Search results for "Scan"
-

 261News
261NewsSamsung Galaxy S8 Iris Scanner Hacked
Chaos PC club hackers were able to defeat the Samsung Galaxy S8 Iris scanner gadget with an image. The Samsung Galaxy S8...
-

 216Vulnerabilities
216VulnerabilitiesSamsung Galaxy S8 Iris Scanner Fooled by a Photo
A photo of a person’s eye taken at a medium distance is more than enough to trick a Samsung Galaxy S8 smartphone,...
-

 111Hack Tools
111Hack Toolsscanless – Public Port Scan Scrapper
Command-line utility for websites that can perform port scans on your behalf. Useful for early stages of a penetration test or if...
-
 214News
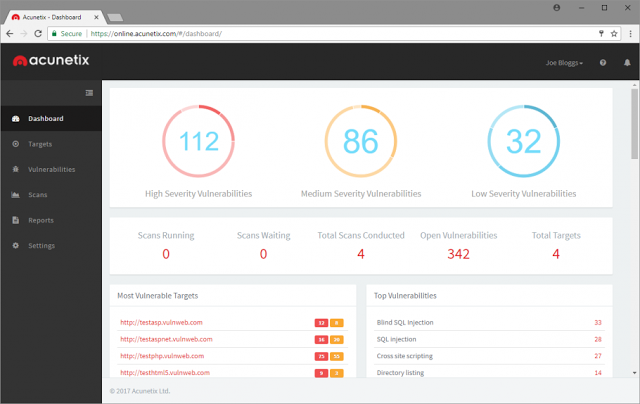
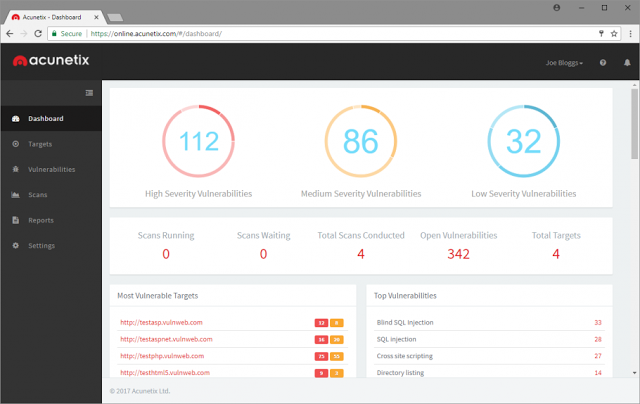
214NewsMajor Update of Acunetix Online Vulnerability Scanner
Acunetix Online has undergone a mammoth update, now enjoying all the features and benefits found in Acunetix On Premise, including: Integrated vulnerability...
-

 222Geek
222GeekMillions of Android Devices Vulnerable to Network Scan Attack
Researchers have recently discovered hundreds of vulnerable apps on Google Play Store which are allowing hackers to inject them with malicious code...
-
 409Hackers Repository
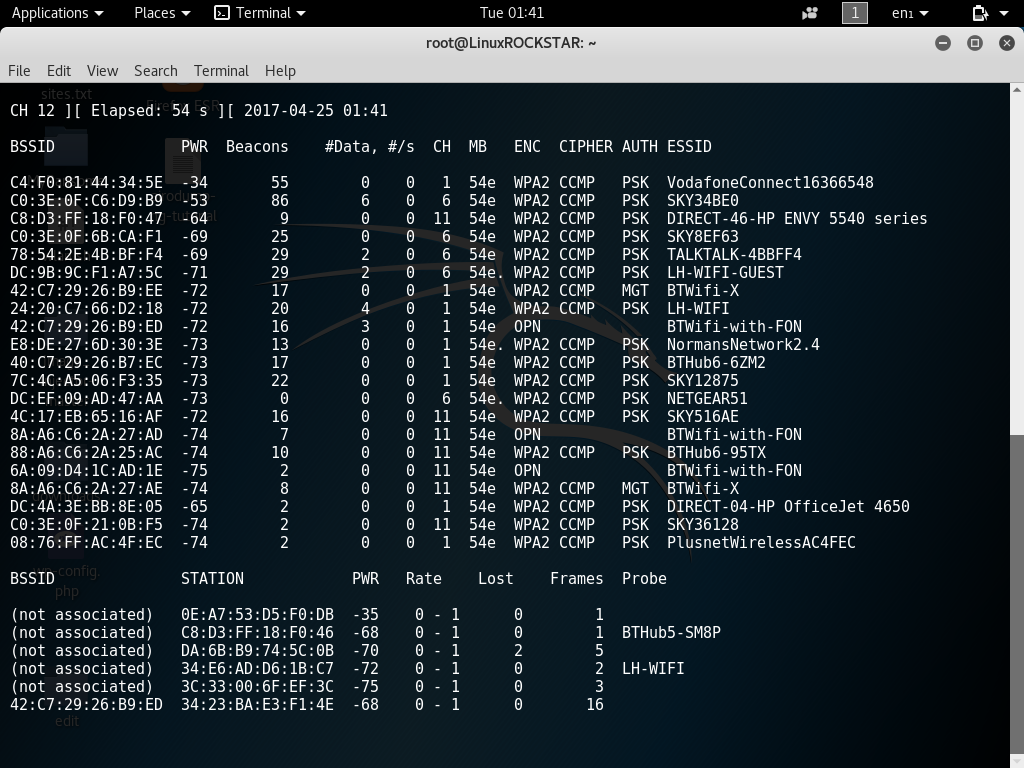
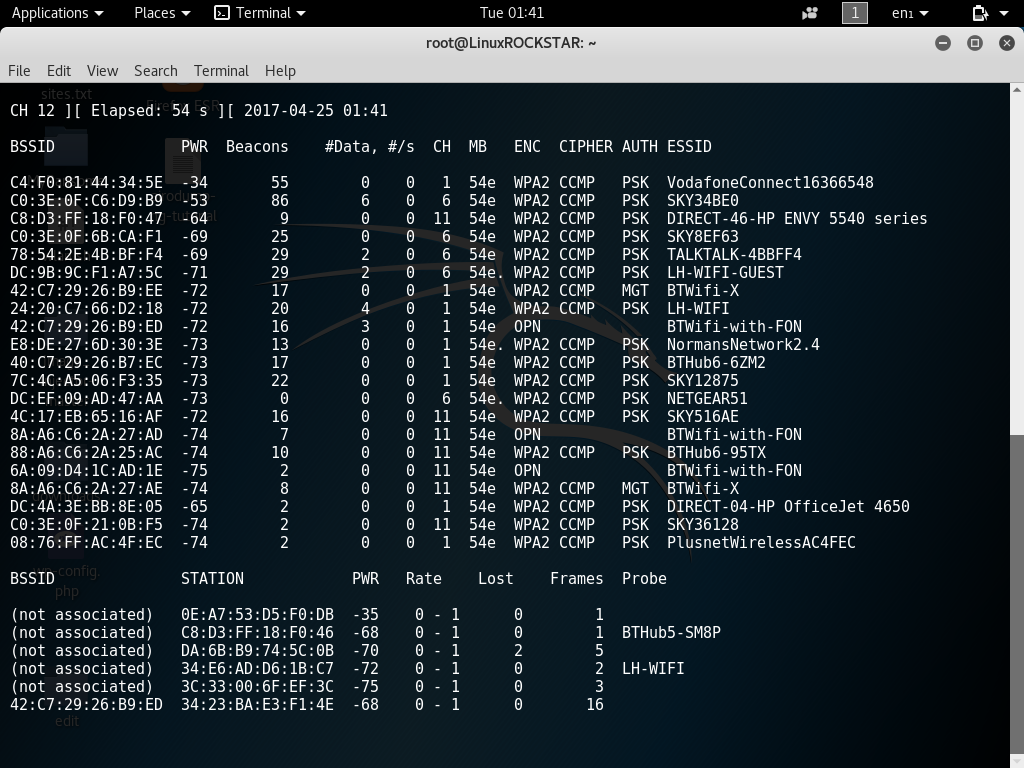
409Hackers RepositoryScanning For Wireless Access Point Information Using Airodump-ng Kali Linux Tutorial
Hi welcome back today in this tutorial you will learn how to scan for various wireless network information using airodump-ng. This information...
-
 172Vulnerabilities
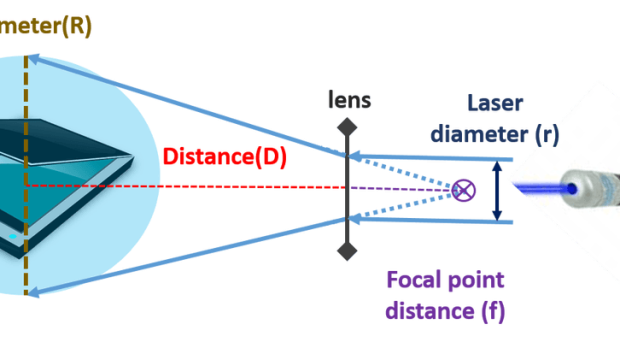
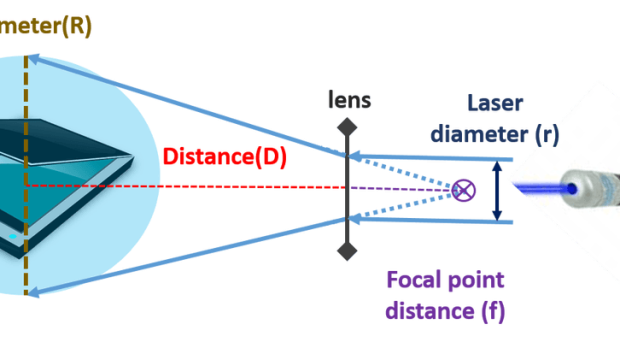
172VulnerabilitiesOps, hackers can exfiltrate data from air-gapped networks through a malware controlled via a scanner
A group of Israeli researchers has devised a new technique to exfiltrate data from a PC in an air-gapped network through malware controlled via scanners....
-

 223News
223NewsCredit Card With Built In Fingerprint Scanner Launched By Mastercard
The credit card has unveiled its today’s fee card that has a built-in biometric fingerprint scanner, permitting customers to authorize payments with...
-
 333Malware
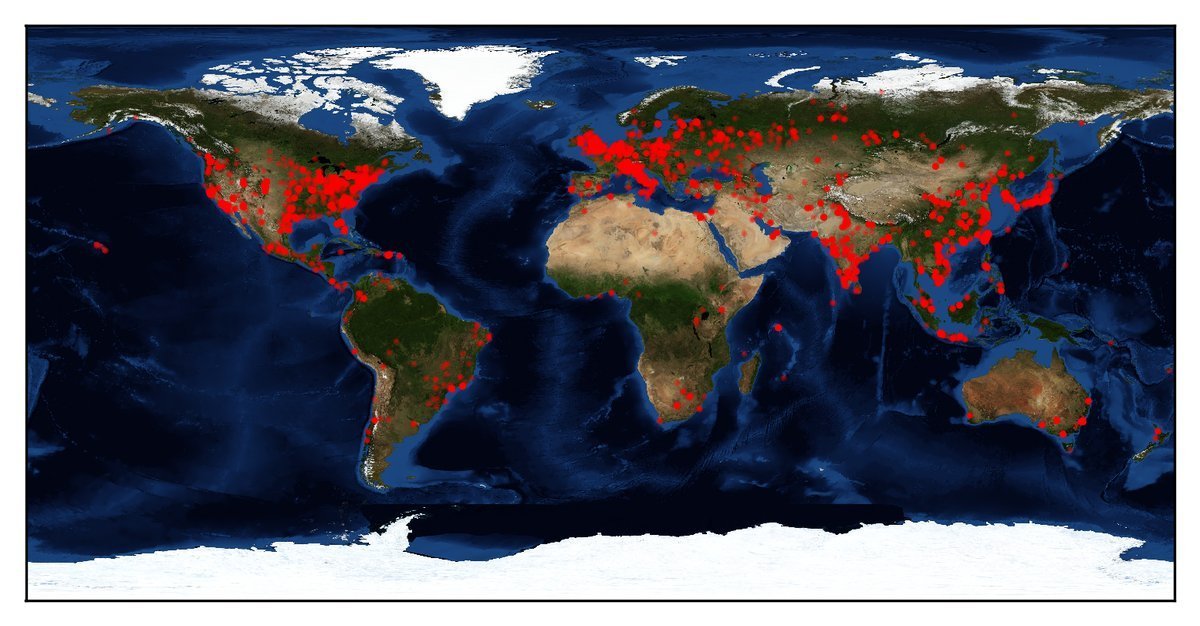
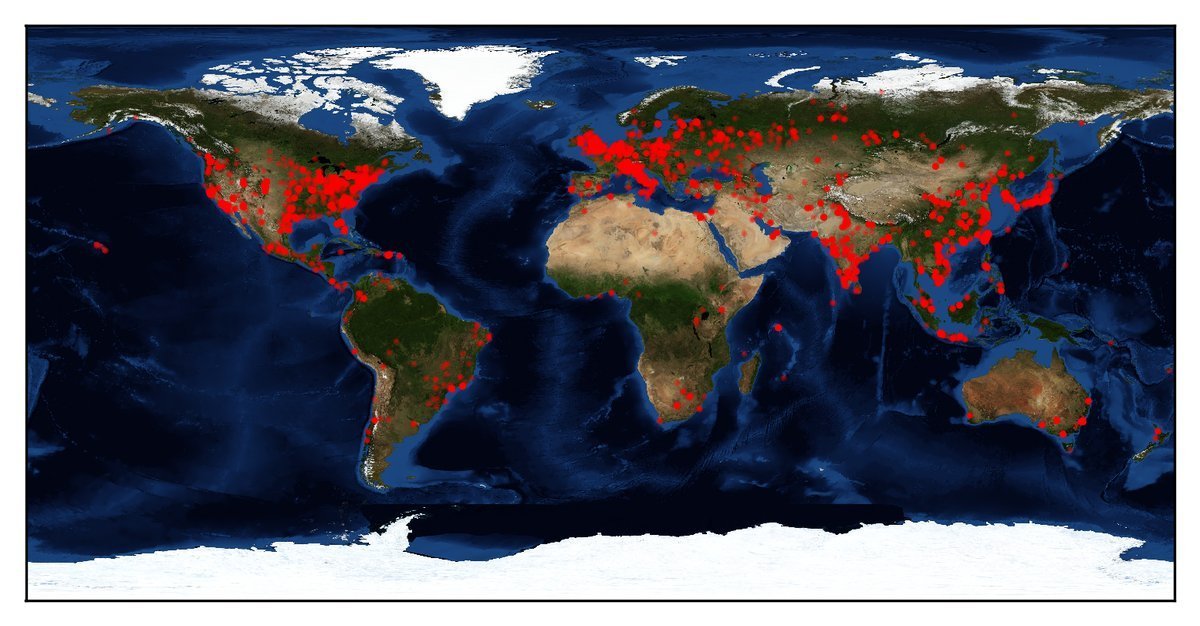
333MalwareMass Scan Revealed More Than 30000 Windows Computers Infected by NSA backdoor DoublePulsar
[jpshare] A Recent Mass Scan Revealed That More than 30000 Windows Machine Infected by National Security Agency Backdoor DOUBLEPULSAR .DOUBLEPULSAR one of the NSA...
-
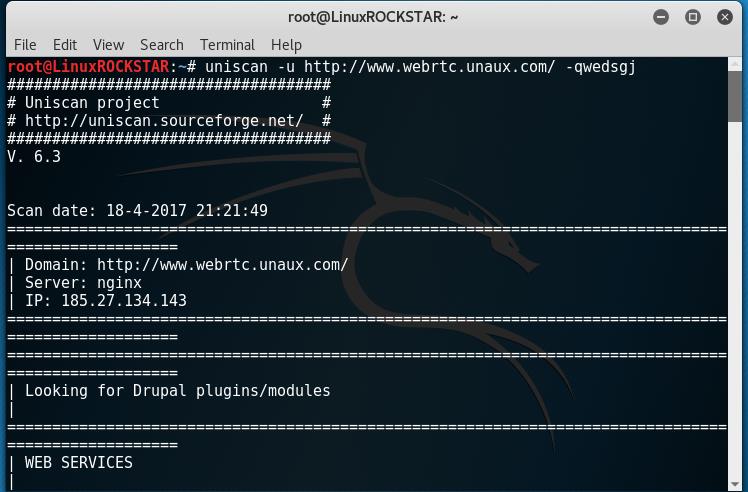
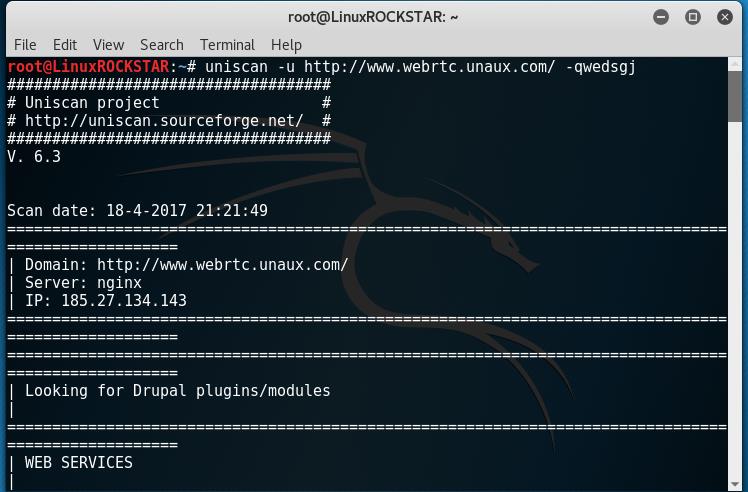 161Hackers Repository
161Hackers RepositoryScan website for vulnerabilities with Uniscan Kali Linux Tutorial
Welcome back, in this tutorial you will learn how to scan and fingerprint a web server or device to find vulnerabilities. To...
-

 442Trojan / Worms
442Trojan / WormsSophisticated Android Based Banking Trojan “BankBot” Reach Play Store Which Avoid Detection by Google Security Scanner
[jpshare]Specifically Target to infect Android Trojan entered into Google Play store which give more pain to Google Security team to find this ...
-

 198Geek
198GeekNew tech allows researchers to bypass fingerprint scanner on smartphone
It’s a common perception that we’re kind of safe by setting up fingerprints scanners on our smartphones. After all, what are the...
-

 131Hackers Repository
131Hackers RepositoryV3n0M-Scanner – Python Pentesting Scanner
Popular Pentesting scanner in Python3.6 for SQLi/XSS/LFI/RFI and other Vulns. [Live Project – Python3.6] https://github.com/v3n0m-Scanner/V3n0M-Scanner V3n0M is a free and open source...
-

 159Data Security
159Data SecurityFlatbed Scanners Used as Relay Point for Controlling Malware in Air-Gapped Systems
Scientists from two Israeli universities have come up with a way to use flatbed scanners as relay points when sending commands to...
-
Hackers Repository
RCE Finder – Scan For Remote Code Execution Exploits
RCE_FINDER How to use root@kali:/rce_finder # python scan_rce.py # LOGO ########################################## #| By Rudra Sarkar - @rudr4_sarkar # #| Loaded Modules :...
-

 513News
513NewsWWE’s Paige X-Rated Photos Leaked – ‘Total Divas’ Star Comments on Scandal
At the moment, rumors are going around about the possible hacking of WWE female superstar Paige. This is after x-rated photos, and...
-

 190Vulnerabilities
190VulnerabilitiesIntel Security (McAfee) Releases Rootkit Scanner Following Vault 7 CIA Leak
Intel Security, soon to be rebranded as McAfee again, released on Wednesday a scanner that can identify hidden EFI firmware rootkits. Intel...
-
Hackers Repository
Davscan – A Tool That Fingerprints servers, finds exploits, scans WebDAV
DAVScan Credits: Graph-X Download Davscan DAVScan is a quick and lightweight webdav scanner designed to discover hidden files and folders on DAV...
-
Hackers Repository
Java Deserialization Scanner
All-in-one plugin for Burp Suite for the detection and the exploitation of Java deserialization vulnerabilities Download Java-Deserialization-Scanner Credits: federicodotta Java Deserialization Scanner...
-

 244How To
244How ToDAVScan – Fingerprints Servers, Finds Exploits & Scans WebDAV
DAVScan is a quick and lightweight webdav scanner designed to discover hidden files and folders on DAV enabled webservers. The scanner works...
-
 276Malware
276MalwareThe new Linux/Rakos, malware threatening devices and servers under SSH scan (Again)
New linux Malware, dubbed Linux/Rakos is threatening devices and servers.The malware is written in the Go language and the binary is usually compressed...






