Search results for "Phishing"
-

 247Geek
247GeekWhat Is Target Blank Anchor Tag Phishing Attack? How To Prevent It?
Short Bytes: When one hits a link (anchor tag) on a web page, and it opens in a new browser tab, there are...
-

 248Cyber Crime
248Cyber CrimePayPal users hit with “Payment Successfully Made Via Ali Express” Phishing Scam
PayPal is one of the most used platforms for sending and receiving payments by small medium and large enterprises. This makes it the...
-
 240Data Security
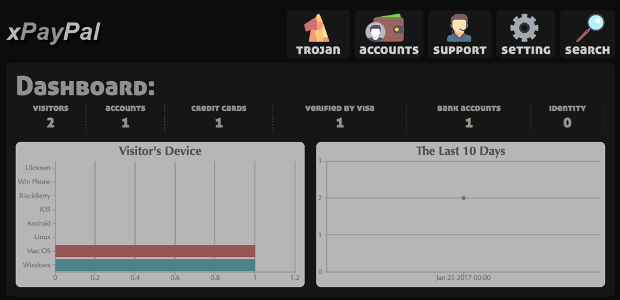
240Data SecurityHigh-End Phishing Kit Automates Attacks on PayPal Accounts
While many financial phishing schemes require development of bank- and region-specific phishing pages, PayPal’s international reach and widespread popularity mean that attackers...
-
 293Cyber Crime
293Cyber CrimeTwitter Users Hit with Blue Badge Verification Phishing Scam
Twitter account verification means your account will get a blue verified badge. Currently, anyone can apply for this verification, yet it depends...
-

 231Cyber Crime
231Cyber CrimePayPal Users Hit with Account Limited Phishing Scam
Recently, Gmail users were targeted with a phishing scam, and now it’s time for PayPal since it is undoubtedly one of the most...
-

 300Data Security
300Data SecurityTwitter Verify Account Phishing Scam Steals Credentials, Credit Card Data
Twitter is now the target of a phishing attack that uses methods to trick brand managers and social influencers into fake account...
-

 196How To
196How ToFiercePhish – Phishing Framework To Manage All Phishing Engagements
FiercePhish is a full-fledged phishing framework to manage all phishing engagements. It allows you to track separate phishing campaigns, schedule sending of...
-

 240Cyber Attack
240Cyber AttackLearn How to Identify And Avoid Phishing Scams
What is a Phishing Scam? Phishing is a form of social engineering approach utilized by hackers to collect sensitive records which include...
-

 309Geek
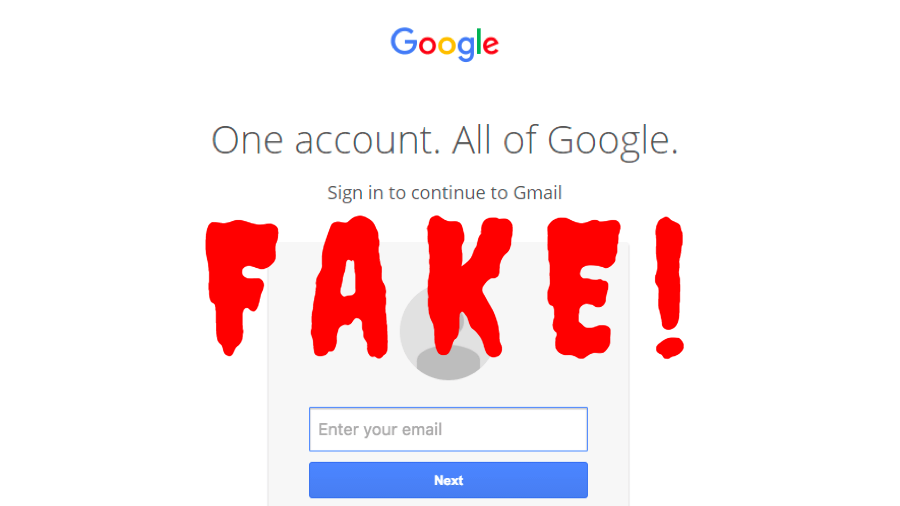
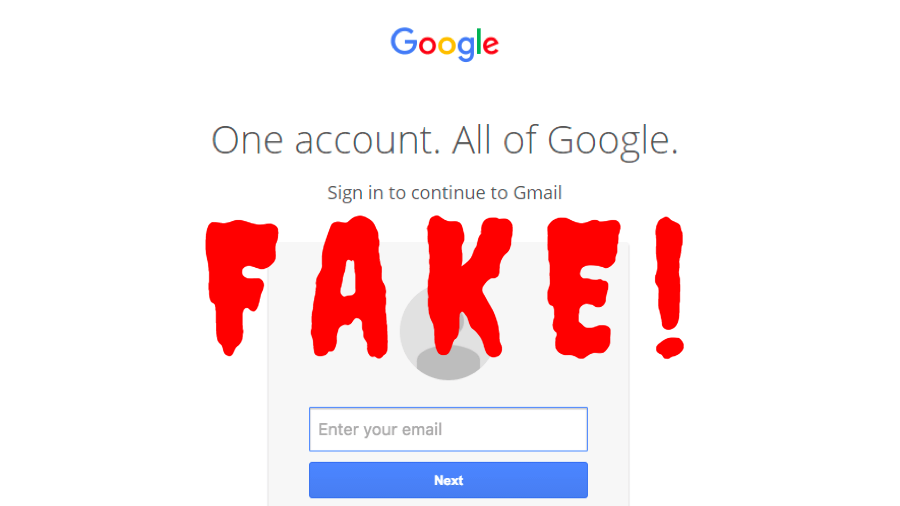
309GeekGmail Phishing Scam Stealing Credentials Through Infected Attachment
Malicious threat actors are using exclusively designed URLs to deceive users into providing their Gmail credentials. This latest phishing campaign, discovered by...
-

 269Phishing
269PhishingBeware : Highly Sophisticated Gmail Phishing Attack Targeting Many Gmail Users
A new highly effective phishing technique targeting Gmail and other services has been gaining popularity during the past year among attackers. Over the...
-
 258Hacked
258HackedBeware! This Is The Smartest Gmail Phishing Attack You’ll Ever Encounter
Short Bytes: Gmail phishing is one of most common methods used by hackers to compromise the online security of naive users. But,...
-
 155Vulnerabilities
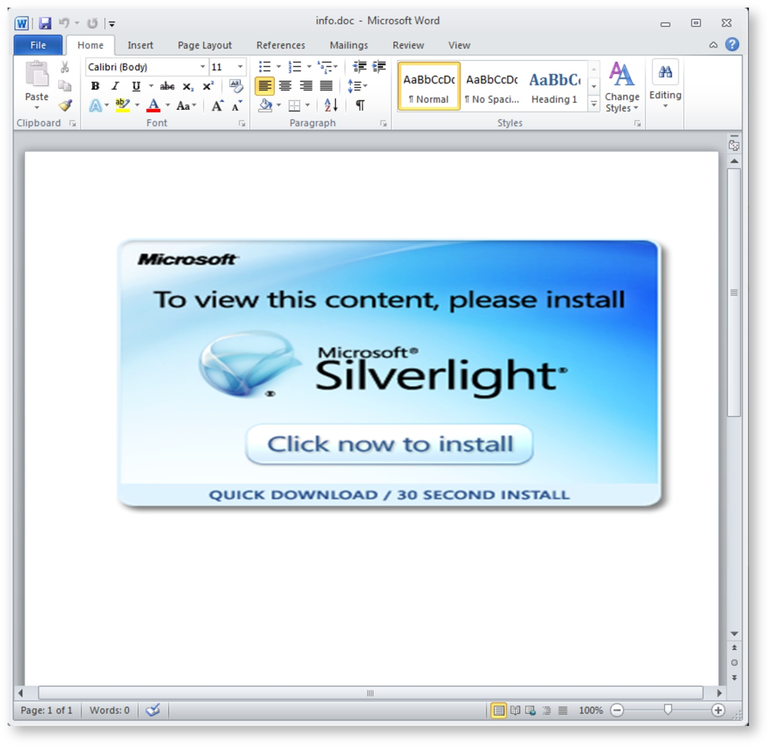
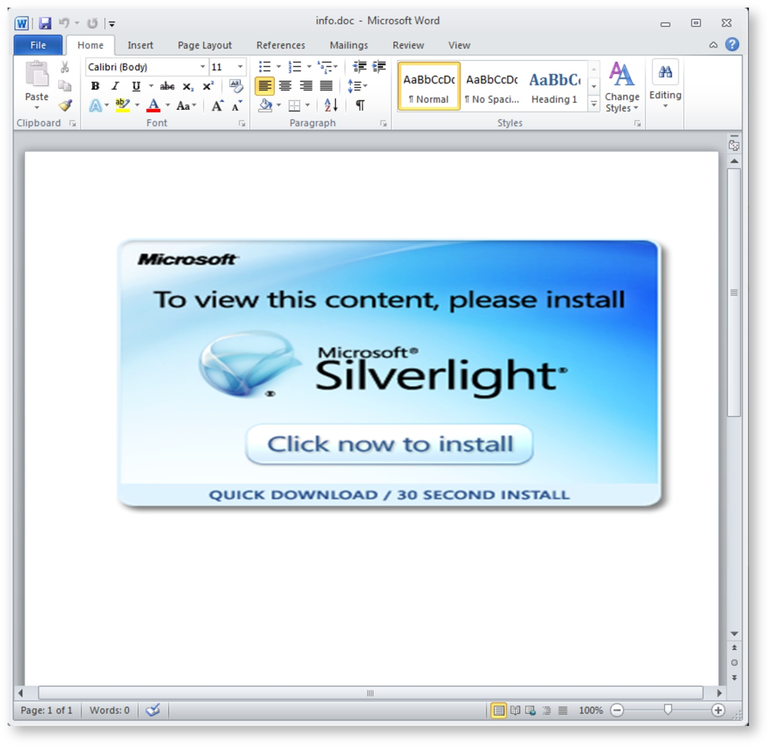
155VulnerabilitiesThis phishing email uses an unexpected trick to infect PCs with keylogger malware
Rather than using macros, this malware uses Visual Basic Script to avoid detection. Cybercriminals are targeting a US major financial services provider...
-
 120Vulnerabilities
120VulnerabilitiesInsidious phishing attack leverages on fake attachments to steal Gmail credentials
Cybercriminals are adopting specially crafted URLs to trick users into entering their Gmail credentials in a new sophisticated phishing campaign. Security experts...
-

 314Cyber Crime
314Cyber CrimeNetflix Users Targeted with yet another sophisticated Phishing Scam
If you have a Netflix account you might be at risk of falling prey to a new phishing scam that targets Netflix users through...
-
 300Phishing
300PhishingBrowser Autofill Profiles are Open for Phishing Attacks
Autofill profiles in browsers are open to phishing vector that permit attackers to gather data from users through the hidden fields, which...
-
 183Incidents
183IncidentsBrowser Autofill Profiles Can Be Abused for Phishing Attacks
Browser autofill profiles are a reliable phishing vector that allow attackers to collect information from users via hidden fields, which the browser...
-

 70Malware
70MalwarePhishing Actors Take a Cue From Malware-Distributing Brethren
Recently, Proofpoint researchers have observed a number of email campaigns with attached password-protected malicious documents. These documents are primarily used to distribute...
-

 122Incidents
122IncidentsAs Bitcoin Price Surges, Phishing Attacks on Cryptocurrency Wallets Intensify
Today’s Bitcoin to US Dollar exchange rate has reached $902, the first time Bitcoin price has gone above the $900 mark since...
-

 184Cyber Crime
184Cyber CrimePhishing attack on LA County computers; personal data of 756k people stolen
The Los Angeles County employees have become the victim of a phishing attack and as a result, the data of around 756,000...
-

 251How To
251How ToWiFiPhisher – Automated Phishing Attacks Against Wi-Fi Clients
Wifiphisher is a security tool that mounts automated victim-customized phishing attacks against WiFi clients in order to obtain credentials or infect the...
-

 217How To
217How ToPhishLulz – Ruby Toolset To Automate Phishing Activities
The VM comes with various open source tools that have been glued together. The two main components are: PhishingFrenzy (https://github.com/pentestgeek/phishing-frenzy) BeEF (https://github.com/beefproject/beef)...






