Search results for "Pentest"
-

 3.0KInfosec
3.0KInfosecPentestGPT – A ChatGPT Powered Automated Penetration Testing Tool
GBHackers come across a new ChatGPT-powered Penetration testing Tool called “PentestGPT” that helps penetration testers to automate their pentesting operations. PentestGPT has...
-

 2.0KTutorials
2.0KTutorialsHow to Use Advanced Network Intelligence Toolkit for Pentesting: badKarma
Searching vulnerabilities on the host (the host can be a website, web server, network device (router and others), end-user computer) begins with...
-

 2.8KTutorials
2.8KTutorialsTutorial for pentesting Android apps using the free ZANTI toolkit
In this tutorial, the specialists of the Cyber Security 360 course of the International Institute of Cyber Security (IICS) will show us...
-

 2.6KMalware
2.6KMalwareAPT Hackers Weaponizing The Red-Team Pentesting Tool To Evade AV & EDR Detection
During the routine malware sample analysis, researchers from Palo Alto’s UNIT 42 uncovered the new malware sample that contains a malicious payload...
-

 2.2KTutorials
2.2KTutorialsHow to perform Kubernetes pentesting and secure it?
Kubernetes is a great platform for container management that has shown a breakthrough lately, both in terms of functionality and in terms...
-

 1.7KTutorials
1.7KTutorialsFind Firewall & CDN used a website during Pentest with VXSCAN
Information gathering phase shows how an pentester should prepare for his next phases. Because in this phase pentester have to collect information...
-

 2.3KMalware
2.3KMalwareAPT Hacker Group FIN7 Uses A Pentesting Tool to Infect Windows Machines
In the recent era, cyber crimes are happening quite often, and this is not the first time that a cybercriminal group pretending...
-

 2.7KTutorials
2.7KTutorialsHow to pentest an Active Directory server?
Bloodhound is a great visual tool that shows the relationship between multiple Active Directory objects and allows you to quickly evaluate the...
-

 4.5KTutorials
4.5KTutorialsHow to do pentesting of VoIP servers? Step by step tutorial for hacking VoIP networks
The adoption of Voice over Internet Protocol (VoIP) technology is becoming broader, allowing organizations to communicate over huge distances and very easily....
-

 3.8KTutorials
3.8KTutorialsHOW TO PERFORM CYBER SECURITY AUDIT/PENTESTING OF CISCO DEVICES
Cisco is one of the most important companies in its field worldwide, offering sophisticated tools for telecommunications, system management, and network security....
-

 3.8KTutorials
3.8KTutorials50 CTF(CAPTURE THE FLAG) & PENTESTING WEBSITES TO PRACTICE YOUR HACKING & CYBERSECURITY SKILLS IN 2021
As with any other professional activity, in the world of ethical hacking practice makes perfect. Today there are thousands of ethical hackers...
-

 2.5KTutorials
2.5KTutorialsHow to do cyber security audit of IP camera network? Pentesting a CCTV system tutorial
The security of Internet-connected cameras remains a very little explored topic. According to IT security audit specialists from the International Institute of...
-

 3.3KExploitation Tools
3.3KExploitation ToolsHack-Tools v0.3.0 – The All-In-One Red Team Extension For Web Pentester
The all-in-one Red Team browser extension for Web Pentesters HackTools, is a web extension facilitating your web application penetration tests, it...
-

 4.3KData Breach
4.3KData BreachCybersecurity Firm FireEye Got Hacked; Red-Team Pentest Tools Stolen
FireEye, one of the largest cybersecurity firms in the world, said on Tuesday it became a victim of a state-sponsored attack by...
-

 1.1KHacking Tools
1.1KHacking Tools6 OSINT Tools That Make a Pentester’s Life Easier
So you have been tasked with performing a penetration test of the internet-facing systems of a customer. The security assessment is due...
-
 3.6KHack Tools
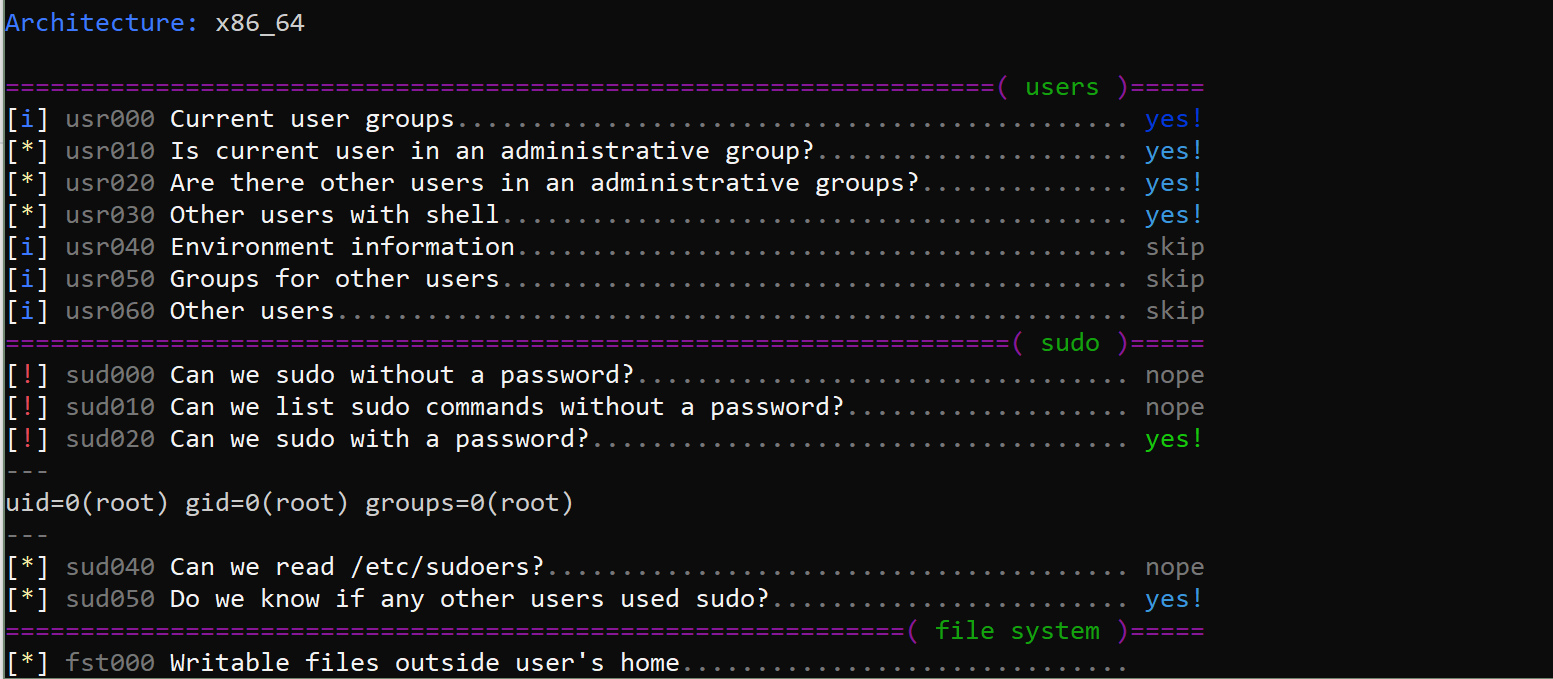
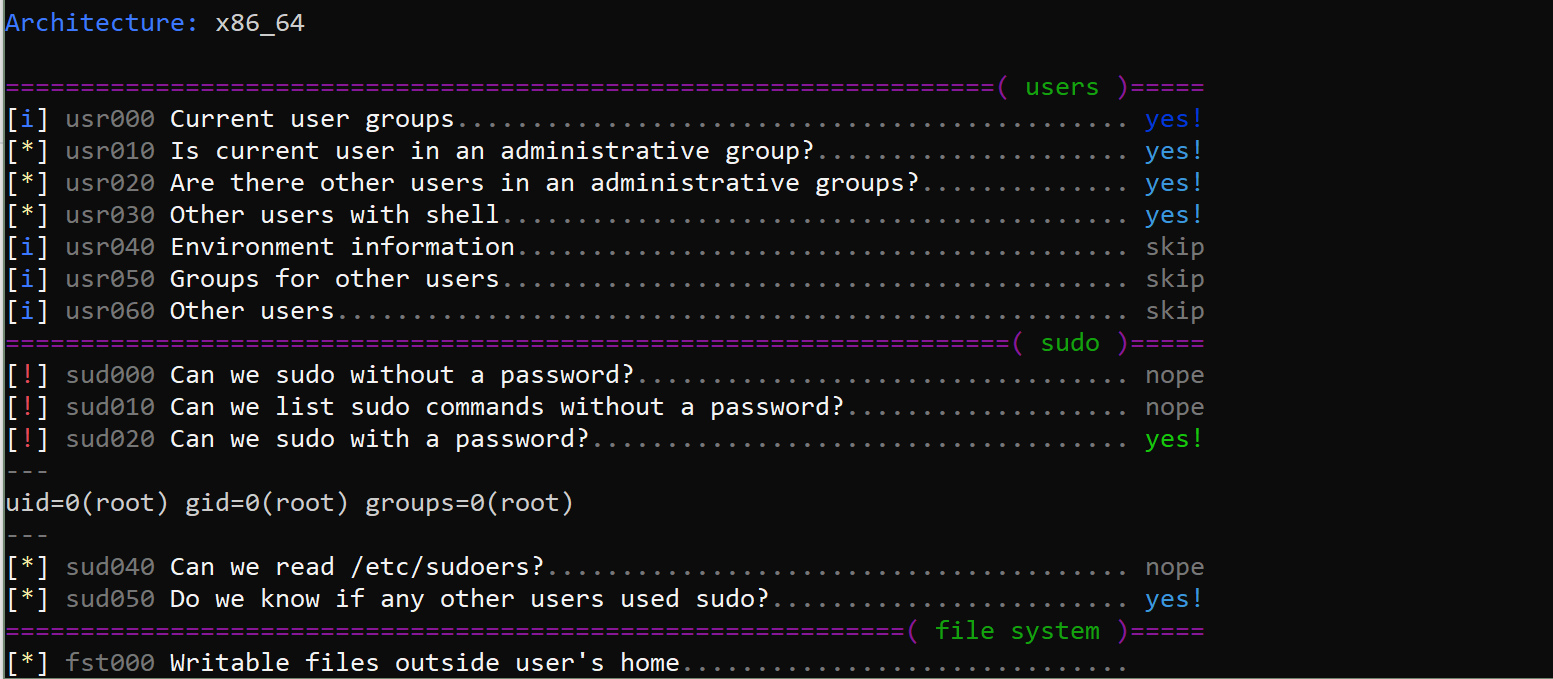
3.6KHack Toolslinux-smart-enumeration v1.9 releases: Linux enumeration tools for pentesting and CTFs
linux-smart-enumeration Linux enumeration tools for pentesting and CTFs This project was inspired by LinEnum and uses many of its tests. Unlike LinEnum, lse tries...
-
 3.9KHack Tools
3.9KHack ToolsEvil-Winrm v1.9 – The Ultimate WinRM Shell For Hacking/Pentesting
This shell is the ultimate WinRM shell for hacking/pentesting. WinRM (Windows Remote Management) is the Microsoft implementation of WS-Management Protocol. A standard...
-
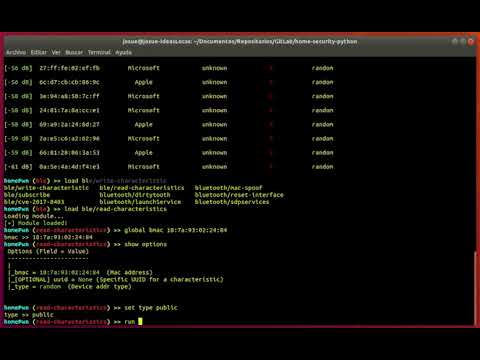
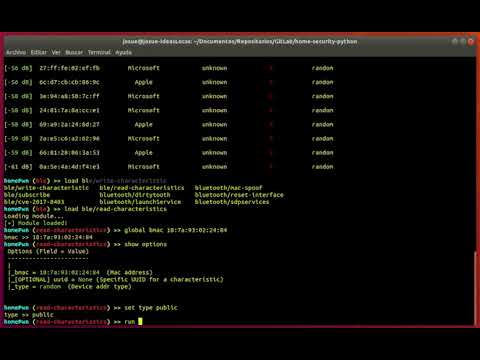 4.1KHack Tools
4.1KHack ToolsHomePwn – Swiss Army Knife for Pentesting of IoT Devices
HomePwn is a framework that provides features to audit and pentesting devices that company employees can use in their day-to-day work and...
-
 450Exploitation Tools
450Exploitation ToolsPenta – Open Source All-In-One CLI Tool To Automate Pentesting
Penta is is Pentest automation tool using Python3. (Future!) It provides advanced features such as metasploit and nexpose to extract vuln...
-
 502Exploitation Tools
502Exploitation ToolsLockdoor – Pentesting Framework With Cyber Security Resources
Lockdoor Framework : A Penetration Testing Framework With Cyber Security Resources. 09/2019 : 1.0Beta Information Gathring Tools (21) Web Hacking Tools(15)...
-
 417Exploitation
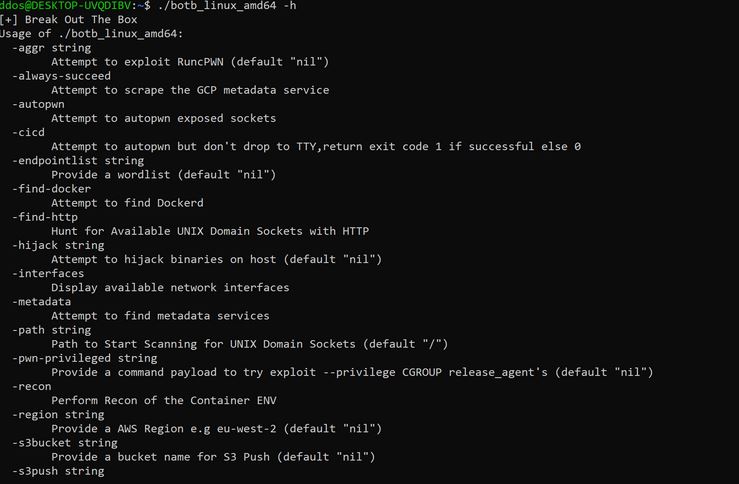
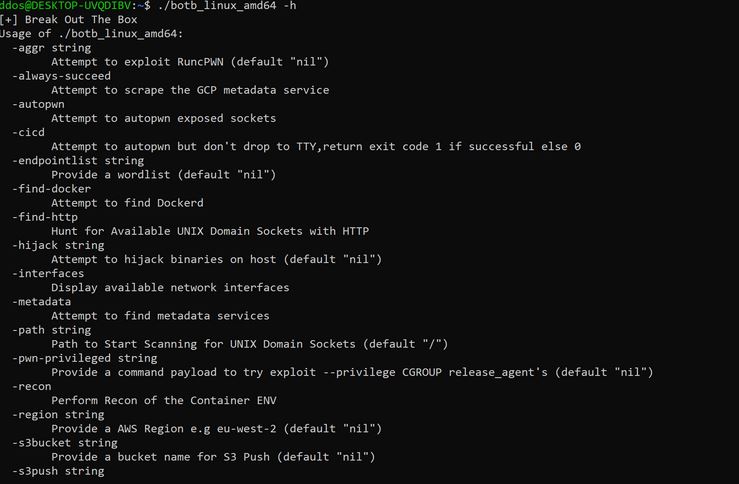
417ExploitationBotB – A container analysis and exploitation tool for pentesters and engineers.
BOtB (Break out the Box) is a container analysis and exploitation tool designed to be used by pentesters and engineers while also...






