Search results for "Router"
-

 204Cyber Attack
204Cyber AttackSatori IoT Botnet Is Exploiting Zero Day To Zombify Huawei Routers
Although the original creator of the infamous Mirai IoT botnet was arrested and sent to prison, botnet options are known because of...
-

 277Vulnerabilities
277VulnerabilitiesHUAWEI ROUTER VULNERABILITY USED TO SPREAD MIRAI VARIANT
Researchers have identified a vulnerability in a Huawei home router model that is being exploited by an adversary to spread a variant...
-
 285Exploitation
285ExploitationRouterSploit – Router Exploitation Framework
The RouterSploit Framework is an open-source exploitation framework dedicated to embedded devices. Requirements gnureadline requests paramiko beautifulsoup4 Installation sudo apt-get install python-requests...
-

 193Hack Tools
193Hack ToolsMITM Router – Man in the middle Router
Turns any linux computer into a public Wi-Fi network that silently mitms all http traffic. Runs inside a Docker container using hostapd, dnsmasq, and mitmproxy to...
-

 226Vulnerabilities
226VulnerabilitiesMotherboard Hacking Livestream: How to Turn a Router Into Part of a Botnet
Join us on YouTube or Facebook to learn how hacking works. Rick Ramgattie is a Security Analyst at Independent Security Evaluators, who will...
-

 3.4KHow To
3.4KHow ToHow to secure your router to prevent IoT threats?
The router is the first device that you must consider, since it not only controls the perimeter of your network, but all...
-

 198Vulnerabilities
198VulnerabilitiesSecond Researcher Drops Router Exploit Code After D-Link Mishandles Bug Reports
Embedi, a hardware security firm, has published details about two vulnerabilities that have yet to be patched in the firmware of D-Link...
-

 398Vulnerabilities
398VulnerabilitiesRouteX Malware Uses Netgear Routers for Credential Stuffing Attacks
A Russian-speaking hacker has been infecting Netgear routers over the past months with a new strain of malware named RouteX that he...
-

 206Bruteforcing
206BruteforcingRouter Password Kracker – Tool For Cracking Router/Modem/Website Passwords
Router Password Kracker is a free program that allows you to crack your router password. You can also use this tool to...
-
 84Cyber Crime
84Cyber CrimeSpiderman pleads guilty to knocking 900,000 German broadband routers offline
It seems that Spiderman is in a spot of trouble, tangled in a web of his own making.
-

 133Incidents
133IncidentsBriton admits to router hack that DDoSed Deutsche Telekom
An as yet unnamed 29-year-old pleaded guilty on Friday to charges relating to the hijacking of more than 1.25 million Deutsche Telekom...
-

 92Malware
92MalwareHacker “BestBuy” Admits to Hijacking Deutsche Telekom Routers With Mirai Malware
A 29-year-old man pleaded guilty in court on Friday to hijacking over 900,000 routers from the network of Deutsche Telekom, according to...
-

 114Cyber Crime
114Cyber CrimeHacker Bestbuy Admits He Hijacked Deutsche Telekom Routers
The 29-year old hacker, who is referred to as Hacker Bestbuy, has reportedly admitted to hijacking over 9 lac routers from the...
-
 334Hackers Repository
334Hackers RepositoryHow to use Hacking Tools Without Opening Ports on Router NAT Firewall
Hello, welcome back in a recent tutorial (How to Use Metasploit, SEToolkit Without Opening Ports Kali Linux) we worked with Ngrok creating...
-
 184Vulnerabilities
184VulnerabilitiesAdvanced CIA firmware has been infecting Wi-Fi routers for years
Latest Vault7 release exposes network-spying operation CIA kept secret since 2007. Home routers from 10 manufacturers, including Linksys, DLink, and Belkin, can...
-
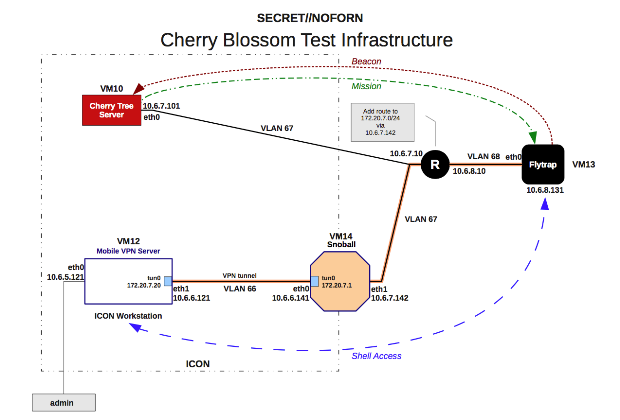
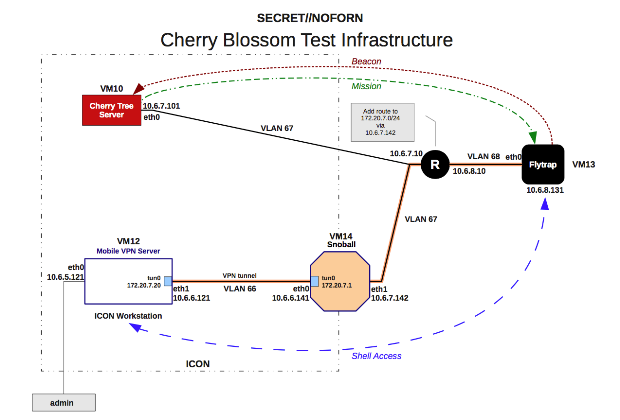
 248Hacked
248HackedCIA’s “CherryBlossom” Can Hack Almost Every Popular Router Brand You Can Think #Vault7
Short Bytes: A new set of CIA documents exposed by Wikileaks describe a firmware called CherryBlossom which can be installed on network...
-

 294Data Security
294Data SecurityHackers can steal large amount of data using router’s LEDs
Researchers from the University of Negvu have developed a way in which hackers can extract data from a victim’s computer using the...
-

 125Hackers Repository
125Hackers RepositoryAround 25 Percent TalkTalk Customers Could Still Be Left With Vulnerable Routers
Up to 25 Percent of TalkTalk UK Customers Could Still Left With Vulnerable Routers Around 25 Percent TalkTalk UK Customers Could Still...
-

 285News
285NewsNetgear Router Firmware Now Collects Analytics Data
Do you have got NightHawk R7000 Netgear router? Netgear router firmware launched a new firmware update last week for the wi-fi...
-

 187Vulnerabilities
187VulnerabilitiesNew firmware for Netgear routers includes a data collection feature
A new firmware released for NightHawk R7000 Netgear routers includes a remote data collection feature, here’s how to turn off it. In...
-
 210Vulnerabilities
210VulnerabilitiesCisco fixes a critical flaw in CISCO CVR100W Wireless-N VPN Small Business Routers
Cisco released a firmware update to fix a critical buffer overflow vulnerability in CISCO CVR100W Wireless-N VPN Small Business Routers. Cisco has...






