Search results for "Payload"
-
 309Data Security
309Data SecurityFake Google Chrome Android App Infecting Users with Malicious Payload
Google Chrome is the go-to browser for almost all the Android users. There is, however, one thing that you need to keep...
-

 196Vulnerabilities
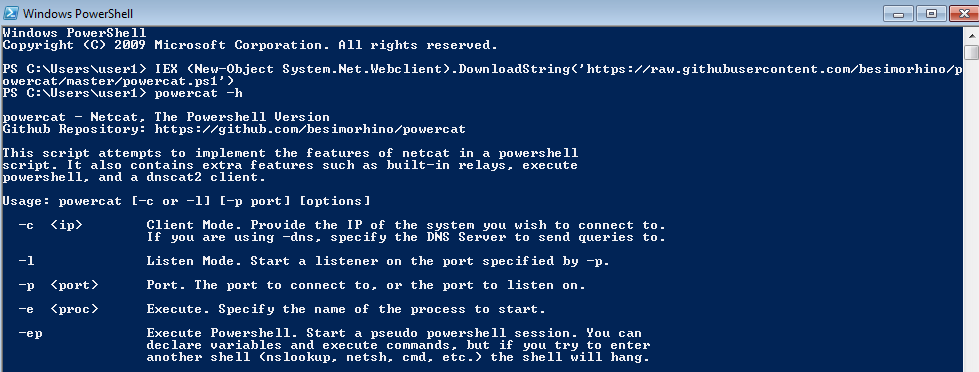
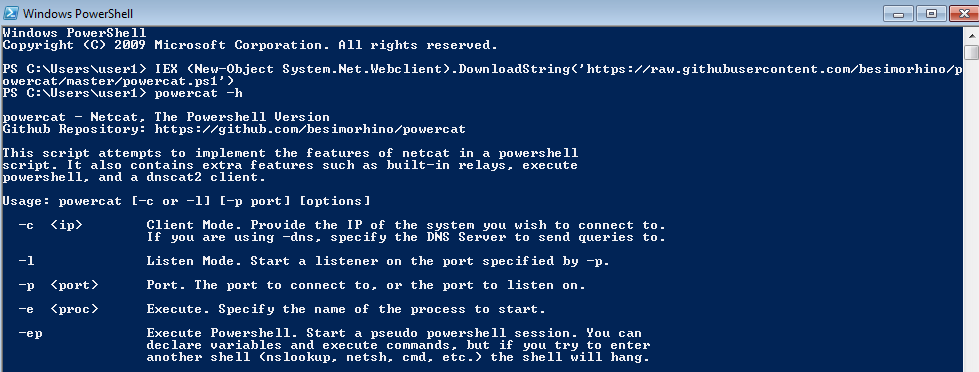
196VulnerabilitiesPowerShell Injection with Diskless Payload Persistence and Bypass Techniques
PowerShell continues to be the tool of choice for defenders, IT administrators, and hackers. The extensibility, support, and ability to have a...
-

 206Hackers Repository
206Hackers RepositoryGenerate-Macro – Powershell Script To Generate a Malicious Microsoft Office document with a Specified Payload and Persistence Method
Credits Matt Nelson (enigma0x3) – Coded by Matt Nelson (@enigma0x3) DOWNLOAD GENERATE-MACRO https://github.com/enigma0x3/Generate-Macro This Powershell script will generate a malicious Microsoft Office...
-
 306Hackers Repository
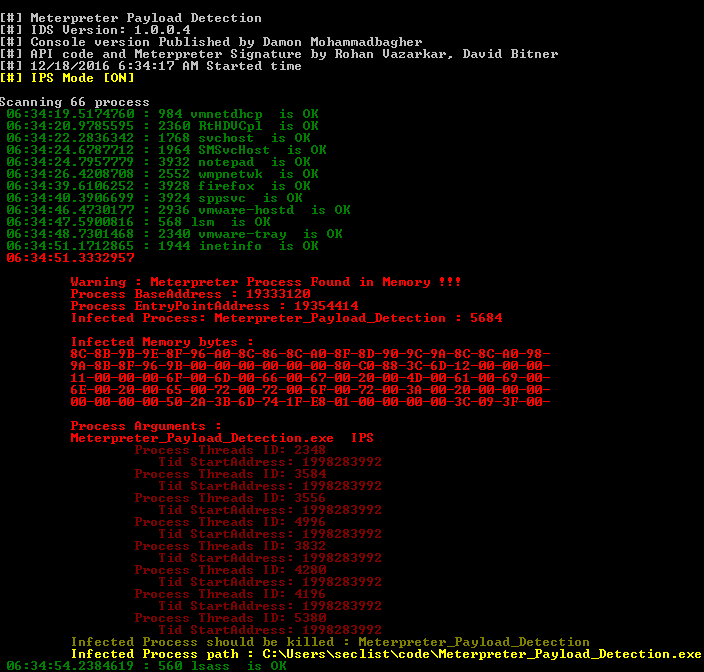
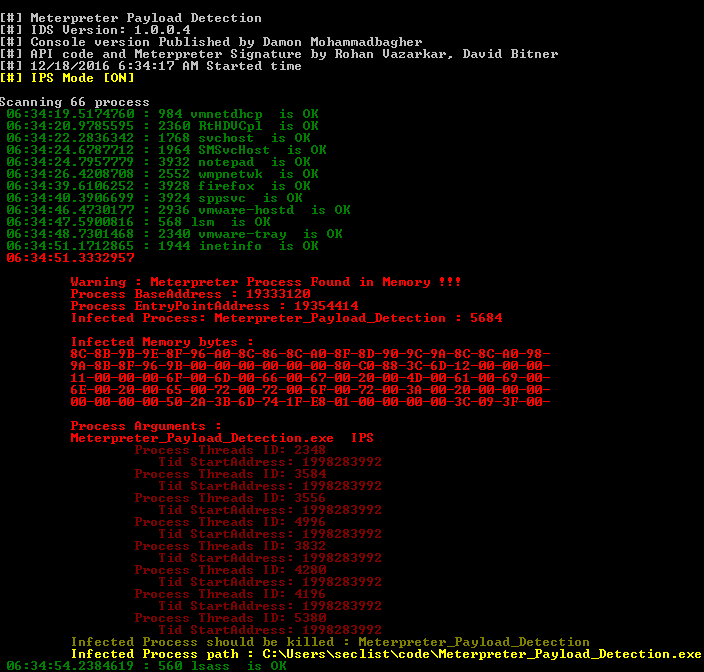
306Hackers RepositoryMeterpreter Payload Detection – Tool for detecting Meterpreter in memory like IPS-IDS and Forensics tool
Meterpreter_Payload_Detection.exe tool for detecting Meterpreter in memory like IPS-IDS and Forensics tool DOWNLOAD Meterpreter_Payload_Detection https://github.com/DamonMohammadbagher/Meterpreter_Payload_Detection CREDITS: DamonMohammadbagher Install Notes Download Meterpreter_Payload_Detection Compile...
-
Hackers Repository
Insanity-Framework a Tool To Generate Payloads and Control Remote Machines
Insanity-Framework to Generate Payloads and Control Remote Machines. Insanity-Framework ** VERSION 1.6 RELEASED !!! ** * Copyright 2017 Insanity Framework (IF) Written...
-
 177Vulnerabilities
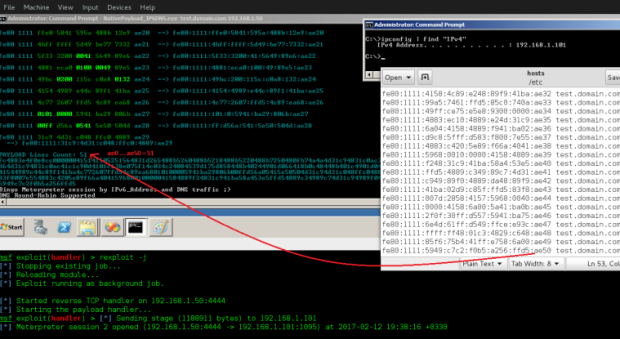
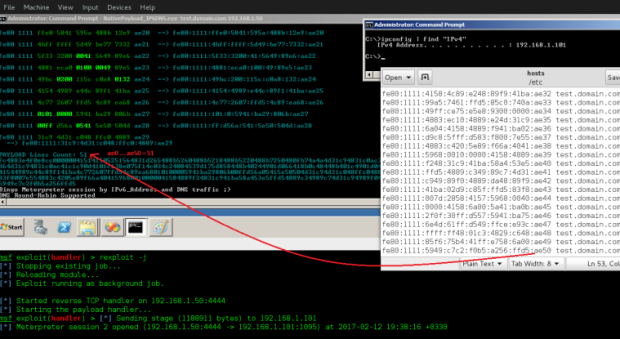
177VulnerabilitiesTransferring Backdoor Payloads by DNS AAAA records and IPv6 Address
Transferring Backdoor Payloads by DNS AAAA records and IPv6 Address. in this article i want to explain how can use IPv6 Address (AAAA)...
-
Hackers Repository
TheFatRat Tutorial – Generate Undetectable Payload FUD, Bypass Anti-Virus, Gain Remote Access
In this tutorial I will show you how to use TheFatRat to generate a Undetectable payload (FUD) to gain remote access to...
-
Hackers Repository
Embedding a Metasploit Payload to an original Android Apk.
Embed a Metasploit Payload in an original Android Apk. Welcome back in the last part of the Android Hacking Series we discussed...
-

 83Hack Tools
83Hack ToolsInsanity Framework – Generate Payloads and Control Remote Machines
With the dynamics of persuasion that prove effective in a pentest, several painstaking means of making a payload has emerged, Insanity Framework...
-
 228Backdoors
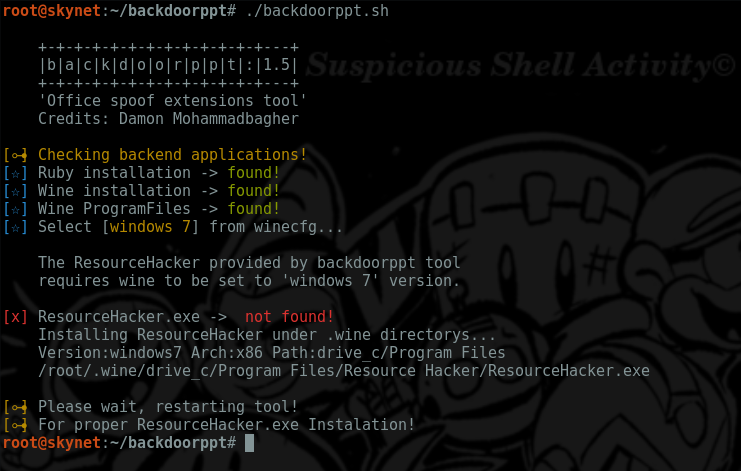
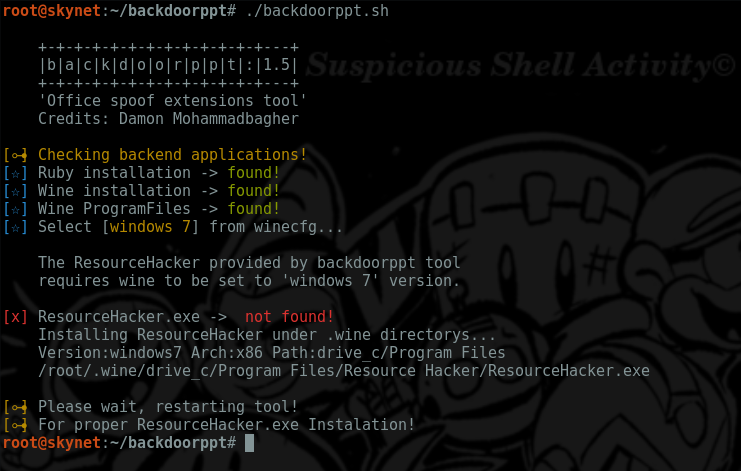
228Backdoorsbackdoorppt – Transform your payload.exe into one fake word doc
Simple script that allow users to add a ms-word icon to one existing executable.exe (using resource-hacker as backend appl) and a ruby...
-
 195Incidents
195IncidentsPentesting Windows environments: remote delivery of PowerShell payloads
PowerShell is an amazing post-exploitation tool available to the attacker during engagements in Windows environments. Tools like PowerSploit or PowerShell Empire help...
-
 192Hack Tools
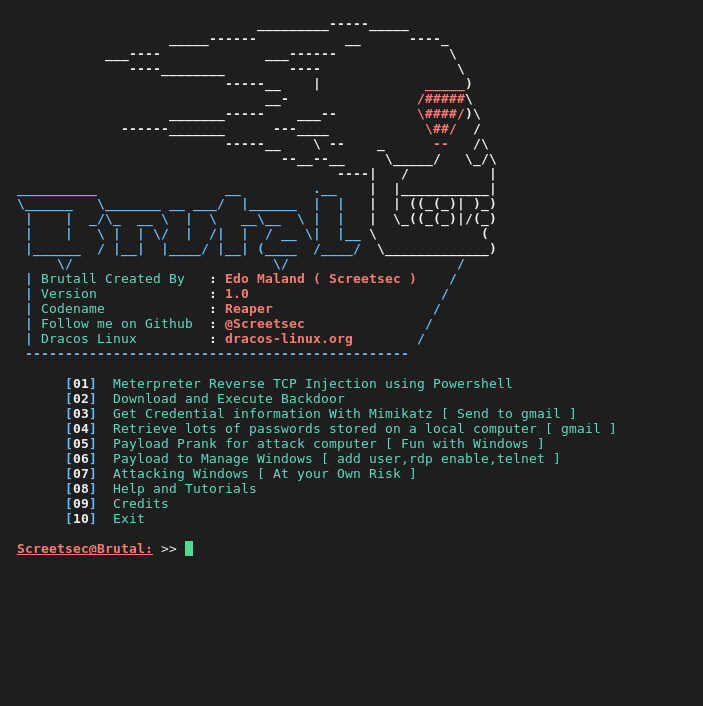
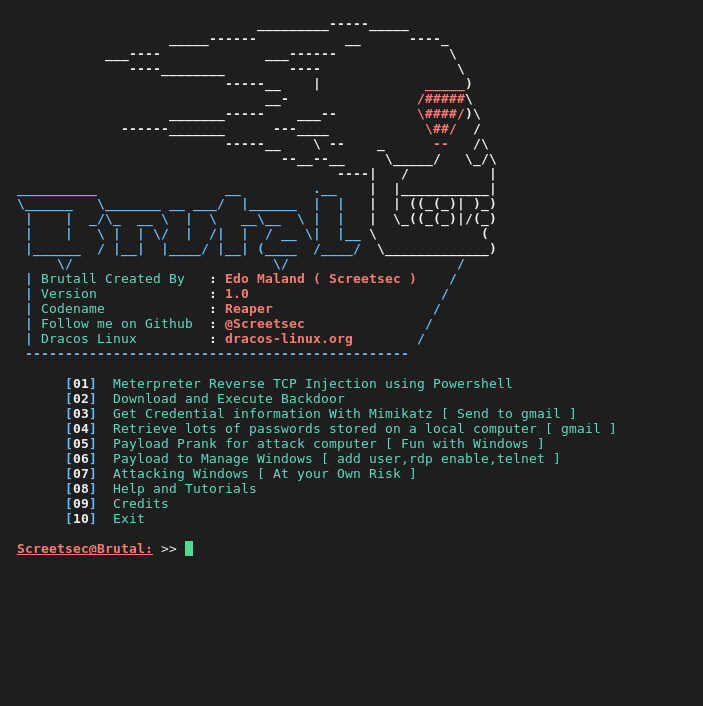
192Hack ToolsBrutal – Toolkit to quickly create various payloads,powershell and virus attacks
Brutal is extremely useful for executing scripts on a target machine without the need for human-to-keyboard interaction ( HID -ATTACK )...
-
 212Data Security
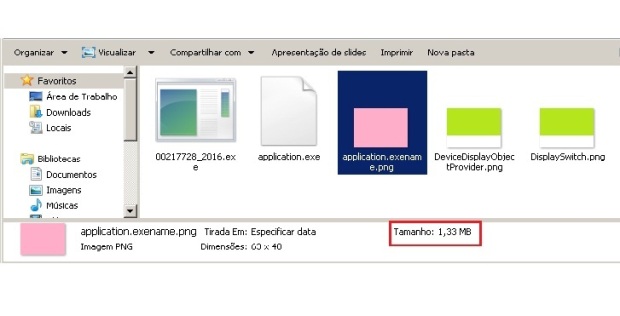
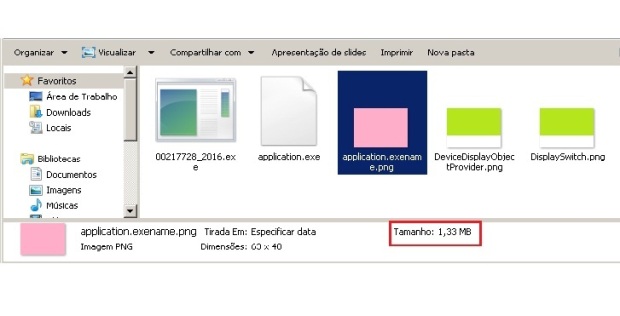
212Data SecurityPNG Embedded – Malicious payload hidden in a PNG file
One of the most complex tasks for the cybercriminals is to ensure their malicious code goes undetected by antivirus and achieves its...
-

 218Cyber Crime
218Cyber CrimeChinese Group ‘Admin338’ Use DropBox To Deliver Their Payload
FireEye Threat Intelligence analysts have discovered a new phishing attack carried by a Chinese group using legitimate service like dropbox. Analysts found...






