Search results for "Research"
-

 2.6KMalware
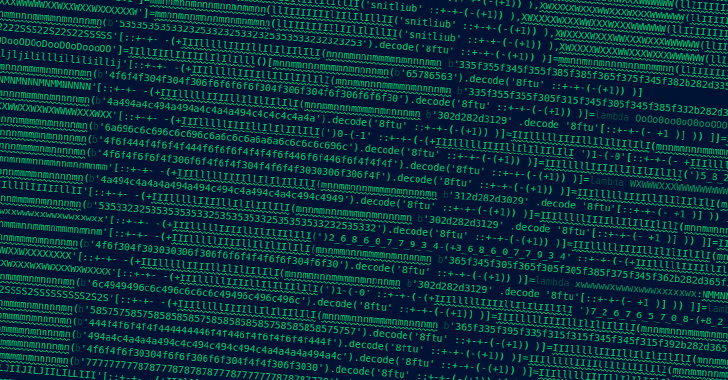
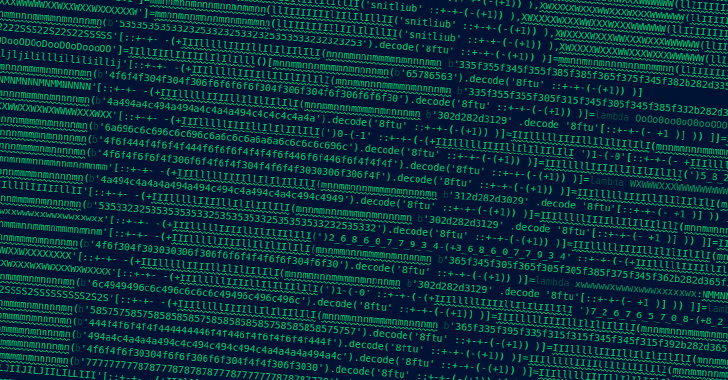
2.6KMalwareResearchers Uncover Obfuscated Malicious Code in PyPI Python Packages
Four different rogue packages in the Python Package Index (PyPI) have been found to carry out a number of malicious actions, including...
-

 1.9KVulnerabilities
1.9KVulnerabilitiesResearchers Uncover New Bugs in Popular ImageMagick Image Processing Utility
Cybersecurity researchers have disclosed details of two security flaws in the open source ImageMagick software that could potentially lead to a denial-of-service...
-

 2.2KMalware
2.2KMalwareResearchers Uncover Packer Used by Several Malware to Evade Detection for 6 Years
A shellcode-based packer dubbed TrickGate has been successfully operating without attracting notice for over six years, while enabling threat actors to deploy...
-
 2.9KMalware
2.9KMalwareResearchers Discover New PlugX Malware Variant Spreading via Removable USB Devices
Cybersecurity researchers have uncovered a PlugX sample that employs sneaky methods to infect attached removable USB media devices in order to propagate...
-
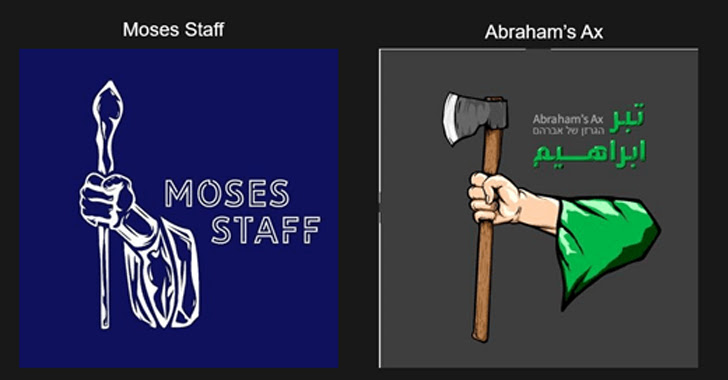
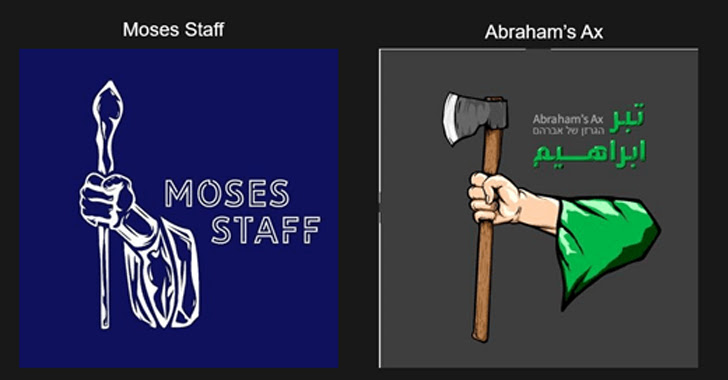 3.3KCyber Attack
3.3KCyber AttackResearchers Uncover Connection b/w Moses Staff and Emerging Abraham’s Ax Hacktivists Group
New research has linked the operations of a politically motivated hacktivist group known as Moses Staff to another nascent threat actor named...
-

 5.0KVulnerabilities
5.0KVulnerabilitiesSecurity Navigator Research: Some Vulnerabilities Date Back to the Last Millennium
Vulnerability analysis results in Orange Cyberdefenses’ Security Navigator show that some vulnerabilities first discovered in 1999 are still found in networks today....
-
 2.3KMalware
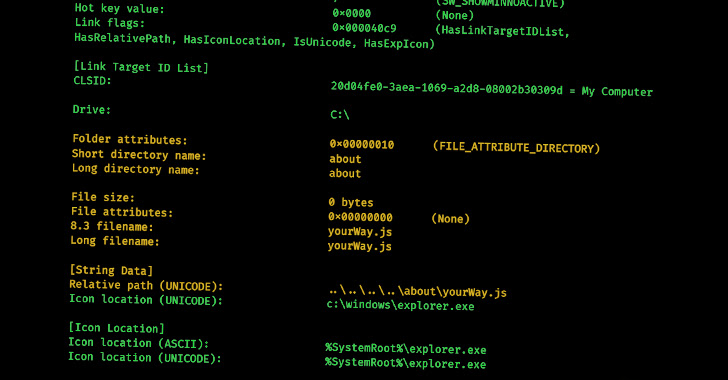
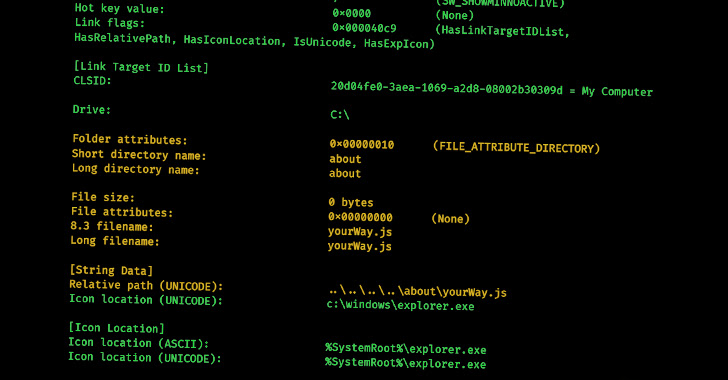
2.3KMalwareNew Research Delves into the World of Malicious LNK Files and Hackers Behind Them
Cybercriminals are increasingly leveraging malicious LNK files as an initial access method to download and execute payloads such as Bumblebee, IcedID, and...
-

 3.5KMalware
3.5KMalwareResearchers Uncover 3 PyPI Packages Spreading Malware to Developer Systems
A threat actor by the name Lolip0p has uploaded three rogue packages to the Python Package Index (PyPI) repository that are designed...
-
 2.9KInfosec
2.9KInfosecBest Malware Analysis Tools List For Security Researchers & Malware Analyst 2023
Malware analysis tools are highly essential for Security Professionals who always need to learn many tools, techniques, and concepts to analyze sophisticated...
-
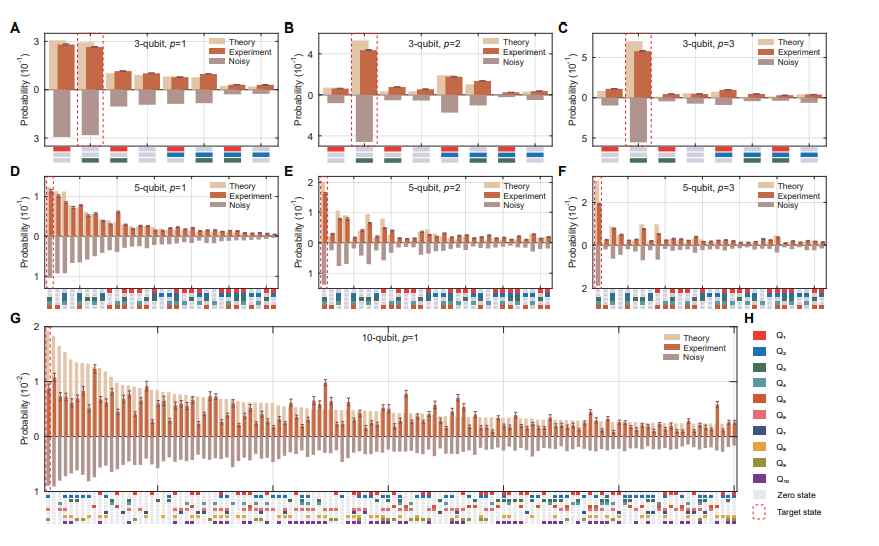
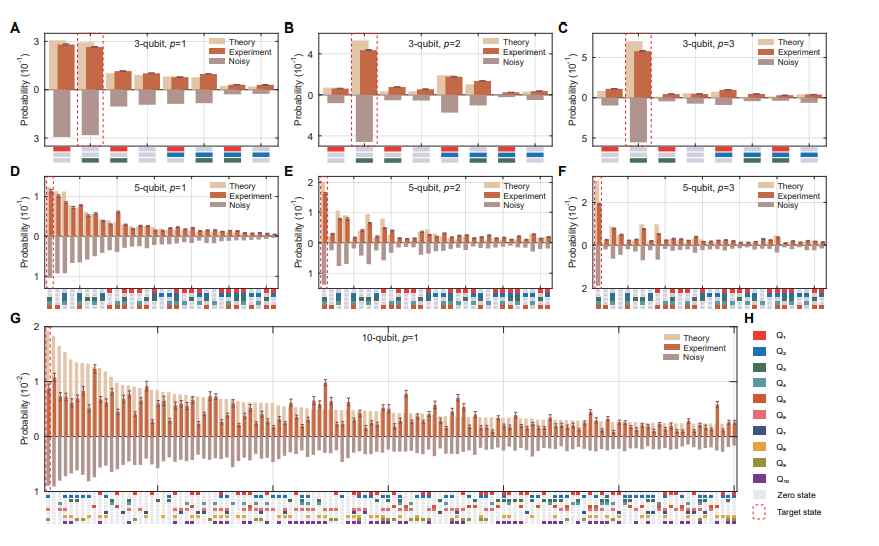 5.2KData Security
5.2KData SecurityResearchers break RSA algorithm with a Quantum Computer
A group of Chinese researchers have just released a paper in which they make the claim that they are capable of breaking...
-
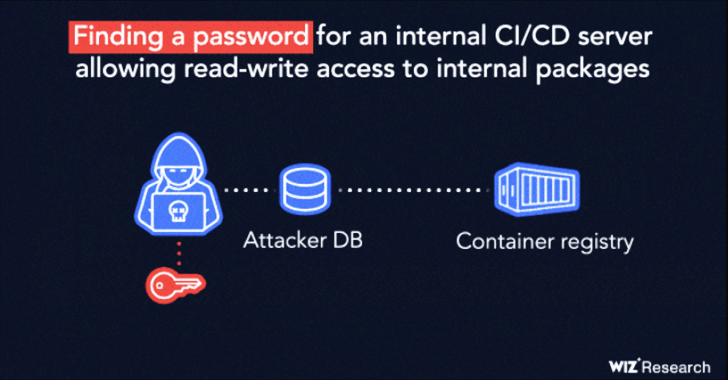
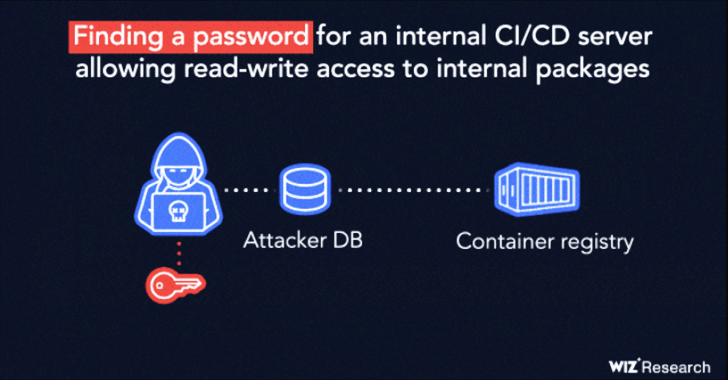 4.6KVulnerabilities
4.6KVulnerabilitiesResearchers Disclose Supply-Chain Flaw Affecting IBM Cloud Databases for PostgreSQL
IBM has fixed a high-severity security vulnerability affecting its Cloud Databases (ICD) for PostgreSQL product that could be potentially exploited to tamper...
-
 3.9KVulnerabilities
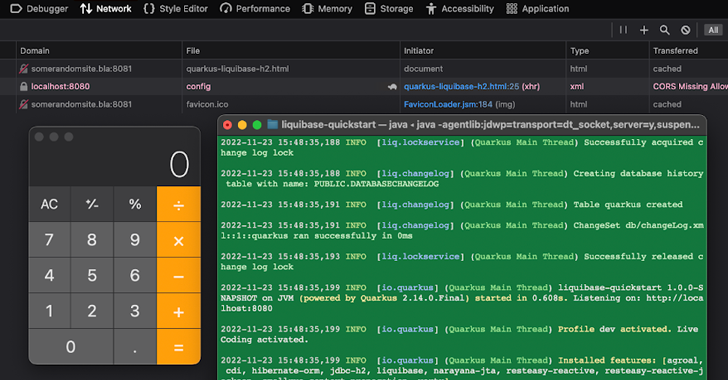
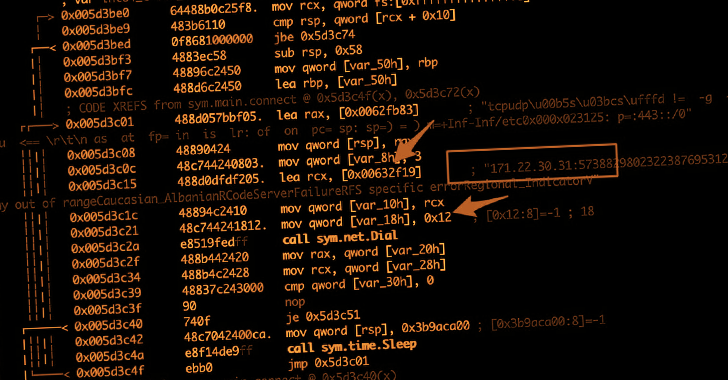
3.9KVulnerabilitiesResearchers Disclose Critical RCE Vulnerability Affecting Quarkus Java Framework
A critical security vulnerability has been disclosed in the Quarkus Java framework that could be potentially exploited to achieve remote code execution...
-
 1.2KMalware
1.2KMalwareResearchers ‘Accidentally’ Crash KmsdBot Cryptocurrency Mining Botnet Network
An ongoing analysis into an up-and-coming cryptocurrency mining botnet known as KmsdBot has led to it being accidentally taken down. KmsdBot, as...
-

 4.5KIncidents
4.5KIncidentsA hacker has posted data of 5.3 million Twitter accounts on a Raidforums, while another researcher confirmed another hack involving 100 million Twitter accounts
Earlier we published an article that provided details of a data breach that occurred on Twitter and affected 5.4 million accounts. Now, the...
-

 3.5KVulnerabilities
3.5KVulnerabilitiesResearchers Detail AppSync Cross-Tenant Vulnerability in Amazon Web Services
Amazon Web Services (AWS) has resolved a cross-tenant vulnerability in its platform that could be weaponized by an attacker to gain unauthorized...
-

 2.8KMalware
2.8KMalwareResearchers Warn of Cyber Criminals Using Go-based Aurora Stealer Malware
A nascent Go-based malware known as Aurora Stealer is being increasingly deployed as part of multiple campaigns designed to steal sensitive information...
-
 4.7KMalware
4.7KMalwareResearchers Uncover 29 Malicious PyPI Packages Targeted Developers with W4SP Stealer
Cybersecurity researchers have uncovered 29 packages in Python Package Index (PyPI), the official third-party software repository for the Python programming language, that...
-
 3.5KMalware
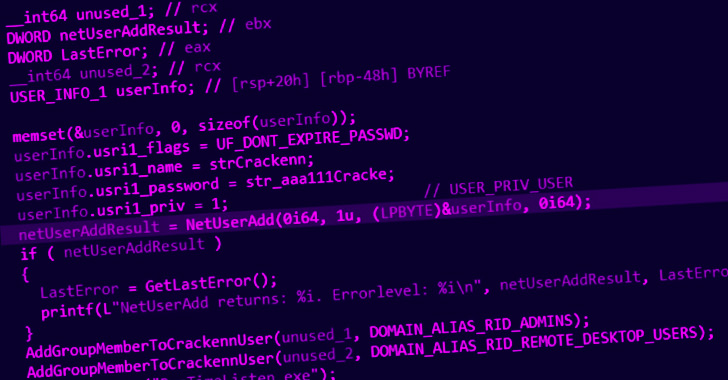
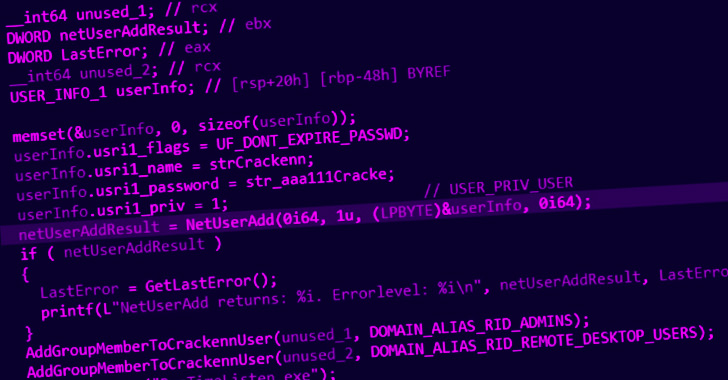
3.5KMalwareResearchers Find Links b/w Black Basta Ransomware and FIN7 Hackers
A new analysis of tools put to use by the Black Basta ransomware operation has identified ties between the threat actor and...
-
Vulnerabilities
Researchers Disclose Details of Critical ‘CosMiss’ RCE Flaw Affecting Azure Cosmos DB
Microsoft on Tuesday said it addressed an authentication bypass vulnerability in Jupyter Notebooks for Azure Cosmos DB that enabled full read and...
-
 4.6KMalware
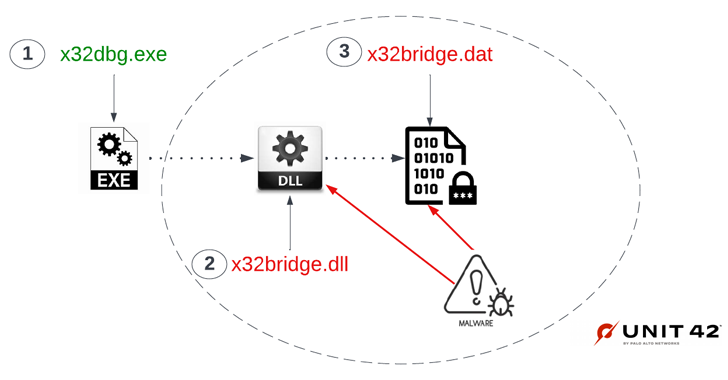
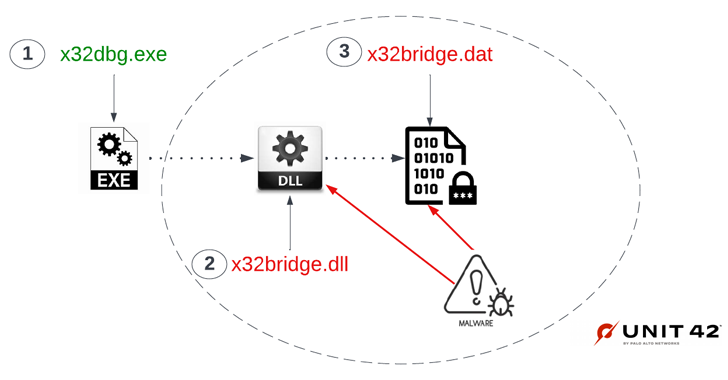
4.6KMalwareResearchers Uncover Stealthy Techniques Used by Cranefly Espionage Hackers
A recently discovered hacking group known for targeting employees dealing with corporate transactions has been linked to a new backdoor called Danfuan....
-
Malware
Researchers Expose Over 80 ShadowPad Malware C2 Servers
As many as 85 command-and-control (C2) servers have been discovered supported by the ShadowPad malware since September 2021, with infrastructure detected as...






