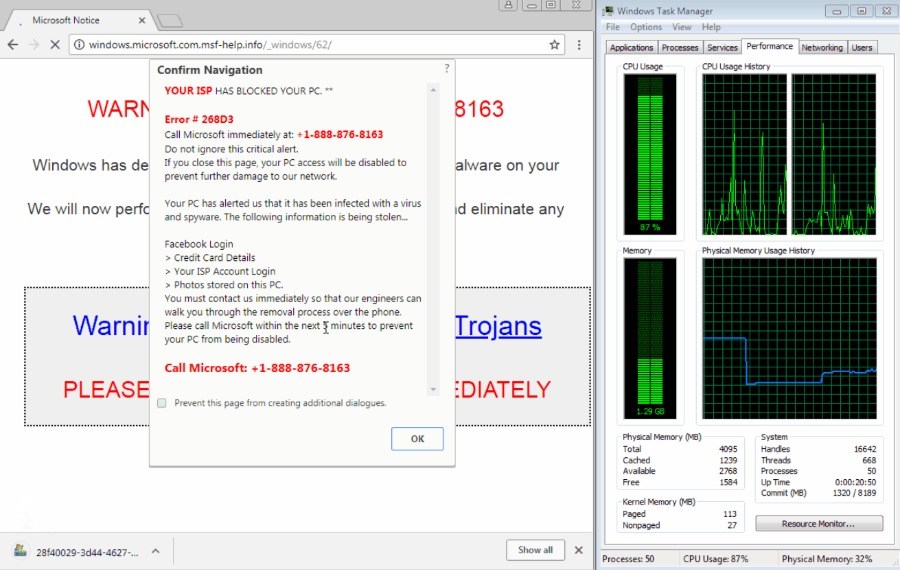
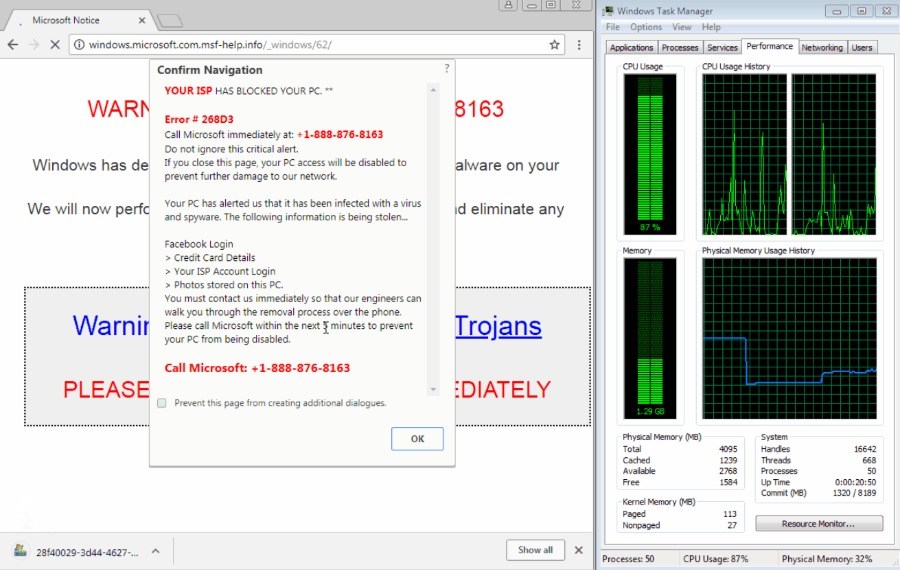
190HackedGoogle Chrome’s “Download Bomb” Attack Is Back, Also Affects Firefox, Opera, Brave
Earlier this year, a bug in Google Chrome was a rejoice for tech support scammers who could freeze people’s browser using the...
-

 276Incidents
276IncidentsHackers attack satellite operators, claims Symantec
Symantec, a software developer, claims to have discovered a cyber espionage campaign focused on infiltrating three telecom operators in Southeast Asia,...
-

 161Data Security
161Data SecurityShip Hacking puts operations in English Channel at risk
Commonlly used technology for ship monitoring can be hacked to falsify the location and size of boats for the purpose of firing...
-

 295Cyber Events
295Cyber EventsDenmark’s largest train operator hit by service crippling DDoS attack
Another day, another DDoS attack causing passengers a great deal of trouble. The largest train operating company in Danmark “Danske Statsbaner” (DSB...
-

 320News
320NewsHacker access critical code of British cell operator EE
EE, a British mobile network giant owned by BT Group has been accused of leaving a critical code repository on an open-source tool protected...
-
 311DDOS
311DDOSWorld’s Biggest DDoS Attack Selling Market Place Finally Taken Down by Operation Power OFF
Administrators of DDoS-for-hire Service were arrested as a result of a joint Operation Power OFF led by the Dutch police, and UK’s...
-

 192Articles
192ArticlesLitepay CEO Terminates Project Operations, Plans to Sell Company After Butting Heads with Litecoin Foundation
Author: Colin Harper Litepay, a Litecoin-specific payment processor, is closing up shop–until it finds a buyer, that is. According to a blog...
-

 441Lists
441Lists12 Best Operating Systems For Ethical Hacking And Penetration Testing | 2018 Edition
Wondering which is the best operating system for ethical hacking and pen testing purposes? Trying to solve this problem, Fossbytes has prepared...
-

 196Malware
196MalwareOperation Honeybee – A Cyber Attack Leveraging a SYSCON Backdoor Using MS Word Documents
A new cyber attack called “Operation Honeybee” deploying the SYSCON Backdoor Using MS Word to attack the humanitarian aid organizations. An SYSCON backdoor...
-

 232Anonymity
232AnonymityWhonix – An Operating System Focused On Anonymity, Privacy and Security
Whonix is a free and open-source desktop operating system (OS) that is specifically designed for advanced security and privacy. Based on Tor,...
-

 266Malware
266MalwareUK-led police operation quashes Luminosity Link RAT
A hacking tool that was able to give full remote control of a victim’s computer to anyone with nefarious intentions has been taken...
-

 513Hacking
513HackingUK‑led police operation quashes Luminosity Link RAT
The investigation showed that the tool, which required little technical knowledge to deploy, had over 8,600 users in 78 countries. Victims are...
-

 332Data Security
332Data SecurityOpera Mobile Browser for Android & iOS Blocks Cryptocurrency Mining
Last month Opera introduced its browser’s 50 beta version with built-in cryptocurrency mining blocker for desktops. Now, the company has launched anti-cryptocurrency...
-
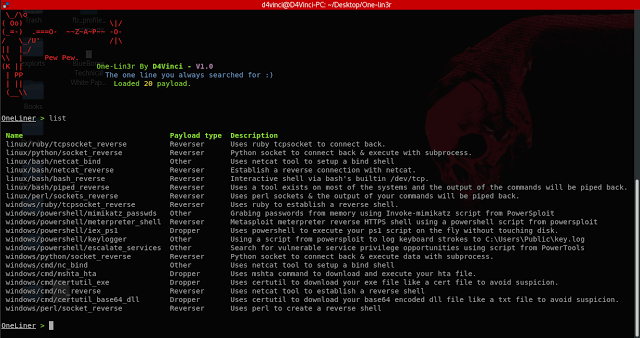
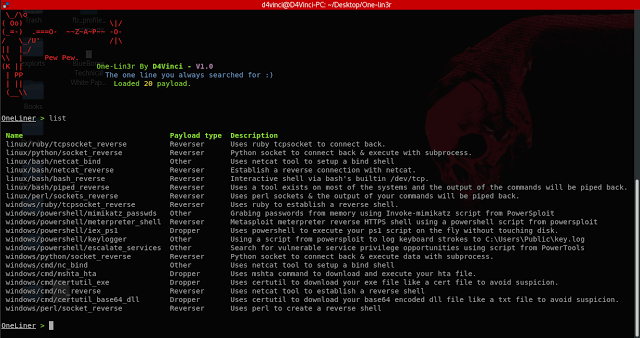 249Exploitation Tools
249Exploitation ToolsOne-Lin3r – Gives you One-Liners that Aids in Penetration Testing Operations
One-Lin3r is simple and light-weight framework inspired by the web-delivery module in Metasploit. It consists of various one-liners that aids in penetration...
-
 216Incidents
216IncidentsCanadian Police Charge Operator of Hacked Password Service Leakedsource.com
Canadian authorities have arrested and charged a 27-year-old Ontario man for allegedly selling billions of stolen passwords online through the now-defunct service Leakedsource.com....






