Search results for "Reverse"
-
 241Courses & Ebooks
241Courses & EbooksReversing: Secrets of Reverse Engineering
Beginning with a basic primer on reverse engineering-including computer internals, operating systems, and assembly language-and then discussing the various applications of reverse...
-

 351Android Hacking
351Android HackingBytecode Viewer – A Java 8 Jar & Android Apk Reverse Engineering Suite
Bytecode Viewer is an Advanced Lightweight Java Bytecode Viewer, GUI Java Decompiler, GUI Bytecode Editor, GUI Smali, GUI Baksmali, GUI APK Editor,...
-
 111Hack Tools
111Hack ToolsMalwasm – Tool For Malware Reverse Engineers
Malwasm is a Cuckoo Sandbox based open source tool that is designed to help malware reverse engineering tasks. How Malwasm Works: The...
-

 122Hackers Repository
122Hackers RepositoryBlack Rabbit – Python Cross-Compiled Reverse Shell for Windows
Black Rabbit – Python Cross-Compiled Reverse Shell for Windows Installation apt-get install wine git clone https://github.com/m4n3dw0lf/blackrabbit.git Usage #Edit the Master host informations:...
-

 292How To
292How ToInstalling Apktool for Reverse Engineering Android Apps
Apktool is used for reverse engineering 3rd party Android apps. Debugging is made easier with Apktool’s ability to decrypt properties to their...
-

 248How To
248How Toreversemap – Analyse SQL Injection Attempts In Web Server Logs
SQL CHAR encoding SQL CAST encoding Case encoding of SQL keywords Substring(Experimental – Disabled by default as it will fail with nested...
-
 183Hack Tools
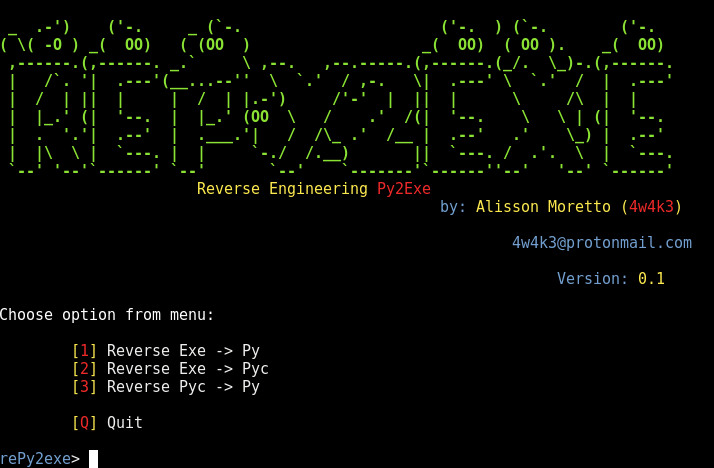
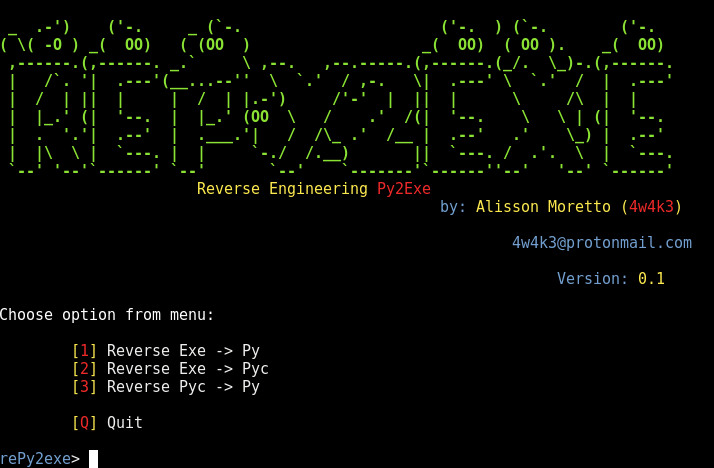
183Hack ToolsrePy2exe – A Reverse Engineering Tool for py2exe applications
Reverse Engineering Tool for py2exe applications. Prerequisites cmake git python2.7 Cloning git clone https://github.com/4w4k3/rePy2exe.git Running python rePy2exe.py or python2.7 rePy2exe.py Authors Alisson...
-

 173How To
173How TorePy2exe – Reverse Engineering Tool For py2exe Applications
rePy2exe, a Reverse Engineering Tool for py2exe applications. cmake git python 2.7 Enter the following command to download rePy2exe file git...
-

 210How To
210How ToLobotomy – Android Reverse Engineering Tool
Lobotomy is a command line based Android reverse engineering tool. Components: Permission Strings Attack Surface Surgical Interact UI De-compile De-buggable Dextra...
-

 232Android Hacking
232Android HackingHack any Mobile APP – Reverse engineering and Analysis Framework.
MARA is a Mobile Application Reverse engineering and Analysis Framework. It is a tool that puts together commonly used mobile application reverse...
-
 189Vulnerabilities
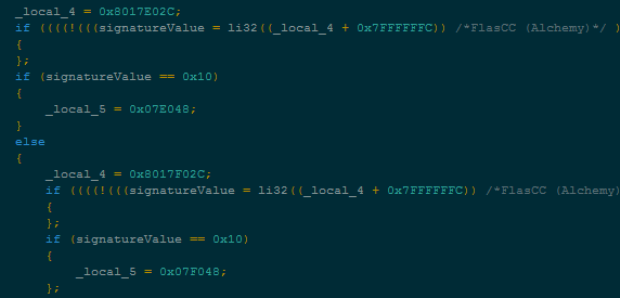
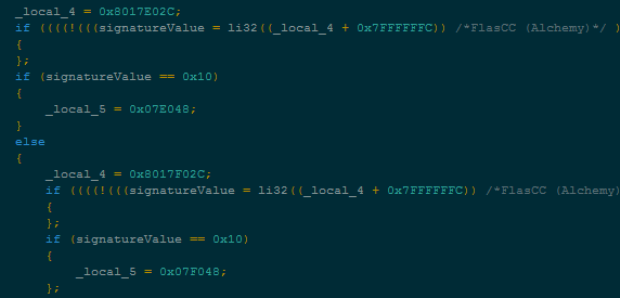
189VulnerabilitiesReverse-engineering DUBNIUM’s Flash-targeting exploit
The DUBNIUM campaign in December involved one exploit in-the-wild that affected Adobe Flash Player. In this blog, we’re going to examine the...
-
 165Data Security
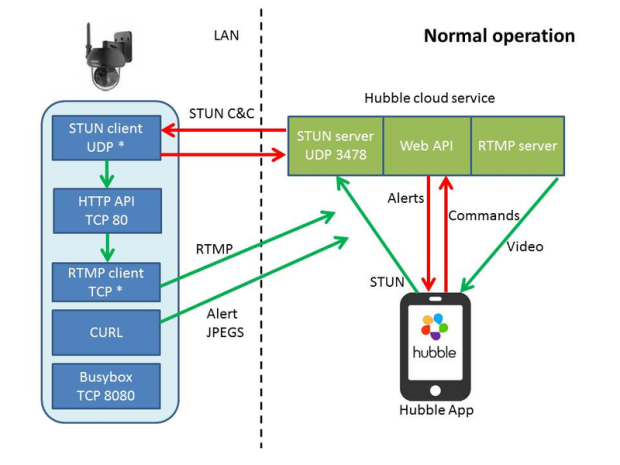
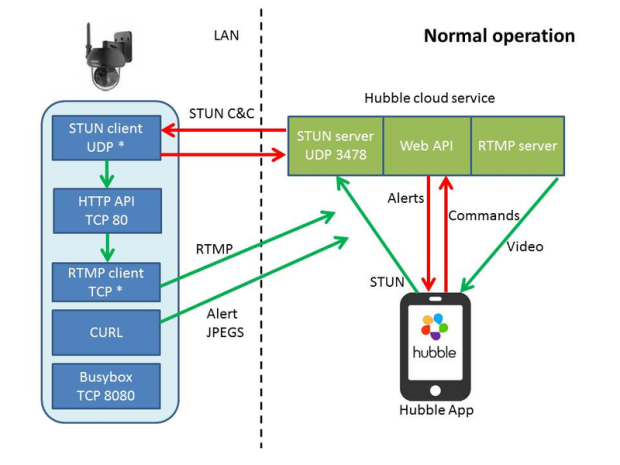
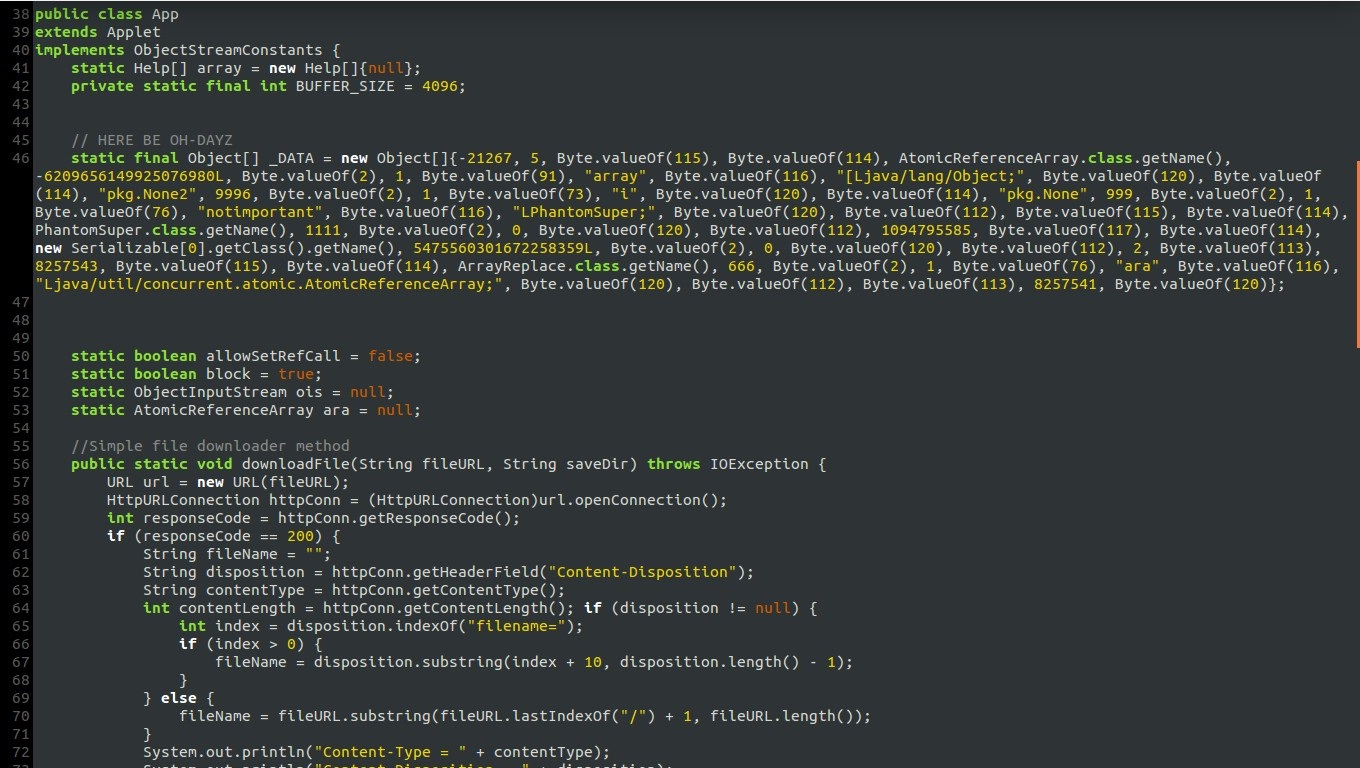
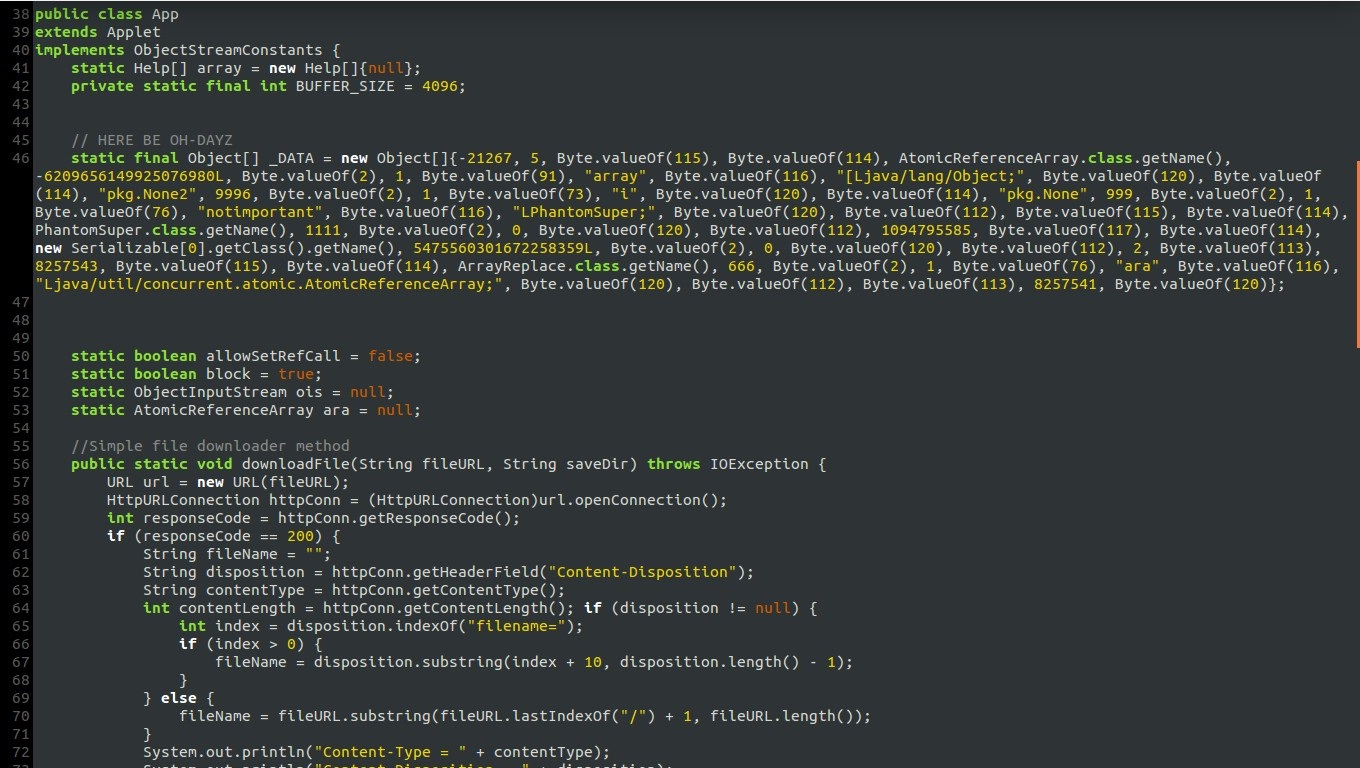
165Data SecurityPush To Hack: Reverse engineering an IP camera
For our most recent IoT adventure, we’ve examined an outdoor cloud security camera which like many devices of its generation a) has...
-
 191Data Security
191Data SecurityHow to do malware reverse engineering
Malicious Software can be Virus, Worm, Trojan Horse, Rootkit, Bot, DoS Tool,Exploit kit, Spyware. The objective of malware analysis is to gain...
-

 213Backdoors
213BackdoorsSideDoor – Debian/Ubuntu Backdoor Using A Reverse SSH Tunnel
Sidedoor maintains a reverse tunnel to provide a backdoor. sidedoor can be used to remotely control a device behind a NAT. Sidedoor...
-
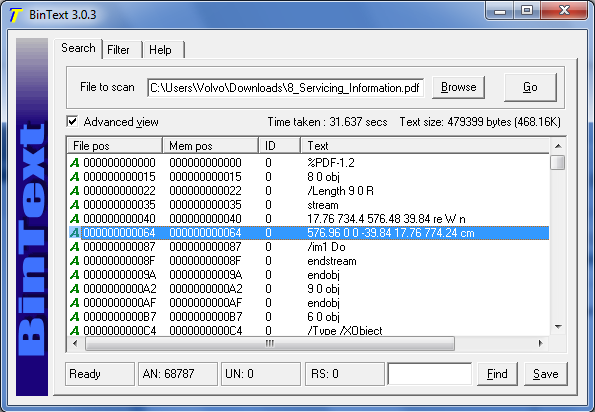
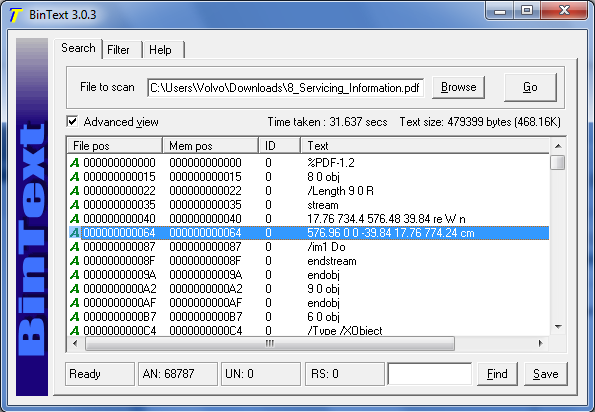 320Binary Analysis
320Binary AnalysisReverse Engineering Tool – BinText
A small, very fast and powerful text extractor.It can extract text from any kind of file and includes the ability to find...
-

 173Incidents
173IncidentsCriminals Steal $4 Million In Cash With Novel ‘Reverse ATM’ Attack
Over the last year, criminals in Russia found a way to steal 252 million Rubles ($3.8 million) from five unnamed banks, using a...
-

 136Data Security
136Data SecurityReverse-Engineering iOS Apps: Hacking on Lyft
If you’ve ever needed to know how another piece of code works, or have been at the mercy of someone else’s bugs,...
-
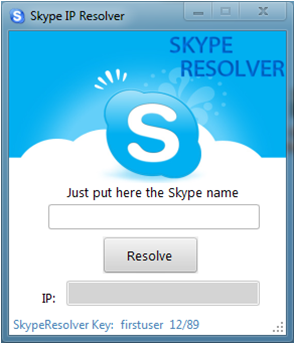
 154Information Gathering
154Information GatheringReverse Skype Resolver (How-to)
A Resolver will “lookup” a username on a VPS hosting the hacked skype, which allows the skype to pull data from the...
-

 81Cyber Crime
81Cyber CrimeReverse charges: How one man turned the tables on PC phone scammers
This week, UK IT worker and social engineering blogger Dale Pearson was targeted - with eight phone calls from a company claiming...
-
Cyber Crime
Carr’s Four Cyber Trends That Must Be Reversed Now
I’m not always in alignment with Jeffrey Carr’s point of view but in this he is spot on. Succinct and to the...






