Search results for "Secrets"
-
 374Data Security
374Data SecurityDistributed Denial o Secrets: a new competitor for WikiLeaks
The cyberactivism has a new anonymous face According to Salvador Ruiz, network security specialist from the International Institute of Cyber Security, Distributed...
-

 325Data Security
325Data SecurityActivists announce massive leaking of Russian politician’s emails on Distributed Denial of Secrets
Cyberactivists have announced the release of a massive archive with leaked information from Russian oligarchs and journalists According to network security and...
-

 315Cyber Crime
315Cyber CrimeFeds accuse Chinese firm of stealing trade secrets of US tech giant
The US Justice Department has accused China to be involved in industrial espionage. According to a press release from the department, the Chinese government...
-

 178Incidents
178IncidentsUnited States: Chinese spies are behind massive hacking that stole aviation secrets
Federal agencies claim that in this hacking campaign 13 firms were attacked for the benefit of a Chinese aerospace company Last Tuesday,...
-

 332Hacked
332HackedSpectre-like “Foreshadow” Flaw In Intel CPUs Can Leak Your Secrets
When the Spectre and Meltdown security flaws in Intel chips were disclosed earlier this year, security researchers called it a loophole so...
-
 341Incidents
341IncidentsNew Spectre attack enables secrets to be leaked over a network
It’s no longer necessary to run attacker code on the victim system. When the Spectre and Meltdown attacks were disclosed earlier this year, the...
-
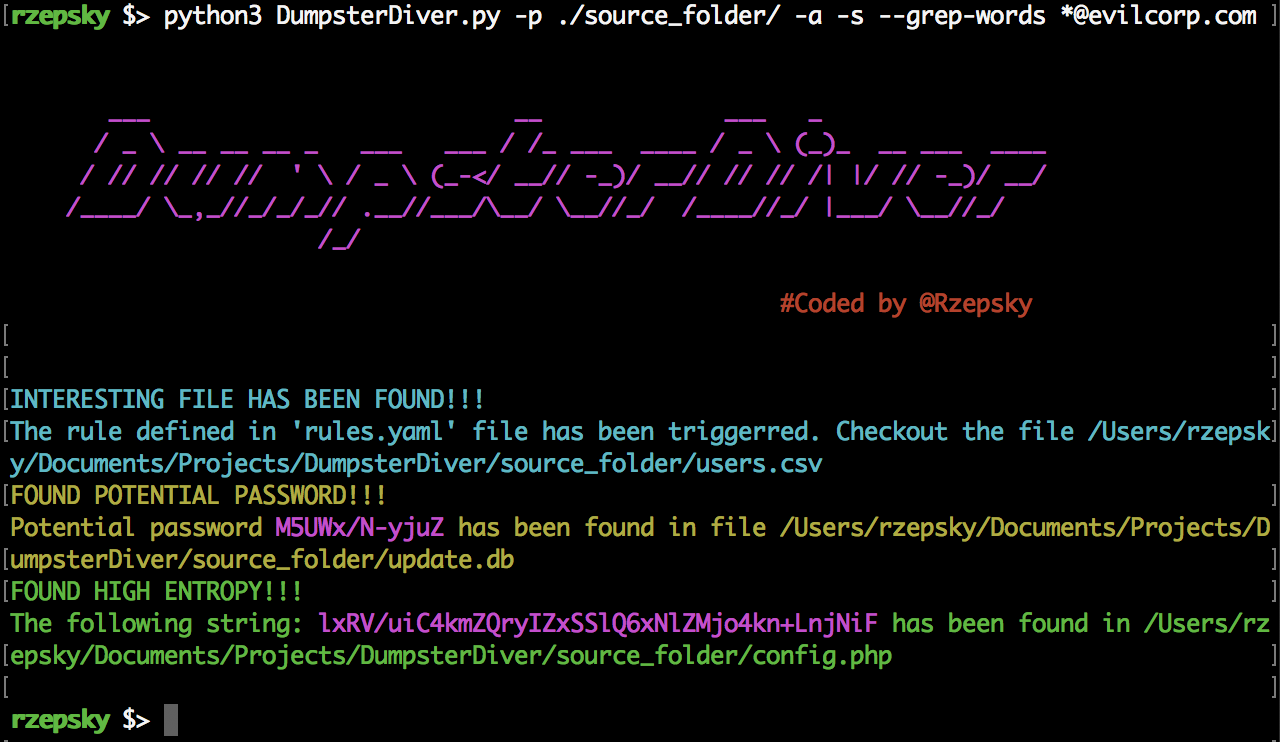
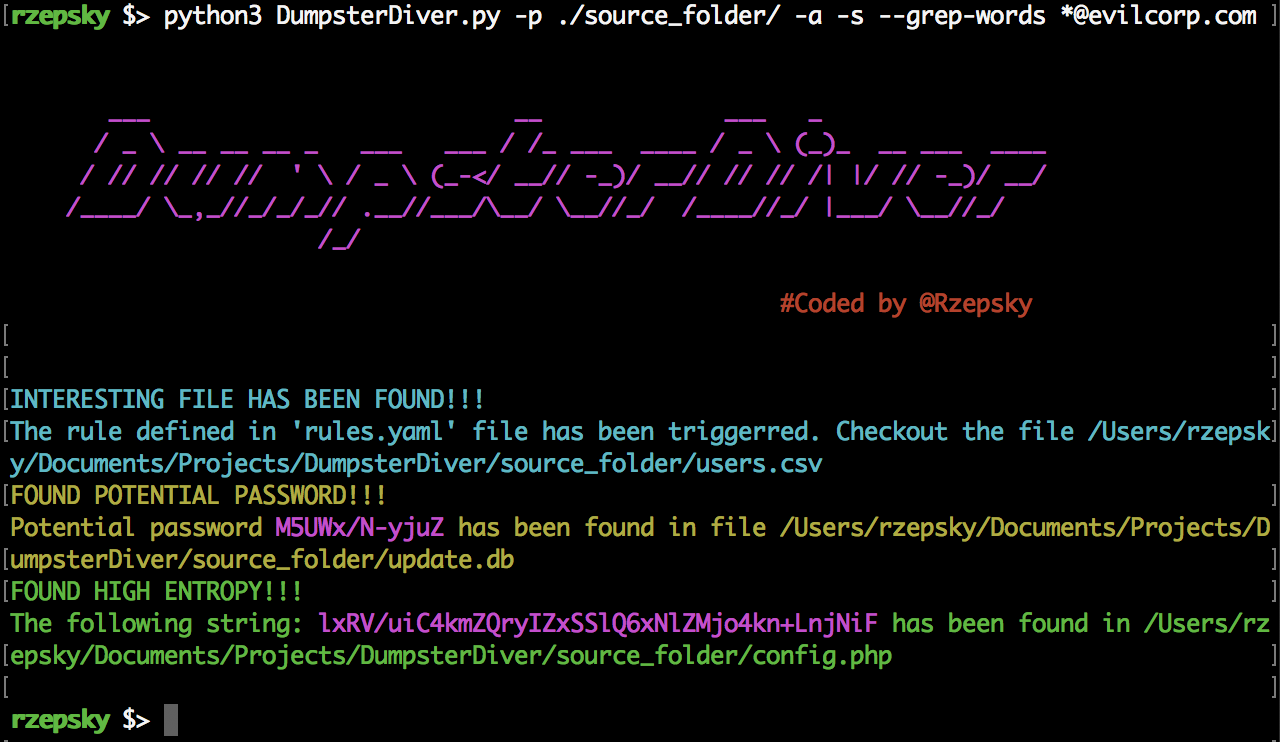 277Hacking Tools
277Hacking ToolsDumpsterDiver – The Tool For Finding Hardcoded Secrets
What is this dumpster diving tool you speak of? The creator of this tool has given us an exclusive insight. LHN have...
-

 420Cyber Crime
420Cyber CrimeEx-employee stole secrets of Israeli spyware firm for dark web deals
Israeli authorities have arrested a 38-year-old man for allegedly stealing secrets of the NSO Group, a Herzliya-based firm that specializes in developing spyware and...
-
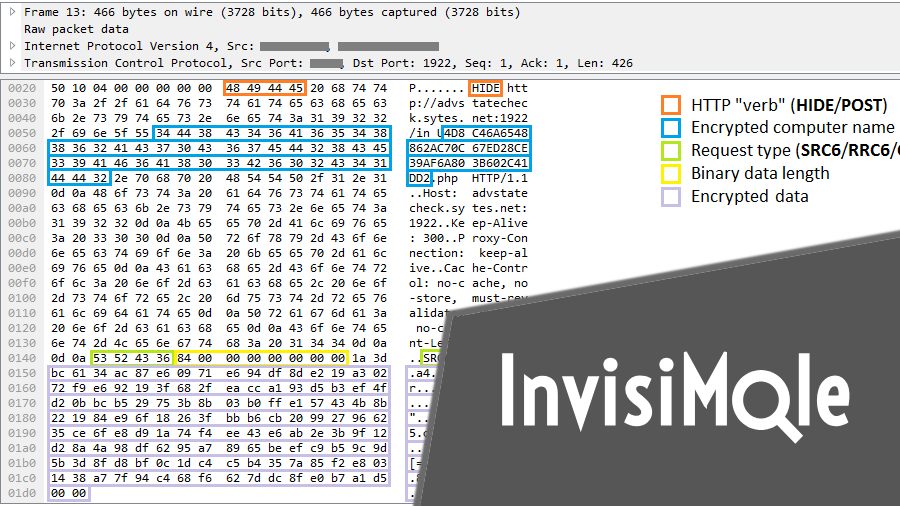
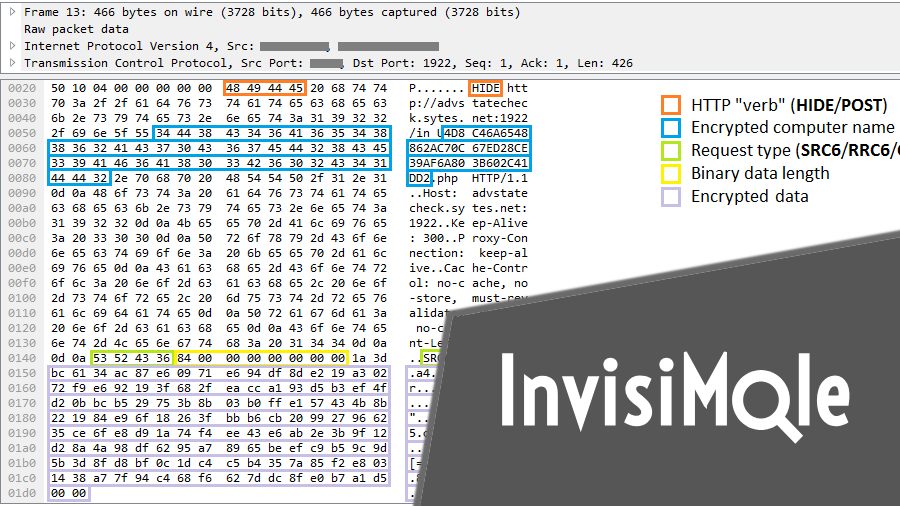 282Hacked
282HackedInvisiMole Spyware Turns Your Computer Into A Video Camera And Steals Secrets
The security researchers at ESET have uncovered InvisiMole: a spyware that has been active at least since 2013. The company’s security products...
-
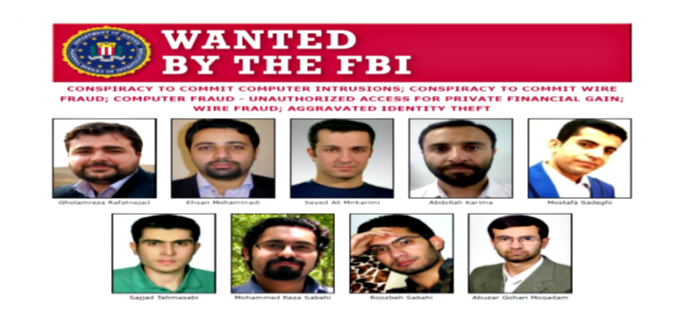
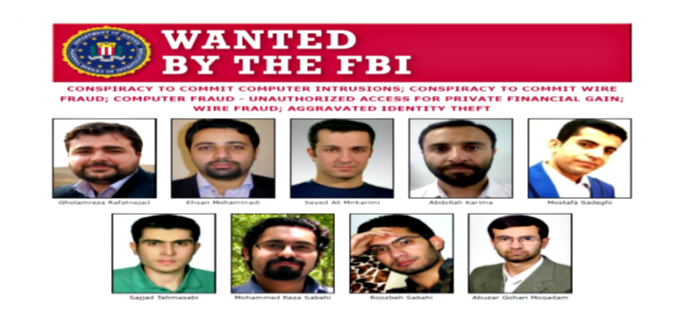 326Cyber Crime
326Cyber Crime9 Iranian hackers charged with hacking universities & stealing secrets
The US Justice Department charged nine Iranian nationals with allegedly hacking on behalf of Islamic Revolutionary Guard Corps (a branch of Iran’s...
-

 394News
394NewsAPT15 Hackers Hit UK Govt Contractor to Steal Military Technology Secrets
The APT15 hacking group has always been associated with Chinese intelligence and it has been part of quite a few, infamous hacking...
-

 357Incidents
357IncidentsSgxSpectre Exploits Recent Intel CPU Flaw And Leaks “Enclave” Secrets
In modern Intel processors, there’s a hardware extension available named Software Guard Extension (SGX) to improve the security aspects. It provides a...
-

 210Malware
210MalwareThis stealthy cat-and-mouse hacking campaign aims to steal diplomatic secrets
Felismus malware deployed to steal documents and carry out surveillance on government foreign policy in a previously unknown campaign. A previously unknown...
-
Articles
U.S. Believes Russian Spies Used Kaspersky Antivirus to Steal NSA Secrets
Do you know—United States Government has banned federal agencies from using Kaspersky antivirus software over spying fear? Though there’s no solid evidence...
-

 237Geek
237GeekRussian Hackers Steal NSA Secrets And Code With The Help Of Kaspersky Antivirus
NSA is one of the world’s most powerful government agencies. But that doesn’t mean it’s immune from different security threats and hacking...
-
 248Courses & Ebooks
248Courses & EbooksReversing: Secrets of Reverse Engineering
Beginning with a basic primer on reverse engineering-including computer internals, operating systems, and assembly language-and then discussing the various applications of reverse...
-

 145Incidents
145IncidentsIn not-too-distant future, brain hackers could steal your deepest secrets
Religious beliefs, political leanings, and medical conditions are up for grabs. OAKLAND, Calif.—In the beginning, people hacked phones. In the decades to...
-

 120Data Breach
120Data Breach‘Professional’ hackers steal industrial secrets from ThyssenKrupp
ThyssenKrupp, one of the world’s major steel makers, has said it has fallen victim to a “professional” hacking attack, with the intent...
-
 266Hacked
266HackedAdultFriendFinder Leak: Hackers Now Know Sexual Secrets Of 412 Million People
Short Bytes: One of the biggest data breaches on the Friend Finder Network has compromised the details of 412 million users across...
-

 295News
295NewsDCNS submarine document leak exposes Indian naval secrets
French naval contractor DCNS said on Wednesday it may have been the victim of “economic warfare” after secrets about its Scorpene submarines...
-
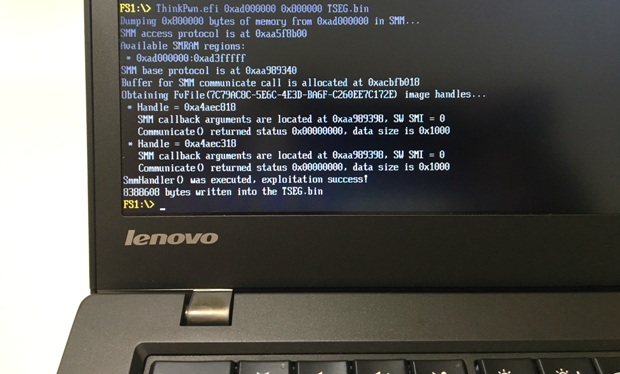
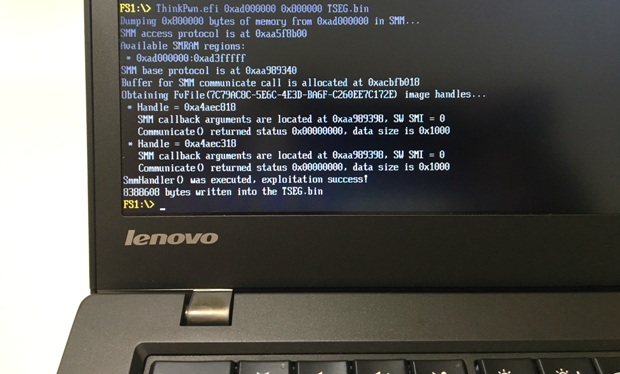 292Vulnerabilities
292VulnerabilitiesExploring and exploiting Lenovo firmware secrets
Hi, everyone! In this article I will continue to publish my research of Lenovo ThinkPad’s firmware. Previously I shownhow to discover and...






