Search results for "Phone"
-
 869Data Security
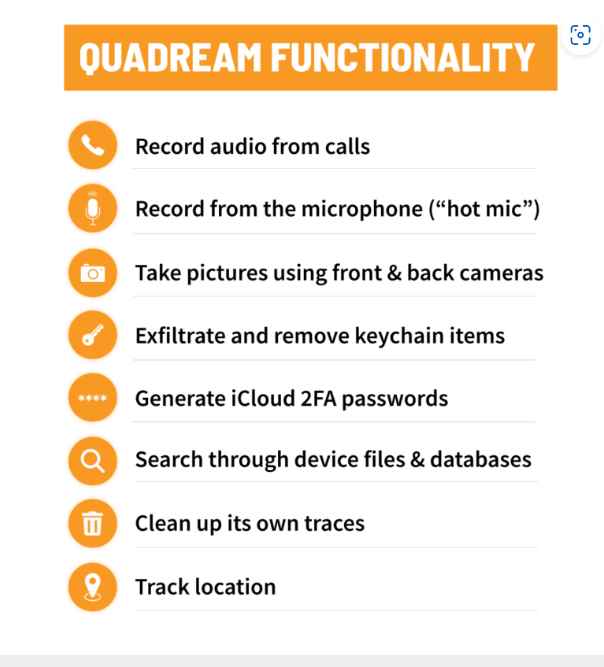
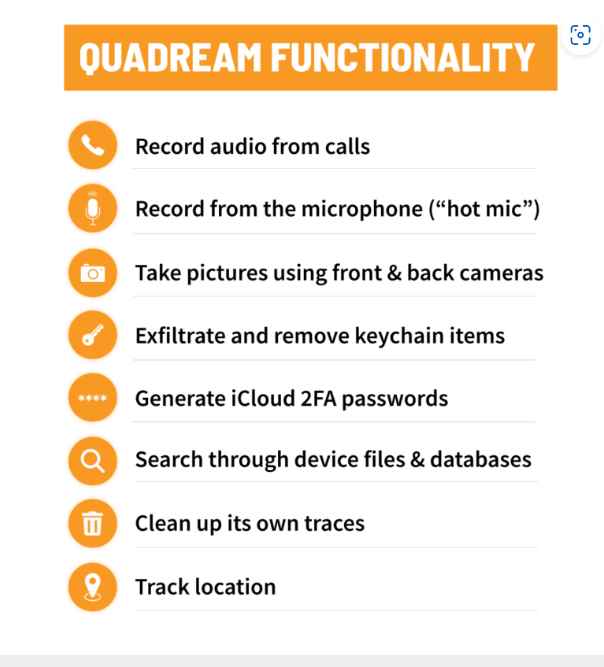
869Data SecurityNew spyware QuaDream is a replacement of Pegasus software used to hack iPhones remotely
Security researchers have uncovered fresh malware with hacking capabilities comparable to those of Pegasus, which was developed by NSO Group. The software,...
-

 4.7KVulnerabilities
4.7KVulnerabilitiesTwo Actively Exploited 0-Day vulnerabilities can be used to hack iPhones and iPads
Apple consumers have been dealt a blow in a world where digital security is of the utmost importance due to the recent...
-
 226Data Security
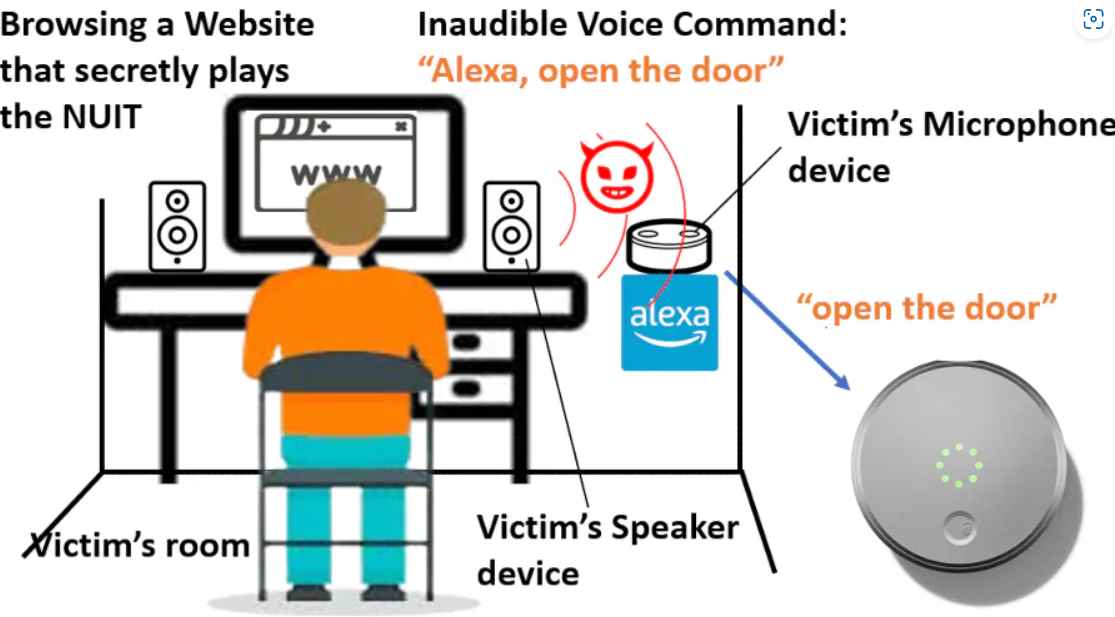
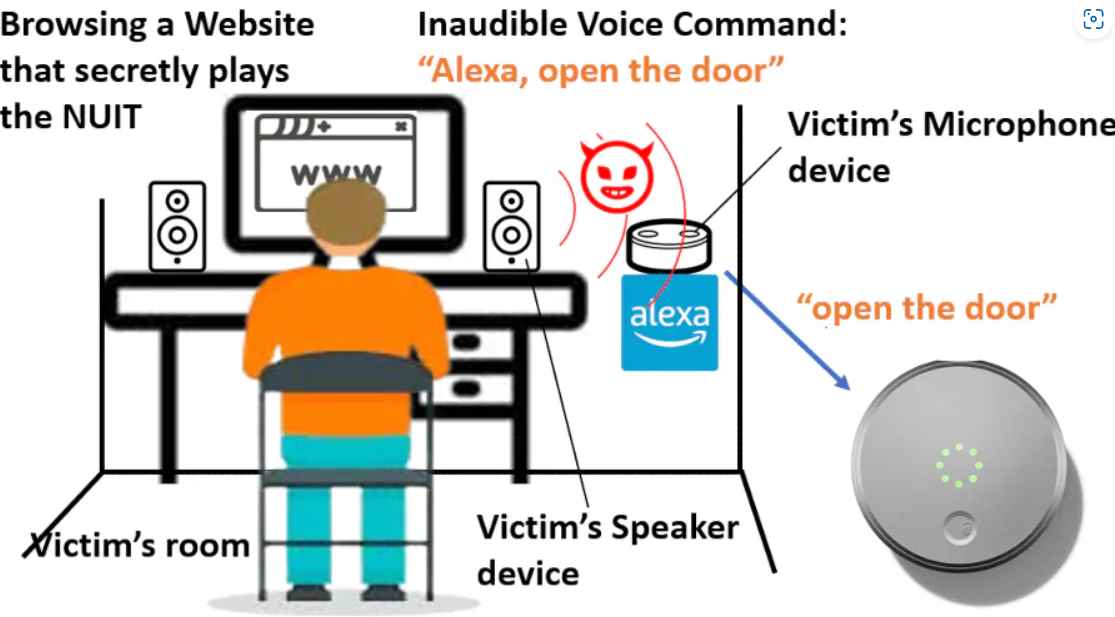
226Data SecurityHacking phones remotely without touching via new inaudible ultrasound attack
The Near-Ultrasound Invisible Trojan, or NUIT, was developed by a team of researchers from the University of Texas at San Antonio and...
-

 1.2KVulnerabilities
1.2KVulnerabilitiesCritical Flaw in Cisco IP Phone Series Exposes Users to Command Injection Attack
Cisco on Wednesday rolled out security updates to address a critical flaw impacting its IP Phone 6800, 7800, 7900, and 8800 Series...
-

 2.1KData Security
2.1KData Security“What happens on your iPhone, never stays on your iPhone”. New privacy lawsuit against Apple for monitoring iPhone users
A new complaint has been filed against Apple, accusing the corporation of monitoring iPhone users’ device data even when those users have...
-

 2.8KKids Online
2.8KKids OnlineHow to set up parental controls on your child’s new smartphone
Give yourself peace of mind and help create a safe online space for your child using Android or iOS parental controls
-

 5.0KKids Online
5.0KKids OnlineHelp! My kid has asked Santa for a smartphone
The time has come for your child to receive their first smartphone. Before handing it over, however, make sure to help them...
-

 3.8KVulnerabilities
3.8KVulnerabilitiesCisco IP Phones 7800 and 8800 series have a critical vulnerability could allow remote code execution or DoS attack
Customers were warned by Cisco on Thursday that fixes for a high-severity vulnerability that affects certain of the company’s IP phones are...
-
 985Data Security
985Data SecurityBad news! The platform certificates of many phone manufactures have been hacked. These are used to sign trusted apps on Android phones. Now these certificates are being used to certify malicious Android applications
Platform certificates, also known as platform keys, are used by OEM Android device makers to certify the core ROM images of their...
-

 899Data Security
899Data SecuritySeventy thousand individuals who police believe may have been victims of phone scams are receiving messages with instructions on what they should do next
Over 70,000 individuals are receiving text messages from the police informing them that they have been victims of online banking frauds and...
-

 3.5KData Security
3.5KData SecurityDon’t even think of taking your real smartphone to FIFA world cup matches in Qatar. Immigration officials will gain access to your phone data forever
It would be wise to get a burner phone if you were traveling to Qatar for the World Cup. Additionally, avoid taking...
-

 763Vulnerabilities
763VulnerabilitiesCritical vulnerability in intercom systems allow access to several government & apartments buildings using just a smartphone with NFC
The research team at cyber security company has identified a flaw that makes it possible to hack video entrance systems with an...
-

 3.0KVulnerabilities
3.0KVulnerabilitiesVULNERABILITY IN GALAXY STORE ALLOWS ATTACKERS TO EXECUTE MALWARE REMOTELY ON SAMSUNG PHONES WITHOUT USER INTERACTION
A flaw in the Galaxy Store enables remote adversaries to trigger the installation and/or start of an application, resulting in the execution...
-

 4.1KVulnerabilities
4.1KVulnerabilitiesSamsung Galaxy Store Flaw Allows Remote Attacker to Run Code on Affected Phones
A security flaw in the Galaxy Store allows attackers to trigger remote code execution on affected smartphones. The now patched vulnerability, which...
-

 2.4KMobile Security
2.4KMobile SecurityWhy your phone is slow – and how to speed it up
You probably don’t have to ditch your phone just yet – try these simple tips and tricks to make any Android device...
-
 2.1KVulnerabilities
2.1KVulnerabilities2 critical Remote code execution flaws in Qualcomm Chipsets affect billions of smartphones
Twelve new security flaws impacting various chipsets were disclosed in this month’s security advisory for Qualcomm’s devices, two of which have been...
-

 2.7KMobile Security
2.7KMobile SecurityCan your iPhone be hacked? What to know about iOS security
Here are some of the most common ways that an iPhone can be compromised with malware, how to tell it’s happened to...
-

 1.5KVulnerabilities
1.5KVulnerabilitiesCritical zero day vulnerability in iOS and macOS affecting iPhone, iPad, iPod and Macs. Update immediately
For a zero-day vulnerability in its macOS and iOS operating systems that has already been exploited, Apple released emergency updates on Monday....
-

 4.5KVulnerabilities
4.5KVulnerabilitiesApple Releases iOS Update for Older iPhones to Fix Actively Exploited Vulnerability
Apple on Wednesday backported security updates to older iPhones, iPads, and iPod touch devices to address a critical security flaw that has...
-

 3.7KData Breach
3.7KData BreachTwilio Hack -Over 1,900 Signal Users’ Phone Numbers were Exposed in the Data Breach
Signal, a cross-platform centralized encrypted instant messaging service declares that a data breach at Cloud Communication Company Twilio exposed almost 1,900 Signal...
-

 4.5KIncidents
4.5KIncidents4TB of confidential data, firmware code of Cellebrite TFS and Cellebrite Mobilogy leaked. UFED tool can be used to unlock any iPhone or Android
A threat actor has leaked 4TB of confidential data from Cellebrite an Israeli digital intelligence company. Cellebrite is an Israeli company specialized...






