Search results for "Secure"
-

 2.0KHow To
2.0KHow ToHow to secure your TikTok account
From keeping your account safe to curating who can view your liked content, we look at how you can increase your security...
-

 5.1KMalware
5.1KMalwareWelcome Chat as a secure messaging app? Nothing could be further from the truth
ESET research uncovers a malicious operation that both spies on victims and leaks their data
-

 3.3KMobile Security
3.3KMobile SecurityHow secure is your phone’s lock screen?
From the humble passcode to biometric authentication, there are quite a few options to lock your Android phone. But which of them...
-

 4.5KNews
4.5KNewsIs WordPress Secure for eCommerce Websites?
Are you thinking of building a WordPress eCommerce website? If yes, then you might be thinking about the fact that is WordPress...
-

 1.5KPrivacy
1.5KPrivacyTop Ten security settings for a secure Windows 10 Computer
Windows 10 is by far the most acknowledged Windows operating system. Microsoft rolls out updates frequently to ensure bugs are fixed and...
-

 4.5KHow To
4.5KHow ToHow to secure your digital Christmas presents
What are some of the key things you should do with your shiny new device as soon as you unbox it?
-

 4.6KIncidents
4.6KIncidentsMagento Marketplace was hacked; the most insecure platform
Data protection experts reported an intrusion that has impacted Adobe Magento Marketplace users, employed to purchase, sell, and download themes and plugins...
-

 2.1KIncidents
2.1KIncidentsPalo Alto suffers data breach. Are its customers’ networks secured?
Information security specialists reported that Palo Alto Networks, a major security firm based in California, US, has become victim to a data...
-
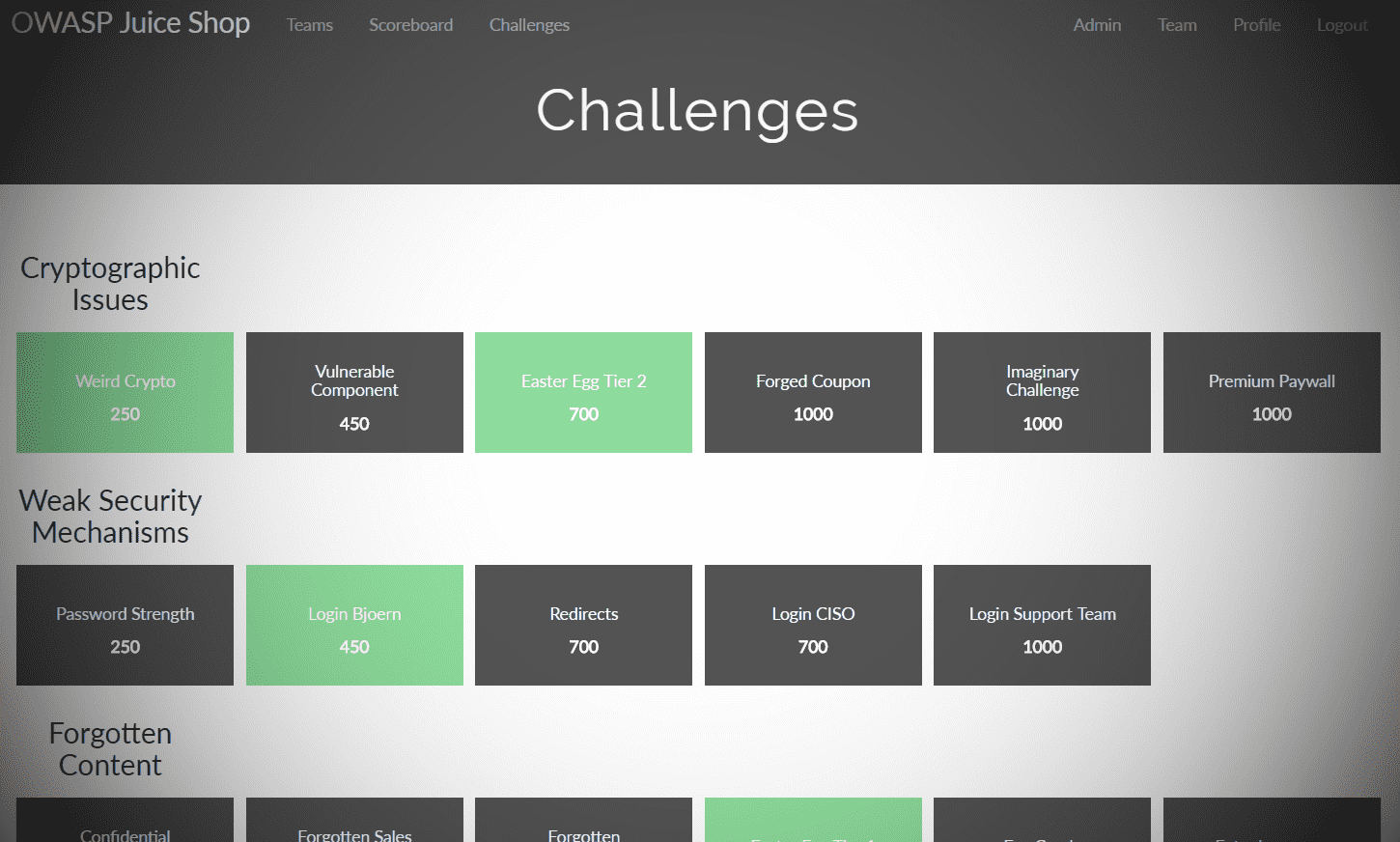
 5.1KHack Tools
5.1KHack ToolsOWASP Juice Shop v9.3 releases: intentionally insecure webapp for security trainings
OWASP Juice Shop OWASP Juice Shop is an intentionally insecure web app for security training written entirely in Javascript which encompasses the...
-

 2.1KNews
2.1KNewsHow to choose secure software for your business
Technologies have grabbed the leadership surrounding us with an enormous amount of information. Some services gather everything in one place and for...
-

 2.1KIncidents
2.1KIncidentsIs it secure to use Monero? Cryptocurrency website and wallet are hacked
Digital forensics specialists report that the official website of Monero, one of the most popular cryptocurrencies, was compromised due to the presence...
-

 5.3KHack Tools
5.3KHack ToolsBrave Browser – Next Generation Secure, Fast And Private Web Browser with Adblocker
The Brave Privacy Browser is your fast, safe private web browser with ad blocker, private tabs and pop-up blocker. Browse without being...
-
 1.3KData Security
1.3KData SecurityWireless Router security: How to set up a WiFi router securely
Highly useful and practical as they are, wireless routers can cost us a lot if we fail to secure them properly. It...
-
 148.3KData Security
148.3KData SecurityAMP for Email: why so secure and how to get whitelisted?
If you’re reading this post, you are probably more or less familiar with brand new AMP for Emails technology developed by Google....
-

 3.9KData Security
3.9KData SecurityGmail is the most secure email service. What about the most insecure? It’s AOL. Full list of email services most exposed to hackers
Unfortunately, data breaches are very common incidents today, with email addresses being one of the most exposed data in these cases. In...
-

 2.6KIncidents
2.6KIncidentsWeb.com, register.com, and Network Solutions were hacked; secure the data of your web domains
Network security specialists report that web hosting services Register.com, Web.com and Network Solutions, were victims of a data breach a couple of...
-

 765Data Breach
765Data BreachUnsecured Adobe Server Exposes Data for 7.5 Million Creative Cloud Users
The U.S. multinational computer software company Adobe has suffered a serious security breach earlier this month that exposed user records’ database belonging...
-

 370Incidents
370IncidentsMedical records of millions of people around the world exposed by insecure software
A group of information security specialists from the security firm WizCase (complete report here) has reported the finding of multiple data leaks...
-

 466Incidents
466IncidentsAvast internal networks were hacked. Did attackers install backdoors in CCleaner? Is it secure to use this tool?
Even security companies are exposed to cyberattacks. IT system audit specialists report that security software developer Avast has become victim of an...
-

 415Vulnerabilities
415VulnerabilitiesPalo Alto, Fortinet and Pulse Secure VPNs are vulnerable to attacks: NSA
Ironically, companies that offer information security services are also exposed to malicious hackers; they’re even a great target. Experts from the National...
-

 406Data Security
406Data SecurityPassword-protected PDFs are not enough to secure sensitive documents. No solutions available
Any deployment, no matter its protections, may be exposed to further hacking attacks. Ethical hacking experts have found a way to extract...






